“Security Status not satisfied” email scam (fake) - Free Instructions
“Security Status not satisfied” email scam Removal Guide
What is “Security Status not satisfied” email scam?
What is the “Internet is a dangerous place” email scam?
Sextortion scams like “Internet is a dangerous place” or “Security Status not Satisfied,” involve criminals claiming they've compromised your computer and recorded you visiting inappropriate websites. The scammers threaten to release these videos to your contacts unless you pay them, usually demanding payment in Bitcoin. Despite the threats, these emails are usually bluffs – they don’t actually have any videos. The goal is to scare you into sending money without questioning the legitimacy of their claims.
| Name | “Internet is a dangerous place” or “Security Status not Satisfied” |
| Type | Email scam, fraud, fake email, sextortion |
| Distribution | Malspam – the attackers send thousands of emails in bulk to extort as much money as possible |
| Operation | Cybercriminals claim that they hacked the system and that access to personal information was acquired. They say that a video of victims visiting porn sites was recorded, and if they don't want it to be disclosed publically, they should transfer bitcoin to a provided crypto wallet controlled by cybercriminals |
| Ransom size | $1,390 to be sent in Bitcoin to the provided crypto wallet |
| Dangers | Financial losses, virus infections |
| Removal | As a precautionary measure, scan your device with SpyHunter 5Combo Cleaner anti-malware software |
| Other tips |
How “Internet is a dangerous place” scam works?
This scam leverages the common fear that the internet is full of threats. The scam email might begin with a line like, “You’ve heard that the Internet is a dangerous place, infested with malicious links and hackers like me?” This sets a tone of fear and acknowledges a widespread belief about online safety.
The scammer will claim to have used sophisticated methods to breach your privacy, including the use of malware and AI to gain control over your devices. They may assert that they have recorded you through your webcam during compromising moments and threaten to release this footage. The goal is to make you panic and pay the ransom without seeking help or verifying the claims. These scammers rely heavily on social engineering techniques to manipulate emotions and prompt quick action.
Why did you receive the “Security status not satisfied” scam email
Receiving a “Security Status Not Satisfied” email does not mean you were specifically targeted because of your online behavior or security lapses. Instead, these emails are typically sent out in large batches to email addresses obtained from various data breaches, online directories, or purchased lists. The scammer's strategy is to cast a wide net, hoping that the sheer number of emails sent will result in some people paying out of fear and embarrassment.
The inclusion of phrases like “Security Status Not Satisfied” plays on the anxiety that one’s personal cybersecurity measures are inadequate. It suggests a failure in your digital defenses, making the scammer’s claims seem more plausible.
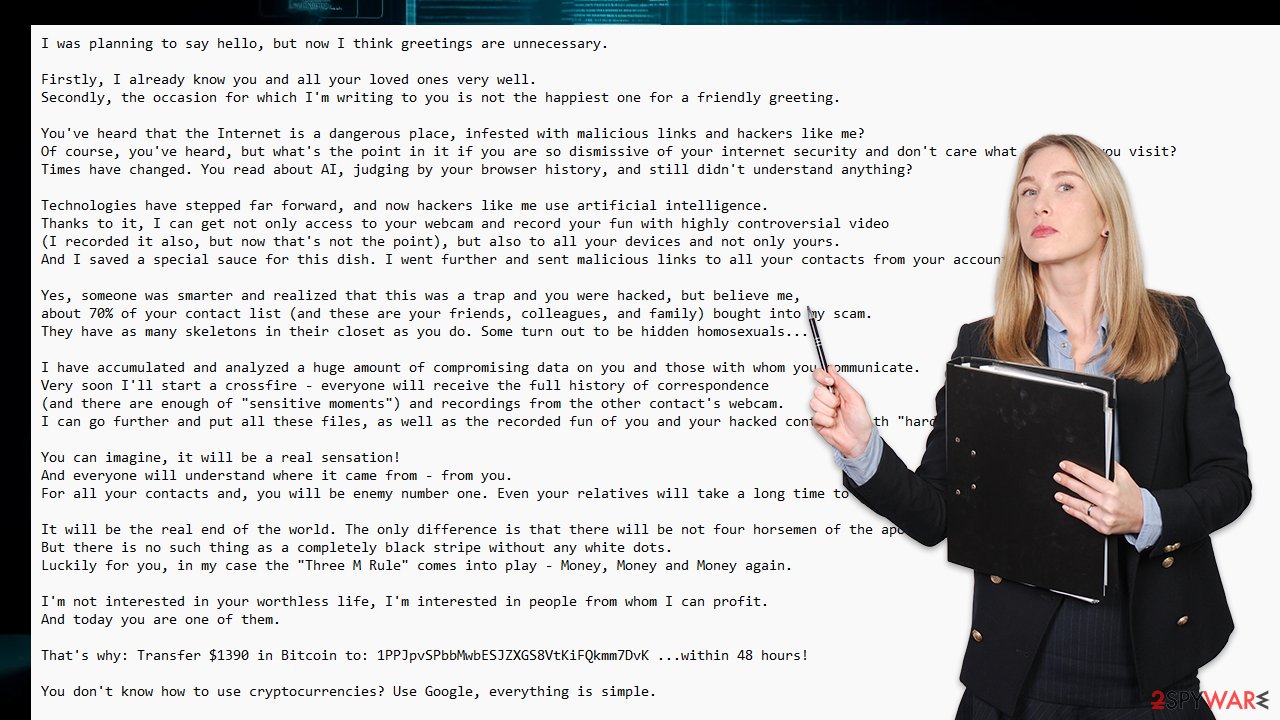
Here's the full message you might receive (with some variations) when dealing with this fakery:
Subject: Security status not satisfied.
I was planning to say hello, but now I think greetings are unnecessary.
Firstly, I already know you and all your loved ones very well.
Secondly, the occasion for which I'm writing to you is not the happiest one for a friendly greeting.You've heard that the Internet is a dangerous place, infested with malicious links and hackers like me?
Of course, you've heard, but what's the point in it if you are so dismissive of your internet security and don't care what websites you visit?
Times have changed. You read about AI, judging by your browser history, and still didn't understand anything?Technologies have stepped far forward, and now hackers like me use artificial intelligence.
Thanks to it, I can get not only access to your webcam and record your fun with highly controversial video
(I recorded it also, but now that's not the point), but also to all your devices and not only yours.
And I saved a special sauce for this dish. I went further and sent malicious links to all your contacts from your account.Yes, someone was smarter and realized that this was a trap and you were hacked, but believe me,
about 70% of your contact list (and these are your friends, colleagues, and family) bought into my scam.
They have as many skeletons in their closet as you do. Some turn out to be hidden homosexuals…I have accumulated and analyzed a huge amount of compromising data on you and those with whom you communicate.
Very soon I'll start a crossfire – everyone will receive the full history of correspondence
(and there are enough of “sensitive moments”) and recordings from the other contact's webcam.
I can go further and put all these files, as well as the recorded fun of you and your hacked contacts with “hardcore videos” into the public domain.You can imagine, it will be a real sensation!
And everyone will understand where it came from – from you.
For all your contacts and, you will be enemy number one. Even your relatives will take a long time to forgive you and forget such a family shame…It will be the real end of the world. The only difference is that there will be not four horsemen of the apocalypse, but only one – (=
But there is no such thing as a completely black stripe without any white dots.
Luckily for you, in my case the “Three M Rule” comes into play – Money, Money and Money again.I'm not interested in your worthless life, I'm interested in people from whom I can profit.
And today you are one of them.That's why: Transfer $1390 in Bitcoin to: 1PPJpvSPbbMwbESJZXGS8VtKiFQkmm7DvK …within 48 hours!
You don't know how to use cryptocurrencies? Use Google, everything is simple.
Once payment is received, I will delete all information associated with you and you will never hear from me again.
Remember one thing: my crypto address is anonymous, and I generated this letter in your mailbox and sent it to you.
You can call the cops, do whatever you want – they won't find me, my demands won't change, but you'll just waste precious time.The clock is ticking. Tick tock, a minute out of 48 hours has passed right now. An hour will soon pass, and in two days your old life will pass forever.
Either goodbye forever (if I get my payment), or hello to a brave new world in which there will be no place for you.Hasta La Vista, Baby!
P.S. Almost forgot. Finally learn what incognito tabs, two-factor authentication, and the TOR browser are, for God's sake!
How to respond to sextortion emails
When faced with a sextortion email, it’s crucial to remain calm and not act hastily:
- Engaging with the scammer or sending money only confirms that your email is active, potentially leading to further harassment. Do not contact these crooks under any circumstances.
- Forward the scam email to the authorities, such as the Internet Crime Complaint Center (IC3) or your national cybercrime unit.
- Conduct a thorough computer scan with reputable antivirus software, such as SpyHunter 5Combo Cleaner or Malwarebytes, to ensure no malware is present.
- Update passwords and enhance security settings across all critical accounts. Implement two-factor authentication where possible to add an extra layer of security.
- Learn about the common tactics used in sextortion and other online scams. Share this knowledge to protect friends and family from similar threats.
Next steps if you’ve already paid the scammer
If you have already responded to the scam by paying the ransom, it's important to take immediate action:
- Contact your financial institution: Inform them of the fraudulent transaction to explore possibilities for stopping or reversing the payment.
- Notify law enforcement: Reporting the scam can help authorities track down the scammer and possibly aid in the recovery of your funds.
- Monitor your financial statements: Keep an eye on your bank and credit card statements for any unauthorized transactions.
- Consult with cybersecurity experts: Consider hiring professionals to secure your digital life and prevent future incidents.
Recovering funds from a Bitcoin transaction can be challenging, but immediate action can increase your chances of regaining some or all of your money. Reporting the incident also contributes to broader efforts to combat online scams and protect others from becoming victims.
How to prevent from getting malware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
