Search.searchtp.com virus (Free Instructions)
Search.searchtp.com virus Removal Guide
What is Search.searchtp.com virus?
Why does Search.searchtp.com redirect you to suspicious sites?
If you have experienced these redirects, most likely you have thought that your computer is affected by Search.searchtp.com virus. In reality, this program is not harmful, but no one can deny that it is a highly annoying one. We have analyzed this program and decided to assign it to “browser hijackers” list due to its questionable functionality. It goes without saying that it belongs to “potentially unwanted programs” list, too. It is recommended to keep computer free of this program; otherwise, you will be forced to experience Search.searchtp.com redirect issues, system slowdowns, and other problems that it can cause.
This search engine will appear in your browser in case you install Tracker Package extension. This extension can read and change all data on sites you visit, as well as manage your extensions, apps, and themes. It adds new homepage and search tool to the browser, which shows up immediately after user launches the web browser or a new tab. Do not be mistaken and do not think that this site offers a reliable search tool. It appears that it presents a lot of sponsored search outcomes, which are meant to point users to third-party websites. It is highly advisable to be very careful while using a search engine that advertises such sites, because after clicking on such paid search results you can be directed to sites that might be insecure. Let’s not forget the fact that the majority of unsafe websites are created to look secure; to avoid potential risks, we strongly recommend you to ignore invitations to update your programs or install new ones. In the worst scenario, you can allow installing a Trojan horse, and it is not a secret that such malicious programs spread around the Internet masqueraded as safe files. Beware of bogus Java Player, or Flash updates – these are the ones that usually distribute malicious files alongside them. We suggest installing software only from reputable sites.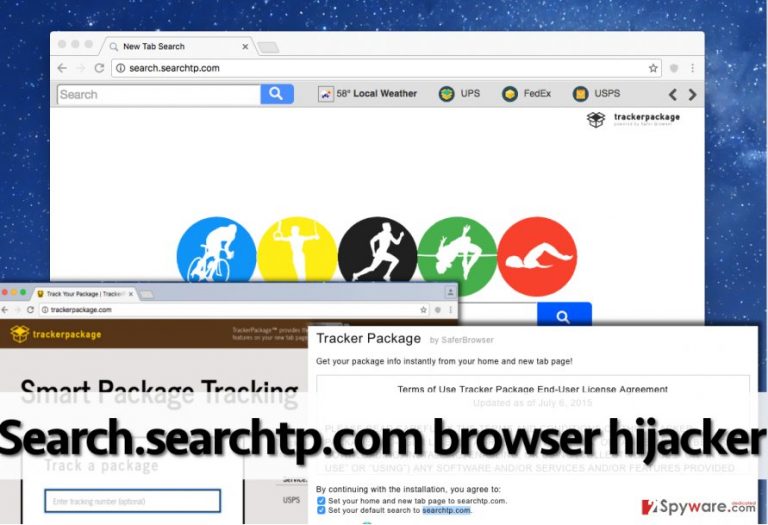
We must note that this browser hijacker tracks your browsing preferences. Although it does not collect personal information, it can collect and store URLS that you visit, words that you enter into search engines, and similar information. The hijacker shares such information with third-parties for marketing purposes and later uses it to integrate sponsored content. If you do not want your search or browsing activity to be tracked, just remove Search.searchtp.com. You can delete it using a spyware elimination software, for instance, FortectIntego, or eliminate it manually with a help of Search.searchtp.com removal guide that is provided at the end of this article.
How did I install this program?
There are two ways to install this program. You can download it from its official website, TrackerPackage(dot)com, or you can allow Search.searchtp.com hijack your computer without even knowing about it. The second situation can occur in case you rush to install PC programs without even modifying installation settings in a proper manner. It is a must to set either Advanced or Custom settings for your installation because then you can access the list of optional apps added to your download and refuse to install them. This list of optional components frequently include statements that grant permission to change browser settings, add toolbars, extensions, new search tools, and so on. Make sure you deselect such permissions, too!
Search.searchtp.com removal tips
To entirely remove Search.searchtp.com virus, you need to do two things. Please follow instructions provided below and delete components of this hijacker manually. In case you cannot remove them all, and also just to complete Search.searchtp.com removal successfully, run a system scan using spyware removal tool afterward. If you do not have one, you can choose one of the following programs that out team recommends:
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Search.searchtp.com virus. Follow these steps
Uninstall from Windows
-
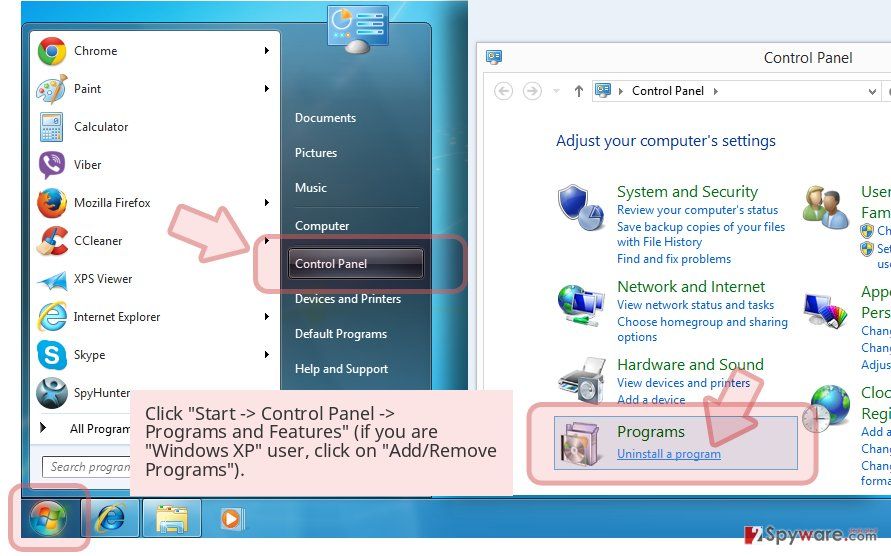
Click Start → Control Panel → Programs and Features (if you are Windows XP user, click on Add/Remove Programs).

-
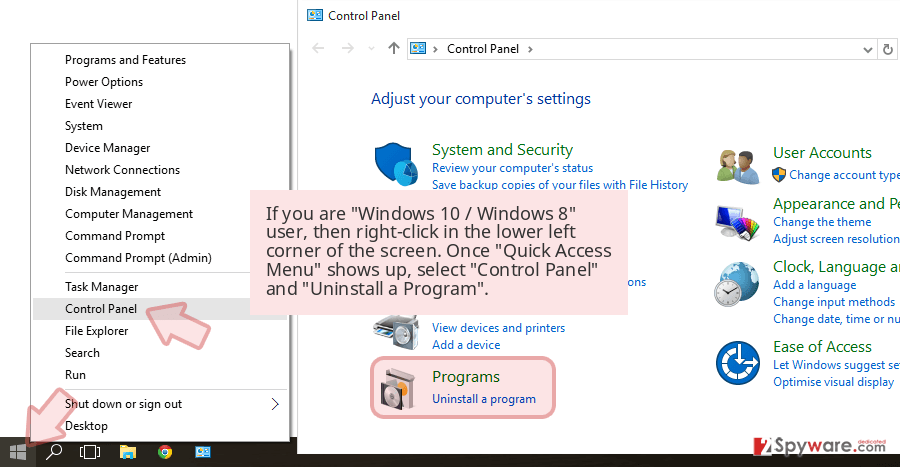
If you are Windows 10 / Windows 8 user, then right-click in the lower left corner of the screen. Once Quick Access Menu shows up, select Control Panel and Uninstall a Program.

-
Uninstall Search.searchtp.com and related programs
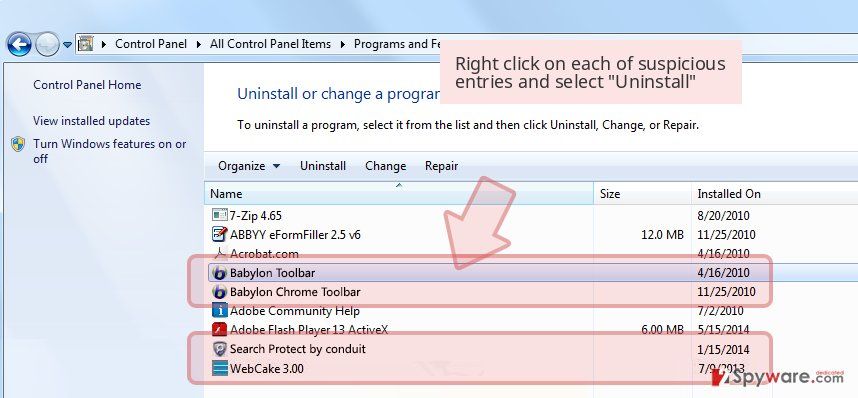
Here, look for Search.searchtp.com or any other recently installed suspicious programs. -
Uninstall them and click OK to save these changes.

Delete from macOS
-
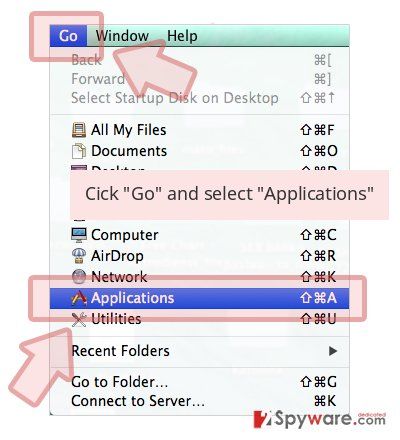
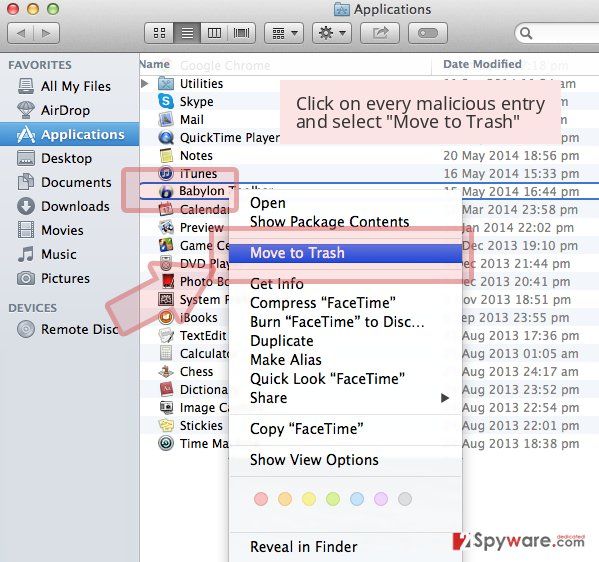
If you are using OS X, click Go button at the top left of the screen and select Applications.

-
Wait until you see Applications folder and look for Search.searchtp.com or any other suspicious programs on it. Now right click on every of such entries and select Move to Trash.

Remove from Mozilla Firefox (FF)
Once you enter Firefox Add-ons panel, go to Extensions and remove an extension called Tracker Package. Do not forget to delete other suspicious extensions as well.
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted extension and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Settings.
- Under Home, set your preferred homepage and new tab settings.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data and Temporary cached files and pages, then click Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Get rid of extension named Tracker Package, and also remove other suspicious add-ons as well.
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all suspicious extensions related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Search.searchtp.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting stealing programs
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.