Hermes ransomware / virus (Virus Removal Guide) - updated May 2019
Hermes virus Removal Guide
What is Hermes ransomware virus?
Hermes ransomware is a crypto-malware used in Lazarus hacking campaigns
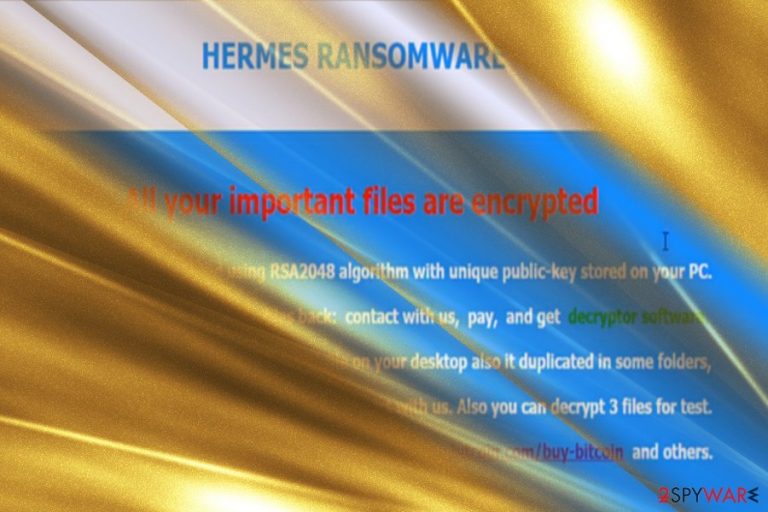
Hermes ransomware is a file locking threat[1] that was first spotted in the wild in February 2017 and is highly associated with cyber criminal[2] group Lazarus. Since its initial release, Hermes 2.0 and Hermes 2.1 variants surfaced, although all versions avoid infecting Russian, Ukrainian and Belarusian netizens.
The initial Hermes ransomware does not append an extension to the file, although it does alter its structure of the file code by attaching HERMES at the end of the string (nevertheless, later variants do mark data with .HRM extension). This process is done with the help of AES-256 and RSA-2048[3] ciphers.
As soon as Hermes locks pictures, videos, documents, databases, and other data, it drops two ransom notes – DECRYPT_INFO.txt, as well as DECRYPT_INFORMATION.html. These messages from hackers inform victims that they need to write an email to BM-2cXfK4B5W9nvci7dYxUhuHYZSmJZ9zibwH@bitmessage.ch or x2486@india.com email address to find out the redemption price, which is paid in Bitcoin or another cryptocurrency.
Additionally, users are also provided UNIQUE_ID_DO_NOT_REMOVE identicator they need to forward to the attackers. Nevertheless, the initial version of the virus is decryptable, so all users have to do is remove Hermes ransomware from their devices and then recover all the data back for free.
In 2018, researchers spotted Hermes 2.1 ransomware being spread with the help of CVE-2018-4878 Flash player vulnerability in the malspam campaigns.[4] In 2019, HermesVirus HT ransomware, which is based on Marozka virus, was found using .Hermes file extension, although these two strings are not related in any way.
| Name | Hermes |
| Type | Ransomware |
| Variants | Hermes 2.0, Hermes 2.1 |
| Hacking group | Lazarus |
| Ciphers | AES-256 and RSA-2048 |
| File extension | None |
| Related files | hermes.exe, reload.exe, system_.bat, shade.bat, shade.vbs |
| Ransom note | DECRYPT_INFO.txt, DECRYPT_INFORMATION.html |
| Contact | BM-2cXfK4B5W9nvci7dYxUhuHYZSmJZ9zibwH@bitmessage.ch, x2486@india.com |
| Decryptable? | Yes. Use decryptor [download link] developed by Michael Gillespie |
| Removal | Employ security software such as FortectIntego or SpyHunter 5Combo Cleaner |
Besides using exploits, Hermes ransomware can be delivered using the following tactics:
- Spam emails;
- Fake updates;
- Hacked sites;
- Web injects;
- Brute-forcing;
- Software cracks, etc.
Interestingly, specialists have unraveled evidence suggesting that the malware might have originated from North Korea. The infamous hackers' group Lazarus[5], associated with this country, is said to have exploited the ransomware to hide tracks of the attack on Far Eastern International Bank (FEIB) located in Taiwan.[6]
If hijack process is successful, Hermes virus encodes data on the computer using encryption algorithms – the procedure lasts only a few minutes. As a result, all affected data becomes inaccessible to the owners, and the only way to retrieve files is by employ specific decryption tools developed by hackers.
However, many computer users are used to computer slowdowns and do not pay attention to them unless they last for a very long time. Once the virus finished its dirty work, it puts some information in a .html file called DECRYPT_INFORMATION.html and also creates a UNIQUE_ID_DO_NOT_REMOVE file on the desktop.
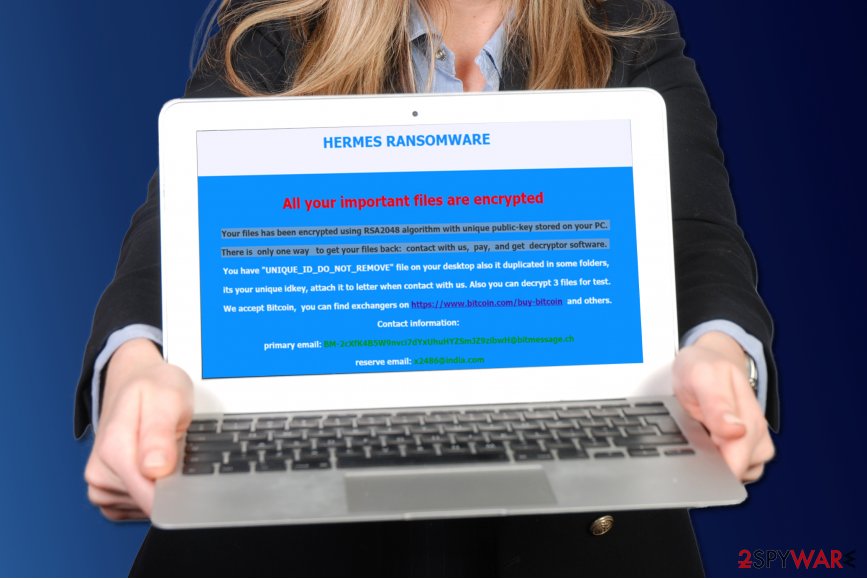
Fraudsters say that the victim can test the decryption tool by sending three files as well as unique victim's ID to criminals via email provided in the ransom note – x2486@india.com. If you have been attacked by this particular Hermes ransomware, please do not panic and wait until malware analysts analyze the sample of this virus.
It turns out that this ransomware has a flaw that allows to find out what the decryption key is, based on the encryption key. Cybersecurity researcher Michael Gillespie managed to create an official decryption tool, allowing to recover all the locked files for free. Please refer to the bottom section of this article for more details.
Before you proceed with file recovery, you need to make sure that Hermes ransomware removal is performed successfully. To do that, enter Safe Mode with Networking and perform a full system scan with the help of the anti-malware program, such as FortectIntego or SpyHunter 5Combo Cleaner.
Other variations
Hermes 2.0 ransomware was released in April. It employs RSA-2048 cipher to encode data. After the process is finished, it launches DECRYPT_INFORMATION.html file which displays the message that all users data has been encoded. In order to retrieve the files, they are urged to pay the ransom in bitcoins and acquire Hermes 2.0 decryptor software. It also provides two single-use email addresses for victims in case they encounter technical difficulties. This version deletes shadow volume copies.
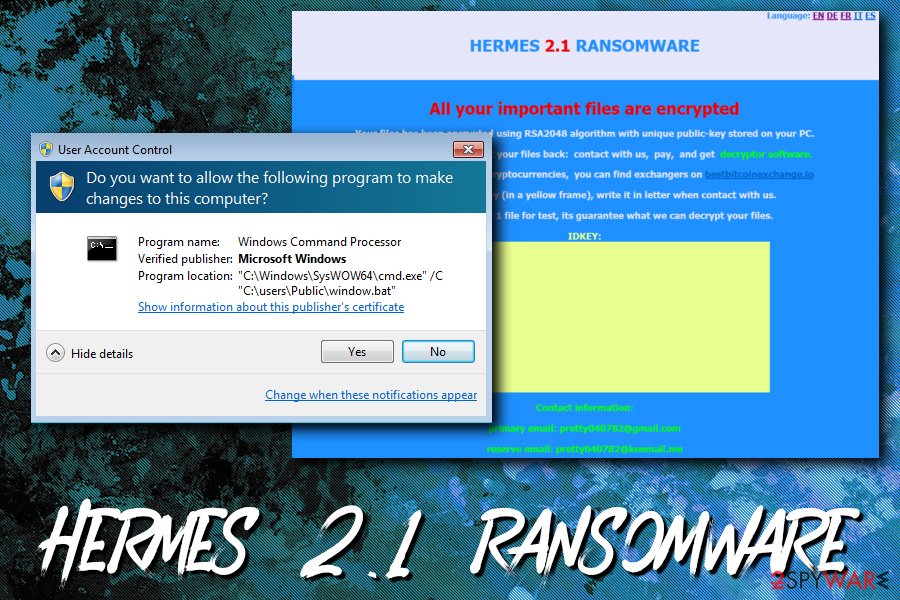
Hermes 2.1 ransomware continues the tradition of deleting the latter copies. The ransom note is identical to the previous version except the title now mentions “Hermes 2.1 ransomware.” It also drops the file named the same way as the former version – UNIQUE_ID_DO_NOT_REMOVE file which contains victim's ID.
This version also provides two newly generated email addresses: BM-2cTSTDcCD5cNqQ5Ugx4US7momFtBynwdgJ@bitmessage.ch and BM-2cT72URgs1AWGV6Wy6KBu2yuj3ychN5vxC@bitmessage.ch. This latest version also includes a code launching the mp3 file which plays Vivaldi's Spring composition.
Ways to prevent ransomware attack
Ransomware viruses are spread using a number of techniques such as malvertising, spam emails, social engineering, pirated software bundles and so on[7]. You can get the virus after opening an infected email attachment, link sent by an unknown person or even your friend on social media sites, or after installing a software crack.
Scammers find more and more ways to deceive victims on a daily basis, and it can be hard to keep up with the latest malware distribution trends all time.
To avoid ransomware, we simply advise you to stay away from suspicious content online[8] and protect your PC with proper security tools such as anti-malware and antivirus. The most important thing is to get yourself covered in time and create some data backups prior to malware infection.
Hermes termination options
If you have discovered Hermes virus on your system, we suggest removing it as soon as possible. It seems that you have already done a little digging and consequently you came across this website for information about Hermes removal – that is a good start. We provide instructions on how to remove Hermes ransomware down below.
Please do not attempt to delete this malicious virus by yourself because you can easily delete important files, which would result in various computer stability problems.
Getting rid of Hermes virus. Follow these steps
Manual removal using Safe Mode
Dear visitor, if your files have been encrypted with ransomware, do not try to fix the situation manually. We strongly advise you to use professional malware removal tools, however, the virus might try to prevent you from launching them. So if you want to wipe the ransomware and related files out of your system, restart your PC using instructions provided below.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Hermes using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Hermes. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Hermes from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files have .hermes extensions now, you probably cannot open them. Sadly, they can only be reverted to their initial state with a help of decryption key, but if you do not have it, you will need to use your data backups to recreate lost data. If you do not have data backup, follow these instructions.
If your files are encrypted by Hermes, you can use several methods to restore them:
Run Data Recovery software
Data Recovery Pro is a recommended tool when it comes to data recovery. You might want to install and run this tool to try and restore corrupted files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Hermes ransomware;
- Restore them.
Windows Previous Versions
If you created a system restore point in the past, you are lucky, because now you will be able to restore some files without paying the ransom. Please, follow these easy steps.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Hermes decryptor
Make use of Hermes decryptor [download link] developed by security researcher Michael Gillespie
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Hermes and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Brian Heater. The Growing Threat of Ransomware. PC Magazine. Technology Product Reviews, News, Prices, and more.
- ^ The Relentless Growth of Cybercrime. Press Release from EUROPOL.
- ^ RSA-2048. Wikipedia. The Free Encyclopedia.
- ^ Jérôme Segura and Vasilios Hioureas. Hermes ransomware distributed to South Koreans via recent Flash zero-day. Malwarebytes Labs. Official blog.
- ^ Catalin Cimpanu. North Korean Hackers Used Hermes Ransomware to Hide Recent Bank Heist. BleepingComputer. News,reviews and tech support.
- ^ Darren Boey. North Korean Hacker Group Linked to Taiwan Bank Cyberheist. Bloomberg. Official website.
- ^ Kevin Savage, Peter Coogan, Hon Lau. The evolution of ransomware. Security Response. Symantec Connect Community.
- ^ Wendy Boswell. How do I avoid dangerous websites?. Lifewire. Tech Untangled.







