Corrupt PC Optimizers
Computer experts and cybersecurity specialists have always been skeptical about PC optimization tools. They often claim that such tools are simply a waste of money and computer’s space. Adding to that, IT professionals point out that these programs rarely even have any visible impact on the system’s performance and emphasize that the same level of optimization can be achieved manually, without having to spend a dollar. Some regular computer users may argue that they do not have the time or proper skills to carry out such procedures, so PC optimizers are the tools they are likely to turn to in case of need. Surely, these programs have their own benefits as well as drawbacks, and we may have different opinions on whether they are worth obtaining or not. But having in mind the large supply of such software online, it is more important to be able to distinguish between legitimate and corrupt PC optimizers.
What is the purpose of PC optimizers?
If you regularly browse online, you may have seen the ads offering to download software that will speed up your computer’s performance, clean up unnecessary junk files and sort out a bunch of other problems. That is exactly what PC optimization software is designed for. It may assist you in your daily computer use by automatically cleaning up your trash folder, outdated registry entries, cached data or browser-related information. Other tools may also help restore accidentally deleted documents or even help bypass ransomware encryption and recover some of the locked files. Finally, you can also choose full security suites that combine tune-up utilities and security software, providing the users with an extended protection and optimization service. All in all, such tools can be useful for those, who do not trust their skills enough to take up such tasks or for the users who would rather have an automatic utility take care of the specific issues in just a couple of minutes. You can read more about the benefits of these legitimate computer management programs in a separate PC Optimizers category.
How rogue PC optimizers differ from the legitimate ones?
It might be a simple question, but it needs to be answered. You cannot avoid potentially dangerous applications if you do not know the specific characteristics that distinguish them from the legitimate software. Of course, the most obvious difference is the fact that these programs are malicious and may inflict some level of damage. But this fact alone in no way helps us draw a strong line between the potentially infectious and the real software. What really discloses the nature of one program or the other is the way it acts on the computer:
- Appearance on the system
Legitimate programs rarely enter computers without the users’ permission. They are usually downloaded from the official websites, reputable software sharing sites or purchased in a material format.
Rogue optimization tools, on the other hand, use stealthy system infiltration strategy quite extensively. Though their developers invest in well-designed and legitimate-looking official websites, users are unlikely to download these applications on their computers directly. Most of the time, rogue optimization tools install along with other freeware or shareware applications as optional software package components. In an attempt to keep the infiltration as quiet as possible, malware creators hide rogue applications under the advanced installation settings which the user tend to ignore simply because they are time-consuming.
- Working strategies
Reputable PC tuneup tools are always adjustable according to the user’s needs: they can be assigned to initiate at the system’s startup automatically or only perform when necessary. Professional utilities do not impact system’s performance, so you should be able to use your computer as usual while the application is running. Remember, these tools are designed to improve, not diminish your computer use experience.
Fake optimizers display quite the opposite behavior. They may modify computer’s settings and create new registry entries in order to initiate at startup or run scheduled processes. Typically, the user has no control over these modifications and simply has to adjust to the new “rules” a rogue optimizer has set on the computer. And this new reality may not be very pleasant. Depending on a type of malware, it may initiate unexpected system scans, drop alarming pop-up notifications warning the user about the supposedly critical condition of the device. In most rogue apps, these warnings are followed by the insistent prompts, encouraging the user to obtain a full version of the software and fix the computer. Despite their considerable price, these programs are useless or completely non-existent. It is merely a fraudulent strategy the cyber criminals have come up with to earn themselves some easy money. Thus, the users who download such applications on their devices can consider themselves scammed. Besides, rogue apps may also block security software from operating, this way ensuring their malicious plans are not ruined.
- Software removal
If you are unhappy with some legal computer optimization tool or simply want to switch to some other utility, you can delete it from your computer like any other program. Once deleted, it should leave no trace or residue content on the device.
Corrupt optimization software is not that easy to get rid of. These programs are designed to hide on the computer and even block installed antivirus utilities from running system scans in order to remain unnoticed. Nevertheless, these programs are not malicious viruses, so it is possible to bypass them and remove them from the computer. On our site, we try to keep up with the latest rogue optimization tools and provide you with the best removal solutions. So keep an eye on our site, to stay updated.
How to avoid downloading a fake PC optimizer?
It is rather easy to mistake fake PC optimizers for the legitimate ones and accidentally download a rogue program on your computer. So, it is always necessary to do a small research about the application before clicking the “Install” button. Most of the malicious programs and their descriptions can be found on our site, so you can always check-up with us if you are unsure whether the software is safe to obtain. However, we should warn you that the web is full of similar fake programs that haven’t been noticed by the security experts yet. That’s why you should always analyze as much of the users’ feedback you can find online and avoid obtaining software from questionable third-party websites.
Latest Software Reviews
Slow PCFighter
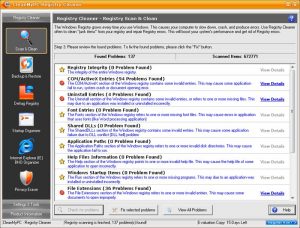
CleanMyPC Registry Cleaner
Information updated: 2017-05-11