Gemheartartisan.top ads (scam) - Free Instructions
Gemheartartisan.top ads Removal Guide
What is Gemheartartisan.top ads?
Gemheartartisan.top – a scam website you should never engage with
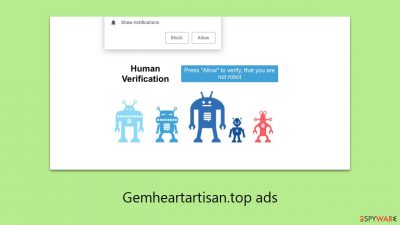
Gemheartartisan.top is an illegitimate website that has been crafted by cybercriminals to mislead internet users. The main tactic used by these scammers is to persuade individuals to subscribe to push notifications under the guise of a routine verification process. This is done by prompting users to click on an “Allow” button, which is misleadingly presented as a necessary step.
Users typically encounter Gemheartartisan.top through unexpected pop-up notifications that appear over other applications, not just within the web browser. This behavior is not only annoying but potentially harmful. Clicking on these pop-ups can lead to redirection to harmful websites. On such sites, users might be conned into paying for services they don't need, downloading malicious software, or unintentionally sharing personal information with untrustworthy sources.
It is strongly advised to ignore these pop-ups and to deactivate Gemheartartisan.top push notifications through the settings of the web browser. Users who have interacted with these notifications should be aware of the risks of phishing and other online threats. To ensure safety, it's recommended to inspect the device for any signs of adware or malware infections.
| Name | Gemheartartisan.top |
| Type | Push notifications, pop-ups, ads, scam |
| Distribution | When the user clicks Allow in the push notification, the website has immediate access to send push notifications |
| Symptoms | Shown pop-ups incorporate fake notices and push scams. Links can also lead to websites filled with malware |
| Risks | You might suffer from monetary losses, install malware or potentially unwanted programs, or disclose sensitive data to cybercriminals |
| Removal | Access browser settings to stop intrusive push notifications. After that, make sure that your system is not infected with adware or malware – scan it with SpyHunter 5Combo Cleaner |
| Other tips | We recommend using FortectIntego to fix any virus damage that might have occurred due to a system infection. The app can also remove various trackers for better privacy |
Scam techniques used
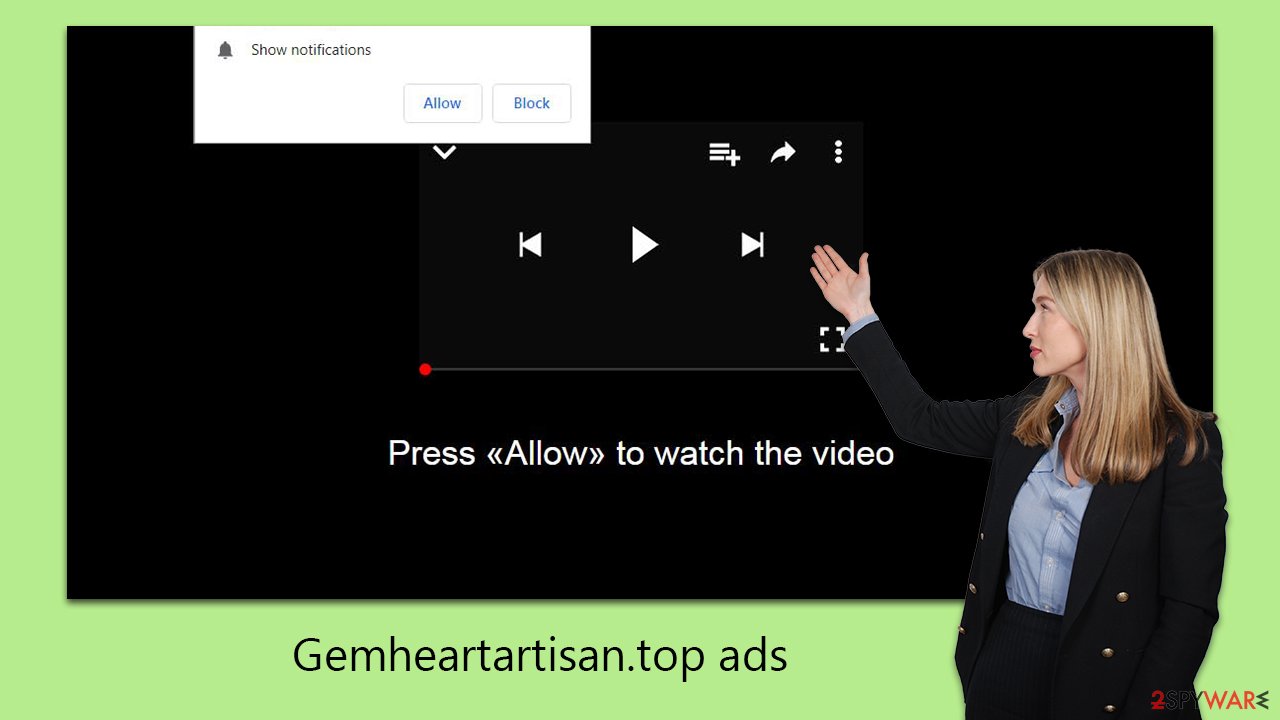
Push notifications are a feature that can be integrated into websites through an application programming interface (API). When visiting a website, users may receive a prompt to enable these notifications, unless they have previously opted out. However, websites like Gemheartartisan.top can employ deceptive backgrounds, leading to confusion about the nature of the notification prompt, and possibly resulting in users inadvertently enabling misleading notifications.
Scammers use various tactics to trick users into enabling notifications. Upon visiting the site, they may encounter messages such as:
- Press “Allow” to watch the video
- Click Allow to confirm that you are not a robot
- Click Allow to start downloading
- If you are 18+, click Allow
- Click “Allow” to win the prize and get it in our shop!
These messages are designed to mimic legitimate website interactions. Users are often familiar with requests to verify they are not bots, a common security measure to prevent DDoS attacks. Similarly, age verification prompts are widely used. Sometimes, the lure of exclusive content or rewards can also entice users.
It's important to recognize that websites like Gemheartartisan.top lack real value and are not worth engaging with. If you have accidentally enabled push notifications from such a site, it is essential not to interact with the pop-ups. As long as these pop-ups are not clicked on or interacted with, the risk remains minimal.
Dangers of engaging with malicious ads
Push notifications from dubious websites, although seemingly appearing out of nowhere, are actually triggered by previously given consent, which may have been provided unknowingly or by mistake. If you are receiving unexpected pop-ups from Gemheartartisan.top, it implies that permission for these notifications was granted at some point.
These notifications can appear regardless of the websites being visited or even when the browser is not actively being used. They often show up as pop-ups in certain areas of the screen, the location of which is dependent on the operating system in use.
The key concern with these notifications is the potentially harmful content they bring. Users might see deceptive advertisements, such as enticing but fraudulent work-from-home opportunities that require an initial payment. Many individuals fall victim to these scams, later realizing that the promised jobs do not exist.
Additionally, some notifications are designed to mimic security alerts, falsely claiming that the system is infected and suggesting the download of protective software. These are often tactics used in tech support scams, leading users to inadvertently install adware or other unwanted software.
Removing unwanted pop-ups
If you have inadvertently activated push notifications from a site like Gemheartartisan.top, the situation is manageable as long as you avoid interacting with any of the ads or links presented in these notifications. By not engaging with these alerts, you significantly reduce the risk of harm. If you're unsure about how to turn off push notifications from a specific website, here are step-by-step instructions for different web browsers to help you through the process:
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
Checking the system for infection
It is crucial to inspect your system for possible infections, which often take the form of adware. Adware is a common type of software that generates revenue for its creators through aggressive advertising. It often appears as a somewhat legitimate applications, especially on platforms that distribute freeware.
While some unwanted programs can be manually removed by checking and deleting browser extensions and installed programs, many malware varieties can evade the detection of average computer users. Therefore, it is recommended to conduct a thorough system scan using specialized tools to automatically identify and remove all infections and malicious files – SpyHunter 5Combo Cleaner or Malwarebytes could do a good job here.
In addition to system scanning, it's vital to ensure that your browsers are free from any unwarranted tracking activities. This involves clearing cookies and other residual files. For an efficient and thorough clean-up, consider using a PC repair and maintenance utility FortectIntego. Such software not only helps in repairing damages caused by malware but also addresses common computer problems that can lead to various stability issues.
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.






