Colorit ransomware (Removal Instructions) - Decryption Steps Included
Colorit virus Removal Guide
What is Colorit ransomware?
Colorit ransomware is the cryptovirus that demands Bitcoins for encrypted users' files

Colorit ransomware is the new version of the malware that appears similar to other threats because it uses similar features. It is common for crypto malware to mimic others with ransom note files, contact emails or payment instruction windows, in this case. However, this is a confirmed version of DCRTR-WDM ransomware.
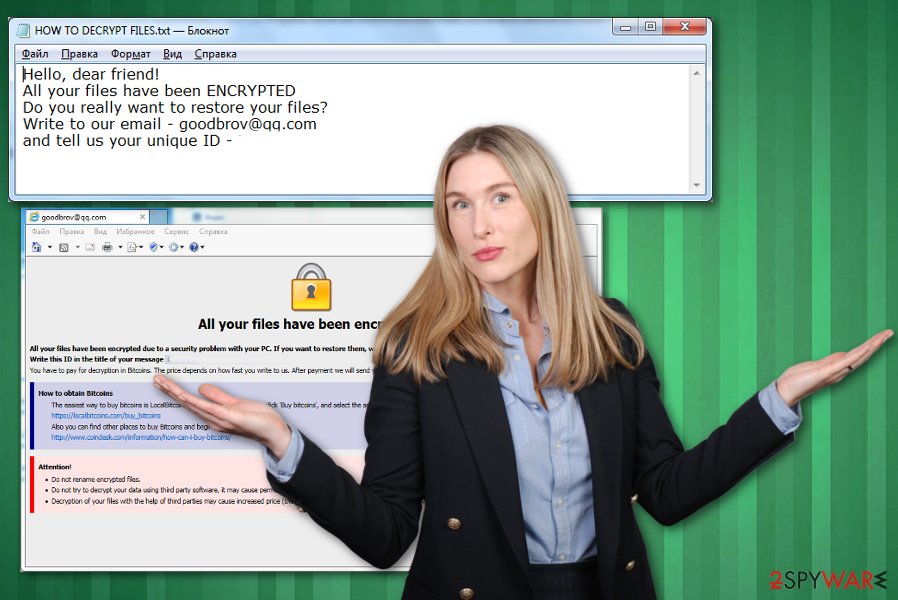
As previous variants in the same cryptovirus family Colorit ransomware uses a sophisticated encryption algorithm, makes users' data useless by locking those files and then demands a ransom in the note placed as HOW TO DECRYPT FILES.txt file. Also, when data gets marked with .COLORIT file extension, browser window named as the ransom note delivers more information regarding the payment methods.
Although the message that COLORIT ransomware developers release, contains only contact email, reaching them is not recommended or advised since it can lead to data or money loss and more severe damage to your device. Since various AV engines can detect this threat, you should rely on anti-malware programs and scan the computer entirely to get rid of the notorious cryptovirus instead of paying the ransom demand.[1]
| Name | Colorit ransomware |
|---|---|
| Type | Cryptovirus |
| Distribution | Spam email attachments, phishing messages, infected documents |
| Symptoms | Files get encrypted and locked, system security functions disabled, a ransom note appears on the locked screen |
| File marker | .COLORIT |
| Family | DCRTR-WDM ransomware |
| Danger | Exposes to malicious content, hackers can damage or steal users' data, affect the infected machine significantly |
| Elimination | Use FortectIntego for Colorit ransomware removal |
Colorit ransomware virus is the cyber threat that belongs to one of the most dangerous virus category – cryptovirus. This is the type of malware that performs encryption-based attacks on targeted systems. Since it focuses on creating ransom notes in English, malware can spread on the bigger part of the world. Although ransomware is the threat that mainly gets on Windows OS, Mac devices also can get infected by similar threats.[2]
The first step of COLORIT ransomware attack is an encryption process, and then virus places the ransom note called HOW TO DECRYPT FILES.txt on the desktop and in every folder with encoded data. The message reads:
Hello, dear friend!
All your files have been ENCRYPTED
Do you really want to restore your files?
Write to our email – goodbrov@qq.com
and tell us your unique ID
Additionally to this file, Colorit ransomware developers want to pose as other threats in this category that display payment instructions, places where to get Bitcoins and other information regarding cryptocurrency wallets and the ransomware attack. These instructions appear on the screen when the encryption is done. HOW TO DECRYPT FILES.hta displays the following:
All your files have been encrypted!
All your files have been encrypted due to a security problem with your PC. If you want to restore them, write us to the e-mail goodbrov@qq.com
Write this ID in the title of your message 6f34b033fce61c65a909e1xxxxxxxxxx
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us. After payment we will send you the decryption tool that will decrypt all your files.
How to obtain Bitcoins
The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click 'Buy bitcoins', and select the seller by payment method and price.
https://localbitcoins.com/buy_bitcoins
Also you can find other places to buy Bitcoins and beginners guide here:
http://www.coindesk.com/information/how-can-i-buy-bitcoins/
Attention!
•Do not rename encrypted files.
•Do not try to decrypt your data using third party software, it may cause permanent data loss.
•Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
The particular ransom amount is not revealed in these files, but COLORIT ransomware developers specify the amount when the victim writes them an email asking for redemption and file recovery. This payment may differ from hundreds of dollars to thousands, based on the amount and the importance of the encrypted data.
However, as many experts[3] always note paying the ransom demanded by cybercriminals like Colorit ransomware creators is not a good idea. You should clean the machine instead and then rely on data recovery software or your file backups and restore affected files.
Colorit ransomware encrypts data from photos, documents, audio, and video files and makes those files useless. In most cases, this is the primary concern for victims, but ransomware also:
- disables system security functions;
- adds new registry entries;
- deletes files and programs;
- damages or steals data.
You should remove Colorit ransomware from the machine and avoid any communication with cybercriminals behind this threat. They are not trustworthy or reliable because the only purpose of such malware is to gain money from victims or steal their personal and valuable information.
For the best results, you should perform automatic Colorit ransomware removal and use FortectIntego or a similar anti-malware program in the process. Professional antivirus tools can check the machine thoroughly and indicate dangerous or malicious, corrupted files and programs.
When COLORIT ransomware virus gets detected alongside other related programs and files, tools like this can delete the threat from your device and improve the performance significantly this way. You should also consider keeping the application on the machine and running a full scan occasionally to keep the system virus-free.
Spam email campaigns and phishing message attacks deliver a malware payload
The most popular method used to distribute such threats like ransomware involves fake email notifications posing as the legitimate company or service, so the user is more likely to believe that this is a truthful message. Unfortunately, this is only a method used to deliver malware on unsuspected users' devices via one click of the button.
Ransomware infiltration happens when the user triggers malicious macros delivered via the spam email attachments, in most cases, PDF or Word documents. Once the document gets downloaded and opened on the targeted machine malicious script is launched, and ransomware payload dropper activates the malware infection.
This can be avoided by paying more attention to processes that happen online, received emails and other notifications that appear on the screen. When you delete emails sent from suspicious companies or services or notifications with grammar mistakes you avoid getting cyber infections.
Terminate Colorit ransomware and clean the machine thoroughly
For the automatic Colorit ransomware removal process, you should employ trustworthy anti-malware programs like FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes. These tools fit the requirements because the antivirus program performs a full system scan and malware removal process.
This is especially crucial when you need to remove Colorit ransomware, so all programs and files can get deleted altogether during one system cleaning. Employ a program from a reputable source to avoid additional infiltrations. Remember that not every antivirus tool performs the same since they all have different databases of malware programs.
Getting rid of Colorit virus. Follow these steps
Manual removal using Safe Mode
Get rid of Colorit ransomware by rebooting your machine in the Safe Mode with Networking before the system scan with AV tools
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Colorit using System Restore
Make the PC safe again by removing traces of Colorit ransomware virus with System Restore feature
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Colorit. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Colorit from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Colorit, you can use several methods to restore them:
Data Recovery Pro serves the purpose of an alternate method of file restoring when data gets deleted or encrypted by threats like Colorit ransomware virus
You should try Data Recovery Pro for encrypted files or accidentally deleted records
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Colorit ransomware;
- Restore them.
Windows Previous Versions feature allows recovering files affected by the virus
To use Windows Previous Versions, System Restore should be enabled before
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer – a method for data recovery when file backups do not help
Colorit ransomware may affect Shadow Volume Copies. If not, you can restore files with ShadowExplorer
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Decryption tool is not developed for this version yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Colorit and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Svchost.exe analysis. Virustotal. Online malware scanner.
- ^ Jim Lynch. Will macOS protect you from ransomware attacks?. Cio. Tech news, analysis and blogs.
- ^ Dieviren. Dieviren. Spyware related news.





















