Inchin ransomware (Improved Instructions) - Virus Removal Guide
Inchin virus Removal Guide
What is Inchin ransomware?
Inchin ransomware – a cyber threat that comes from the Scarab ransomware family
Inchin ransomware is a notorious infection that comes from the Scarab family and appends the .inchin extension to each locked file and document. Discovered by Amigo-A and announced on Twitter,[1] this ransomware virus drops the RECOVER.txt ransom message where it provides Inchinaiturtle@protonmail.com and WuTang444@protonmail.com email addresses for creating communication between the cybercriminals and victims. The crooks offer to help the users to decrypt their files by delivering them the decryption software for a specific payment. Also, Inchin virus developers offer to send them one file up to 5 MB for a free decryption process as bringing up evidence that the recovery tool truly exists. Additionally, this ransomware virus has multiple similarities with Danger ransomware.
| Name | Inchin ransomware |
|---|---|
| Type | Ransomware virus/malware |
| Founder | Amigo-A is a cybersecurity researcher that has announced about his findings on Twitter social network |
| Appendix | The ransomware virus uses symmetric or asymmetric encryption to lock up the files and adds the .inchin appendix to each filename |
| Ransom note | This malware provides all of its threatenings and demands via the RECOVER.txt text message |
| Crooks' emails | The criminals add Inchinaiturtle@protonmail.com and WuTang444@protonmail.com email addresses as a way to contact them |
| Distribution | Ransomware infections are most commonly distributed through phishing emails and their infectious attachments. These cyber threats can also spread through cracked software that is downloaded from p2p networks, and through vulnerable Remote Desktop Protocol configuration |
| Removal | You can get rid of the ransomware virus by employing automatical software and carrying out the process with a strong and reliable antimalware tool. Keep in mind that the manual elimination is not an option in this case as you might miss some crucial steps or locations where the malware might be hiding |
| Data recovery | If you have discovered .inchin files and documents on your Windows computer system, you should not rush to pay the cybercriminals as these people might seek to scam you. Instead of taking such risk, go to the end of this article and try some data recovery methods that are placed there |
| Fix tip | If you have found some compromised entries or other areas on your affected device, you can try repairing them with automatical software such as FortectIntego |
Inchin ransomware is a notorious malware strain that can apply suspicious modifications to the Windows Task Manager and Registry locations. There you might discover unknown processes and registry keys injected. Note that such processes might allow the ransomware to boot itself up within every Windows computer startup process.
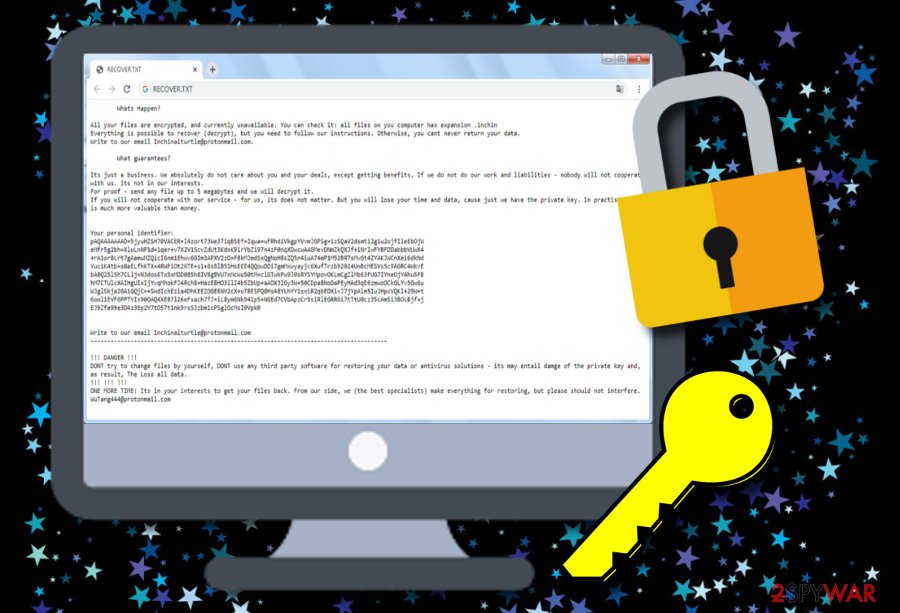
Continuously, Inchin ransomware might be able to scan the entire system once in a while and search for encryptable components. Once all files are locked, the cybercriminals save both encryption and decryption software on remote servers where the keys become unreachable for anyone except the cybercrooks themselves.
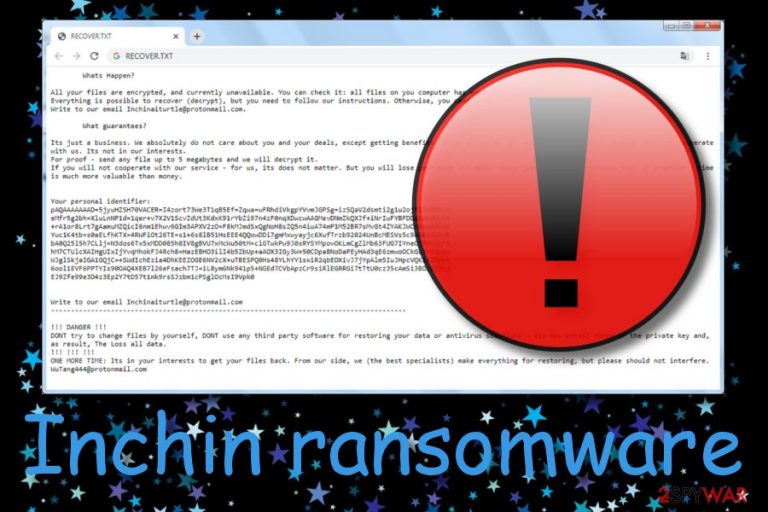
Afterward, Inchin ransomware provides a ransom message and threatens the users that the only way to recover the lost data is by purchasing the key from them, otherwise, the files might be lost forever:
All your files are encrypted, and currently unavailable. You can check it: all files on your computer have extension .inchin. Everything is possible to recover (decrypt), but you need to follow our instructions. Otherwise, you can never return your data. Write to our email Inchinaiturtle@protonmail.com.
It’s just a business. We absolutely do not care about you and your deals, except getting benefits. If we do not do our work and liabilities – nobody will cooperate with us. It is not our interests.
For proof – send any file up to 5 megabytes and we will decrypt it.
If you will not cooperate with our service – for us, it does not matter. But you will lose your time and data, because we have the private key. In practice – time is much valuable than money.
However, we recommend not falling for believing in Inchin ransomware developers as these people might easily scam you. They might ask you for an inadequate sum of money and leave you with no tool at all. Mostly, such crooks demand Bitcoin or another type of cryptocurrency that allows the process to remain safe and untrackable.
Continuously, Inchin ransomware might try to harden the process for you by deleting or permanently damaging the Shadow Volume Copies of infected files by running specific PowerShell commands. Also, the malware might be capable of destroying the Windows hosts file to prevent you from accessing security-related websites and forum pages.
In addition, Inchin ransomware makes the infected Windows computer system vulnerable to other infections. As a result, you might end up with a Trojan virus on your machine. If this happens, it may result in serious data and money theft. Also, your machine might receive serious damage that can be hardly repairable.
You should remove Inchin ransomware from your Windows computer, otherwise, it might experience serious damage. Besides, you will not be able to recover your files properly until the infection is gone. If you are having trouble with detecting the malware, travel to the end of the article where you will find system rebooting steps.
After Inchin ransomware removal, you should scan your entire computer system for possible damage. If the software finds any signs of corruption, you can try fixing the touched areas with the help of a repair program such as FortectIntego. When the virus is gone and the damage is fixed, continue with data recovery techniques that are added to the end of this page.
Malicious actors deliver the infectious payload attached to phishing emails
Security experts from LosVirus.es[2] state that ransomware infections are widely distributed through email spam[3] and the malicious attachments that come clipped to the phishing email message. This happens when the crooks succeed to trick the victims by pretending to be from well-known shipping companies such as FedEx and DHL or from other healthcare and banking organizations.
You should always carefully verify the sender and his email address. If you are seeing a questionable email sender address, you should avoid opening the message. However, if you have already viewed the content of the message, do not click on any hyperlinks that are provided in it and check for possible grammar mistakes as if it were a note from a reliable organization, no mistakes would be left in the text.
Continuously, cracked software is another possible delivery source of ransomware. If you are a frequent visitor of peer-to-peer networks, you might find yourself sitting with malware afterward. A piece of advice would be to get all of your products and services only from reliable websites and the official developers. Also, use antimalware protection so that you would be alerted if something dubious or malicious is trying to sneak into your computer system.
Last but not least, ransomware infections are distributed through unsecured Remote Desktop Protocol configuration. If the RDP includes an easy-guessable password such as “abc123”, then the hackers might easily hack your machine. Having none password at all, doubles the risk. What you have to do is properly secure your RDP. Think of complex security codes that include symbols, letters, and numbers.
Automatical removal guidelines for Inchin ransomware
If Inchin ransomware has been launching malicious processes that have been preventing you from detecting or eliminating the malware, you should boot your computer in Safe Mode with Networking or via System Restore to deactivate the ransomware virus first. We have provided instructions for both booting methods at the end of this article.
Afterward, you should proceed with Inchin ransomware removal automatically. This includes downloading and installing antimalware software that is strong enough to detect and remove the ransomware virus from your Windows computer. Also, if you want to look for possible damage, you can try employing software such as SpyHunter 5Combo Cleaner or Malwarebytes.
If the tools discover any corrupted areas, you can try fixing them with a tool such as FortectIntego. Once you remove Inchin ransomware from the computer and fix all the damage that it might have brought, you can start going through some data recovery tips that have been added to the end of this page and might help you to restore some of your files.
Getting rid of Inchin virus. Follow these steps
Manual removal using Safe Mode
To deactivate malicious settings on your Windows computer system and disable the parasite, you should boot your machine in Safe Mode with Networking. If you do not know how to opt for this feature, you should complete the below-provided step-by-step guide.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Inchin using System Restore
To disable bogus changes on your Windows computer and deactivate Inchin ransomware virus, you should opt for the System Restore feature. You can use the steps below to apply for this function.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Inchin. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Inchin from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If you have spotted files with the .inchin appendix, it is an accurate sign of Inchin ransomware hacking your computer and encrypting your files. Rather than paying the demanded ransom price and risking to get scammed, you should try alternative data recovery techniques such as the ones that are provided below.
If your files are encrypted by Inchin, you can use several methods to restore them:
Using Data Recovery Pro might allow you to restore at least some of your files and documents.
If the ransomware virus has locked all of your files and documents, you can try recovering them back to their previous state by employing such software. Also, complete all steps exactly as displayed in the instructions, otherwise, you might not be able to reach the best results possible,
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Inchin ransomware;
- Restore them.
Windows Previous Versions feature might help you with data recovery tasks.
If you have activated System Restore on your Windows computer and disabled all malicious changes, you should give this method a try as it might recover some of your individual files.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Use Shadow Explorer for the files' restoring process.
Try using this piece of software if there is some data that you want to bring back to its previous state. Note that this technique might not work properly if the ransomware virus has launched specific PowerShell commands to eliminate the Shadow Volume Copies of your encrypted files and documents.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Currently, the cybersecurity experts are working on the official decryption tool.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Inchin and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Amigo-A. New variant of #Scarab-#Danger #Ransomware. Twitter. Social platform.
- ^ LosVirus.es. LosVirus. Security and spyware news.
- ^ Email spam. Wikipedia. The free encyclopedia.







