DNS Changer Malware (Improved Guide) - updated Jan 2017
DNS Changer Malware Removal Guide
What is DNS Changer Malware?
DNS Changer trojan is an infection that is used to redirect users to fraudulent domains, change user’s search results and serve compromised ads. This is done by altering PC’s DNS addresses to Rove Digital domain name server. As soon as you get infected with DNS changer malware, criminal gets ability to connect you to fraudulent websites or to interfere with your browsing activities. Besides, you may also get infected with other malware as well. This problem was noticed and seemingly stopped in November, 2011, when FBI shut down[1] DNSChanger’s servers, taking away access to the Internet from those with affected computers. The scammers are reported to earn millions of dollars from their affiliates.
Modus operandi of DNS Changer malware:
More than one million of computers reportedly have been infected by DNS Changer malware[2]. The most popular way to infect victims with this trojan is to push fake video codecs and fake flash updates. Though FBI locked down a group of hackers who should be blamed for spreading this malware in November, 2011[3], note that these means might be used by hackers in the future.
The most important thing about DNS Changer malware is that July 9, 2012 was the last day when FBI was helping users infected with DNS Changer Malware to connect to the FBI’s temporary servers to access the Internet and, if you were unknowingly infected with this trojan, you probably have temporarily lost your Internet connection[4]. If you have been infected with this trojan without realizing it, you won’t be capable to reach or find anything on the web because you will be redirected to servers that are dead.
Updated on January 5, 2017: DNSChanger virus is making rounds on the Internet again
DNSChanger trojan is back, and this time it spreads via malware-laden ads. It appears that DNSChanger is being spread via corrupted banner ads that contain malicious code, and clicking on these ads reroutes the victim to a website that hosts DNSChanger exploit kit[5]. This technique reminds us of Stegano exploit kit, which is also currently infecting users who are unaware of malware-laden ads. Then the exploit kit checks if the victim has any unsecured routers (those with weak passwords or outdated firmware) and infects them immediately. As soon as the router gets compromised, the malware configures router’s settings to use malicious DNS servers instead of real ones. Reportedly, currently there are over 166 router models vulnerable to this malware. Below, you can find a list of known router models that are vulnerable to this attack:
- NetGear WNDR3400v3 (also, possibly other models);
- Netgear R6200;
- Pirelli ADSL2/2+ Wireless Router P.DGA4001N;
- D-Link DSL-2740R;
- COMTREND ADSL Router CT-5367 C01_R12.
We strongly recommend you to secure your router by giving it a strong password. Also, check if your router is running the latest firmware version, and disable remote administration.
How to remove DNS Changer Malware:
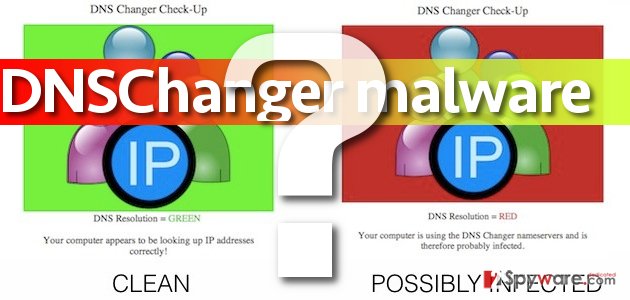
First of all, you should check whether you are have been infected with DNS Changer Malware by visiting this page.
In addition, restore DNS settings to default:
For Windows XP:
1. Go ‘Start’ > ‘Control Panel’ > ‘Network Connections’ and select your local network.
2. Right-click ‘Properties’, choose ‘Internet Protocol’ (TCP/IP).Right-click, choose ‘Properties’ again.
3. Click ‘Properties’ and choose ‘Obtain DNS server address automatically’, ‘OK’.
For Windows 7:
1. Go ‘Control Panel’, click ‘Network and Internet’, then ‘Network and Sharing Center’, and click ‘Change adapter settings’.
2. Right-click ‘Local Area Connection’, then ‘Properties’.
3. Choose ‘Networking’ tab, ‘Internet Protocol Version 4’ (TCP/IPv4) or ‘Internet Protocol Version 6’ (TCP/IPv6) and click ‘Properties’.
4. Choose ‘Advanced’ and select ‘DNS’ tab, ‘Obtain DNS server address automatically’, OK.
Finally, note that DNS Cnager Malware goes together with nasty viruses, such as Trojan.Fakealert or Trojan.Generic, or is capable to block anti-virus software and hide the security updates. That’s why we highly recommend running a full system scan with FortectIntego and SpyHunter 5Combo Cleaner anti-malware programs.
How to prevent from getting trojans
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Chloe Albanesius. FBI Shuts Down DNSChanger Servers. PC Magazine. Technology Product Reviews, News, Prices & Downloads.
- ^ DNSChanger. Wikipedia, the free encyclopedia.
- ^ Fahmida Y. Rashid. FBI Busts Massive Click-Fraud Cyber-Ring That Netted $14 Million. eWeek. Technology News, Tech Product Reviews, Research and Enterprise Analysis.
- ^ Paul Ducklin. DNS Changer – how not to lose your internet connection on July 9. Naked Security. Computer security news, opinion, advice and research from anti-virus experts Sophos.
- ^ Tom Spring. DNSChanger Exploit Kit Hijacks Routers, Not Browsers. Threatpost. The first stop for security news.
