Locky ransomware (Removal Instructions) - Aug 2017 update
Locky virus Removal Guide
What is Locky ransomware?
Locky ransomware makes a comeback in August 2017

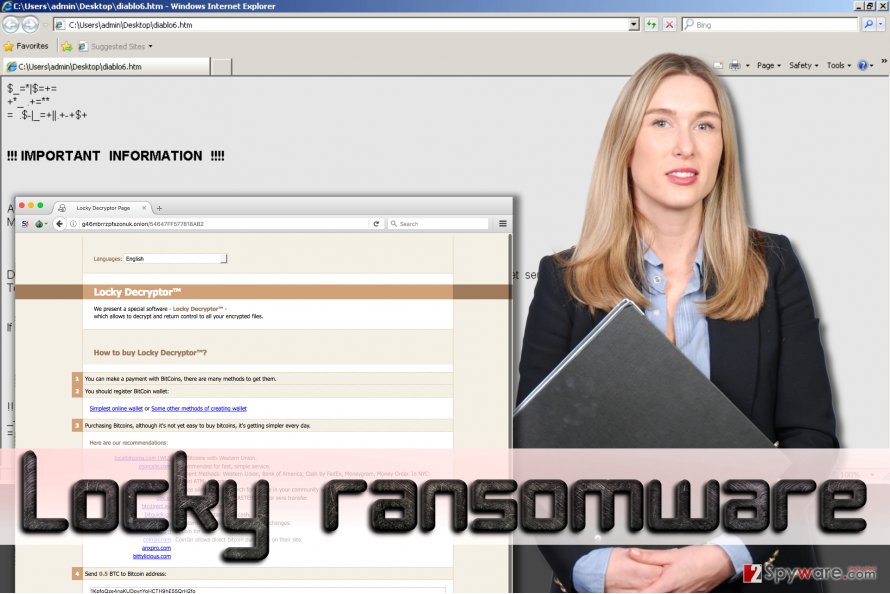
Locky virus is a dreadful data-encrypting parasite which managed to dangerously proliferate and infect thousands of computers since its first appearance at the beginning of 2016. Convinced by the success of the initial virus version, authors of this crypto-ransomware have created more differently named versions of it – Diablo6, Osiris, Aesir, Bart or Zepto virus.
These viruses pose a serious threat to the computer system because Locky encryption algorithm can corrupt files not only on the compromised computer system and devices plugged into it, but also data on unmapped network shares. The reason why this virus encrypts victim's data is that it wants to receive a ransom payment, and this is why this virus is known as Locky ransomware.
After infecting the system, this Trojan-type pest uses an embedded encryption key (earlier, this ransomware used to connect to its Command & Control servers to get this key), then scans all system folders for particular file types and encrypts them with military-grade encryption, which securely detains victim's files as hostages.
The virus does not only encrypt files but also changes their filenames and adds .locky file extensions to them; this way, the virus seeks to confuse the victim and make it harder to decrypt particular data. If you are looking at suspicious file extensions added to your data, you are infected with this ransomware which will keep your files blocked until you pay a ransom.
To explain to the victim how to pay the ransom, the virus creates a ransom note called _Locky_recover_instructions.txt and saves a copy of it in every single folder that holds encrypted data. The ransom note contains the following message:
! ! ! IMPORTANT INFORMATION ! ! !
All of your files are encrypted with RSA-2048 and AES-128 ciphers.
More information about the RSA and AES can be found here:
[links to Wikipedia]
Decrypting of your files is only possible with the private key and decrypt program, which is on our secret server.
To receive your private key follow one of the links:
[links to .onion sites accessible via Tor browser]
If all of this addresses are not available, follow these steps:
[Instructions how to install Tor browser]
! ! ! Your personal identification ID: [ID number] ! ! !
After that, virus changes desktop background with a _Locky_recover_instructions.bmp image, which displays the same information as the ransom note provides. The .onion links presented in both these files left by the virus lead to Locky payment website, which offers the Locker Decrypter for 0.5 or 1.0 BTC, (approximately 300-600 USD dollars at the time of writing this report).
You might think, “why I have to pay when I can use Volume Shadow Copies to restore my data?” Well, we have to disappoint you by saying that the virus runs the following function – vssadmin.exe Delete Shadows /All /Quiet , which carries out elimination of these copies. Therefore, there is no way to recover your precious files from these copies.
On top of that, malware researchers still cannot crack virus' source code and defeat this virus by creating a free Locky ransomware decryptor, so affected PC users have two options only:
- Let crooks win and pay the ransom to them;
- Refuse to pay the ransom and restore them from backup or wait until a decryption tool gets released.
If you decide to pay the ransom, you should note that security experts do NOT recommend doing so as there is no guarantee that hackers actually give their victims a key that they need. In this case, you have to remove Locky ransomware from your computer. You can use FortectIntego for that.
Update August 15, 2017. As summer 2017 draws to a close, Locky's developers presented their latest creation – Diablo6 ransomware virus. A relatively quiet summer season is usually known as a “holiday season” for cyber criminals; however, it seems that this doesn't apply for Locky's cybercrime gang. The malware developers are actively pushing this upgraded ransomware variant that uses .diablo6 file extension to mark victim's files once they're encoded.
The new ransomware wave was first noticed on August 9th, with a small test campaign the day before it. This time, virus' developers rely on spam again – they distribute the virus via email. The first spam campaign used archived VBS files to compromise victims' computers.
Criminals distributed emails with such subject lines -E [date] (random numbers).docx. The attachment inside the email is named identically, except that its file format is different – it is a ZIP file. The archived file contains a VBS file that works as a ransomware downloader.
The second campaign used malicious DOCM files disguised as PDF files. Criminals distributed emails with such subject lines – IMG_[random digits].PDF. The PDF file contains an embedded DOCM file with malicious Macro code. If the victim enables documents' contents, the code activates and connects to a remote domain to download the virus from it.
Opening these files guarantees instant data loss as the Diablo6 virus hidden in remote servers gets downloaded to the system by the malicious VBS or DOCM file instantly.
The main Locky's attack vector
This computer threat spreads as a malicious Word document attached to spam emails that pretend to be delivering an invoice:
Dear [Name],
Please see the attached invoice (Microsoft Word Document) and remit payment according to the terms listed at the bottom of the invoice.
Let us know if you have any questions.
We greatly appreciate your business!
[Randomly generated name of the sender]
This email contains an attachment, which is named invoice J-[8 random numbers].doc. If the user opens this file using Word, Locky malware might start its malicious processes right away. It all depends on whether the user has Macros function enabled in Word or not.
If user does not have Macros turned on, Locky's document showcases a distorted text and then it asks to enable Macros to review it – “Enable macro if the data encoding is incorrect.” You should NOT do as commanded! If the user enables Macros, a malicious code gets activated.
It downloads and runs an executive file of Locky virus, which immediately starts file encryption process. The ransomware runs its processes that scan system for personal files, including audio, video, image files, documents, and locks them using RSA-2048 and AES-128 encryption algorithms.
What is more, this virus can access and encrypt data stored on external drives that are plugged into your device. After the encryption process is done, this virus renames the affected files – it adds a .locky extension to the filenames.
Recently, authors of Locky and Zepto created a new crafty technique to deceive anti-virus programs from detecting the source of infection and allowing the virus to freely encrypt all files without being stopped. For that, the virus is distributed via an archived JavaScript attachment, aka downloader script.
Once executed, it downloads and decrypts malicious payload which arrives in the form of DLL file. This file is run with the help of rundll32.exe file. Typical antivirus programs consider the rundll32.exe file as safe one, so Locky and Zepto easily passes computer protection and steps into the system to wreak havoc there.
We also must add that people who tend to keep their computers unprotected risk to be attacked by JS.Nemucod Trojan horse, which can remain silently in the system for a while and then drop malware on the system. This Trojan horse is well-known conspirator involved in Locky's distribution scheme.
Locky ransomware variations
Locky virus. The first version of the malware has been spotted at the beginning of 2016. Since then it was updated several times, and now it is responsible for 50% of recognized ransomware attacks. The virus drops a three (some versions leaves two) files that include a ransom note. Hackers launched malicious email campaigns and spread infected Word documents.
When users activated macro command, virus infiltrated the system and encrypted files using AES-128 and RSA-2048 algorithms. Then it dropped a ransom note _Locky_recover_instructions.txt to each folder that stores encrypted files. The ransom note includes information about data encryption and decryption. Hackers explain that paying the ransom (0.5-1 BTC) is the only possibility to decrypt files.
Ransom note also provides information how to purchase Bitcoins, install Tor browser and use Locky Decrypter – a tool which is supposed to restore all damaged files. Unfortunately, malware researchers haven’t created a free data decryption tool yet. However, we do not recommend using any data recovery solution suggested by the criminals. At the moment the only safe and free solution is to restore files from backups.
AutoLocky virus. Oppositely from Locky, AutoLocky was written not in C++ but in Autolt language; and this made malware the weakest version. Malware spreads via malicious spam emails.
Hackers attach an infected PDF file, and when users open it, the virus gets inside and starts encrypting files using the AES-128 cipher. It demands 0.75 Bitcoins for data recovery, but it’s not necessary. There’s a free AutoLocky decryption tool.
.locky file extension virus. Similarly to other malware variants, it encodes files using RSA-2048 and AES-128 ciphers and appends a .locky file extension to all corrupted documents, pictures, audio, video and other files. Following data encryption, it drops a ransom note where hackers demand 0.5 Bitcoins.
Unfortunately, malware researchers haven’t created a free decryption tool yet, but it’s not the reason to pay the ransom. If you have data backups, you can restore files after virus elimination. Another bad news is that .locky file extension virus has been updated in June 2016.
The newest version is called Diablo6 virus. For possibility to decrypt files with Locky Decryptor, criminals ask for 0.5 BTC . Please, do not transfer this enormous amount of money, because there’s no guarantee that this tool will decrypts your files.
Bart virus. Instead of encrypting files with a sophisticated algorithm, this version of Locky virus adds files into a password-protected ZIP archive. All archives have .bart file extensions and only Bart Decryptor can retrieve damaged files for 3 BTC. The payment website offers translation to several languages and looks similar to Locky’s. The virus has another unique characteristic.
Before data encryption, it checks computer’s default language settings. If targeted computer’s language is Russian, Ukrainian or Belorussian, malware uninstalls itself. Malware researchers have created a free decryption tool and this fact motivated hackers to update the virus.
They have developed a Bart v2.0 ransomware virus that still adds targeted files to ZIP archive, but appends .bart2 extension to each of them. Unfortunately, this version is still undecryptable, unless you are willing to pay about 2 BTC for cyber criminals (NOT recommended).
ODIN virus. For data encryption virus use the same encryption method, but appends different file extension – .odin. The virus mostly targets Europe, but computers in Asia, Africa, and the USA suffered from it as well. The virus spreads via malicious email attachments.
It’s already known that some emails have a subject line “Receipt [random numbers]”; however, there’re hundreds of different infected emails. After successful file encryption, it drops a ransom note and tells that the only possibility to get back access to the files is to pay the ransom.
Thor virus. This variant appeared on October 2016.It encrypts for more than 400 different file extensions and encodes them using RSA and AES encryption. Following a successful file encryption, virus delivers two files _WHAT_is.html and _WHAT_is.bmp. These files include so-called ransom messages and explain to victims that they can restore their files using Locky Decryptor for 0.5 Bitcoins.
Shit virus. At the same time when Thor launched its first campaigns, computer users from France reported that their files were corrupted and had a .shit file extension. For file encryption virus uses a military grade AES CBC 256-bit encryption and, unfortunately, there’s no way to decrypt them for free.
The virus leaves the same ransom note and demands the same amount of money like Thor. Unfortunately, victims can restore their files for free only from backups.
Hucky virus. It’s a Hungarian version of the Locky which appends a .locky file extension to all affected files. It can only encrypt around 200 different file types. The virus uses an updated version of the _locky_recover_instructions.txt, and after file encryption malware drops a _Adatok_visszaallitasahoz_utasitasok.txt.
In this ransom message, victims learn that they have only 24 hours to contact cyber criminals via provided email. Hackers do not reveal the size of the ransom, but it might vary from 0.5 to 2 BTC.
Diablo6 virus. Diablo6 ransomware emerged in August 2017. The virus wreaks havoc on the computer system, turning all files into useless pieces and adding .diablo6 file extension to them. After a successful data encryption, malicious software drops diablo6.htm and diablo6.bmp files.
One of these is set as desktop's background, and the other one opens a message from cyber criminals. As usual, the victim gets instructions on how to access a payment site via Tor network and learns that files can be decrypted for a ransom worth half a Bitcoin.
The new Locky version is currently being pushed via two spam campaigns. One of them delivers a malicious ZIP attachment with a VBS file into it, and the other spreads malicious PDF files with embedded DOCM documents in them. The victim can get easily convinced to open these attachments because scammers spoof sender's email to make it appear legitimate.
Besides, the message body usually contains no suspicious details. The criminals may leave a short note such as “Files attached. Thanks.” Opening attachments of such email can completely compromise your computer and make you lose your files for good.
Steps to take if the system gets compromised by Locky virus
Speaking of ransomware, it is always better to secure yourself before it attacks you. No matter how attentive and careful computer user you are, you can still be deceived by cyber-criminals, because they tend to spread malware like Trojan horses. In other words, malware comes as a safe-looking file that is infected. We strongly recommend to regularly create copies of your data and store them on an external hard drive.
Unfortunately, Locky is a disastrous virus, which can lock your personal files forever. As we have mentioned, you should not think that it lets its victims recover their files from Shadow Copies because this noxious virus simply deletes them.
Therefore, the only 100% working method to recover your files is to import them from an external drive. However, you must eliminate Locky malware before you do so, because as we have already stated before, it can encrypt records stored on external drives that are plugged into the infected machine, too.
If you do not have copies of your files xeroxed on an external drive, you have three options left:
- You can try to use one of these tools (they might help you to decrypt at least some of your files): Kaspersky virus-fighting utilities, R-Studio or Photorec;
- You can wait until someone creates a Locky decryption tool (this might take a long time);
- The last option is to pay the ransom, but we DO NOT recommend doing so. Not surprisingly, there is NO guarantee that cyber-criminals will give the decryption key for you. Plus, think about it – do you want to support cyber-criminals in such way?
To implement Locky removal, we recommend using one of the following anti-malware programs: FortectIntego (Windows OS) or Malwarebytes (Windows/Mac OS). Alternatively, you can try SpyHunter 5Combo Cleaner software. These three programs are professional malware removal tools that can completely terminate the virus.
NOTE. Anti-malware programs DO NOT decrypt the encrypted data. They are meant to eliminate malicious programs and their components.
Avoid ransomware by following these rules:
- Keep your computer security software up-to-date. Update it as soon as the new version is available;
- Protect your PC with anti-malware software and make sure Windows Firewall is always turned on;
- Back up your files. We do not recommend using online data storage clouds because some viruses can reach them using your Internet connection;
- Do not wander through 'Spam' or 'Junk' email sections and make sure you do not open any suspicious emails or attachments that come with them;
- Update software frequently – make sure Java, Adobe Flash Player or other programs are up-to-date.
Expert tips on Locky virus removal
Before you try to remove Locky virus from your computer, you have to realize that you are dealing with a seriously dangerous virus. To remove this virus entirely, you have to get rid of each of its files because it can easily come back to your computer and encrypt NEW files right after rebooting it.
If you are looking for a reliable Locky ransomware removal tool, we recommend you to choose FortectIntego or Malwarebytes. However, the virus can attempt to block these programs, so in order to launch them, or if you do not have one of these yet – download them, you have to reboot your PC into the Safe Mode first.
Please look at instructions provided below and carry them out carefully to run the malware removal program and complete Locky removal procedure.
Getting rid of Locky virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Locky using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Locky. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Locky from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Unfortunately, .locky file extension files can be recovered only with the help of the unique decryption key that is securely held by cyber criminals. If you are not willing to pay money for your own files, or simply if you do not want to give away your money for filthy scammers, you DO make the right choice.
We always encourage users not to pay up, because first of all, no one gives any guarantees that the decryption tool offered by criminals actually works, second, it might arrive in a package together with more malicious files. To recover your records, please use backup drives.
If you haven't created a data backup back in the day, then you can try to search for healthy files to replace the encrypted ones by looking through your USBs, files sent via social media or emails, CDs or DVDs. Make sure that you delete the virus first before trying to recover your files!
Otherwise, it will encrypt files in the data storage device as soon as you plug it in or encode files that you download to your computer system from the Internet.
If your files are encrypted by Locky, you can use several methods to restore them:
Use Data Recovery Pro service
To recover your files, you can try this tool – Data Recovery Pro. Although there is no guarantee, it might help you to restore the encrypted data.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Locky ransomware;
- Restore them.
Use Windows Previous Versions feature
If your files have been corrupted by this filthy ransomware, you might want to restore some individual files. You can try to do that by carrying out the following commands:
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Locky and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.







