CryptoJoker ransomware (Removal Guide) - Jul 2017 update
CryptoJoker virus Removal Guide
What is CryptoJoker ransomware?
CryptoJoker ransomware is a true menace to your computer
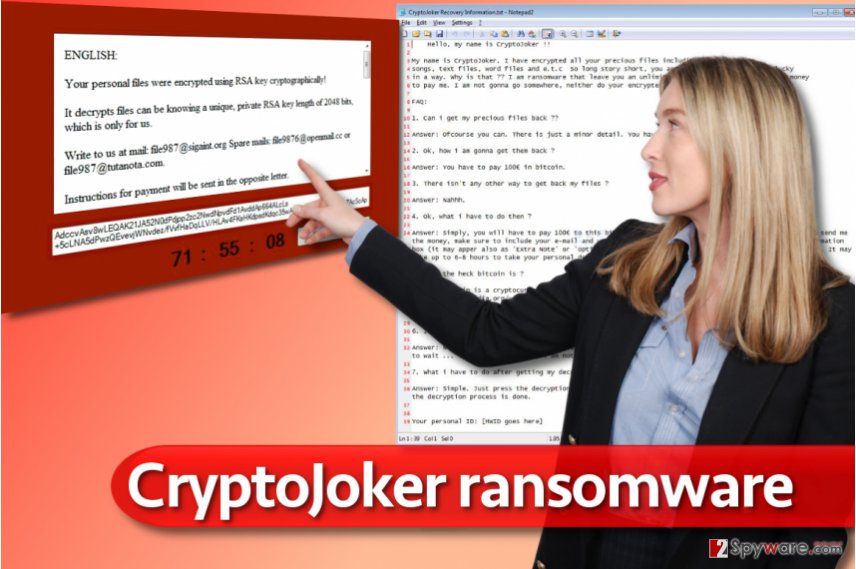
CryptoJoker is a name of a ransomware virus that damages personal files stored on computers. The virus first emerged in 2016[1], but in July 2017, CryptoJoker 2017 ransomware virus emerged. Both viruses seek to encrypt files on victim's computer to demand a ransom.
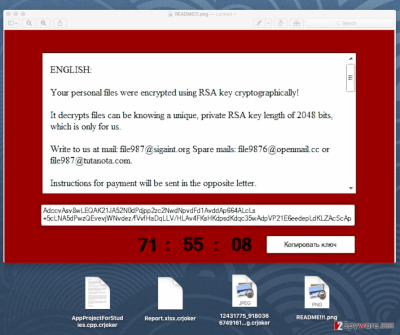
As much as we know, the initial CryptoJoker seeks to infect files with extensions such as .txt, .docx, .doc, .xls, .pdf, .java, .jpeg, .sql, .db, .docm, .odt, .csv, .xlsb, .xlsm, .aspx, .html, .psd, .pptx, .mdb, .sln, .xlsx, and many more. The virus encrypts these files using the AES-256[2] encryption algorithm. After the file gets encrypted, this ransomware adds a .crjoker extension to the filename.
If you have noticed that your files have changed their names in such way, you should immediately take actions to stop this deadly virus! For that, we STRONGLY recommend using a reputable anti-malware software, for instance, FortectIntego or any other reliable one.
Keep in mind that once CryptoJoker virus encrypts these files, you will not be able to access them anymore. Crypto Joker leaves messages in the folders that hold the encrypted files as .txt or .html documents. The message states that the personal records were encrypted, and to retrieve them, user needs to contact CryptoJoker developers by sending an e-mail letter to them:
Write to us at mail: file987@sigaint.org
Spare mails: file9876@openmail.cc or file987@tutanota.com.
Instructions for payment will be sent in the opposite letter.
As you can see, this terrible computer threat demands to pay a ransom to retrieve the encrypted files back. Surprisingly, this machine threat does not demand a fixed amount of money, and that gives an idea that the cybercriminals are ready for a negotiation. However, security vendors do not recommend paying the ransom, because there is no guarantee that you will get your files back. Plus, do you wish to support cyber-criminals so that they can continue their knavish activities?
2017 brings another version of CryptoJoker
In June 2017, malware analysts spotted a CryptoJoker 2017 ransomware virus making rounds on the Internet. It was dubbed identically as the malware that emerged in 2016, but to distinguish both viruses, a year of the first appearance was added. The ransomware encodes files but experiences problems when trying to corrupt files that are opened by the user.
The ransomware checks .txt and .md files' sizes with FileInfo.Length property, and encrypts large files partially. The virus marks these files with .partially.cryptojoker extensions. For smaller files of the same types, the malware uses a .fully.cryptojoker extension. The rest of files get encrypted partially and get corresponding file extensions.
The developer of the ransomware has published the ransomware code online, stating that it was created “for education purposes only.” Such statement is a complete nonsense since script kiddies can quickly take that code and convert the ransomware into a fully working extortion tool. If you accidentally got infected with this ransomware, we strongly suggest using anti-malware software to remove CryptoJoker 2017 as soon as possible.
Tricks used to spread the ransomware
In most of the cases, this or any other ransomware viruses are distributed via harmful e-mail attachments. Ransomware is spread like Trojans – mostly, these viruses pretend to be a safe file to convince the user to download and open it. According to VirusActivity[3] research, the described virus is spread as a PDF file. However, you can also infect your computer with this virus by browsing insecure websites or clicking on corrupted links. We have some tips how you should prevent installing CryptoJoker ransomware:
- Do not browse through suspicious web sources – there is a chance you might click on an infected link and download a computer threat without realising that.
- NEVER OPEN e-mails AND attachments from senders that you DO NOT personally know! Also, do not open suspiciously looking e-mails, because some viruses tend to take over victim’s e-mail and forward the infected letter to victim’s contacts.
- Install software safely. Some programs tend to promote third-party freeware in an indirect way, so you have to be careful when installing new apps. Select either Advanced or Custom installation settings and opt-out any suspicious or unfamiliar attachments.
Remove CryptoJoker and try existing data recovery tools
You can remove CryptoJoker virus on your own, but you will need to use an anti-malware software to complete this task. It is highly advisable not to attempt to delete the ransomware manually because you can never know what files and programs it brought into your system. Leave this task for a professional anti-malware tool that can detect potentially dangerous files automatically.
Before you begin CryptoJoker removal procedure, take a look at instructions provided below. They are designed to help you to delete the malware from the system. See, some ransomware viruses are made to block anti-malware programs, and our guide explains how to bypass this obstacle.
Getting rid of CryptoJoker virus. Follow these steps
Manual removal using Safe Mode
Use the provided instructions to remove CryptoJoker while in Safe Mode with Networking.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove CryptoJoker using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of CryptoJoker. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove CryptoJoker from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.At the moment of writing, there are no verified ways to completely recover the lost files unless you have backups. However, you can still try one of the following tools to recover the files – some people say that they have helped them. You can find some useful tips below.
If your files are encrypted by CryptoJoker, you can use several methods to restore them:
Run Data Recovery Pro tool
\
Running Data Recovery Pro on your computer allows you to detect compromised files. The tool may or may not be capable of restoring them.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by CryptoJoker ransomware;
- Restore them.
Use Volume Shadow Copies
Volume Shadow Copy Service is available on Microsoft Windows. It helps to recover lost, corrupted or damaged files using their previous versions.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Crypto Joker decryption tools are not available yet
Neither CryptoJoker or CryptoJoker2017 have official decryption tools released yet. As soon as they appear on the market, the article will be updated.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from CryptoJoker and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Lawrence Abrams. The CryptoJoker Ransomware is nothing to Laugh About. BleepingComputer. News, Reviews, and Technical Support.
- ^ Advanced Encryption Standard. Wikipedia. The Free Encyclopedia.
- ^ The Official Website of VirusActivity. VirusActivity. The Latest News about Virus Activity.





















