NTK ransomware / virus (Removal Instructions) - Virus Removal Guide
NTK virus Removal Guide
What is NTK ransomware virus?
A ransomware dubbed NTK is not as dangerous as it seems to be
NTK virus is a screen-locking Trojan horse[1], which earns the name of ransomware[2] due to its ability to block access to the computer and demand a ransom from the computer owner or user. Just like any other ransomware virus, it is a vicious software that functions as an extortion[3] tool. NTK Screenlocker virus displays a full-screen message for the victim, and at the moment NTK ransomware supports French language only. Upon installation, it runs itself as a Winban.exe file, also adds shady entries into Windows Registry[4] and ensures that it stays on the computer system for a long time. However, despite efforts that the developer of NTK malware put into it, the ransomware can be removed with anti-malware tools like FortectIntego or Malwarebytes easily. The screen-locking window contains a message, which says:
You got pOwned by NTK
Ton PC est bloque 🙂 Si tu veux pouvoir le reutiliser, suis les instructions ci-dessous.
- Appuyez sur Afficher coordonnees
- Envoyez un mail et mettre en objet : Code UTK
- le vous enverrai code contre une rancon
Afficher coordonnees
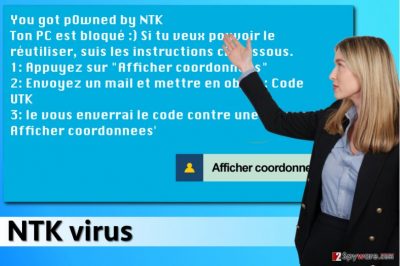
In short, virus’ author who names itself as NTK, says that the victim has to click on “Afficher coordonnees” button (display coordinates), which reveals cyber criminals’ email address. They will then ask you to pay a ransom to get access to your own PC, but obviously, you shouldn’t pay it. If you enter this code – 15s4e56dsjdhfy87 into the provided field, you would be redirected to another panel that explains how to remove the virus and unlock access to the computer. However, since we are going to provide you these instructions for free, you do not need to waste your time contacting cyber criminals, or, even worse, spending your hard-earned money by paying ransoms[5]. You can find the guide on how to remove NTK malware below this article. Do not forget to use professional anti-malware tools after NTK removal to scan your system and find any additional threats that you may have installed in the past.
How does this ransomware disseminate?
You do not want to be deceived by cyber criminals again, don’t you? If so, please read this paragraph attentively. Please try to avoid opening emails that come from unsolicited and unknown individuals or companies. Here are some tips how you can identify malicious emails:
- Look at sender’s email address. Check it on Google if you doubt that it comes from a trustworthy person/company.
- If you have any doubts about an individual email message, do not open files attached to it, nor links included in the letter.
- Check what kind of link appears in your browser’s bottom left corner as you hover over the message or underlined text including hyperlinks. If these URLs appear to be very long and suspicious, do not click on anything!
- Ransomware can also be delivered to you via exploit kits or compromised websites, so to prevent such attacks, we suggest keeping your programs up-to-date and installing an anti-malware program on the system.
Remove NTK virus by yourself
Ransomware is a complicated program, and NTK removal needs to be completed with extreme caution. You do not want to leave those ransomware files on your system, especially because most of them are assigned as default startup programs, which means they are going to be run immediately after booting the computer system. To remove NTK virus, follow instructions provided below.
Getting rid of NTK virus. Follow these steps
Manual removal using Safe Mode
- Click Control + Alt + Delete buttons on your keyboard. This will open Windows Task Manager.
- Run a task explorer.exe.
- Click on Windows button on your keyboard.
- Click on Startup folder. Here, delete the winban.exe file.
- Reboot your PC in a Safe Mode with Networking as explained below and scan the system for malware remains using the anti-malware program.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove NTK using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of NTK. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from NTK and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ What is a Trojan Virus? - Definition. Kaspersky Internet Security Center. Cyber Security Resource for Tips, Topics, and Trends.
- ^ Kim Boatman. Beware the Rise of Ransomware. Norton. Your Security Resource.
- ^ Ransomware and Cyber Extortion: Computers Under Siege. Kaspersky Lab. Kaspersky Blog.
- ^ Tim Fisher. What is the Windows Registry?. Lifewire. Tech Untangled.
- ^ Before You Pay that Ransomware Demand…. Krebs On Security. In-depth security news and investigation.





















