Earthheartsmith.top ads (scam) - Free Guide
Earthheartsmith.top ads Removal Guide
What is Earthheartsmith.top ads?
Earthheartsmith.top ads can bring malicious links directly to your desktop

Earthheartsmith.top is an online domain known for triggering unexpected pop-up notifications. These pop-ups often appear directly on the user's desktop, regardless of which website he is viewing. This can be confusing to many users, as persistent notifications appear to pop up without a clear source.
The root cause of these ads can usually be attributed to the user accidentally enabling push notifications from his Earthheartsmith.top. Websites often use deceptive strategies that trick users into subscribing to these notifications without fully understanding their meaning. These unwanted notifications can be delayed in onset and can cause confusion for users who have difficulty linking ads to previous actions on your site.
A significant problem with Earthheartsmith.top notifications is their intrusive nature and the potential risks they pose. These notifications aren't just annoying; These often act as a conduit for harmful content such as scams. Interacting with these notifications can expose users to malware, compromise personal information, and cause financial loss from fraudulent services and products. It is important for users to be cautious and aware of the tactics used by such websites to prevent unwanted consequences.
| Name | Earthheartsmith.top |
| Type | Ads, push notifications, pop-ups, scam |
| Distribution | The only way the ads would start being shown is by users pressing the “Allow” button within the notification prompt |
| Symptoms | Push notifications from the site show up on the desktop. These pop-ups show fake notices and push scams. Links can also lead to websites filled with malware |
| Risks | The ads shown within push notifications might include misleading messages and links to malicious websites. If clicked, you might end up infecting your system with malware, disclosing your personal information, or losing money |
| Removal | To prevent the site from displaying notifications, access the site settings section via your web browser settings – we explain how to do that below. As a precautionary measure, we recommend checking the system for adware with SpyHunter 5Combo Cleaner |
| Other tips | By cleaning web browser caches and web data, you would ensure that third parties can no longer track you – use FortectIntego for this job |
Adware infection could be the reason why you stumble upon websites like Earthheartsmith.top
Push notification scams have surged in popularity over recent years, primarily due to their effectiveness in persuading users to subscribe to push notifications. The cornerstone of this scam is directing users to a phishing site, often facilitated through insecure ad networks and websites with lax security.
Users are frequently redirected to sites like Earthheartsmith.top when they interact with links on torrent sites and similar platforms. These high-risk sites are known for deceptive elements like misleading “Download” buttons or even initiating redirects through malicious scripts when a user clicks anywhere on the page. To avoid such risks, it's advisable to steer clear of illegal or untrustworthy websites, which generally lack the robust security measures of more reputable sites.
Another common vector for these redirects is adware, often covertly installed on users' systems. This software usually enters systems through software bundles or deceptive tactics, leaving users unaware of its presence. Ensuring that no such software resides on your device is a key preventive measure.
To safeguard your system, regular scans with reputable security software like SpyHunter 5Combo Cleaner, Malwarebytes, or other robust tools are recommended. These applications are designed to eliminate adware and other malicious entities in one go. Additionally, tools like FortectIntego can assist in clearing the browser cache and addressing any system damage that might have occurred due to the infection.
Scammers use various tricks to convince users to enable push notifications
Push notifications, introduced to web browsers in 2015, are inherently benign, serving to deliver pertinent information from websites to users. For these notifications to work, users must consciously agree to receive them. Generally, reputable websites use this feature responsibly, avoiding spamming users with excessive messages or exposing them to phishing content.
However, in the case of push notification scams like Earthheartsmith.top, the situation is markedly different. These sites lack legitimate content and are entirely fraudulent. The primary objective of these scammers is to persuade users to click the “Allow” button, enabling them to later bombard them with commercial content. Users encountering these scam sites are often presented with deceptive messages like:
- If you are 18+, tap Allow
- Just one more step! Allow to continue
- Click Allow if you are not a robot
- To access the video, click 'Allow'
- Click Allow to win a prize and get it in our shop!
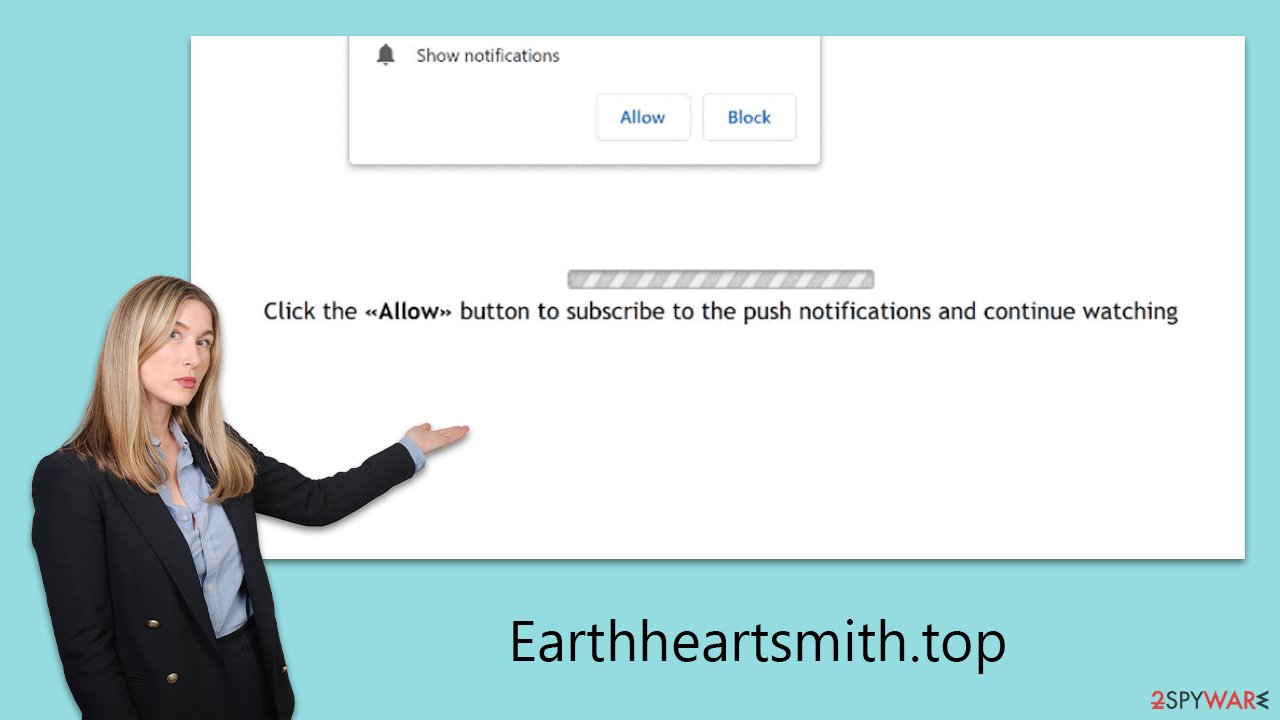
These prompts are, at best, misleading. They disguise the “Allow” button as a tool for age verification or as a confirmation that the visitor is not a robot, employing social engineering tactics that exploit familiar online interactions. However, their context and purpose are entirely different from legitimate requests. It's important to note that these types of alerts could also be employed by other fraudulent websites.
Regrettably, scammers prioritize their own financial gain over the well-being and browsing experience of users. Their aim is to generate revenue from the ads displayed in these notification prompts. As these individuals often don't ensure the security or credibility of their advertising networks, users are likely to encounter low-quality, misleading, or even harmful ads.
Remove Earthheartsmith.top ads
Numerous individuals may find themselves unsure about how to eliminate unwanted notifications from Earthheartsmith.top, primarily because they were deceived into subscribing.
Given that even on legitimate websites, most users do not intentionally opt into these notifications, they often lack knowledge on how to reverse this unwelcome activity. Fortunately, the process to rectify this is quite straightforward and involves a few steps within the browser settings. Here's how to do it:
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.






