DKOM.doublepulsar (Virus Removal Guide) - Free Instructions
DKOM.doublepulsar Removal Guide
What is DKOM.doublepulsar?
DKOM.doublepulsar – a backdoor that could be used by criminals to install more malware on your system
DKOM.doublepulsar is a computer virus that exploits out of date Windows computers. This backdoor is an advanced trojan that leaves an open gate for a hacker to connect to your PC. It was used for spreading a well-known ransomware WannaCry and accessed PCs through Windows vulnerability. It is very important to follow up with updates to avoid such infections.
DKOM.doublepulsar can collect various data, such as financial and personal info, copy/steal files, etc. It also disables security software that's installed on the computer, thus making the device unprotected. This allows the trojan to upload and install any other malicious software that it's programmed to.
While the infiltration can be entirely prevented by patching Windows with the latest version, the threat is still extremely prevalent in the wild. So if your anti-malware tool flagged it, or you see any suspicious symptoms of the infection (crashing, slower performance,errors) – you came to the right place. In this article, we explain how to remove the malware and repair corrupted system files.
| name | DKOM.doublepulsar |
|---|---|
| Type | Trojan, backdoor virus |
| Category | Malware |
| Symptoms | Most of backdoors are programmed to remain on the system undetected, so the only symptom you might see is a warning from your security software |
| possible Purposes | Stealing financial and personal data, spying through webcam and microphone, downloading/uploading files, disabling features, taking screenshots, etc. |
| Distribution | Spam emails, software bundles, deceptive ads, file-sharing platforms |
| Removal | Malicious software should be taken care of by using trustworthy anti-malware applications |
| System repair | Malware corrupts system files and settings. This impacts the system's performance by slowing it down, showing errors, and so on. To get your machine back on track, use the FortectIntego tool |
Double Pulsar was developed by the U.S. National Security Agency,[1] although it was later stolen by cybercriminals who spread the infection worldwide. Malware places a backdoor on the system and exploits a vulnerability inside the Windows kernel known as EternalBlue. In 2017, more than 200,000 computers were infected with the infamous WannaCry ransomware thanks to the usage of this backdoor, resulting in a worldwide cybersecurity disaster.
Trojans like DKOM.doublepulsar, are one of the most hazardous types of malware that are created. They can have an array of built-in functions. To name just a few:
- Copying all files on the infected machine and uploading them to a pre-determined server
- Deleting all data or some system files that would disable the machine
- Downloading and installing additional malicious software
- Displaying an abnormal amount of ads
- Disabling anti-malware software and any security-related services
- Stealing financial info, such as credit card details, logins, passwords, etc.
In the past years, an increasing number of Remote access Trojans (RATs) surfaced, which let the threat actors gain remote control over a victim's computer. That way, the hackers can infect other computers on the network or do whatever they please with the infected one.
Trojans are very hard to detect, as they can be camouflaged as a legitimate application and wait for a trigger to begin what it's developed for. That's why professional anti-malware tools such as SpyHunter 5Combo Cleaner or Malwarebytes must be installed on every computer. This type of software is designed to catch malware, just keep its virus databases up to date.
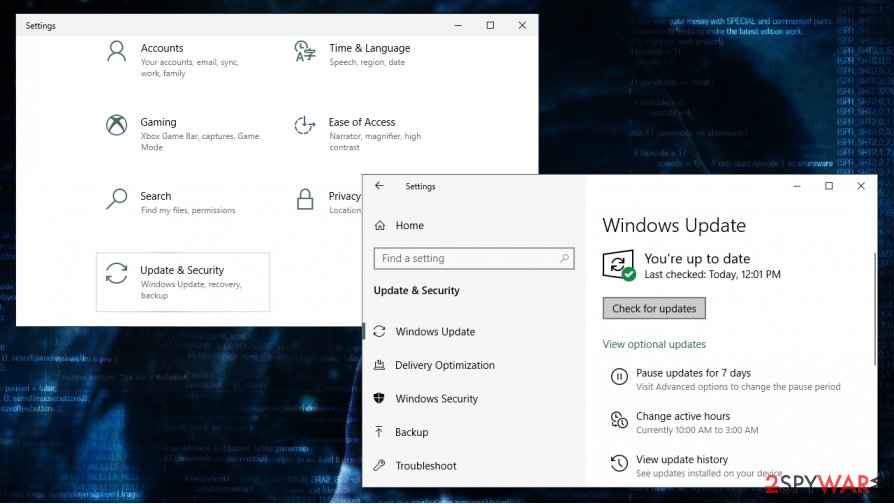
To effectively mitigate the infection and remove DKOM.doublepulsar, users need to disconnect the infected PC from the network, apply the MS17-010 Windows update, reboot the device, and then perform a full system scan with reliable anti-malware. Run the software, perform an entire system scan, and get rid of any suspicious files that the tool flags.
Malware, especially backdoors, insert themselves in the system registry and other core settings and files. That's why after DKOM.doublepulsar removal, cybersecurity experts from LesVirus.fr[2] recommend using powerful system repair tools such as the FortectIntego app to delete any new entries and correct any system irregularities.
Sneaky techniques used by trojan developers to distribute them
Trojans are spread using different techniques, but they can't execute themselves. That's why cybercriminals spread them as deceptive ads. For example, while visiting a website, a pop-up abruptly appears stating that you have a virus infection and that you need to scan your system with the advertised tool ASAP. As soon as a user downloads the software and installs it, a trojan plants roots.
Another popular way the trojans are distributed is via file-sharing platforms. Cybercriminals love to exploit the lack of end-to-end security in torrent sharing websites, where they can upload any virus and wait for a soon to be victim to download it. Malicious software is usually named as a game crack for the latest game, unlocked expensive licensed software, and in any other way that would lure someone to download it.
And last but not least – spam emails, yet another way to deliver trojans. Payload files are usually hidden either in email attachments or in hyperlinks to malicious websites. To avoid trojan infections, please refrain from clicking any deceptive ads, don't use file-sharing platforms, and don't open any phony emails and their contents.
Tutorial for DKOM.doublepulsar removal and system repair
If you feel that your computer performance is down, you see an abnormal amount of ads, new programs are installed, the internet connection is extremely slow, that might mean that your device is infected with a trojan or other kind of malware.[3] You have to take action immediately and perform DKOM.doublepulsar removal correctly.
There are several steps that you have to do in order to eliminate this backdoor fully. It consists of the following steps:
- Disconnect your PC from the network if it is connected to one.
- Restart your computer.
- Update Windows to the latest version. You can do that by right-clicking on Start and then selecting Settings > Update & Security > Windows update and clicking Check for updates.
- Wait till the system is fully updated, and patches applied.
- Reboot the machine and perform a full system scan with SpyHunter 5Combo Cleaner, Malwarebytes, or another robust security application.
Once you remove DKOM.doublepulsar from your device, you should also take care of your system stability after infection elimination. Malware is developed to disable certain features by making changes to system files and settings. You can fix all system irregularities by performing a system tune-up with powerful system repair tools such as the FortectIntego app or similar software.
Getting rid of DKOM.doublepulsar. Follow these steps
Manual removal using Safe Mode
In case you have other malware installed on your machine through the backdoor, you can use Safe Mode to eliminate all the infections without disruptions in Safe Mode:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove DKOM.doublepulsar using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of DKOM.doublepulsar. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from DKOM.doublepulsar and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting backdoors
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ DoublePulsar. Wikipedia. The free encyclopedia.
- ^ LesVirus. Lesvirus. Spyware and security news.
- ^ Roger A. Grimes. 9 types of malware and how to recognize them. Cso. Security news, features and analysis.





















