DXXD ransomware / virus (Improved Guide) - Oct 2016 update
DXXD virus Removal Guide
What is DXXD ransomware virus?
An overview of the DXXD ransomware:
It seems that hackers own some kind of ransomware manufacturing machine as they have recently struck the Internet users with yet another malicious creation – DXXD virus. As it is still a newbie, it is too early to decide what or who are the primary targets of this ransomware. Regarding the ransom note that this virus presents for its victims, one might suspect that it has connections with the recently swept-by restore@protomail.com and Fantom ransomware. In case you visited our website looking for a solution to remove DXXD virus, rest assured. We provide all the necessary instructions below this article. While you are getting accustomed to the operation ways of this ransomware, start DXXD removal by employing FortectIntego anti-malware.
Observing the current trends in the ransomware world, it is obvious that while some hackers concentrate on developing an invincible threat, others are more keen on showing off. This ransom may not give such ambiguous impressions as Cyber_baba@aol.com or Nagini ransomware. Certainly, the ransom note left by this virus does not leave an impression of refinement. The hacker makes fun of his victims by apologizing for the encrypted files. However, this poor play and disguise do not diminish the danger level of this file-encrypting malware. DXXD ransomware does not deviate from using ordinary encryption techniques.
However, it has one exceptional feature. While other viruses often leave their mark on the infected computer by appending an extension; the current malware leaves a bit different autograph. Let us take an example when notorious Locky first emerged; the virus marked the encrypted data by attaching the .locked extension. In this case, the corrupted files bear dxxd extension pinned after the original one. So, the infected computer file may look something like this: “randomfilename.jpgdxxd.”
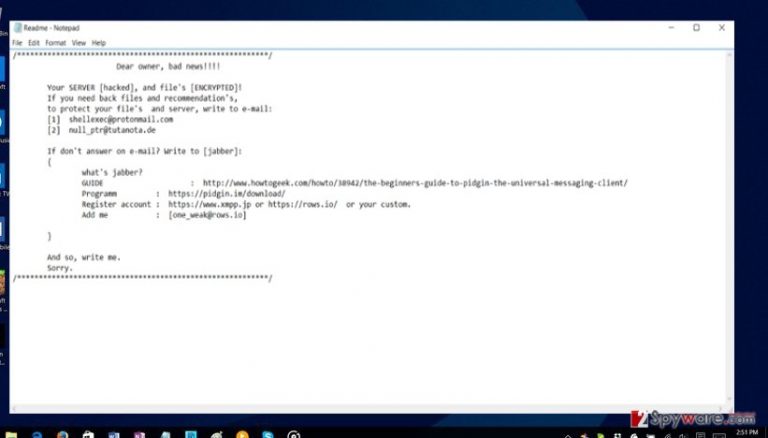
Moreover, dxxd extension virus does not indicate the fixed amount of ransom in its ransom note that it drops on the computer after the data encryption. Instead, the ReadMe.txt document only features a couple of email addresses that the victims must contact in order to recover their files. Likewise, the current version of the file-encrypting malware might be just a test version before the grand improved edition will emerge. The .txt file contains brief instructions how to use a chat room. Besides such mocking notes, the ransomware provides two main email addresses: shellexec@protonmail.com and null_ptr@tutanota.de.
October 2016 update: Ransomware developers publicly announce having upgraded DXXD ransomware
Malware developers have joined DXXD support forums to announce that they are working on a more complex version of the virus. They claim having made the new version even more difficult to decrypt. Besides, they also seem to have changed their ways of hacking into servers. Now, the virus brute forces passwords using Remote Desktop Services. So, if your PC has already been infected with this ransomware, please change your Windows login details and other passwords on your computer.
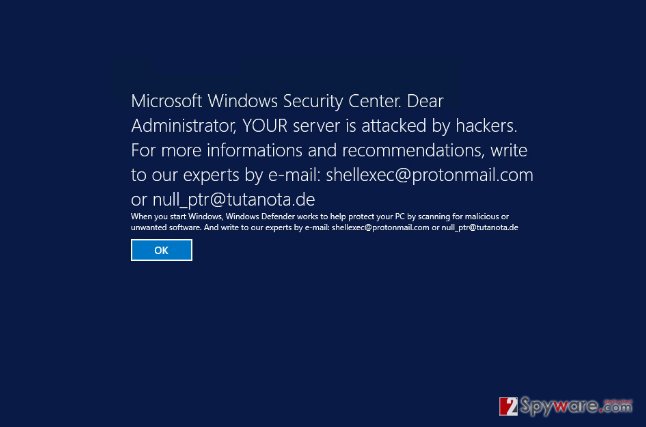
Another new feature that the virus developers have decided to integrate is the lock screen. The virus alters Windows Registry entries to display a notification screen whenever you try to log into your computer. The lock screen imitates a BSOD notification, announcing that the computer has been attacked by hackers and Microsoft Windows Security Center urges the administrator of the device to contact the provided emails. These emails are the same ones as provided in the ransom note, so it leaves us no doubt that this Legal Notice is fake. An example of this notification is presented below:
How the hackers distribute this parasite?
DXXD ransomware might employ several and intriguing forms of transmission to carry out its malicious mission. As it is common with the majority of ransomware threats, they attack users via elaborate spam messages which come as fake financial and package delivery reports. Regarding DXXD malware, it is suspected to spread via malware which generates fake messages which are seemingly issued by Windows Security Center. The ransom note is accompanied by additional alert informing about the hacked server. In any case, IT experts warn users to be very vigilant when reviewing spam folder. It would be best to ignore such emails even if they address you personally. Similar emails may contain infected links or scripts with ransomware executables. In order to decrease the number of such emails, install a powerful malware removal utility.
Is there a way to terminate the ransomware and recover the data?
First of all, DXXD removal should be performed. In this regard, do not waste time and switch to automatic elimination. Install a security application, for example, FortectIntego or Malwarebytes, and update it. The overall termination procedure does not require much of your time. If you struggle to remove DXXD virus because the essential computer functions fail to respond, feel free to employ our access recovery guide. Below it, you will also locate advice on data recovery.
Getting rid of DXXD virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove DXXD using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of DXXD. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove DXXD from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by DXXD, you can use several methods to restore them:
How useful is Data Recovery Pro?
Though there are not many guarantees that the software will succeed in encrypting or recovering all of your files, you might give it a try. The best way would be to recover the files using back-ups or acquire the original decrypter.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by DXXD ransomware;
- Restore them.
Opting for System Recovery
By enabling this function, you will acquire a valuable thing – time. Since the operating system is reverted to the previous state, you might find your files unaffected by the ransomware. But be quick! The ransomware might be on its way to locking your files again.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow Explorer: does it help?
It is extremely practical in case ransomware does not delete volume shadow copies if your files first. Luckily, not all file-encrypting malware bear this feature. In relation to this, it is not known whether DXXD tends to so as well. Thus, you might have one more chance to retrieve valuable documents.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from DXXD and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.







