Dridex virus (Virus Removal Instructions) - updated Apr 2020
Dridex virus Removal Guide
What is Dridex virus?
Dridex malware – a well-developed banking trojan that can avoid detection by AV engines and anti-malware tools
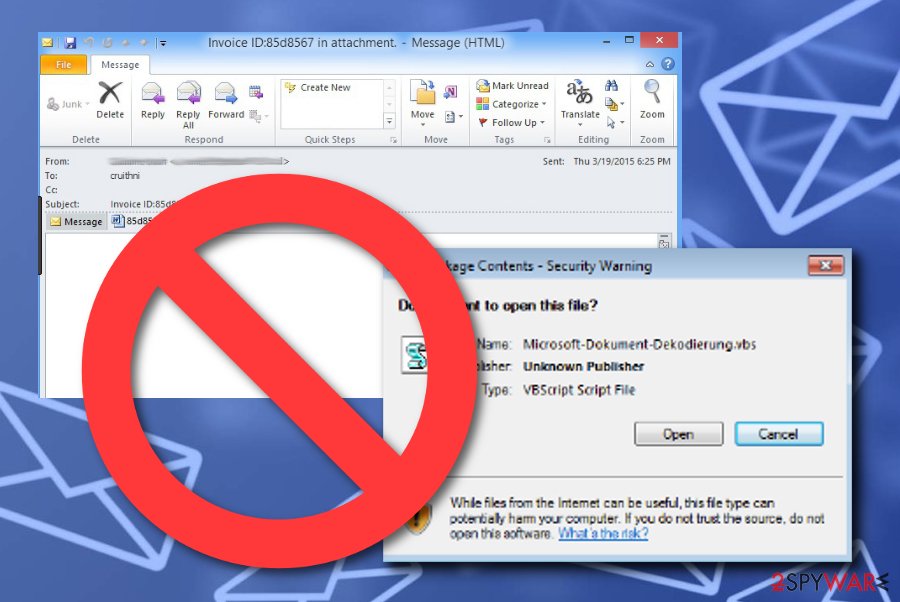
Dridex virus is malware used to steal data, access sensitive information, or perform secondary attacks on the already infected machines. Developers of the Trojan use spam campaigns to spread the infection and disguise it as UPS delivery company or other services, so people open those emails without thinking twice. As soon as the attachment is opened, malware begins its infection routine, which impacts various system files and settings.
During the active years of this Trojan, criminals use many names of different companies to mimic their billing emails and other notifications, so malware scripts are launched without direct installs. The last activity of Dridex was noticed in April 2020 when FedEx-themed malspam campaigns were surfacing.
Dridex, also recognized as Bugat or Cridex,[1] is a notorious piece of software that aims to steal banking details and track keystrokes of Windows users. Up to now, no campaigns targeting macOS were detected, but it might be possible in the future. Date stolen by Dridex Trojan might be used or transferring money from victims' accounts, which results in huge monetary losses.
Also, the malicious payload gets dropped using compromised FTP websites and hyperlinks added on those emails directly or included on Microsoft documents as rerouting links. Unfortunately, it is extremely easy to trigger the install of this virus because a few clicks on the screen launches the macro malware drop.
| Name | Dridex |
|---|---|
| Type | Malware |
| Modules | Trojan, worm, keylogger, botnet |
| Other names | Bugat, Cridex |
| Target | Windows users |
| Distribution | Infectious Microsoft Windows or Excel documents, infected websites |
| Aim | To steal banking data and perform illegitimate money transfers, inject scripts, and obtain sensitive information like passwords and logins. The malware poses as UPS, FedEx, or another service to fake the legitimacy of malware-laden emails |
| Detected as | Win32:Trojan-gen, Trojan.GenericKD.41400500, Trojan.GenericKD.41400500 (B), Trojan.TR/AD.Dridex.nbtoz, Trojan.Packed2.41796 |
| Active since | 2014 |
| Elimination | Dridex malware removal process can be easier if you choose the proper AV tools and run the full system scan, so all the intruder get deleted |
| Repair | You can download and install software such as FortectIntego to find all traces of the virus and affected files or corrupted programs. These PC optimization applications can help and fix damaged data on the system |
Dridex malware aims to operate in more than just one way on the infected computer system. Security experts have discovered that this notorious virus is capable of recording the victim's keystrokes and has gained the name of keylogger.[2] Tracking users key presses can relate to different types of illegitimate and dangerous activities.
For example, criminals who distribute Dridex banking trojan can use its key-logging feature for spying on sensitive login details, various account passwords, personal information, and the same credentials that we have talked about before. Collection of such data might relate not only in monetary losses but also to serious identity theft.
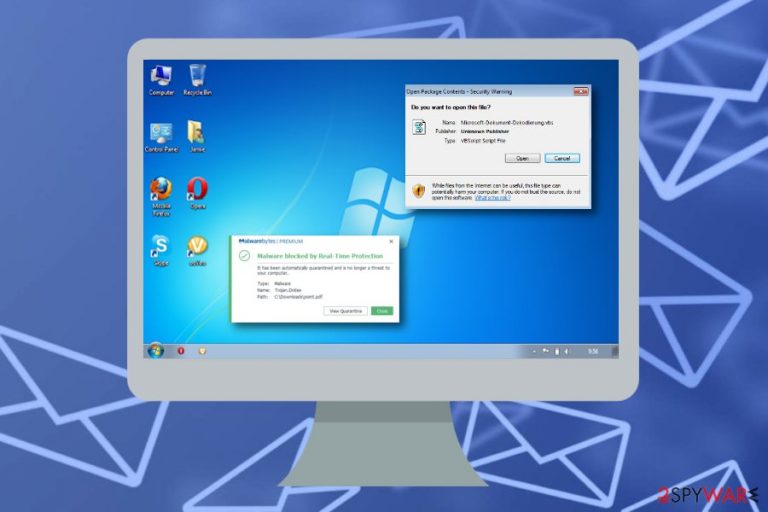
The antivirus avoidance feature is also the one belonging to Dridex trojan. Reports say that this malware might be hard to detect as it is good at hiding. However, some well-known anti-malware programs are still capable of spotting strings of this cyber threat and it can be found in these types of names:[3]
- Win32:Trojan-gen.
- Trojan.GenericKD.41400500.
- Trojan.GenericKD.41400500 (B).
- Trojan.TR/AD.Dridex.nbtoz.
- Trojan.Packed2.41796.
Note that instant Dridex malware removal is a necessity once your anti-malware detects such threat names. Also, you can try using a program such as FortectIntego for searching for malware strings. It is very important to react fast as this trojan can inject other dangerous infections remotely and cause severe damage to your computer. This tactic is known as “injection attack”.

Nevertheless, Dridex is capable of disabling Windows Script Host objects by using the Application Whitelisting tool and its WMIC vulnerability. Additionally, this dangerous form of computer virus brings infectious VBS content to the system which is carried through XLS-based scripts. As you can see, it is very important to take quick actions after spotting the first signs of malware. Performing Dridex removal should be your first priority now.
There are many more activities that the virus might be capable of but they might not be identified yet. For example, Trojan viruses often overuse CPU and GPU power which causes regular system crashes. They also might end up placing infectious processes and files all over the system. So, remove Dridex and avoid possible computer and software corruption.
The name of Dridex has been known since 2014
Dridex has become a notorious celebrity already in 2014 when countless corporate users worldwide reported their stolen passwords of bank accounts. As a result, they suffered huge financial losses. Due to the complex and exquisite structure as well as distribution methods, the malware has succeeded in causing the entire chaos in the IT world.
Dridex virus techniques helped it to stand its ground among other aggressive computer threats and remain invincible. While the malware mainly targeted North America and Western Europe, now it moves further east. The Baltic states are the next target of this malware. Ordinary users are likely to become victims as well.
Talking about nowadays, the year of 2019, there were numerous reports coming out that Dridex has been avoiding antivirus detection and infecting computer systems worldwide without big effort. Nevertheless, experts revealed that the malware has expanded its distribution plot from email spam to misleading FTP pages.[4]
Information on other characteristics of the malware
Alternatively known as Worm.Win32.Cridex or Cridex, the threat is able to steal log-in data and passwords by making several significant modifications in the browser. Since it operates both, as a trojan and as a computer worm, it managed to escape detection of a security program in the past. Regarding its characteristics of a worm, it might infect a system via a link encountered in the file-sharing domain.
Once Dridex malware successfully settles on the computer, its trojan features get activated. Likewise, the malware meddles with your browser settings by redirecting you to the fake version of your bank instead of leading to the original site. As a result, it is able to track and record all your passwords and spy on your activity by taking secret screenshots of your computer screen.
Moreover, when Dridex botnet takes control of the device, you might notice occasional system errors and notifications to reboot the system. When the required information is collected, it is transferred to hidden hackers‘ servers. As a result, victims might suffer financial losses overnight or within a couple of hours.
The main goal of the virus is to steal sensitive information related to bank accounts, si fraudulent transactions to criminal-belonging accounts can be made. Stealing money is the most common aim of various malware creators. This Dridex trojan can also operate as a key logger and record keystrokes on sites where logins and passwords. This malware can also perform injection attacks during which remote commands can be executed on code injected into specific programs. 
The operation and transmission techniques of Dridex malware
Its distribution and operation ways are worth mentioning as they assisted the malware in to remain active for such a long time. The first signs of Dridex banking trojan were already spotted in 2014. Due to the botnet (the network of machines and devices which manage the distribution of the malware), the malware successfully infiltrated thousands of computers.
Ordinary users may not be familiar with Dridex as it mainly targeted banks and financial institutions. Its success also lies in spreading the menace via macros embedded in spam messages. In order for victims to activate the threat, the hackers label the emails as invoices or financial report files. If the targeted operating system automatically enables the macros, the malware sets out to perform its misdeed.
After the infiltration, the malware causes real havoc: it creates backdoors to secretly install other malignant files. Moreover, the malware has joined forces with multiple ransomware developers. It has been observed that such a virus as Bart also facilitated the distribution of Dridex and Locky ransomware.[5] That is how this dangerous malware has also earned the name of the ransomware.
malware creates campaigns and delivers emails stating about invoices, billing information, or bookings. Notifications mainly include links or Microsoft documents with information supposedly sent from services like UPS or FedEx. Enabling content buttons launches malicious macros automatically.
Some examples of Dridex malware distributing emails:
Subject: Invoice Due #7300980
Good morning,
Attached is the invoice for the work completed at your property. Payment should be remitted to the invoice below. We appreciate your business.
For security reason the invoice is password protected: 159
Should you have any questions, please do not hesitate to contact us.
Jess Tiffani RSW, CCAC, ICADC, CEC
Director
Pegasus Recovery Solutions
m: 250.514.1083
f: 250.294.6850
a: 270 – 2950 Douglas St, Victoria BC, V8T 4N4
w: www[.]pegasusrecoverysolutions[.]com
e: Jess.Tiffani@pegasusrecoverysolutions.com
Subject: FedEx Billing – Invoice Ready for Payment
You have a FedEx invoice ready for payment.
Your invoice is ready for payment
Dear Customer
Your account has a new invoice(s) from FedEx ready for payment.
Invoice number: Invoice amount:
9-053-76763 180.82Thank you for your business,
FedEx
Ensuring proper cybersecurity is a crucial step to take
Security experts from LosVirus.es[6] warn users that taking recommended precautionary measures should be a crucial step for each person that uses a computer, laptop, or similar device. Malicious infections are ready to sneak into the system through different types of ways such as email spam campaigns, infected networks, malicious links, fake software updates, etc.
Talking about spam emails, the malicious payload will supposedly come inserted into a Microsoft Word document or into an EXE file. If you ever find such components clipped to an email, use a reputable anti-malware program to scan the entire content and identify rather it is harmful or safe to open.
Continuously, you should always have trustworthy antivirus protection working along your side while completing browsing work. Try avoiding all rogue-looking networks as they supposedly lack protection. These types of websites usually appear to be based on piracy, gambling, online gaming, or porn-watching.
Dridex malware termination steps
Trojans and computer worms are surely highly destructive and frustrating viruses. In order to remove Dridex virus completely, update your anti-virus, and install an additional security application, such as SpyHunter 5Combo Cleaner or Malwarebytes. The anti-spyware software is specifically created to confront such malware as this banking trojan.
In addition, it will help you block other samples of this category as well as ransomware threats. Manual Dridex removal is not recommended as detecting its executables might be a futile activity. Your cautiousness also plays a great role in increasing cybersecurity. However, what you can do on your own is rebooting your computer to Safe Mode or performing a System Restore.
These two below-provided features allow disabling malicious processes that might be ongoing on your machine and reversing previous changes that were made during the activation period of Dridex malware. However, do not feel too relaxed after the cyber threat vanishes as you need to ALWAYS follow security recommendations if you want to keep your device/machine protected from hazardous infections. Remember to double-check and install FortectIntegofor virus damage repair purposes before running the AV tool or after the proper malware removal.
Getting rid of Dridex virus. Follow these steps
Manual removal using Safe Mode
Use these instructing steps to reboot your machine to Safe Mode with Networking and disable malicious processes:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Dridex using System Restore
Reverse all suspicious changes that were done to your computer by Dridex malware. Reboot your machine with System Restore:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Dridex. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Dridex and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting keyloggers
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Dridex. Wikipedia. The free encyclopedia.
- ^ Margaret Rouse. Keylogger (keystroke logger or system monitor). Search Security. Tech Target.
- ^ 48 engines detected this file. Virus Total. Malware indentification.
- ^ Charlie Osborne. New Dridex malware strain avoids antivirus software detection. ZDNet. News articles.
- ^ Dridex Malware Has Evolved To Locky Ransomware. Alert Logic. Seamless Threat Management.
- ^ LosVirus.es. LosVirus. Spyware and security news source.







