NX Gone adware (virus) - Free Instructions
NX Gone adware Removal Guide
What is NX Gone adware?
NX Gone is a dubious browser extension that crooks use to generate revenue

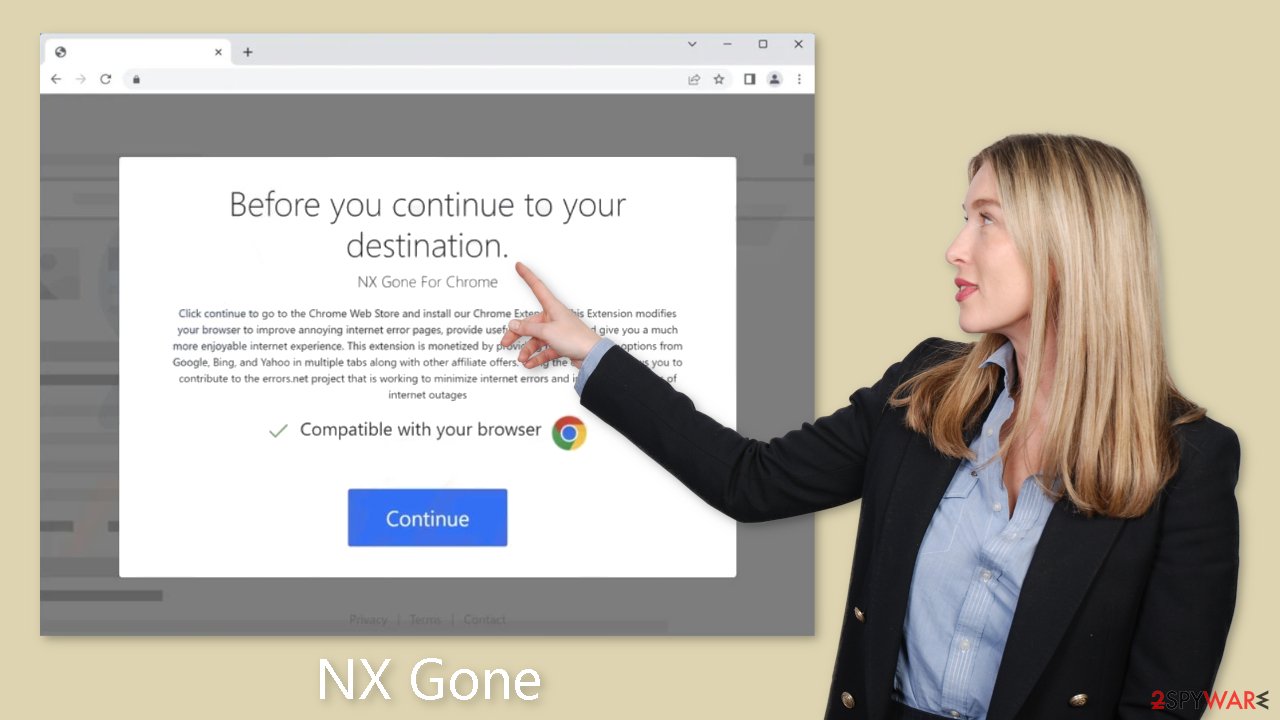
NX Gone is a browser extension that acts as adware,[1] displaying more commercial content such as pop-ups, banners, and redirects. While it claims to help inexperienced users navigate the Internet, this claim is rarely true. Crooks frequently try to make their applications appear useful and appealing in order to encourage user installation or discourage removal. Unfortunately, this app provides no benefits, so we recommend that you remove it using our instructions.
Fraudsters use these applications to generate revenue through pay-per-click (PPC) advertising. Although some advertisements appear to be harmless, they can actually be dangerous. Unfortunately, dishonest advertisers frequently use rogue advertising networks to display advertisements that lead to dangerous websites.
As a result, users may unintentionally visit scam pages designed to trick them into disclosing personal information, downloading potentially unwanted programs (PUPs),[2] or even downloading malware. Ads promoting counterfeit antivirus software, software deals, surveys, giveaways, and other deceptive content are not uncommon. As a result, seemingly innocuous pop-ups can lead to more serious problems. It is critical to remove this intruder as soon as possible, especially if the affected device is used by underage people.
| NAME | NX Gone |
| TYPE | Adware |
| SYMPTOMS | Annoying pop-ups and other types of advertisements start appearing on the screen |
| DISTRIBUTION | Shady websites, deceptive ads, freeware installations |
| DANGERS | Links embedded in the ads might lead to dangerous websites |
| ELIMINATION | Eliminate the extension through your browser settings; scanning the machine with anti-malware tools is recommended |
| FURTHER STEPS | Use FortectIntego to get rid of any remaining damage and to optimize the machine |
Distribution methods
Applications like NX Gone are frequently found on dubious download pages like Watchintenselyoriginaltheproduct.vip. These pages use social engineering techniques to trick users into thinking they need to install a browser plugin in order to perform certain actions.
We strongly advise against visiting unfamiliar websites and avoiding clicking on random links or advertisements, as these can lead to malicious websites. Websites that engage in illegal activities, such as illegal streaming platforms, should be avoided because they are unregulated.
It is best to use official web stores and developer pages to ensure security. Apps that are listed on digital marketplaces go through a rigorous review process. However, thorough research is still recommended, as some malicious apps may slip through the cracks. Before making a decision, always read reviews, consider ratings, and keep the number of users in mind.
Freeware installations
It is also possible that the NX Gone adware entered your computer without your knowledge, especially if you use freeware distribution platforms. To monetize user activity, these platforms frequently bundle additional software in their installers.
It is critical to remain vigilant during the installation process and to select the “Custom” or “Advanced” installation methods. Read the Terms of Service and Privacy Policy to understand how your data will be used. The most important step is to go through the file list carefully and uncheck any boxes next to unrelated applications.
Remove NX Gone adware
To eliminate the NX Gone adware, you can access your browser settings and navigate to the extension list. We suggest removing the plugins individually to observe any noticeable alterations.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Adware. Malwarebytes. Cybersecurity Basics.
- ^ Potentially unwanted program. Wikipedia, the free encyclopedia.
- ^ Dusan Vasic. What Are Cookies? The Good and the Bad of Browser Cookies. Dataprot. Security Solutions.










