Protectalldevices.space scam (fake) - Free Instructions
Protectalldevices.space scam Removal Guide
What is Protectalldevices.space scam?
Protectalldevices.space claims that your system is infected: do not fall for this scam

Protectalldevices.space is a fraudulent website implicated in a deceptive scheme that mimics virus infection warnings, ostensibly from well-known cybersecurity firms. This website falsely presents these threats to coerce users into buying what it claims to be antivirus software. It is crucial to understand that these virus infection warnings are entirely bogus and are designed to replicate the look of a genuine security scan.
Despite the lack of authenticity in the virus scans presented by Protectalldevices.space, the potential presence of adware on your device should not be ignored. Adware is frequently the source of such false alerts and can expose your system to various cybersecurity threats if not addressed in a timely manner.
In the later parts of this article, we will delve into the details of the Protectalldevices.space scam and provide detailed guidance on how to identify and remove potential adware from your device. It is vital to be well-informed and vigilant to protect your digital environment from such deceptive tactics.
| Name | Protectalldevices.space |
| Type | Scam, phishing, redirect |
| Scam content | Shows a pop-up that claims that trojans and other malware have been detected, then prompts users to purchase software to remove the allegedly found threats |
| Distribution | Redirects from other malicious websites, adware |
| Risks | Loss of finances due to fake subscriptions; redirects to other malware-laden, scam websites; installation of potentially unwanted or malicious software |
| Removal | You should not interact with any links or ads shown on the scam page and shut it down immediately. Then, perform a full scan with SpyHunter 5Combo Cleaner security software as a precautionary measure |
| Other tips | To prevent third parties from tracking your online activities, we recommend clearing browser caches and other leftover files with FortectIntego |
Dangerous websites can be reached in numerous ways
Users typically come across scam websites like Protectalldevices.space through two main channels: accidental encounters on compromised websites or as a result of adware and other malware infections.
The first scenario occurs when users, unknowingly, visit legitimate but compromised websites. These sites might have been exploited due to security vulnerabilities or outdated software, allowing hackers to insert harmful codes. These codes, once interacted with, redirect the user to harmful websites. The deceptive nature of these embedded links makes them hard to distinguish from legitimate ones, often leading to users realizing the scam only after experiencing harm.
Alternatively, users might have their devices infected with adware or similar malware. Adware, characterized by the automatic display of unwanted advertisements, often sneaks into systems bundled with other downloads from the internet. This leads to unexpected redirections to scam websites or annoying pop-ups that direct users to these sites.
Regardless of how one encounters these fraudulent websites, the consequences can be severe, including financial loss or identity theft. This highlights the need for vigilant online behavior and robust security measures to protect against such threats.
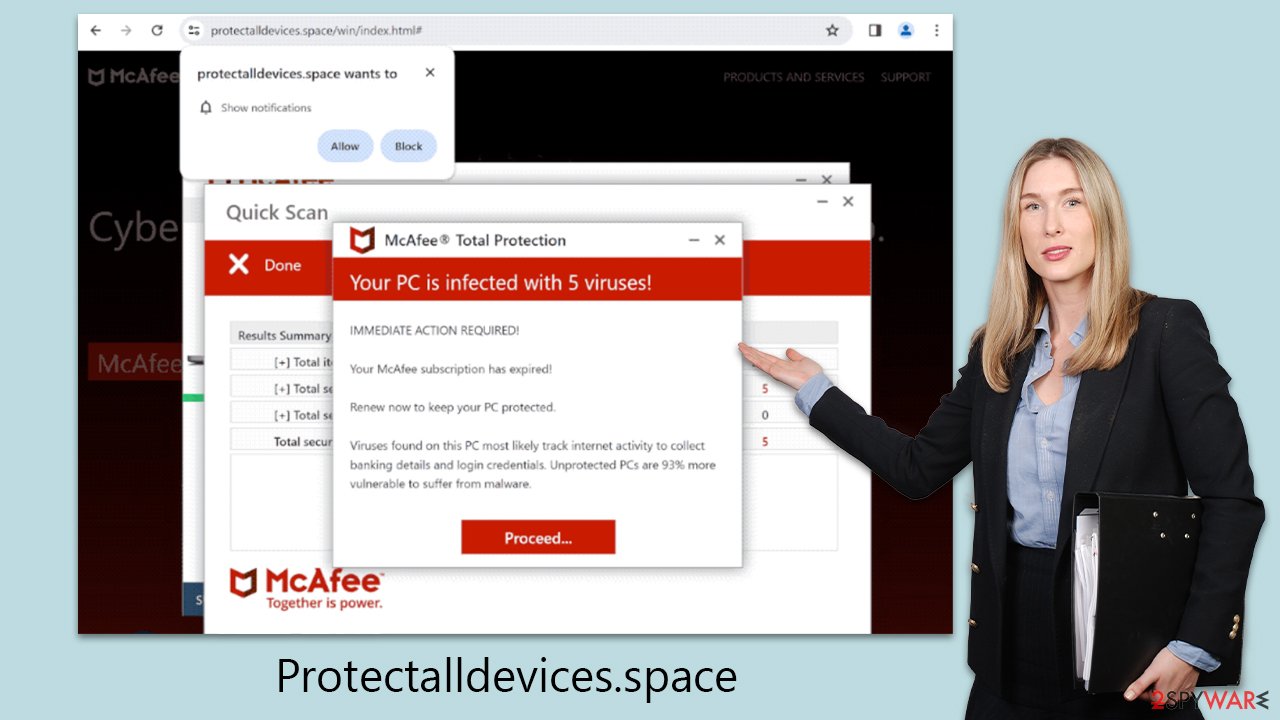
Fake messages imitating McAfee security scans
Upon accessing Protectalldevices.space, users are met with a false system scan followed by a deceiving alert claiming their computer is heavily infected with viruses. This deliberate misinformation is designed to create urgency and fear, suggesting that these nonexistent viruses could jeopardize the user's system security and expose sensitive information like personal credentials or financial data.
The website then prompts visitors to use McAfee Antivirus to remove these alleged threats. It's crucial to note that Protectalldevices.space is not associated with McAfee. Instead, it is operated by affiliates aiming to earn commissions by promoting and selling McAfee antivirus subscriptions through their links.
This type of scam, often referred to as a “fake virus alert scam,” skillfully manipulates human psychology, exploiting fears about cybersecurity to trap victims. The scammers use tactics ranging from fear-mongering to creating a sense of urgency, compelling victims to act hastily.
For example, the site might display alarming messages like:
Your PC is infected with 5 viruses!
IMMEDIATE ACTION REQUIRED!
Your McAfee subscription has expired!
Renew now to keep your PC protected.
Viruses found on this PC most likely track internet activity to collect banking details and login credentials. Unprotected PCs are 93% more vulnerable to suffer from malware.
This tactic of creating a false sense of urgency is a critical component of the scam's strategy. By convincing users that immediate action is necessary, scammers effectively prevent them from pausing to question the legitimacy of the alert. This urgency is carefully engineered to make the threat seem imminent, suggesting that any delay could result in further damage or data compromise.
Remove adware and other unwanted apps
To effectively handle an encounter with a scam site like Protectalldevices.space, initiating an adware scan is crucial. Employing trusted security software, such as SpyHunter 5Combo Cleaner or Malwarebytes, allows for a thorough system check. These programs specialize in quickly identifying and removing any unwelcome software, helping restore your system to a secure state.
Manual removal of unwanted applications can be complex and risky, with the potential of mistakenly deleting useful programs. Automated removal, on the other hand, offers a faster and more straightforward approach. Once you're certain your device is clear of malware and adware, it's vital to clean your browser's cookies and other tracking elements promptly.
This can be achieved either through specialized software FortectIntego or by following detailed instructions we'll provide later. This dual approach of cleansing both your device and browser not only protects your system but also enhances your online browsing experience, keeping it free from intrusive tracking.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Disable unwanted push notifications
A significant tactic of Protectalldevices.space is to prompt users to enable push notifications. This is a crucial point where users need to be wary, as consenting to these notifications can lead to more deceptive practices. These notifications may show further false alerts, amplify a sense of urgency, and flood users with unwanted ads, possibly leading to other malicious sites.
If you've enabled notifications from this site, it's important to block them to prevent these risks. The upcoming sections will guide you on how to do this effectively, ensuring your online safety.
Getting rid of Protectalldevices.space scam. Follow these steps
Stop browser notifications
Remove unwanted notifications from Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate Privacy and security section and pick Site Settings > Notifications.

- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Remove unwanted notifications from Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Remove unwanted notifications from Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.

- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Remove unwanted notifications from Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

Remove unwanted notifications from MS Edge:
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.

- Toggle the switch to the left to turn notifications off on Microsoft Edge.

Remove unwanted notifications from MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Remove unwanted notifications from Internet Explorer:
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
- Locate web address in question under Allowed sites and pick Remove.

How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.














