Salsa ransomware / virus (Virus Removal Instructions) - Feb 2020 update
Salsa virus Removal Guide
What is Salsa ransomware virus?
Salsa ransomware – file locking malware that presents ransom notes in 40 different languages

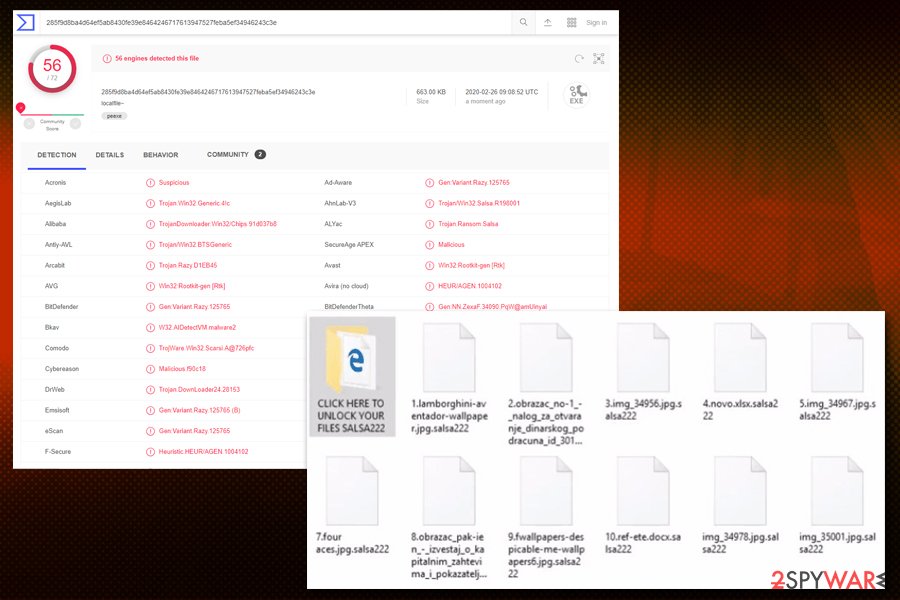
Salsa ransomware, otherwise known as Salsa222 ransomware, is a cyber threat that locks all personal files on the infected machine and then asks for a ransom in Bitcoins to redeem access. The virus uses the XOR encryption algorithm and marks all pictures, videos, music, documents, PDF, and other data with .salsa222 marker. Additionally, to explain to victims what happened to their computers and personal files, Salsa222 virus drops READ TO UNLOCK FILES.salsa.html.
When the virus first hit the stage in April 2017, it immediately drew attention for its one peculiar feature. While there are multiple file-encrypting threats that present the ransom note in several languages, Salsa ransomware drops ransom notes in 40 different languages to ensure that victims get the message through. Besides, the malware also replaces the default wallpaper with “bg222salsa.jpg,” which is essentially a black background with a text “SALSA PERSONAL FILES ENCRYPTED.”
| Name | Salsa ransomware, Salsa222 ransomware |
| Type | Cryptomalware, file locking virus |
| Distribution | Spam emails, malicious or hacked websites, booby-trapped ads, cracks/keygens, exploits, etc. |
| Encryption algorithm | Malware uses a mix of XOR and cipher of unknown origin to lock data on the system, skipping system and executable files |
| Related files | Salsa222.exe, SalsaDownload.exe, SalsaDecryptor.exe, bg222salsa .jpg |
| Extension | Each of the encrypted files are appended with .salsa222 marker, e.g., picture.jpg.salsa222 |
| Ransom note | The virus drops 40 different ransom notes, each representing a different language, which includes French, Spanish, German, Swedish, Turkish, Russian, Korean, Japanese, Arabic, and many others |
| Ransom size | Crooks are asking for ransom in Bitcoins, and the size may vary from $150 to $500, or even more |
| File recovery | Without paying cybercriminals and having no backups, recovering data is difficult. Nevertheless, it may be possible to retrieve some of your files with the help of alternative methods we provide in our recovery section below |
| Malware termination | Perform a full system scan with the help of anti-malware software that can detect[1] the threat |
| System fix | In case the Windows is malfunctioning after you terminate the infection, repair virus damage with FortectIntego |
The prevalence of Salsa222 ransomware is relatively low, despite the attackers' efforts to satisfy every potential “customer” from 40 countries. Nevertheless, they may use several different methods to spread the malware around, which includes:
- Spam email attachments and hyperlinks
- Exploit kits
- Software cracks
- Repacked application installers
- Web injects
- Malicious ads
- Fake updates, etc.
However, before encrypting files, Salsa ransomware performs the necessary changes on the Windows system, which include modification of the registry, deletion of shadow volume copies, connection to a remote server, creation of new malicious processes, etc. These changes may sometimes complicate Salsa ransomware removal, and it may only be performed in the Safe Mode.

Once the machine is compromised, the Salsa virus encrypts all the personal data and drops 40 different ransom notes into a separate folder titled “Click here to Unlock your files Salsa222.” Each of the files represents the following languages:
Arabic; Belorussian; Bengali; Bosnian; Bulgarian; Chinese; Croatian; Czech; Danish; Dutch; English; Estonian; Finnish; French; German; Greek; Gujarati; Hebrew; Hindi; Hungarian; Icelandic; Indonesian; Italian; Japanese Javanese; Kannada; Korean; Latvian; Lithuanian; Malayalam; Marathi; Norwegian; Persian; Polish; Portuguese; Romanian; Russian; Serbian; Simplified Slovak; Slovenian; Spanish; Swedish; Tamil; Telugu; Thai; Traditional Turkish; Ukrainian; Urdu; Vietnamese;
Connections to Razy ransomware and other details
According to its technical specification, it links to the malware called Razy ransomware, which came into the daylight last year[2]. However, the latter threat is not single-use ransomware. Its hackers have developed it into a bigger virus project. Underestimating, it might be lead to severe outcomes. Even if you got infected with this malware, there is no need to comply with the demands. It would be a wiser solution to remove Salsa ransomware with reputable anti-malware software. To fix your damaged Windows system files, employ FortectIntego.
This malware follows the manner of some cyber infections that appeared last year, which preferred changing your desktop picture into a ransom notification. Likewise, Salsa attempts to scare users more by replacing their background picture into black wallpaper with few words informing that the victims’ files have been infected. It indicates the deadline when users have to pay 500 dollars or 0.465112 bitcoins[3].
They also give instructions for users in case the decryption process fails to complete successfully. In that case, they should reboot the device and download Salsa Decrypter from the indicated servers. Note that installing this file might only corrupt the system more. Even if you succeed in retrieving the wanted documents, later on, you might be struck with another wave of the cyber attack.
It does not take long for victims to notice their compromised files as all of them are marked with .salsa222 file extension. Another feature raises concern as this virus can delete show volume copies. Unfortunately, this factor leaves fewer chances for file recovery. Nonetheless, it does not mean that you should follow the pre-determined scenario set by hackers. Thus, it would be better to concentrate on Salsa222 removal.
Ransomware prevention
The majority of ransomware threats are spread via spam email attachments, specifically, via the .zip, .doc, .pdf, and similar files. Previously, Google has declared war on JavaScript attachments[4]. Nonetheless, gearheads have easily found a way how to evade this ban. The fraudulent attachments might be even placed in double .zip folders[5].
Furthermore, Salsa ransomware has been detected as Gen:Variant.Razy.125765, Trojan.DownLoader24.28153, a variant of Win32/Kryptik.FQQS, Gen:Variant.Razy.125765, etc. Likewise, it is necessary to improve the overall security of your system. For that purpose, the combination of an anti-virus and anti-spyware utilities might be efficient. A firewall would come in handy as well. Lastly, such protection will be wasted if you carelessly review the contents of spam messages and enable shady browser attachments.
Getting rid of Salsa222 malware
Looking for tips on how to carry out efficient Salsa ransomware removal, you will come across multiple articles that promote one or another security application. In general, you should not meddle with ransomware manually as it often corrupts and modifies your system files.
Unless you are a virus researcher, manual intervention might have a perilous effect on the system. After you remove Salsa virus, you might try some of the data recovery methods. Take a look at the bottom of the page. Some of the recommendations might be effective in your case.
Getting rid of Salsa virus. Follow these steps
Manual removal using Safe Mode
Can't launch an anti-malware app? Regain access by completing these steps.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Salsa using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Salsa. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Salsa from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Salsa, you can use several methods to restore them:
Is it worth installing Data Recovery Pro?
This utility is said to recover your files as well as damaged or lost emails.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Salsa ransomware;
- Restore them.
Make use of Windows Previous Versions
If System Restore is enabled, you might recover some of the files by following the below-suggested links.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Salsa222 Decrypter
Do not get tempted to download the tool offered by the crooks. In exchange for the decrypted files, you might be an easier target for future ransomware attacks.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Salsa and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ 285f9d8ba4d64ef5ab8430fe39e8464246717613947527feba5ef34946243c3e. Virus Total. File and URL analysis.
- ^ Danny Palmer. This old ransomware variant is back - with sneaky new tricks. ZDNet. Technology News, Comments, Analysis, Comments and Product Reviews.
- ^ Phil Muncaster. Star Trek Ransomware Demands Monero Payments. InfoSecurity. Insight. Strategy. Technology.
- ^ Chris Merriman. Google to ban JavaScript attachments in Gmail. TheInquirer. News, reviews, and opinion for tech buffs.
- ^ Alice Woods. Sage 2.0 ransomware virus. 2-Spyware. Remove spyware, adware.





















