Biteg.xyz referral spam (Free Instructions) - Tutorial
Biteg.xyz referral spam Removal Guide
What is Biteg.xyz referral spam?
Learn how Biteg.xyz referral spam affects Google Analytics data
Biteg.xyz referral spam is a type of fake traffic that appears in your Google Analytics[1], which is also frequently identified as “ghost spam.” It doesn’t damage your website in any way but also doesn’t add anything useful because the website that is presented as referrer doesn’t actually drive traffic to your website. It is quite new and confusing way to attract traffic to websites that belong to an infamous spammer known as Vitaly Popov[2]. He is a creator of such bogus sites such as ilovevitaly.com, o-o-8-o-o.com, lifehacĸer.com and Secret.ɢoogle.com. The spammer seems to be obsessed with the idea to smash Google’s popularity into pieces[3]. The scammer has discovered a way to insert fake referral URLs into webmasters’ Google Analytics to make people think that certain website is driving traffic to their sites, while in reality, they do not deliver any additional traffic. The point of injecting such fake data into Google Analytics is that people are curious and most likely they will click on an unknown domain that ostensibly drives traffic to their websites. This way, the spam imitates traffic while it actually attracts it to a particular website using Google Analytics. In this article, we will describe how can your remove Biteg.xyz referral spam virus and make your Analytics data accurate again. 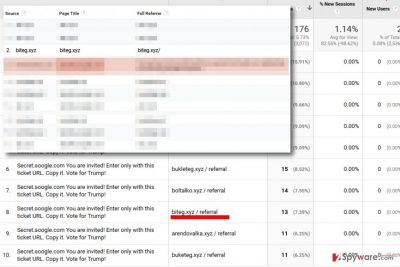
Biteg.xyz referrer spam is bad because it prevents you from seeing actual statistics, which can result in bad decisions regarding your site’s improvement. It is a well-known fact that fake traffic is generated by bots meanwhile real traffic comes from people who actually visit your website[4]. Referral spam can be recognized from 100.00% indicator in bounce rate and new sessions fields. If you noticed suspicious new sources that unexpectedly started driving traffic to your website, do not rush to click on them. These URLs can be dangerous, and you might end up installing a dangerous spyware or malware type program on the system. Therefore, if the suspicious URLs started emerging in Google Analytics, do not waste any more time and use the removal tutorial provided below to remove Biteg.xyz referral spam immediately.

Reasons why referral spam targets you
If you had a chance to encounter referral spam, you probably want to know why did you become a target. The reason why people become targets is simply spammers’ greed to make money in quite unfair ways[5]. Once you click on the link in your GA, you will reach a website controlled by a spammer. Most of Vitaly’s websites cause redirects to AliExpress or Alibaba websites, and once you buy something there, he gets a commission. You can also experience redirects to dangerous websites. Therefore, we recommend you to ignore shady URLs that mess up your GA data and take actions to remove Biteg.xyz spam from it.
Learn to remove Biteg.xyz referral spam from Google Analytics
The guide provided below explains how to block Biteg.xyz referral spam so that it would never emerge in your Analytics reports again. Follow the steps carefully and do not make mistakes such as creating a referral exclusion list. The guide we prepared can be used to remove all kinds of Google Analytics spam. You will need to create a filter for ghost spam, crawler spam, and filter for other spam types, such as language spam.
We will start by creating a valid hostname filter:
- First of all, find a list of your hostnames. Go to Network Report and select Audience. Then click on Technology to see hidden options and select Network.
- Click Hostname next to Primary Dimension section. Then, make a list of all important host names provided there. Do not include websites that you do not control, for example, bbc.com or google.com. Include only those that have added tracking code. Examples of such websites can be Youtube, Bing Translate, Paypal, etc.
- Create a list of hostnames by separating each of them with | character. Make sure you insert \ before dots and hyphens in URLs you collected, for example, youtube\.com|[next hostname here]|
- Don’t leave any spaces. If you want, use this filter in a test view for a few days to be sure that you’re not losing any valid data.
- Go to GA > Admin Tab. Choose a view where you want to enable the filter. Under the View column, select Filters and click + Add Filter. Entitle the filter as Valid Hostnames.
- Choose Custom for the Filter Type. Select Include option and then Hostname. You will see a Filter Pattern box, and this is where you need to enter the list of valid hostnames you created.
- Save. Do not forget to update the list whenever you add tracking ID to new domains or services.
Create a Filter for Crawler Spam:
- Go to Admin Tab. Under VIEW column, choose Filters and click +Add Filter.
- Entitle it as Crawler Spam.
- Choose Custom Filter type and opt for Exclude.
- In Filter Field, choose Campaign Source.
- In Filter Pattern, paste this expression:
(best|dollar|success|top1)\-seo|(videos|buttons)\-for|anticrawler|^scripted\.|semalt|forum69|7makemon|biteg|sharebutton|ranksonic|sitevaluation|dailyrank|vitaly|profit\.xyz|rankings\-|dbutton|uptime(bot|check|\.com) - Save.
To create a filter for Language Spam, see a tutorial provided in a post about Secret.ɢoogle.com referral spam. An alternative Byteg referral spam removal guide can be found here.
How to prevent from getting spam tools
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Referer spam. Wikipedia. The Free Encyclopedia.
- ^ Joseph Cox. This Russian Is Spamming Google Analytics to Show His Support for Trump. Motherboard. Multi-Platform, Multimedia Publication, Relying on Longform Reporting, In-Depth Blogging, and Video and Film Production.
- ^ Google Is Battling a Russian Spammer Over the Use of the Letter 'G'. Motherboard. Multi-Platform, Multimedia Publication, Relying on Longform Reporting, In-Depth Blogging, and Video and Film Production.
- ^ Dave Buesing. What To Do About a Fake BS Surge of Google Analytics Visits. Dave Buesing website. SEO, Online Marketing, and General Writing Thoughts.
- ^ Georgi Georgiev. Google Analytics Referral Spam Explained in 5 minutes – Infographic. Analytics-Toolkit Blog. Blog for Web Analytics, Statistics and Data-Driven Internet Marketing.
