Conficker.C (virus) - Free Instructions
Conficker.C Removal Guide
What is Conficker.C?
Conficker – a computer parasite responsible for millions of infection worldwide
Attacks of such malware can lead to crippled computer networks of cities and interference with elections and social media. Since there are many versions of the botnet, it can launch any of these processes and lead to far worse attacks. This worm is one of the more persistent threats in the history of cybersecurity.
This virus spreads using various methods that are more common and unconventional techniques like exploiting vulnerabilities and looking for system flaws on the targeted system. Ransomware, miners, worms, and other malware set to perform system changes and launch processes in the background come unnoticed, and the victim only encounters system issues or suspicious activity.
| Name | Conficker |
|---|---|
| Type | Worm |
| Danger level | High |
| Symptoms | Annoying messages on the screen, crashes of the system, suspicious processes running in the background |
| Distribution | Exploits MS08-067 vulnerability, spreads through insecure external drives, infected files |
| Known | Since 2008 |
| Elimination | Use anti-malware tools for system cleaning and virus removal |
| System fix | FortectIntego can help to restore the overall system's health |
Mainly Windows OS has been subject to attacks by this malware. Furthermore, it may run under the disguise of comaddin32.dll, svchost.exe, explorer.exe, or services.exe command in the Task Manager. Since its appearance, different variations have been detected. Naturally, they bear alternative names, such as Downup, Downadup, Kido, and Conficker B++[1].
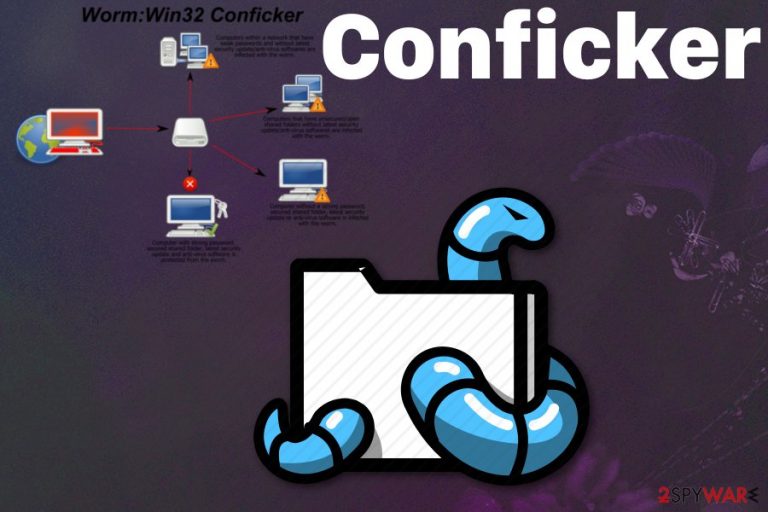
The computer worm was first detected in November 2008[2]. It breaks into a computer system and then connects to a larger network of machines – botnet, which then spreads the malware to other devices. Security vulnerabilities and outdated systems serve as the main vector for the worm to occupy the device. The malware is also capable of infecting removable devices such as USB sticks.
During the years, malware has evolved into a significant threat. Microsoft has even issued a 250 000 USD dollar reward for finding the culprit. Interestingly, ransomware developers decided to share the notorious fame of the worm and Conficker ransomware.
The emergence of this malware initiated the formation of the Conficker Working Group, which investigates the computer networks and IP addresses whether they are infected with the malware. It is suspected that over 600 000 devices still possess the threat. Over the years, the discussions about the infection have subsided. It has been a popular tendency among cybercriminals to revive older viruses.
Likewise, the same scenario may be applicable for this worm as well. Luckily, even if you get infected with this malware, the majority of anti-spyware security applications are able to detect and remove it. Most researchers believe that the worm is developed by Ukrainian hackers who focus on creating the platform for global theft.
Malware employs sophisticated encryption algorithms RC4, RSA, and MD6 that are produced by the premier cryptologist. The Ukraine clue was spotted when the feature about self-destruction on Ukrainian PCs was discovered.
The worm displays tons of redirects to suspicious domains to disguise the source of commands and this way machines come to the point where they overheat and crash. There are versions of the worm and the most known appears to be Conficker.C that was especially active at the end of 2011.
While improving technical specifications, the developers also shifted from using the previous title to the current one. When this worm emerged, few have anticipated what damage it would inflict on the entire cyberspace globally. Business companies and individual users in more than 190 countries have suffered from the hijack[3].
The flexibility of this malware was one of the key reasons why this malware has remained on the market. Once it gets into the system, it may disable security applications, download corrupted files, collect personal information and, most importantly, connect the device to a botnet.
Once Conficker.C malware settles on the operating system, it will add a specific file to the removable drive to the local drives. Then the dialogue box emerges asking to “Open folder to view files.” The only thing which might trigger your suspicion is the line indicating – “Publisher not specified.” During its presence, the computer processes significantly deteriorate.
Nonetheless, to the bewilderment of the virtual community, the virus has not been terminated yet. Indeed, it is less active than in 2008. Interestingly, the worm would not have emerged if not for a fatal Microsoft patch (MS08-67) released in 2008[4].
Certain technical specifications allowed the virus to emerge and remain one of the top 5 most destructive threats. Since it targets system vulnerabilities, devices with poor passwords, it explains why the threat has not been seized and still remains potentially dangerous.
Furthermore, the current version of the worm targets not only ordinary computers but MRI machines, IoT devices, and CT scanners, such as police surveillance cameras. Such actors emphasize the necessity to secure devices by updating crucial system applications, features. Install a proper anti-virus program. You should pay close attention to all the parts and possible risks on the device you don't want to remove Conficker in the future.
Besides anti-malware utilities such as SpyHunter 5Combo Cleaner and Malwarebytes, are practical as well. They might detect minor malicious files which signal a more elaborate threat. Lastly, it is no less important to be aware of the distribution. Once the threat is successfully terminated, you should use the FortectIntego tool to get your system back on its feet.

Methods for virus distribution
The sophisticated method this worm infiltrates the core of computer requires knowledge of `particular Microsoft engineering. This worm discovered new flaws in the Windows operating system and can exploit them to infiltrate the needed machines before users patch those vulnerabilities.
The worm also can disguise its point of origin and hide controllers, malicious files. It even encrypts commands and controls to avoid the shut down by security tools or even IT experts. Another common way to spread such malicious files dropping the worm on the computer involves spam email campaigns and file attachments. Various documents, PDFs, and common types like DLLs or EXE files pose as attachments on the email containing legitimate-looking financial messages.
These emails look safe due to facts like:
- familiar company or service name;
- financial or informational purpose of the email;
- the email received going to the main email box, not spam.
Remove Conficker by using reliable security tools
When the worm entered cyberspace and started spreading terror, one of the key questions was whether it was possible to remove Conficker virus. The identity of developers remains a mystery as well as the specific number of still functioning bots.
On the other hand, you should bear in mind that the virus is still present in the virtual space and spreads around the world. Even if you happen to get infected with this computer worm, a variety of anti-virus programs both, professional and less powerful, are capable of detecting the threat[5]. Launch it and start Conficker removal.
Developers of the worm can even use the infected machine for more attacks, and current threats can launch a range of different processes. Although many researchers took over the control of this botnet, they cannot indicate particular instructions and offer a remedy for the victim. You need to rely on FortectIntego, SpyHunter 5Combo Cleaner, Malwarebytes and clean the machine thoroughly from all the malware installed without your permission.
How to prevent from getting worms
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ PrintPrint Newsletter Help protect yourself from the Conficker worm. Microsoft. Everything about Microsoft products.
- ^ Conficker. Wikipedia. The free encyclopedia.
- ^ The odd, 8-year legacy of the Conficker worm. WeLiveSecurity. News, views, and insight from the ESET security community.
- ^ Graham Cluley. Seven years on, the Conficker worm is not dead... but dominating. Graham Cluley. Award-winning computer security news, advice and opinion.
- ^ Tom Spring. Conficker Used in New Wave of Hospital Iot Device Attacks. ThreadPost. The first stop for security news.
