Freeadvworld.com ads (Free Instructions)
Freeadvworld.com ads Removal Guide
What is Freeadvworld.com ads?
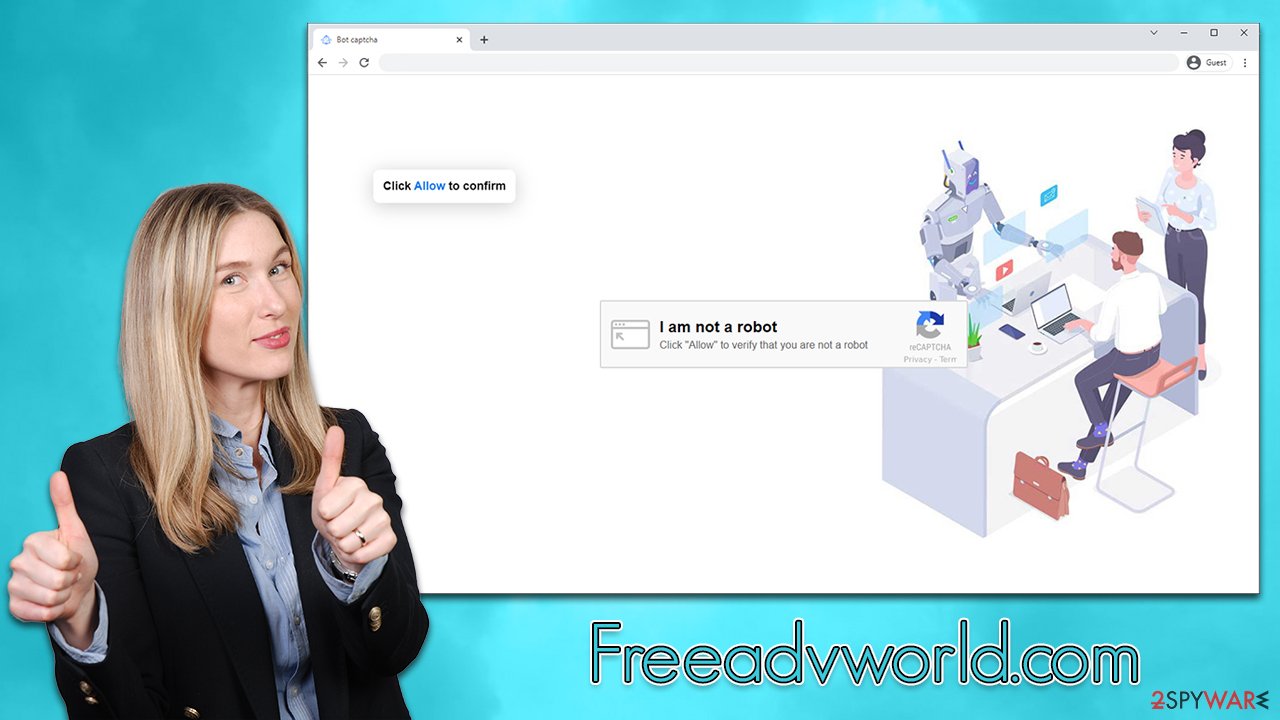
Freeadvworld.com is a fake website that tricks users into subscribing to push notifications

Freeadvworld.com might show up on your browser unexpectedly – usually after you click a booby-trapped link somewhere else. The behavior is more prevalent on websites of dubious origin, such as those that distribute torrent files and cracked software. Alternatively, adware[1] could also be the cause of abrupt redirects to suspicious websites, accompanied by an increased amount of pop-ups, banners, in-text links, auto-play, and other intrusive ads.
After being redirected, you might be asked to confirm that you are not a robot or that there is content to be explored – all you have to do is click the “Allow” button within the pop-up window at the top-left of the page. If you do so, you will allow Freeadvworld.com to send you notifications at any point, irrespectively of which websites you would be visiting at the time.
Only sometime later you would notice that your desktop is getting filled with suspicious pop-ups, which show various misleading information. For example, you might be told that your computer has been infected with viruses and that you need to install an alleged removal tool to get rid of it. Do not interact with Freeadvworld.com ads, or you might be led to malicious websites, followed by monetary losses or malware infections. Use the guide below to get rid of them instead.
| Name | Freeadvworld.com |
| Type | Push notifications, ads, scam, pop-ups |
| Distribution | Desktop notifications start showing up at random times after clicking on the “Allow” button upon the site entry |
| Symptoms | Pop-up notifications show up on the desktop at random times – the ads often include inappropriate, scam, phishing, or other similar content |
| Risks | If you click on links provided by the website, you might end up infecting your system with malware/PUPs, disclosing your personal information to cybercriminals, or losing money for useless services |
| Removal | To stop the intrusive pop-ups, you need to access the settings section of your browser. You should also check your system with security software to eliminate adware and malware |
| Additional tips | It is important to clean your browsers after removing potentially unwanted programs from your system – use FortectIntego for quick and reliable results |
Scam methods
Push notifications are not well understood by many people because of their relatively recent arrival on desktop browsers. While many users have already seen requests to enable push notifications, they are usually not used in this context – where the push notification prompt's functionality is presented as something entirely different.
In fact, websites like Freeadvworld.com have no content in them whatsoever – they simply show fake notifications to make people subscribe and then usually redirect to other malicious pages. These are a few examples of messages you may encounter on push notifications scam sites:
- Click “Allow” if you are not a robot
- Just one more step! “Allow” to continue
- Click the Allow button to subscribe to notifications and continue watching
- Press “Allow” to watch the video
- The download is ready! Click Allow to download the file
Thousands of push notification scam websites operate in the same manner – Directoffers.xyz, Womenlifewellness.com, or Greaterfiledownload.com are just a few examples. They even use the same pictures and messages to convince users to subscribe. Thus, if you see similar requests in the future, make sure you ignore them and leave the page by closing down the tab without interacting with its contents.
Removal of intrusive push notifications
It is important to note that Freeadvworld.com ads are not a symptom of a computer infection – it is a result of you letting the site send you information via a legitimate browser feature. However, the possibility of adware or other malware infection should still be considered, as those infected are more likely to encounter potentially dangerous or phishing[2] websites while browsing the web. This is especially important if you also notice the increased activity of ads on all visited websites.
Keep in mind that malware can be difficult to find and eliminate manually, as it might use obfuscation and resistance techniques, making its removal without adequate tools rather difficult. Therefore, before you proceed with the removal of unwanted push notifications, we recommend you scan your system with SpyHunter 5Combo Cleaner, Malwarebytes, or another powerful security software.
After that, you should also use FortectIntego to clean your browsers and leftover files accordingly. This way, you can be sure that cookies[3] aren't used to track your online activities anymore, as they might remain on the system for years if not removed.
To remove Freeadvworld.com pop-ups, you should access your browser settings and then go to the site settings category – you can stop any website there from sending you push notifications.
Google Chrome
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off position).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Adware. Investopedia. Source of financial content on the web.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ HTTP cookie. Wikipedia. The free encyclopedia.






