Citadel virus (Virus Removal Instructions) - updated Mar 2021
Citadel virus Removal Guide
What is Citadel virus?
Citadel virus is a notorious banking trojan that stole the credentials of millions and caused immense financial losses
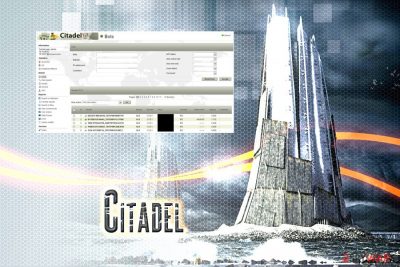
Citadel trojan is a data-stealing malware that was first spotted in the wild back in 2011 and was based on the Zeus virus. Its impressive keylogging and evasion capabilities allowed its developer Mark Vartanyan, also known as “Kolypto,” and his affiliates to harvest the login credentials from the most popular password managers, including Keepass or Password Safe.
During its successful years of operation, Citadel trojan managed to infect over 11 million computers worldwide, which resulted in $500 million worth of damage to users.[1] Fortunately, with the help of combined efforts of the FBI and Microsoft, the operator was extradited to the United States in March 2017 to face criminal charges related to malware and sentenced to five years in federal prison later that year.[2]
Citadel trojan was offered on the underground forums for years and was one of the first viruses that were used for malware-as-a-service (MaaS) scheme. The affiliates used a variety of infection methods, such as Blackhole EK,[3] to infect users with a malicious payload and then included the computer network into a botnet, further proliferating malware.
| Name | Citadel virus |
| Type | Trojan |
| Stems from | Zeus banking malware |
| Developer | Mark Vartanyan or “Kolypto” |
| Start of the operation | 2011 |
| Business model | Malware-as-a-service (MaaS) |
| Capabilities | Stealing master passwords, locking users out of security sites, compiling a botnet, etc. |
| Distribution means | Exploit kits, vulnerabilities, spam emails, etc. |
| Termination | Use anti-malware software |
| System repair | Tools like FortectIntego should also help with virus damage |
While the developer Kolypto is already behind bars, it does not mean that Citadel virus is gone forever, mainly because it was operating the malware-as-a-service program. Therefore, users should beware of older threats, as the presence of a trojan can result in money loss, installation of other malicious software, or even identity theft.
Soon after the distribution of Citadel virus seized in 2016, a new version based on it was released – Atmos.[4] It was mainly developed to perform targeted attacks against banks. However, it later turned out that the malware was also used to drop TeslaCrypt ransomware,[5] initially infecting users via malicious web injects.
What's so special about the malware is that it is capable of entering the machines and idling for months, meaning that no security solutions can detect it during that time. However, the updated versions of security applications should be able to help with Citadel virus removal and prevention.

The complex nature of the trojan requires users to be extremely careful when browsing the internet, as the infection can come when its least expected. Citadel virus might be delivered using a variety of methods, so the prevalence is guaranteed.
We recommend using security solutions such as AV tools order to terminate the malicious threat and restore the computer to a working state. Remember, trojans are usually silent and do not show any signs or symptoms, so it vital to scan your device with anti-malware on a regular basis.
Prevent malware by employing adequate security options
Unlike potentially unwanted programs that are considered less harmful, various malware, including ransomware, and banking trojans are usually operated by a sophisticated criminal group. Therefore, the distribution methods of such threats are usually much more complex and advanced – it ensures the benefit of infecting millions of users. Here are a few examples of malware distribution methods:
- Exploits
- Software vulnerabilities
- Spam emails
- Web injects
- Fake updates
- Pirates software installers, etc.
Let's make it clear: having comprehensive anti-malware software installed is one of the major steps towards infection prevention. However, it is not enough just to be safe online. We can recommend trying SpyHunter 5Combo Cleaner or Malwarebytes for the proper malware termination.
You should also make sure you update your operating system along with all the installed applications as soon as new security patches are deployed. Updates can fix security flaws, which would consequently stop the trigger of the exploit, which would otherwise install malware automatically as soon as you enter the compromised site. Tools like FortectIntego can also help with malware damage.

Additionally, you should avoid torrent and crack sites that offer illegal software – these are full of malicious software and should not be tampered with.
Remove Citadel banking trojan and prevent the intrusion of other malware
Besides Citadel's capability of stealing credentials, credit card details, and operating a botnet, it was also capable of proliferating other malware. As we previously mentioned, ransomware like TeslaCrypt might be delivered – the infection that can lock personal files on the hard drive and all the connected networks. In most cases, data recovery is impossible, unless security experts come up with the decryption tool.
Therefore, manual Citadel virus removal might not be enough, as other malware might be operating in the background. We suggest you refrain from tampering with system files and rather trust comprehensive anti-malware programs to do the work automatically. Try SpyHunter 5Combo Cleaner or Malwarebytes for this.
In some cases, Citadel virus removal might be difficult as it can tamper with anti-virus software. If that is the case, you should enter Safe Mode with Networking – a safe environment that stops malware-initiated tasks from running. We explain how to enter the mode below – please check it out and perform a full system scan. You might also want to run a tool FortectIntego that repairs system files and fixes other problems for you.
Getting rid of Citadel virus. Follow these steps
Manual removal using Safe Mode
In case the malware does not let your security application function normally, access Safe Mode with Networking as explained below and complete Citadel malware removal by scanning your computer:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Citadel and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Nate Raymond. Russian sentenced in U.S. to five years prison for 'Citadel' malware. Reuters. Business & Financial News, US & International Breaking News.
- ^ Russian Citizen who Helped Develop the "Citadel" Malware Toolkit is Sentenced. Department of Justice. Official website.
- ^ Fraser Howard. Exploring the Blackhole exploit kit. Sophos. Naked Security.
- ^ Tom Spring. ZeuS Banking Trojan Resurfaces As Atmos Variant. ThreatPost. The first stop for security news.
- ^ Citadel. NJCCIC. NJ Cybersecurity & Communications integration cell.














