.code virus (Free Instructions)
.code virus Removal Guide
What is .code virus?
.code file extension virus: highly dangerous and bothersome
There has been a tendency to launch a new type of ransomware which attach a certain extension to the encrypted files. Thus, .code virus is one of such threats. Like other ransomware-viruses, it sneaks into the computer, locks personal information and requires a sum of money in exchange. It is known that it demands a relatively astounding amount of money. If you happen to fall into the victim list, do not rush to pay the money. You might end up with no recovered data and money. Thus, you need to collect yourself and start thinking about .code virus removal.
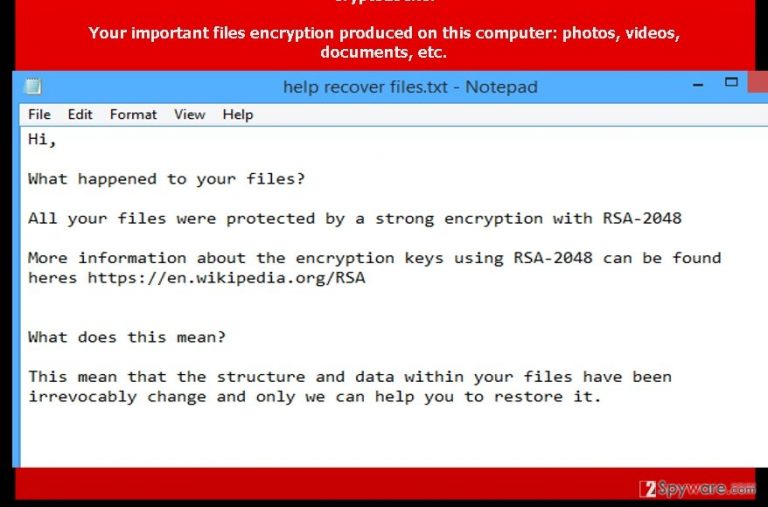
Regarding the amount of ransom, the virus can be treated as relatively greedy. After the ransomware sneaks into your computer, it demands more than $2000 which equal 5 Bitcoins. Moreover, the virus uses common encryption method – RSA-2048 algorithm which helped hijackers create such infamous viruses as CryptoMix, Cerber, and TeslaCrypt 4.2. Furthermore, it seems that hijackers shift from using an anonymous browser to specific emails. The victims of .code file extension virus are encouraged to contact the developers using these addresses: xoomx_@_dr.com and xoomx_@_usa.com . Though such method decreases the chance of remaining anonymous, IT experts still haven’t tracked the main source domain of the spreading virus. In addition, the number of encryptable documents significantly rocketed. .code ransomware locks a number of various .doc files, odt, audio and video formats: mp3, .mp4, .avi, ns2, .ns3, .ns4, .nw.
How does the virus spread?
.code malware often is seen dispersing via infected spam attachments. The strategy of deceiving users by false invoices, trial invitations, accounts and postal notifications seems quite working. Consequently, a huge number of Internet users have been infected with .code file extension virus. Once the attachment is opened, the virus executes itself and starts scanning for the files. Depending on the size of hard drive and PC processing speed, for a while, you might not have the slightest idea that a menacing virus is misbehaving itself on the system. Later on, Help_Your_Files.txt emerges on the screen declaring of the wrongdoings of this virus. You may notice that all locked data bears .code extension. Thus, it might become tiresome activity locating the corrupted files. Though you may fall into huge desperation over the important data being encrypted, you need to calm down and think rationally. You can use data recovery programs (PhotoRec or R-studio) though they do not guarantee the information retrieval. If you think of paying the money – it is not an option. That is why it is wiser to think of the ways to remove .code virus. One of the most effective methods is to run a system scan using FortectIntego.
Is there a way to remove .code virus?
There are two possibilities to terminate the ransomware. The first encompasses manual elimination. You can either search for the instructions online or use the ones provided below. If you do not trust yourself on following the instructions correctly, then save time and energy by installing ransomware removal tool. The program is specifically designed for performing .code ransomware removal. It will ensure that no related files, which might cause re-infection process, are left. The anti-spyware program is also apt in locating trojans and malware which are associated with .code virus.
Getting rid of .code virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove .code using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of .code. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from .code and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.







