Fantom ransomware / virus (Removal Guide) - Jul 2017 update
Fantom virus Removal Guide
What is Fantom ransomware virus?
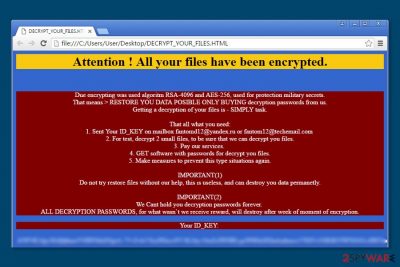
Fantom ransomware warns: attention, all files on your computer are encrypted
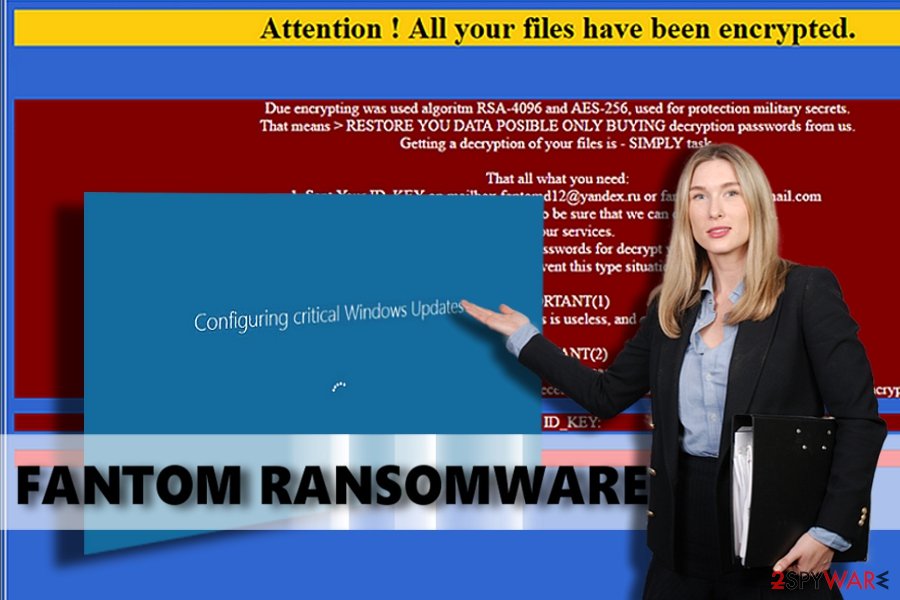
Fantom is a crypto-malware that emerged at the end of summer 2016. In the affected machine it shows fake Configuring critical Windows Updates screen[1] while it encrypts files using a combination of RSA-4096[2] and AES-256[3] ciphers. Malware has several variants that might append one of these file extensions:
- .fantom,
- .locked,
- .locked4,
- .11232323.
Following data encryption, the virus then leaves DECRYPT_YOUR_FILES.HTML ransom note which starts with a line Attention! All your files have been encrypted. You can stop this unwanted process initiated behind your back with the help of Ctrl + F4 combination.
Different variants of malware might use slightly different ransom-demanding text. However, the main message remains the same – people have to pay the money in order to get back access to their files. Fantom virus might also change the desktop picture with the threatening message:
Attention! All your files have been encrypted.
Due encrypting was used algorithm RSA-4096 and AES-265, used for protection military secrets.
That means RESTORE YOU DATA POSIBLE ONLY BUYING decryption passwords from us.
Getting a decryption of your files is – SIMPLY task.
That all what you need:
1. Send Your ID_KEY on mailbox.
2. For test, decrypt 2 small files, to be sure that we can decrypt you files.
3. Pay for our services.
4. GET software with passwords for decrypt you files.
5. Make measures to prevent this type situations again.
IMPORTANT(1)
Do not try restore files without our help, this is useless, and can destroy you data permanently.
However, the files can be recovered even after the removal of our program and even after reinstalling the operating system.
[…]
According to the ransom note, the malware uses encryption systems which can't be cracked. Also, it provides the unique key called ID_KEY to each of its victims and asks them to contact its developers via one of these email addresses:
- fantomd12@yandex.ru,
- restorefiles@protonmail.ch,
- fantom12@techemail.com.
Unfortunately, crooks are not lying. Fantom ransomware relies on an advanced military-grade encryption system. This system relies on a public encryption key, which is used to encrypt files, and RSA encryption used to protect the first key. This key is the life saver for those who want to decrypt .fantom file extension files; however, cyber criminals are not willing to give it up for free, so you should not wait for their mercy.
The threat can set a different size of ransom according to the title of the executable. Thus, the cyber criminals gain the chance to earn different sums of profit employing the same executable. For example, if it contains a certain number, let's say, fantomv2.exe, you will be required to pay 2 Bitcoins.
In the case or ransomware attack, we would like to encourage you not to pay the ransom.[4] Files can be retrieved from a backup, but before you plug it into your PC, remove Fantom ransomware first. It helps to clean the system and prevent further possible cyber attacks.
We understand that everyone wants to keep their precious files safe and sound, and that is why we always urge users to create their copies and import them to external devices – in other words, to back them up. Data backups[5] come in handy when the original ones get corrupted, encrypted, or deleted by malware.
Security experts do not advise users to mess with ransomware viruses manually because these malicious programs are designed to hide deeply in the computer system, and they typically consist of many files. The best way to recognize and delete them all is to allow an automatic malware removal tool to do it. Fantom removal can be finished using the FortectIntego.
Quick analysis of malware operation
This ransomware operates in a rather crafty way. As we have mentioned in the first paragraph, this ransomware manages to deceive a user and pretends to be a Critical Windows Update, asking the victim not to turn off the computer. In the meantime, the ransomware rummages the compromised system, searching for predefined file types.
It scans the computer and encrypts precious memories, work files, and other important documents, leaving no chance to restore and use them. It bypasses essential system files to keep the computer running, creates a ransom note, changes desktop wallpaper, and opens the delback.bat file.
If the victim is not the administrator, a pop-up dialog will show up, asking the victim to make changes on the device. Since this message says that it comes from a verified publisher – Microsoft Windows, inexperienced victims might unknowingly click Yes. This deletes Shadow Volume Copies, which can help you to recover encrypted data.
Modifications of Fantom ransomware virus
On March 2017, malware researchers spotted a new version of ransomware.[6] The unique feature about this variant of Fantom is that after the infiltration, malware checks computer’s location. If it finds out that it ended up in Russia, it discontinues the attack. Otherwise, it starts data encryption procedure and appends a specific file extension based on the timestamp of the contamination event.
One month later, on April 2017, security community started talking about the possibility that Fantom RaaS might show up soon.[7] Researchers find an improvement in ransomware’s code that allowed assuming that authors of the ransomware are about to launch RaaS platform. However, it seems that this day hasn't come yet.
However, the same month Fantom ransomware changed its design. Virus researchers have detected a brand new version of this threat. The hackers of this peculiar malware noticed that it contains major improvements in its source code and execution manner. As a result, they lead to alternations in its veneer as well.
In contrast to previous versions, it appends a different file extension. Now all encoded files contain .11232323 file extension. Payment guidelines are also presented in a different file RESTORE-FILES.11232323.hta. Besides this file, it also loads additional two images hxxp://iplogger.ru/1qzM6.gif and hxxp://iplogger.ru/1wzM6.gif to inform about the hijacking process.
Interestingly, that the malware also locates the country of victims' residence. According to the initial report, the malware terminates itself if a victim is Russian. No major changes in its distribution process are reported.
Infiltration methods of the ransomware virus and how to avoid it
Fantom ransomware is distributed via malicious websites, emails, malware-laden ads, and other methods. There are several methods how the user can protect its computer from ransomware attacks, and the main thing that PC users should know that it is a must be careful while browsing the Internet:
- Avoid clicking on suspicious ads, links or buttons.
- Bypass clicking on ads or articles with click bait titles.
- Never open email attachments that unknown people send to you. No matter if the attachment is named as invoice, resume, phone bill, or similarly, it does not necessarily mean that it is a safe file. Vice versa – crooks tend to name malicious attachments exactly like that because their aim is to make the victim feel safe about the file and open it without even thinking about potential hazards.
- Try to avoid opening files that your computer system identifies as potentially dangerous, and keep a proper anti-malware software installed on your computer.
The safe way to remove Fantom virus from the system
You have to clean the computer from malicious files completely; otherwise, any malicious files left behind can make your system vulnerable to further ransomware attacks and cause computer malfunctions. Fantom removal must be completed using a powerful software, such as FortectIntego or Malwarebytes, that can remove viruses.
The virus might attempt to stop you from running security programs, so in such cases, follow instructions provided below. They will help to disable the virus and remove Fantom with the help of security software.
Getting rid of Fantom virus. Follow these steps
Manual removal using Safe Mode
If your scanner is blocked, try rebooting your computer to Safe Mode with Networking before a full system scan. Once you finish it, you should check your computer when in normal mode as well.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Fantom using System Restore
If you can't launch your anti-spyware, you can try System Restore method to disable the virus. However, don't forget to remove its files from the system after disabling your virus.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Fantom. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Fantom from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Please, do not support frauds by paying the ransom. Keep in mind that cyber criminals might send you a useless piece of software that cannot help to recover your files. Besides, it can be filled with malicious components allowing crooks to exploit your computer system even more. If you have lost your precious files, try recovering them from a backup or use one of the methods listed below.
If your files are encrypted by Fantom, you can use several methods to restore them:
Use Data Recovery Pro software
To recover your files, we recommend using Data Recovery Pro program. It might help you to restore your lost data. We definitely think that it is worth a try since a free and official Fantom decryption tool hasn't been released yet.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Fantom ransomware;
- Restore them.
Windows Previous Versions feature can help you to restore data
If you have a few exceptionally important documents you have to recover, we recommend using Data Recovery Pro. This program helps to retrieve individual files, besides, before you use it, remember that it can help you only in case you have enabled Windows Previous Features feature in your PC.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Fantom decrypter is not available yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Fantom and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Warning! Ransomware posing as critical Windows update. SGCyberSecurity. Singapore’s leading cyber security portal.
- ^ RSA (cryptosystem). Wikipedia, the free encyclopedia.
- ^ Advanced Encryption Standard. Wikipedia, the free encyclopedia.
- ^ Why you shouldn't pay the ransomware fee. CSO Blog. Backup and recovery.
- ^ MICHAEL MUCHMORE. The Best Online Backup Services of 2016. PCMag Reviews.
- ^ March 2017: The Month in Ransomware. Tripwire. Advanced Threat Protection & File Integrity Monitoring.
- ^ April 2017: The Month in Ransomware. Tripwire. Advanced Threat Protection & File Integrity Monitoring.





















