JapanLocker ransomware / virus (Removal Instructions) - updated Oct 2016
JapanLocker virus Removal Guide
What is JapanLocker ransomware virus?
JapanLocker ransomware virus. What do we know?
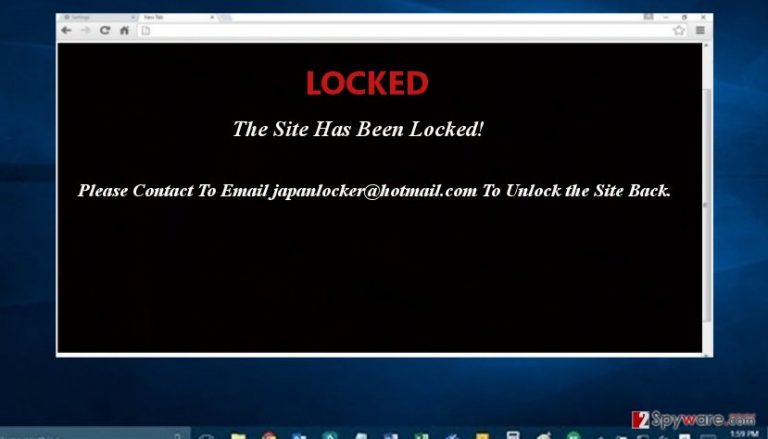
JapanLocker virus is a ransomware-type virus which joined the community of viruses in the beginning of October. According to the latest reports, its developers have nothing to do with Japan. This ransomware belongs to Indonesian gang which has already become famous for publishing various scripts and exploits on hacking forums. However, it seems that now this gang is ready to make the money with the help of another illegal way – distribution of an open source ransomware that targets websites. According to security researchers, JapanLocker ransomware can encrypt web sites with a help of combination of base64 encoding, ROT13 encryption algorithm and top-bottom swapping. The server can be decrypted by reversing this process or using a free decrypter that has already been presented, so you should Brush aside the considerations to pay the money, and make JapanLocker removal your current priority. As soon as this cryptomalware finishes its work, it presents japanlocker@hotmail.com email address to the victim.
The ransom message which is displayed by JapanLocker claims: “LOCKED. The site has been locked!” It seems that there has been a new wave of “Locker” virus series. The “predecessor” of this family – CryptoLocker has been officially terminated a few months ago. However, there have been several other Locker threats appearing, such as CTB Locker, TorrentLocker, and VenusLocker. Certainly, not all of them are as complex as the mentioned threat which managed to rampage on the internet for several months and make thousands of dollars profit. Taking a look at the current virus, it is surely an interesting sample. At the moment of writing, it seeks to affect websites so you are likely to encounter this ransomware if you own a domain and you haven’t paid much attention nor resources to the protection of your web page. However, there are ways how to remove JapanLocker. You can do it with the help of FortectIntego.
Besides, following the current trend, this ransomware may turn into an ordinary crypto virus that targets users or company’s data and then encrypts it with the RSA-2048 or RSA-1024 algorithm. After that, the virus opens a .txt message with the instructions of data recovery and payment transmission. Depending on the sense of personal greed, hackers may demand 1 (1BTC≈ 600 USD) or more Bitcoins. Looking back at the notorious case of CryptoLocker, the cyber criminals have managed to collect several millions of dollars revenue. Therefore, there are no or few reports about data return. In the case of JapanLocker malware, hackers may require a delicate amount of money as well since they target websites which monitor larger amounts of money. It might be only a matter of time when this ransomware starts assaulting private users. Thus, you should be more vigilant than ever before.
Furthermore, there have been already Japan-themed file-encrypting threats. A few months ago, hackers decided to make fun by launching KawaiiLocker. The authors of this malware were hardly Japanese as the ransom message was presented in the Russian language. Around the same time, Takahiro Locker ransomware made the appearance. This virus has been named after the name of notorious layer Takahiro Karasawa. Dissatisfied Japanese citizens have made numerous mocking posts about his behavior. The scandals inspired hackers‘ imagination as well. However, the ransomware is surely not a small computer pest, as it uses several channels for distribution: spam messages and exploit kits. The ransomware employed a complex encryption technique and demanded three bitcoins in exchange for the encrypted data. Though website blocking is performed using different techniques, JapanLocker ransomware should not be underestimated as well.
How can I get infected with this cryptomalware?
The current main target rests on websites. Thus, web page administrators, who failed to update their WordPress or CloudFare proxy servers, risked running into Japan Locker malware. In addition, the malicious code which locks the website might have slipped through another infected web page which shared the same proxy. You should not exclude the possibility that the malware exploits exploit kits for facilitating its attacks. When it comes to these malicious tools, it is of utmost importance to employ proper security applications which specialize in confronting and terminating ransomware threats.
How to remove JapanLocker?
Ransomware threats are surely an unpleasant phenomenon. While you can get rid of ordinary viruses quite easily, the former threats leave lingering aftermaths, such as encrypted data. We suggest using security applications, e.g. FortectIntego or Malwarebytes, for the termination. After you remove JapanLocker virus, you might notice that your website includes several encrypted elements. In that case, you might use the below-suggested data recovery tools. If the computers of the infected server are hard to control, you will need to regain full access. In order to perform full JapanLocker removal, the following instructions assist you in continuing the process.
Getting rid of JapanLocker virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove JapanLocker using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of JapanLocker. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove JapanLocker from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by JapanLocker, you can use several methods to restore them:
Use Data Recovery Pro to recover your files
Data Recovery Pro is a utility that restores damaged and missing files. It also comes in handy after ransomware attack, so make sure you try it if encrypted by JapanLocker. Steps that you need to follow are written below.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by JapanLocker ransomware;
- Restore them.
Use a free JapanLocker decryptor by FortiGuard Lion Team
If infected with JapanLocker, you can use a free decryptor presented by FortiGuard Lion Team. It is available at (copy this link and paste to your web browser): https://github.com/fortiguard-lion/schRansomwareDecryptor/blob/master/schRansomwarev1_decryptor.php
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from JapanLocker and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.







