Sage 2.2 ransomware / virus (Removal Guide) - Oct 2017 update
Sage 2.2 virus Removal Guide
What is Sage 2.2 ransomware virus?
Sage 2.2 ransomware hits computer users again in October 2017
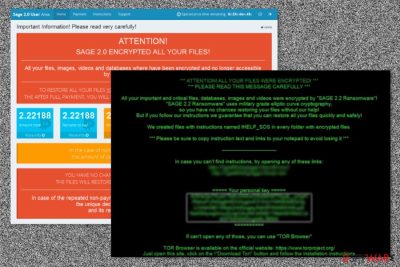
Sage 2.2 ransomware is a new version of crypto-virus which hails from the same family of malware as Sage ransomware and Sage 2.0. After infecting the system, the virus encodes files and adds .sage file extensions to their names. Afterward, it plays an audio message, deletes Volume Shadow Copies, drops a ransom note !HELP_SOS.hta and changes the desktop wallpaper with !HELP_SOS.bmp image. The virus demonstrated outstanding activity in October 2017.
First signs of Sage 2.2 ransomware were spotted in mid-January this year. One of the peculiarities of this malware was that it delivered the malicious infection in the double zipped .zip folder[1] which is named as [random numbers]_ACH20022017.zip or min1_201720103191.58778.zip. This .zip folder contains either a .doc or .js file.
Beware that some emails even do not present any message content. However, some of them might be disguised as notifications sent from Central Security Treatment Organization. The malware works on a basic model – it sends UDP (User Datagram Protocols) to thousands of IP addresses.
After extracting the content, the malware would execute via spam1.exe. It might also hide under the disguise of startup.php. Later on, Sage 2.2 ransomware downloads its main payload to %Temp% folder and replicates itself to C:\Users\[loginname]\AppData\Roaming.
Such behavior triggers the UAC messages. Luckily, you might interfere with its operation by canceling this command. The UAC message pretends to be initiated by Microsoft Corporation. The only hint referring to the virus is the odd location of AppData folder. As soon as you notice any of these symptoms, remove Sage 2.2 right away.
The developers of Sage 2.2 virus do not seem to waste lots of their time while renewing this ransomware – the most of it is built using an old code of Cerber. But, having in mind its popularity, we should all think about a proper security software and knowledge. Otherwise, malware can infect your computer system without any sign as it spreads under different names.[2]
Speaking of similarities with Cerber, this virus also has ability to “speak” to the victim. The malicious virus plays the following audio message for the victim using Microsoft SAPI:
Attention! Attention! This is not a test!
All your documents, data bases, and other important files were encrypted, and Windows can not restore them without special software.
User action is required as soon as possible to recover the files.
The links provided in the ransom messages lead to a sophisticated payment website that consists of Payment, Instructions, Test decryption, and Support pages.
If, unfortunately, this threat has already descended upon you, follow Sage 2.2 ransomware removal steps. Launch FortectIntego to speed up the process.
As it is common for this type of threats, the malware alarms victims to pay the ransom within the specified amount of time. Needless to say, that these files are said to be deleted after the expiration. Soon afterward, Sage 2.0 was released[3].
It demanded over 2 000 USD for the decryption of files. Data recovery instructions reveal that the developers are trying their best to scare users to comply with the demands. That's why they emphasize that there is no other solution to retrieve the files.
October 23, 2017, update: BlankSlate campaign stops spreading Locky, starts pushing Sage 2.2
On October 13th, researchers spotted an increased number of complaints from computer users affected by Sage 2.2 ransomware virus. It appears that the BlankSlate malspam campaign stopped distributing Locky ransomware and started pushing the 2.2 version of Sage ransomware instead.
The so-called BlankSlate attacks have enormous reach, and there is no surprise why so many computer users received deceptive emails containing the virus. Initial analysis of these fraudulent emails shows that each of them contains a .ZIP attachment entitled with a random set of digits.
Once extracted, the .ZIP file drops another .ZIP file. Inside the second .ZIP, a JavaScript file waits for the user to double-click it. Once the victim does so, the malicious script connects to a remote domain, downloads Sage 2.2 and runs it on victim's computer immediately. This wreaks absolute havoc on the system, corrupting each valuable file without leaving any easy ways to recover it.
The new version demands 0.17720 BTC (approximately $1000) as a ransom. The provided ransom price is valid for 7 days. After 7 days of non-payment, it doubles. Experts from Dieviren.de[4] do not recommend paying the ransom since there are no victims who confirmed that crooks actually recover the data after receiving the payment.
The exceptional specifics of crypto-ransomware distribution
The malware preys on new victims through spam messages. Bear in mind that ransomware often disguises under fake invoice and other official documents. Do not rush opening the attachments as you will need to deal with the termination of such threat.
The crooks have also thought about additional transmission methods. Sage 2.2 virus has been detected as these trojan horse versions:
- Win32.Trojan.WisdomEyes.16070401.9500.9973
- Trojan/Win32.SageCrypt.C1798570
- Trojan.Encoder.10307
- Win32/Trojan.Ransom.aac
Beware that Cerber distributors have shifted to spreading Sage 2.2 malware, so they might use the old tricks to boost up the infection rate. In the end of 2016, Cerber was spreading with the assistance of RIG exploit kit[5] and corrupted Adobe Flash Player attachments.[6]
Also, it was revealed that Sage 2.2 might disguise as an Adobe Service Manager as well. Besides, it is also known that this threat is able to delete shadow volume copies. Thus, it is of key importance not only to protect your system with an anti-malware program but stay vigilant while browsing online and save backups of the most important data.
Remove Sage 2.2 virus for good
When it comes to a file-encrypting malware, you should save every minute if possible. For that reason, start Sage 2.2 removal immediately. Install an anti-spyware program, e.g. FortectIntego or Malwarebytes, eradicate the malware completely. If you are having difficulties eliminating the threat due to the paralysis of the system, enter Safe Mode with Networking.
The following instructions will show how to launch it. Then, you will be able to remove Sage 2.2 virus. Keep in mind that the software does not decrypt the files. For that, you will need to look for alternative solutions. A few are presented below.
Getting rid of Sage 2.2 virus. Follow these steps
Manual removal using Safe Mode
To remove Sage 2.2 from Windows, reboot your computer to Safe Mode with Networking first. In this mode you will disable your ransomware.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Sage 2.2 using System Restore
Use System Restore to get rid of ransomware if your anti-virus program is blocked. Steps that you need to perform are given bellow:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Sage 2.2. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Sage 2.2 from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Sage 2.2, you can use several methods to restore them:
What is Data Recovery Pro?
This app comes in handy when locating damaged files. Though there is no 100% guarantee that the program will recover all files, you might still give it a try.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Sage 2.2 ransomware;
- Restore them.
Opt for Windows Previous Versions function
Follow the steps to retrieve the previously automatically saved copy of your file. Though this method takes time, but you might succeed in recovering some of the files.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Using Sage Decrypter to recover your files encrypted by virus
At the moment, there is no LEGITIMATE Sage 2.2 decryptor for files' recovery. However, make sure you do NOT think about purchasing the one that belongs to the developers of this malware. It can be just another scam used to extort people's money.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Sage 2.2 and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Michael Mimoso. Sage and Satan Ransomware, Double Trouble. Thread Post. The first stop for security news.
- ^ Sage 2.2 ransomware. Virus Total. Analysis of suspicious files and URLs.
- ^ Larry Loeb. Sage Ransomware Levels Up. Security Intelligence. Analysis and Insight for Information Security Professionals.
- ^ DieViren. Dieviren. Malware Removal Guidance, Security Tips.
- ^ Jérôme Segura. RIG exploit kit takes on large malvertising campaign. Malwarebytes Labs. Official Malwarebytes Security Blog.
- ^ Richi Jennings. Just say NO to Adobe Flash Player -- emergency patch vs. Cerber ransomware. ComputerWorld. It news, careers, bsuiness technology, reviews.





















