Carenotifsolution.xyz ads (fake) - Free Instructions
Carenotifsolution.xyz ads Removal Guide
What is Carenotifsolution.xyz ads?
Carenotifsolution.xyz ads bring users misleading and even dangerous alerts to a computer screen

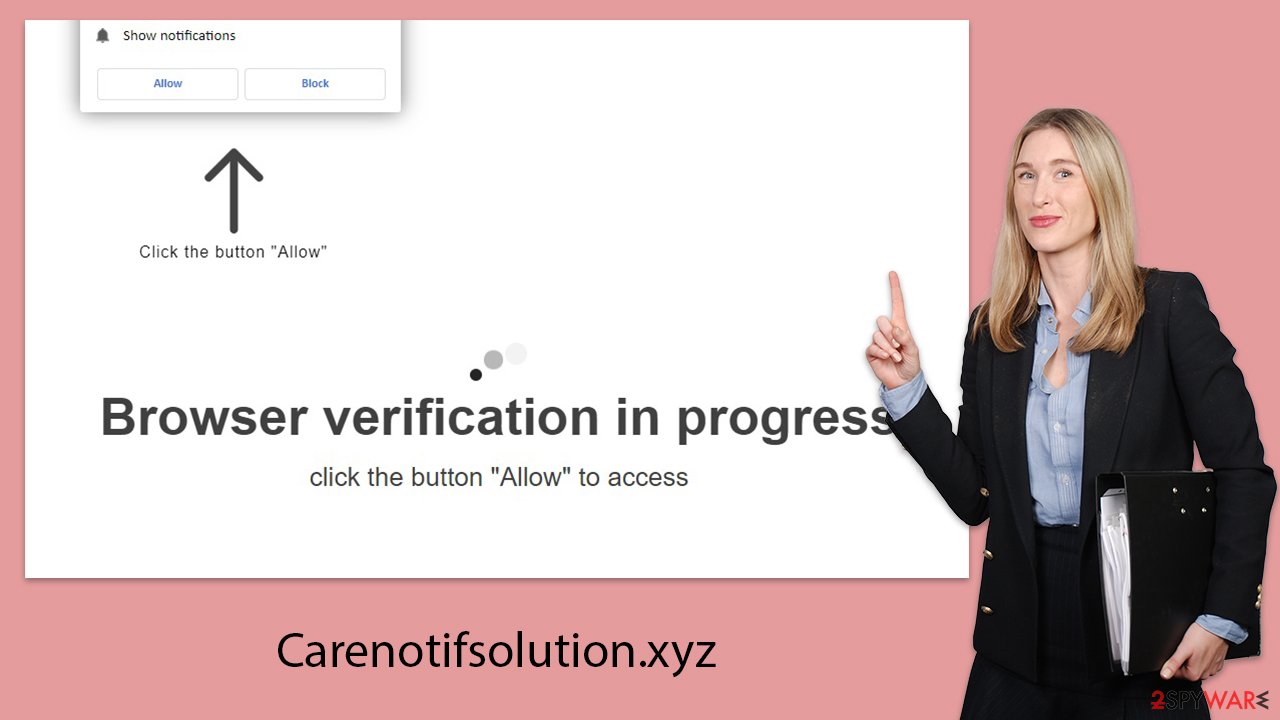
Carenotifsolution.xyz is recognized for orchestrating an online scheme designed to trick individuals into enabling push notifications. This maneuver permits the site to flood the user's desktop with unwelcome ads. Many find themselves navigating to Carenotifsolution.xyz by accident, usually triggered by a misclick on a dubious link during their internet explorations. Upon arrival, visitors encounter a cleverly disguised invitation encouraging them to click the “Allow” button, misleadingly suggested to fulfill a harmless function.
Falling for this trick leads to the relentless display of Carenotifsolution.xyz advertisements. These ads disrupt the user's digital activities, popping up unexpectedly regardless of what the user is doing or the applications they are running. The primary issue with these notifications is the potentially harmful content they disseminate, including schemes to phish for personal information, false virus alerts, bogus contest winnings, and other forms of deceit.
Users are strongly advised against interacting with any content or links emanating from this suspect site. To safeguard one's online privacy and secure personal information, it is crucial to follow certain measures to halt these invasive notifications effectively.
| Name | Carenotifsolution.xyz |
| Type | Push notifications, ads, pop-ups, scam |
| Distribution | After you click the “Allow” button within the prompt upon site entry |
| Symptoms | Pop-ups show up regularly on the screen – these ads often include inappropriate, scam, phishing, or other similar content |
| Risks | You might suffer from monetary losses, install malware or potentially unwanted programs, or disclose sensitive data to cybercriminals |
| Termination | Access browser settings to stop intrusive push notifications. After that, make sure that your system is not infected with adware or malware – scan it with SpyHunter 5Combo Cleaner |
| Recovery | To make sure that third parties can no longer track your online activities, we suggest clearing browser caches and other leftover PUP files with FortectIntego |
Scammers use legitimate premises for malicious purposes
Carenotifsolution.xyz is cleverly engineered to surprise visitors, drawing them into a carefully orchestrated scam designed to trick individuals into activating unwanted notifications on their devices.
Below are some common deceptive prompts used by Carenotifsolution.xyz to trick visitors into clicking the “Allow” button:
- “Click Allow to confirm that you are not a robot.”
- “Can't play this video! Perhaps your browser doesn't allow video playback. Please click the Allow button to watch the video.”
- “Click 'Allow' to win the prize and get it in our shop!”
- “If you are 18+, click Allow.”
- “Your file is ready to download – press Allow to continue.”
These messages are ingeniously designed to play on users' curiosity, urgency, or sense of necessity, making the request seem harmless or necessary. It's crucial to understand that these are manipulative tactics intended to entice users into enabling the site's intrusive push notifications.
Falling for this trick results in Carenotifsolution.xyz gaining permission to send direct push notifications laden with intrusive and potentially malicious advertisements to the user's device. These notifications can pop up at any moment, disrupting online activities and exposing users to risky content. Recognizing the strategy behind this deceit is key to avoiding the traps laid out by such deceptive websites.
Dangers of allowing notifications from a malicious website
Upon enabling notifications from Carenotifsolution.xyz, individuals may be overwhelmed by a deluge of unsolicited push notifications as long as their browser remains open. This situation creates an avenue for scammers to bombard users with an array of advertisements, thereby generating income for themselves.
However, the credibility of these advertisements often leaves much to be desired. Rather than affiliating with legitimate advertising networks, the entities behind Carenotifsolution.xyz tend to push advertisements that are misleading or downright harmful, taking various guises:
- Get-rich-quick scams
These advertisements lure individuals with the promise of significant financial gain from minimal investment in very little time. They often use fabricated endorsements from celebrities or counterfeit social proof to entice unsuspecting victims into their scams. - Fake malware infection alerts
Certain ads might wrongfully convince users that their devices are infected with viruses and urgently recommend their anti-malware solutions. These ads cleverly imitate reputable cybersecurity firms to trick users into downloading harmful software. - Bogus Gift Cards and Giveaways
Some advertisements tempt users with the chance to win lavish prizes from well-known companies like Amazon or Google. However, these are mainly tactics to gather personal information, potentially leading to identity theft or further cyber fraud.
The cunning strategies employed in the ads from Carenotifsolution.xyz can expose users to a variety of risks, including financial loss and privacy breaches. Users must remain vigilant, avoiding these pitfalls and being judicious when giving out notification permissions, especially from questionable sources.
For individuals who have already granted permissions to such sites and are now facing unwanted consequences, it is recommended to quickly withdraw these permissions as detailed in the next section, and run a comprehensive system check with a trusted antivirus program to ensure the integrity of their systems.
Remove threats from your system
Navigating the web, users may unintentionally land on phishing sites through various channels, yet one of the less obvious culprits behind these redirects is adware. Adware, classified as a Potentially Unwanted Program (PUP), bombards users with unsolicited ads and reroutes them to dubious sites like Carenotifsolution.xyz. This software often slips onto systems unnoticed, bundled with free applications or via other shady avenues, making some individuals oblivious to its existence on their devices.
To safeguard your device, conducting a thorough scan using a robust anti-malware solution, like SpyHunter 5Combo Cleaner or Malwarebytes, comes highly recommended. It's crucial to have the latest malware definitions updated in your chosen tool to enhance its detecting and cleaning capabilities.
Following the identification and elimination of any adware or malware, employing a dedicated utility FortectIntego to purge your browsers of cookies and various tracking mechanisms is wise. This step not only cleanses your browser of remnants but also assists in rectifying any damage inflicted by the malware, adding an extra shield of protection and ensuring your digital well-being.
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.






