Playbar.biz virus (Free Instructions) - Jul 2018 update
Playbar.biz virus Removal Guide
What is Playbar.biz virus?
Playbar.biz is a potentially unwanted program that modifies web browsr settings without permission
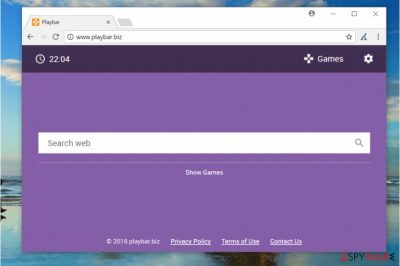
Playbar.biz is a dubious website that gives users the opportunity to pick from a variety of different games and play them directly from Google Chrome, Internet Explorer or Mozilla Firefox web browsers. However, the suspicious app is considered to be a browser hijacker which is distributed with the help of a deceptive marketing technique called software bundling. It allows the potentially unwanted program to stay off-radar during freeware installation and users can then see the color-changing background as their front page every time they want to browse the web. Additionally, despite the efforts of developers, users soon notice that redirecting, advertisement, slowdowns, and other issues are forcing them to look for Playbar.biz removal methods.
| Name | Playbar.biz |
|---|---|
| Type | Browser hijacker |
| Symptoms | Homepage, new tab, search engine settings changed |
| Distribution | Software bundles |
| Dangers | Can attract malware |
| Elimination | Use FortectIntego for the Playbar.biz removal |
Playbar.biz PUP tends to sneak into the computer system unnoticed. It might get installed alongside a free game or another free app downloaded from the Internet. As a consequence, it places hxxp://Playbar.biz/ as default homepage and search engine provider to start annoying the victim right away.[1] The worst is that it clutters search findings with sponsored links. Some of these are considered dangerous as they can trigger redirects to shady external sites, and that is how Playbar.biz can cause malware infections.
You should remove Playbar.biz from the device as soon as you notice this activity. You can do it quickly with the help of FortectIntego. These are the main features why browser hijacker are not wanted on the computer or another device:
- Hijacker might spy on your browsing preferences. It might attempt to collect data such as your IP address, search queries, clicks and similar.
- The quality of search results might not be satisfying as more advertising domains are presented. Clicking on them might lead to insecure web domains.
- All those browser changes result in useless online searches because results are filled with commercial content.
- The later you eliminate the described hijacker, the more unwanted tools might get attached to the browser.
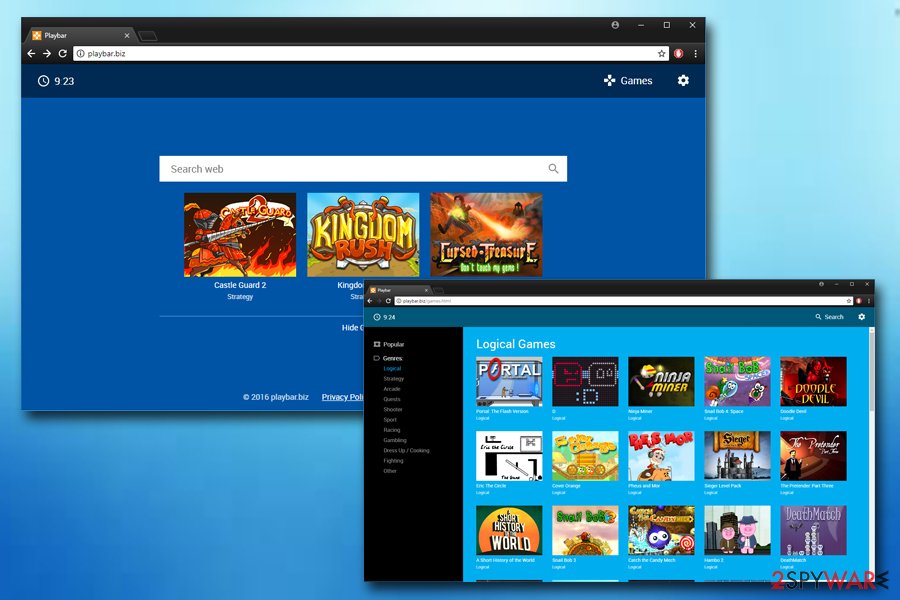
Though there are multiple PUPs which try to allure users with a basic design, others attract attention with eye-attracting themes and designs. Quick access links to gaming websites that Playbar.biz provides are another tools to catch users' attention. The latter is a common feature of many browser hijackers. However, such promotion of third-parties has its negative flaws. You might get redirected to affiliate websites forcefully. This intrusive and unwanted activity makes people eager to call it Playbar.biz virus.
Playbar.biz browser hijacker might also implant its “helper elements.[2]” They are not only responsible for consolidating the hijacker’s position on the system but they might also accelerate the installation of additional plug-ins and browser extensions. They are rarely practical. They might also trouble the uninstallation process.
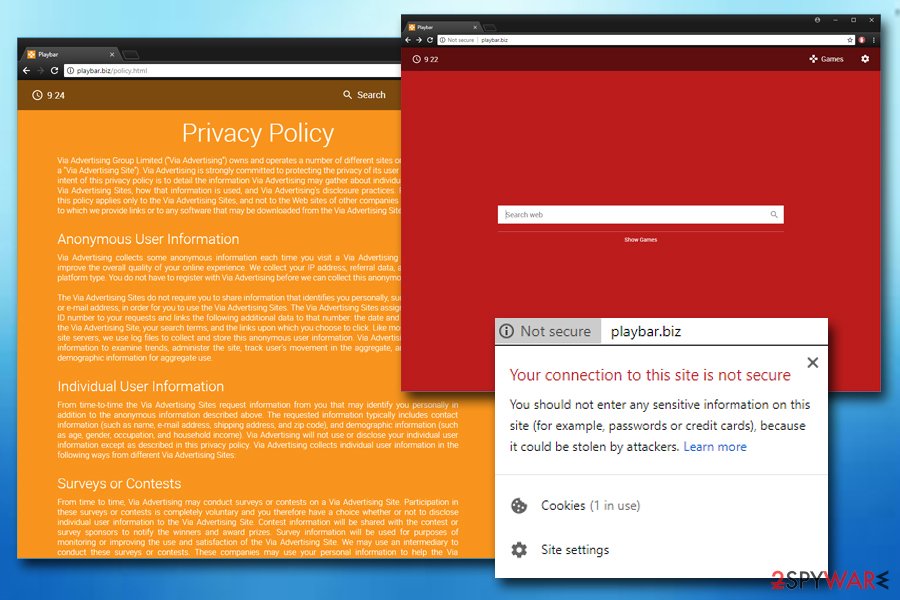
Finally, the Playbar.biz collects a variety of non-personal information, such as IP address, web search data, technical information, etc. Although many websites do it for marketing purposes, it is highly unlikely that users would be kept on such behavior. In other words, Playbar.biz knows everything about your hobbies, which cinemas you like to visit, etc.
According to Playbar.biz' Policy Policy, some personal information can be collected and stored when users provide it themselves. The worst part is that this data might be transferred in case of a merger:
In the event Via Advertising goes through a business transition, such as a merger, being acquired by another company, or selling a portion of its assets, users' personal information will, in most instances, be part of the assets transferred.
All in all, if you want to play games online, pick a legitimate source which will not spam you with advertisements, redirect you to dubious sites and display not so genuine search results.
Freeware providers and virus developers bundle their products together
This browser hijacker might have sneaked into the PC while you recklessly installed another application. Specifically, the browser hijack occurs when you quickly rush through the installation of software or updates. Spyware distributors are aware of such common tendency, thus, they place the unwanted tools to freeware.
Unfortunately, the method still proves to be effective as users dash through the stages without giving a second look. Furthermore, within seconds the hijacker finds its place in the system. If you are willing not to commit the same mistake again, keep in mind this advice. After installing any application, opt for “Custom” settings. Likewise, you will see optional applications. Unmark the unnecessary applications and proceed with installing the preferred program.
Playbar.biz removal requires professional help
To remove Playbar.biz, you need to use anti-malware tools. These applications are specifically designed for locating all elements of the hijacker and other PUPs. If you try to remove all additional parts of the hijacker yourself, it might take time.
If you would rather avoid additional software on your computer, follow the Playbar.biz removal instructions below. We have prepared a step-by-step guide with possible methods of virus termination and some helpful tips. Security experts[3] advise users do not forget to keep anti-spyware tools up-to-date and running. An occasional scan with anti-malware tools can help users to avoid infection repetition.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Playbar.biz virus. Follow these steps
Uninstall from Windows
Remove browser hijacker from your Windows OS:
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
These are the steps if you got Playbar.biz virus on your Mac:
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Find all entries associated with PlayBar.biz virus and delete them. If you do not know where to look for such entries in Chrome, enter chrome://extensions in the URL bar.
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Playbar.biz registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting stealing programs
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Eric Chien. Techniques of Adware and Spyware. Symantec Security Response. Security Information of a Time critical Nature.
- ^ Browser Hijack Objects (BHOs). Malwarebytes Blog. Latest Security News, Threat Research.
- ^ NoVirus. NoVirus. Cyber Security Experts Share Their Opinion, Malware and Spyware News.























