Allahu Akbar ransomware (virus) - Recovery Instructions Included
Allahu Akbar virus Removal Guide
What is Allahu Akbar ransomware?
Allahu Akbar is a file-locking virus that can cause permanent data loss if there are no backups

Allahu Akbar is the name of a data-locking virus that has just been discovered by malware researchers and poses serious risks to its victims. This dangerous program uses complex encryption methods after entering an operating system to effectively encrypt users' files.
These include a variety of personal information, from images and videos to important documents. These files are given a distinctive “.allahuakbar” extension by the malware, which also changes their icons into blank white pages, making them unavailable and preventing previewing. After the encryption procedure is finished, the infected system generates a ransom note with the filename “how_to_decrypt.txt.”
| NAME | Allahu Akbar |
| TYPE | Ransomware, data locking virus, crypto virus |
| FILE EXTENSION | .allahuakbar |
| RANSOM NOTE | how_to_decrypt.txt |
| DISTRIBUTION | Infected email attachments, peer-to-peer file-sharing platforms, torrents, malicious ads |
| FILE RECOVERY | It is next to impossible to recover the files if you do not have backups or the decryption keys were not leaked; in some cases, recovery is successful with third-party software |
| ELIMINATION | Scan your machine with anti-malware software to eliminate the virus safely; this will not recover the locked files |
| SYSTEM FIX | You can avoid Windows reinstallation with FortectIntego maintenance tool, which can fix damaged files and system errors |
The ransom note
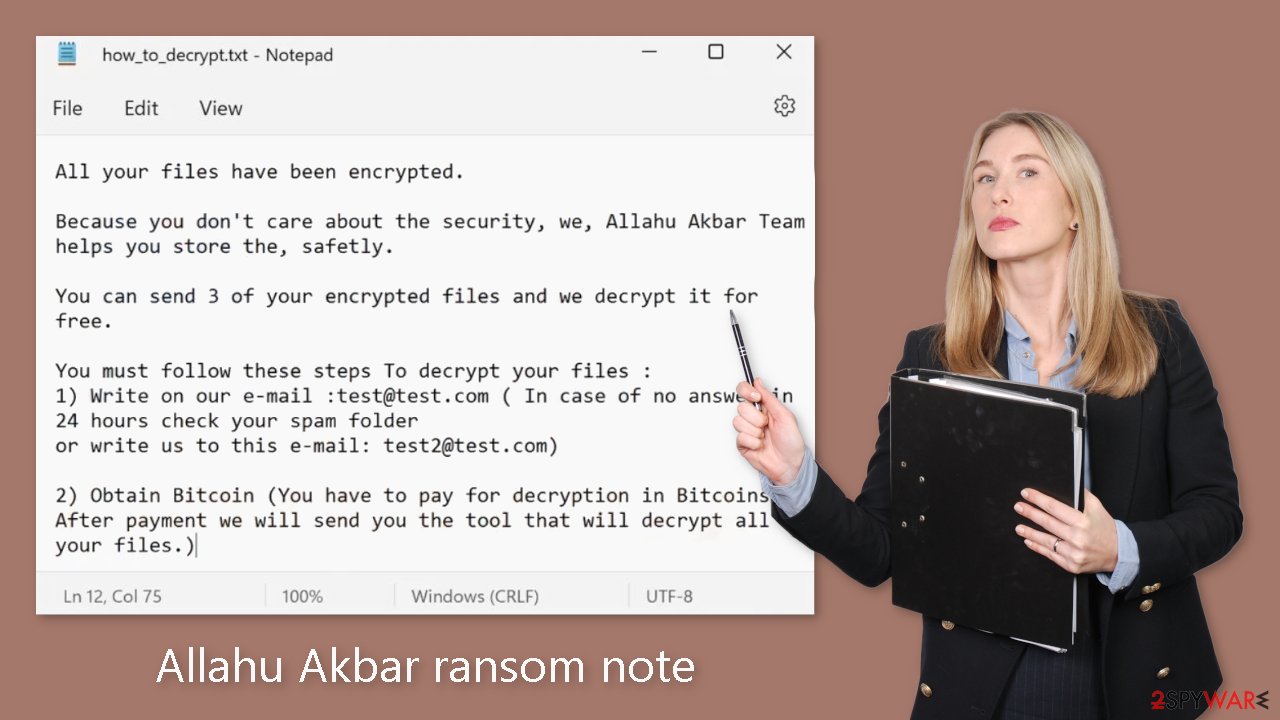
Allahu Akbar ransomware generates a ransom note how_to_decrypt.txt which reads as follows:
All your files have been encrypted.
Because you don't care about the security, we, Allahu Akbar Team helps you store the, safetly.
You can send 3 of your encrypted files and we decrypt it for free.
You must follow these steps To decrypt your files :
1) Write on our e-mail :test@test.com ( In case of no answer in 24 hours check your spam folder
or write us to this e-mail: test2@test.com)2) Obtain Bitcoin (You have to pay for decryption in Bitcoins.
After payment we will send you the tool that will decrypt all your files.)
By asserting that all data have been encrypted and providing a short window of time to decode three files for free, the message seeks to evoke a sense of urgency and anxiety. The note further implies that the attackers are offering a service to help protect the victim's data in an effort to trick them into paying. It's possible that the mention of the “Allahu Akbar Team” is meant to instill worry.
It's important to ignore the pressure and intimidation techniques present in such notes, though. In order to explore safer and more moral possibilities for recovering their data, victims should report the incident to law enforcement authorities and seek advice from cybersecurity experts. Up-to-date security software, strict cybersecurity procedures, and regular data backups can all help shield users from ransomware attacks in the first place.
Distribution methods
The particular techniques used to spread the Allahu Akbar ransomware are still unknown. However, there are a few typical strategies that hackers frequently use. The malicious malware typically enters through an executable file (.exe), which is frequently hidden inside a compressed zip folder, integrated into macros[1] of Microsoft Office documents, or disguising itself as an attachment that appears to be legitimate, like a fax. These incidents are typically linked to user error and a lack of knowledge of security flaws.
A prominent phenomenon is the propensity for certain people to install software that has been “cracked”[2] in order to avoid paying for licensing. These software repositories, which operate in an unregulated and unsafe environment, regrettably serve as a breeding ground for malware and potentially unwanted programs (PUPs). Downloads from these sources almost often contain dangerous files.
Exploiting flaws in software or operating systems is a common strategy used by hackers. Thus, it is essential to regularly upgrade all systems and software parts. In response to recently discovered vulnerabilities, developers often deploy security updates, making non-compliance a possible point of vulnerability.
Use professional security tools to eliminate malicious files
The first thing to do is cut off the hacked device's connection to the local network. Unplugging the ethernet cable is sufficient as a fix for those at home. The disconnecting procedure could be challenging for people who run across this problem in a work environment. Detailed corporate environment guidelines are supplied at the end of this guide.
Attempting to restore your data prematurely carries the risk of irrevocable loss. Moreover, there exists the possibility of secondary encryption of your files. The malicious process will persist unabated until the root cause, represented by the malevolent files, is eradicated. Undertaking the removal of malicious software independently is not recommended unless you possess relevant experience.
Use anti-malware tools like SpyHunter 5Combo Cleaner or Malwarebytes to scan your system. This security software should find all the related files and entries and remove them automatically for you. In some cases, malware is not letting you use antivirus in normal mode, so you need to access Safe Mode and perform a full system scan from there:
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.
Windows 10 / Windows 8
- Right-click on the Start button and select Settings.
- Scroll down to pick Update & Security.
- On the left side of the window, pick Recovery.
- Now scroll down to find the Advanced Startup section.
- Click Restart now.
- Select Troubleshoot.
- Go to Advanced options.
- Select Startup Settings.
- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
Fix system errors
One should be prepared to experience performance deterioration, decreased stability, and usability concerns after a malware infection, which can call for a full reinstallation of the Windows operating system. These viruses have the capacity to disrupt crucial bootup processes, change the Windows registry database, delete or destroy crucial DLL files, among other things. A system file can no longer be repaired by traditional antivirus software once malware has damaged it.
Hence, the advent of FortectIntego aimed to address these concerns. This tool is proficient in rectifying a substantial portion of the harm incurred from infections of this nature. Blue Screen errors,[3] system freezes, registry issues, and impaired DLL files can render a computer utterly nonfunctional. Through the application of this maintenance utility, the need for a full Windows reinstallation can be avoided.
File recovery options
The ability of anti-malware solutions to restore files is a common misperception; however, this is not how they were designed to work. Security programs basically work to find and remove harmful files and suspicious processes from your system. In reality, the recovery of files depends completely on having access to specialist software or a decryption key that is only available to hackers.
In scenarios where data was not previously backed up, the potential for permanent file loss exists. While resorting to data recovery software is an option, third-party applications are not universally equipped to decrypt files. We recommend, nonetheless, giving this avenue a try. It's important to preface this endeavor by duplicating the corrupted files and transferring them onto a USB flash drive or another storage medium. Moreover, exercise caution – only proceed with this method if you have successfully eradicated the Allahu Akbar ransomware from your system.
Before you begin, several pointers are essential while dealing with this situation:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
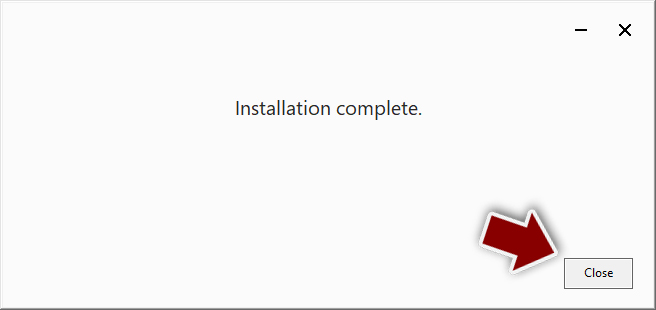
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.
- Follow on-screen instructions to install the software.
![Install program Install program]()
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.
![Select what to recover Select what to recover]()
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
![Recover files Recover files]()
Getting rid of Allahu Akbar virus. Follow these steps
Isolate the infected computer
Some ransomware strains aim to infect not only one computer but hijack the entire network. As soon as one of the machines is infected, malware can spread via network and encrypt files everywhere else, including Network Attached Storage (NAS) devices. If your computer is connected to a network, it is important to isolate it to prevent re-infection after ransomware removal is complete.
The easiest way to disconnect a PC from everything is simply to plug out the ethernet cable. However, in the corporate environment, this might be extremely difficult to do (also would take a long time). The method below will disconnect from all the networks, including local and the internet, isolating each of the machines involved.
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
If you are using some type of cloud storage you are connected to, you should disconnect from it immediately. It is also advisable to disconnect all the external devices, such as USB flash sticks, external HDDs, etc. Once the malware elimination process is finished, you can connect your computers to the network and internet, as explained above, but by pressing Enable instead.
Find a working decryptor for your files
File encryption is a process that is similar to applying a password to a particular file or folder. However, from a technical point of view, encryption is fundamentally different due to its complexity. By using encryption, threat actors use a unique set of alphanumeric characters as a password that can not easily be deciphered if the process is performed correctly.
There are several algorithms that can be used to lock data (whether for good or bad reasons); for example, AES uses the symmetric method of encryption, meaning that the key used to lock and unlock files is the same. Unfortunately, it is only accessible to the attackers who hold it on a remote server – they ask for a payment in exchange for it. This simple principle is what allows ransomware authors to prosper in this illegal business.
While many high-profile ransomware strains such as Djvu or Dharma use immaculate encryption methods, there are plenty of failures that can be observed within the code of some novice malware developers. For example, the keys could be stored locally, which would allow users to regain access to their files without paying. In some cases, ransomware does not even encrypt files due to bugs, although victims might believe the opposite due to the ransom note that shows up right after the infection and data encryption is completed.
Therefore, regardless of which crypto-malware affects your files, you should try to find the relevant decryptor if such exists. Security researchers are in a constant battle against cybercriminals. In some cases, they manage to create a working decryption tool that would allow victims to recover files for free.
Once you have identified which ransomware you are affected by, you should check the following links for a decryptor:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

If you can't find a decryptor that works for you, you should try the alternative methods we list below. Additionally, it is worth mentioning that it sometimes takes years for a working decryption tool to be developed, so there are always hopes for the future.
Create data backups to avoid file loss in the future
One of the many countermeasures for home users against ransomware is data backups. Even if your Windows get corrupted, you can reinstall everything from scratch and retrieve files from backups with minimal losses overall. Most importantly, you would not have to pay cybercriminals and risk your money as well.
Therefore, if you have already dealt with a ransomware attack, we strongly advise you to prepare backups for future use. There are two options available to you:
- Backup on a physical external drive, such as a USB flash drive or external HDD.
- Use cloud storage services.
The first method is not that convenient, however, as backups need to constantly be updated manually – although it is very reliable. Therefore, we highly advise choosing cloud storage instead – it is easy to set up and efficient to sustain. The problem with it is that storage space is limited unless you want to pay for the subscription.
Using Microsoft OneDrive
OneDrive is a built-in tool that comes with every modern Windows version. By default, you get 5 GB of storage that you can use for free. You can increase that storage space, but for a price. Here's how to setup backups for OneDrive:
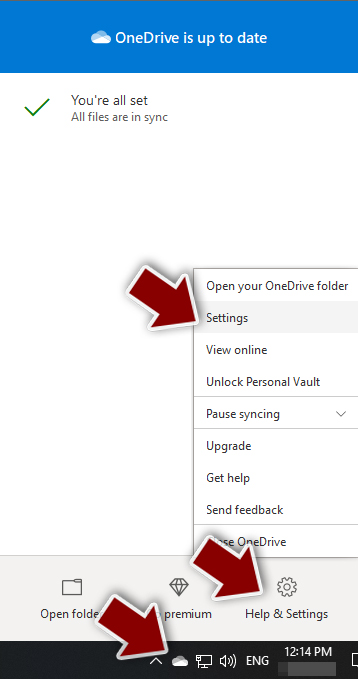
- Click on the OneDrive icon within your system tray.
- Select Help & Settings > Settings.

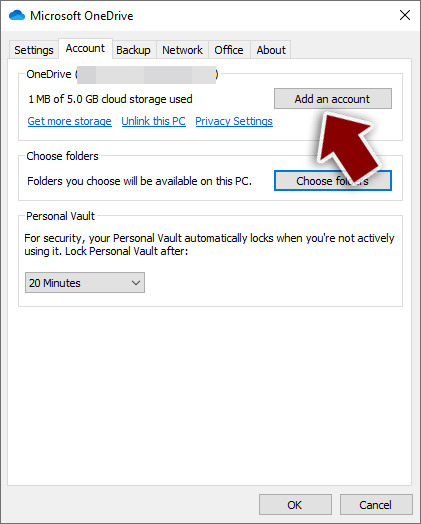
- If you don't see your email under the Account tab, you should click Add an account and proceed with the on-screen instructions to set yourself up.

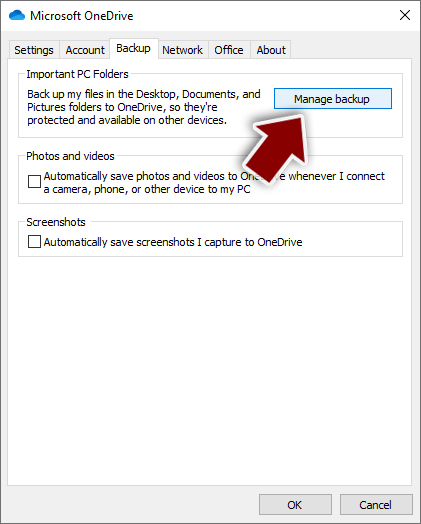
- Once done, move to the Backup tab and click Manage backup.

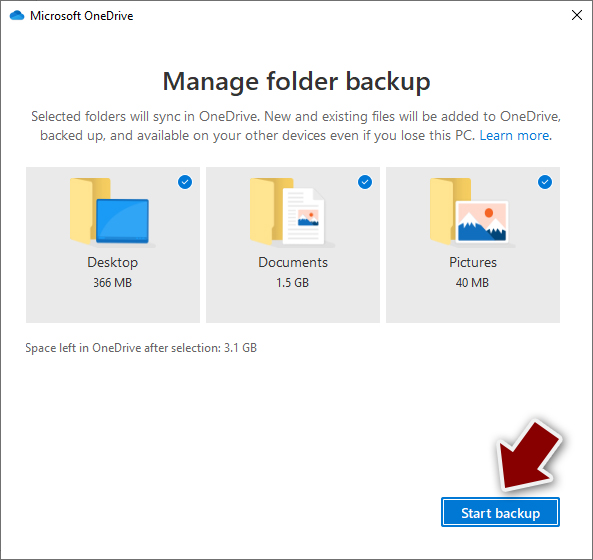
- Select Desktop, Documents, and Pictures, or a combination of whichever folders you want to backup.
- Press Start backup.

After this, all the files that are imported into the above-mentioned folders will be automatically backed for you. If you want to add other folders or files, you have to do that manually. For that, open File Explorer by pressing Win + E on your keyboard, and then click on the OneDrive icon. You should drag and drop folders you want to backup (or you can use Copy/Paste as well).
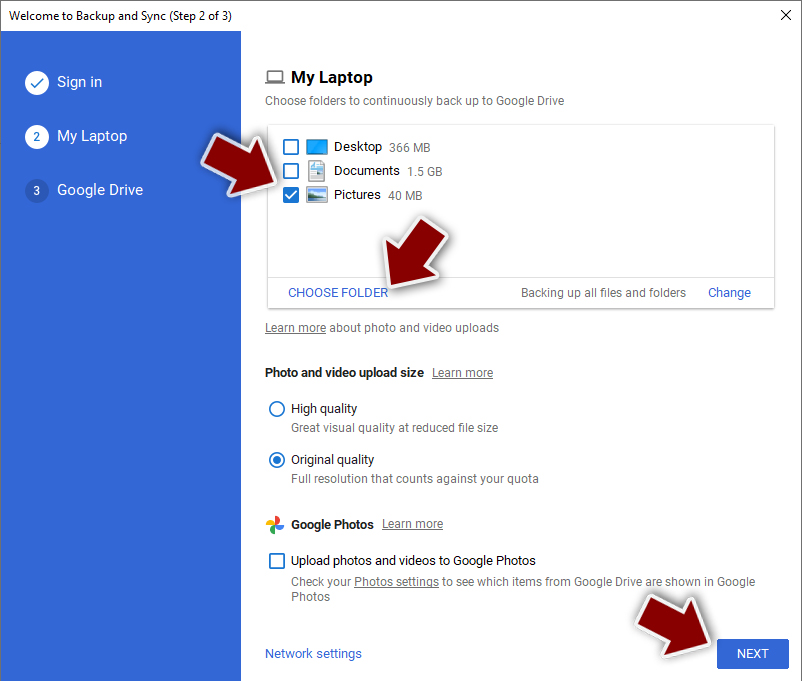
Using Google Drive
Google Drive is another great solution for free backups. The good news is that you get as much as 15GB for free by choosing this storage. There are also paid versions available, with significantly more storage to choose from.
You can access Google Drive via the web browser or use a desktop app you can download on the official website. If you want your files to be synced automatically, you will have to download the app, however.
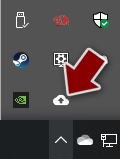
- Download the Google Drive app installer and click on it.

- Wait a few seconds for it to be installed.

- Now click the arrow within your system tray – you should see Google Drive icon there, click it once.

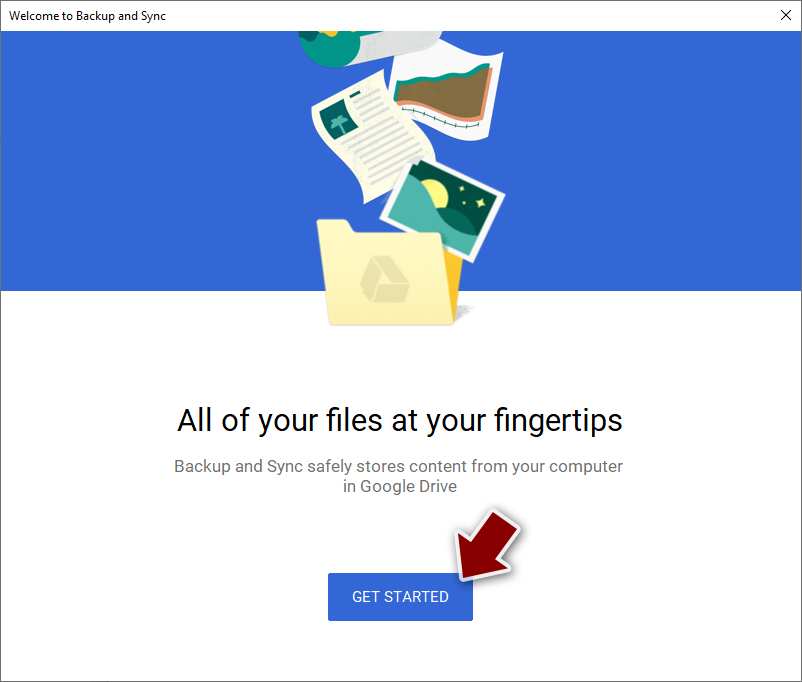
- Click Get Started.

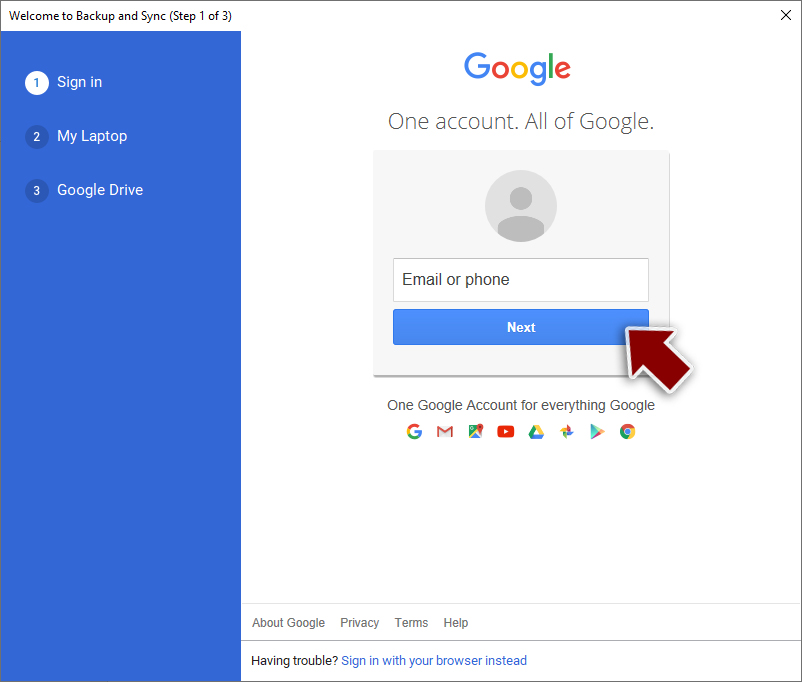
- Enter all the required information – your email/phone, and password.

- Now pick what you want to sync and backup. You can click on Choose Folder to add additional folders to the list.
- Once done, pick Next.

- Now you can select to sync items to be visible on your computer.
- Finally, press Start and wait till the sync is complete. Your files are now being backed up.
Report the incident to your local authorities
Ransomware is a huge business that is highly illegal, and authorities are very involved in catching malware operators. To have increased chances of identifying the culprits, the agencies need information. Therefore, by reporting the crime, you could help with stopping the cybercriminal activities and catching the threat actors. Make sure you include all the possible details, including how did you notice the attack, when it happened, etc. Additionally, providing documents such as ransom notes, examples of encrypted files, or malware executables would also be beneficial.
Law enforcement agencies typically deal with online fraud and cybercrime, although it depends on where you live. Here is the list of local authority groups that handle incidents like ransomware attacks, sorted by country:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

If your country is not listed above, you should contact the local police department or communications center.
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Macro malware. Microsoft. Security Intelligence Blog.
- ^ Georgina Torbet. 5 Security Reasons Not to Download Cracked Software. Makeuseof. Technology Blog.
- ^ Chris Hoffman. Everything You Need To Know About the Blue Screen of Death. Howtogeek. Tech Reviews.