Nature Of The World Extension browser hijacker (virus) - Free Guide
Nature Of The World Extension browser hijacker Removal Guide
What is Nature Of The World Extension browser hijacker?
Nature Of The World Extension is a bogus app designed by crooks to spam ads and collect data
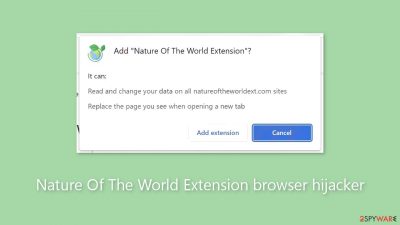
The Nature Of The World Extension is a browser hijacker that promotes a fake search engine. It is falsely touted as a tool that displays breathtaking natural landscapes. By changing the browser's settings, this extension sets notw.natureoftheworldext.com as the new tab page, homepage, and default search engine. As a result, users who open their browsers or try to search finally end up at bing.com after being continuously redirected to notw.natureoftheworldext.com.
Although Microsoft owns the genuine search engine bing.com, its credibility is called into question given that notw.natureoftheworldext.com was promoted through browser hijacking. False search engines have the ability to gather and utilize user data for potentially harmful purposes, such as browsing history, search requests, and personal information.
Furthermore, by exposing users to the possibility of visiting dangerous or deceptive websites, these fake search engines raise the possibility that they will become victims of malware, phishing scams, or other scams. To reduce these risks, users should use caution and rely on reputable, well-known search engines.
| NAME | Nature Of The World Extension |
| TYPE | Browser hijacker; potentially unwanted program |
| SYMPTOMS | Pop-up ads appear in the corner of the screen and redirects take users to suspicious websites; the man settings, like the homepage, suddenly change |
| DISTRIBUTION | Shady websites, deceptive ads, freeware installations |
| DANGERS | Pop-ups and redirects generated by the extension can lead to dangerous websites where people can get tricked into providing their personal information or downloading PUPs and malware |
| ELIMINATION | Remove the extension via browser settings; performing a scan with professional security tools is recommended |
| FURTHER STEPS | Use a maintenance tool like FortectIntego to fix any remaining damage and optimize the machine |
Distribution methods
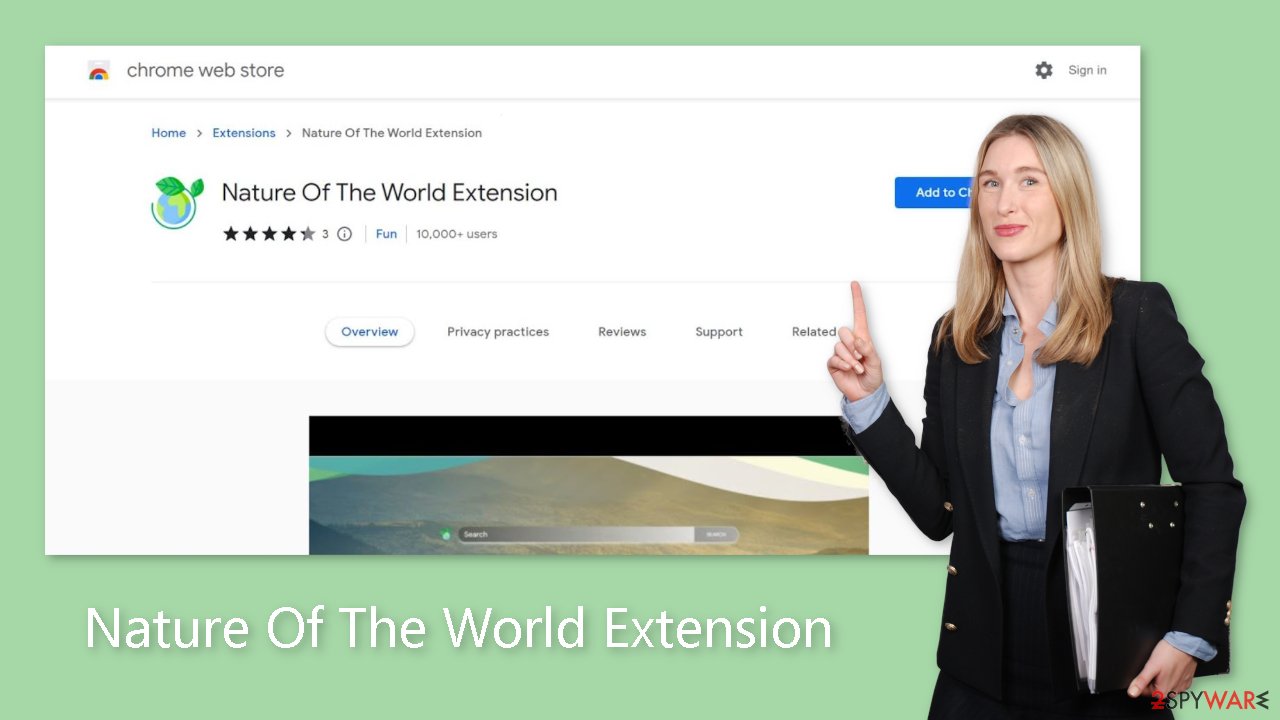
Though most rogue browser extensions propagate via questionable file downloaders, crooks occasionally set up their own “official” websites to promote these add-ons. These websites overstate features that don't exist in an effort to get visitors to download the extensions themselves.
Stick to official web stores instead, as they have rigorous review processes in place for listed apps. Nevertheless, certain fraudulent applications, like the browser hijacker Nature Of The World Extension, are able to get past security measures. For this reason, it is imperative that comprehensive research be done at all times.
Examine ratings, read reviews, and see how many people are using it. Select programs that have a large user base and a lot of positive ratings. Furthermore, pay close attention to the descriptions because scammers frequently use poor grammar and spelling.
Start the removal via browser settings
You should first try to locate the extension responsible for the changes in your browser settings and move on to the next step:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.
![Remove extensions from Edge Remove extensions from Edge]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Clear cookies and cache
Installing a dubious software on your browser can have more negative effects than just intrusive advertisements and pop-ups. These plugins can monitor websites you visit, links you click, and purchases you make via cookies. They can also track your browser behavior. Advertising networks may then purchase this gathered data, allowing them to target you with increasingly customized advertisements.
It's important to regularly clear your cache and cookies, and there is an automated way to do so. FortectIntego is a great maintenance program that may clean your browsers and make your computer run more smoothly. Moreover, it fixes any harm, including registry problems, system faults, and corrupted files, which makes it very helpful following virus infections.
Check your system for adware
Adware[1] may be present on your system if you have deleted the Nature Of The World Extension from your extensions list but are still experiencing annoying symptoms like pop-ups and redirects to dubious websites. These kinds of programs frequently sneak into systems undetected and perform a variety of background functions, like creating advertisements.
Bundling software is the most popular way for potentially unwanted applications (PUAs)[2] to get onto users' systems; this is especially true on freeware[3] distribution websites. These websites include extra software since they don't make money from offering free software.
These applications often belong to the class of programs known as potentially unwanted programs (PUPs), which take advantage of the actions of users. Once inside the system, they might be difficult to detect since they frequently pose as helpful applications like photo and video editing software, antivirus software, and system optimizers.
In order to prevent this, we advise you to use reputable security software such as SpyHunter 5Combo Cleaner or Malwarebytes to scan your computer, get rid of any threats, and alert you in advance to possible PUPs before they have a chance to alter anything. If you prefer a manual approach and know which program is causing issues, we have instructions for both Windows and Mac machines:
Windows 10/8:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till the uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Windows 7/XP:
- Click on Windows Start > Control Panel located on the right pane (if you are a Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.
![Uninstall from Windows 7/XP Uninstall from Windows 7/XP]()
- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Mac:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
How to prevent from getting browser hijacker
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.










