Numberonevpn.com (Free Instructions) - Removal Guide
Numberonevpn.com Removal Guide
What is Numberonevpn.com?
Numberonevpn.com is the infection that shows fake warning messages and alerts to spread useless applications
From the name of this domain, Numberonevpn.com virus should distribute or at least promote a VPN tool, but this adware shows fake warning messages and pushes ReSecure software that is not considered a safe and useful iPhone application. When you follow up with the warning and go to Repair Now option button, the intruder automatically redirects you to download page of this app. If you click any further, the program may get installed without any additional permission requirement from one click on the redirect or the website itself.
| Name | Numberonevpn.com |
|---|---|
| Type | Mac virus |
| Promoted tool | ReSecure |
| Symptoms | The machine becomes slower than usual due to additional processes and pop-ups that appear out of nowhere with warnings and fake alerts from the OS stating about malware and possible damage or danger |
| Distribution | Deceptive advertisements, freeware programs, bundled software, fake installs, and updaters, other PUPs |
| Possible danger | Exposes to malicious sites, promotes useless tools, can install them directly on the machine without permission. PUPs get to access and track data regarding users' browsing habits |
| Elimination | Get the anti-malware tool and remove Numberonevpn.com |
| Remediation | For best results, scan your machine with FortectIntego |
Numberonevpn.com is a redirect virus that was created by fraudulent hackers who focus on carrying these bogus alerts and warning messages. Content may be very convincing as they appear on your mac asking to click Repair Now button and claiming that the alert is from the system of the machine. Unfortunately, this is a scamming technique or social engineering campaign, in other words.[2]
The shady message that Numberonevpn.com alerts deliver states the following:
ATTENTION – Viruses found!
Your Apple is severely damaged by (39) viruses! Soon your Apple SIM card will be corrupt and it will damage your contacts, photos, data, applications, etc..
or
Your iPhone is severly damaged by (39) viruses
We've noticed that your Apple is 28.1% Damaged by (30) harmful viruses from recent adult sites. It will soon corrupt your iPhone's SIM card and damage your contacts, photos, data, and applications.
4 minutes and 52 seconds
If you don't remove the virus now, it will cause serious damage to your iPhone. Here's what you need to do (step by step):Step 1: Tap and install ReSecure for free on the App Store!
Step 2: Open the application to speed up and fix your browser now!
Once you close the alerts with the particular error or malware list, Numberonevpn.com redirects you to another window wit questionable alert that has Repair Now button. This window may show specific names of threats like worms or trojans and say that your device is damaged by a certain amount of percent. You shouldn't believe those claims and exit the web browser as soon as possible. 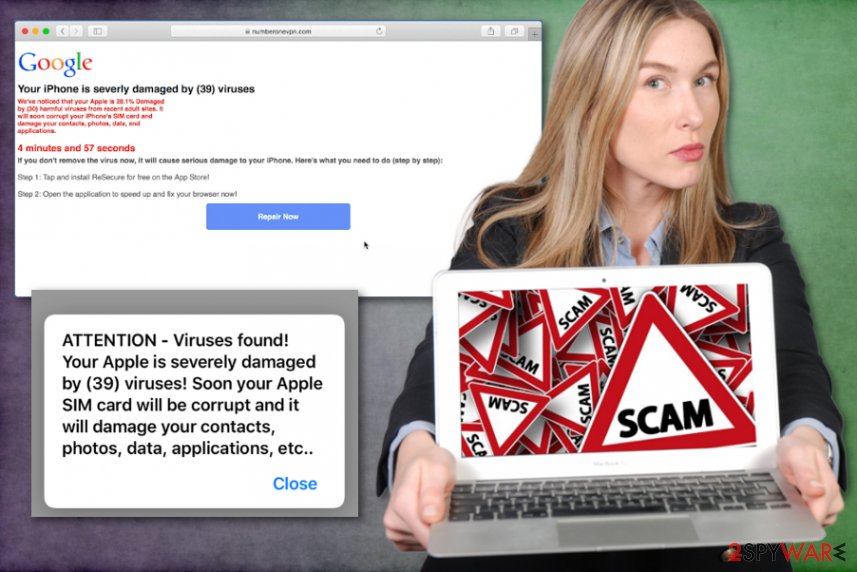
Since this intruder targets mobile devices as well as computers, Numberonevpn.com can even reroute you to direct download of the application. Unfortunately, it is not valuable to have a shady protection tool on the machine. It does nothing even though it offers safety features.
You need to avoid any installations from such alerts, warnings, and scammy messages or promotional content. Remove Numberonevpn.com immediately by exiting web browser windows with those alerts and run a scan on the system using anti-malware tool to eliminate the PUP that initial causes these issues.
Get an automatic antivirus program for the complete Numberonevpn.com removal and clean the system from all the PUPs, virus damage, other possible intruders. Tools like FortectIntego can help repair the damage that adware caused on your device. If your mobile phone got affected by this intruder, you can find applications capable of removing malware on the App Store. Also, experts[3] have prepared tips and guides for cleaning the machine below. 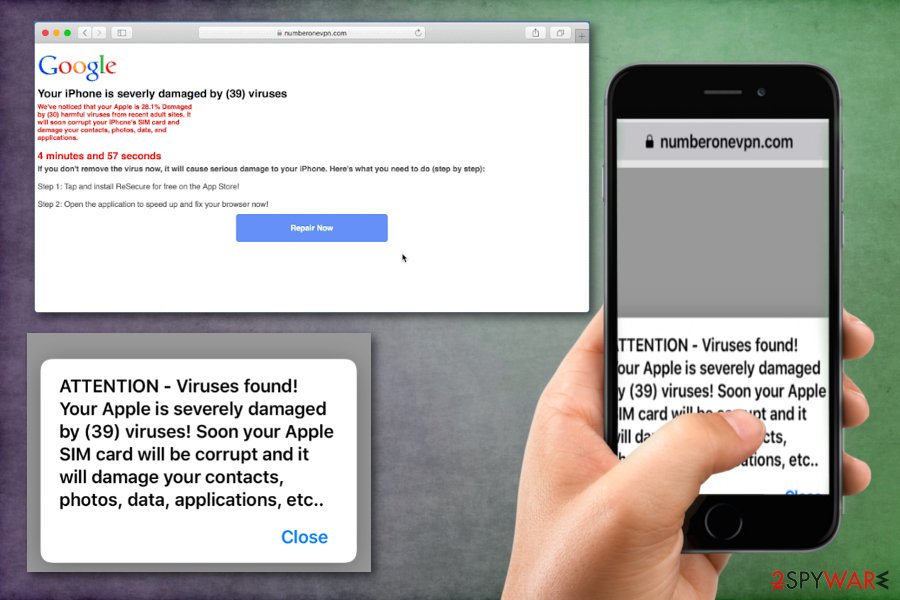
Bundled freeware and file-sharing networks deliver shady programs
Redirect malware, pop-up ads, scams and adware-type intruders, in most cases, come during insecure installation processes and from malicious websites, torrent pages, p2p sharing services, or even with cracked software installs. You should pay closer attention to sources you choose for your applications and system tools or even OS updates.
Getting anything installed on the machine can create the risk for the safety of the system. However, if you go for Advanced or Custom installation options, you can control what is coming to the machine and check the purpose of those applications set to come automatically. De-select programs listed on the setup if you don't know what those are for and install the tools you need.
Get rid of Numberonevpn.com virus and fake virus detection alerts with a proper antivirus tool
To remove Numberonevpn.com entirely from the device with all the associated browser extensions and related files, you need a tool that checks multiple parts of the system at once. When the adware gets on the system, it changes startup preferences and alters other parts of the system to ensure that this program runs every time you reboot the machine.
Due to these alterations and other intrusive symptoms, shady distribution techniques, features that keep the program persistent, users call the PUP a Numberonevpn.com virus. This is not a malware or program that can damage the machine, but adware can lead to infiltration of other viruses.
You need to take all those questionable features and symptoms into consideration when thinking about Numberonevpn.com removal. However, the best method for a threat like this is automatic anti-malware tool that fully checks the system and deletes all PUP damage, possible threats.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Numberonevpn.com. Follow these steps
Delete from macOS
You need to get rid of Numberonevpn.com and any associated programs or in-browser extensions, so all the shady activities can be stopped
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
You should check for suspicious extensions, add-ons and so on, so all the traces of the adware get eliminated
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Numberonevpn.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ I received a virus notice stating my iPhone was severely damaged. Discussions. Apple community forum.
- ^ Social engineering. Wikipedia. The free encyclopedia.
- ^ NoVirus. NoVirus. Spyware related news.












