Rain or Shine browser hijacker (virus) - Free Instructions
Rain or Shine browser hijacker Removal Guide
What is Rain or Shine browser hijacker?
Rain or Shine takes over the browser by changing the most important settings
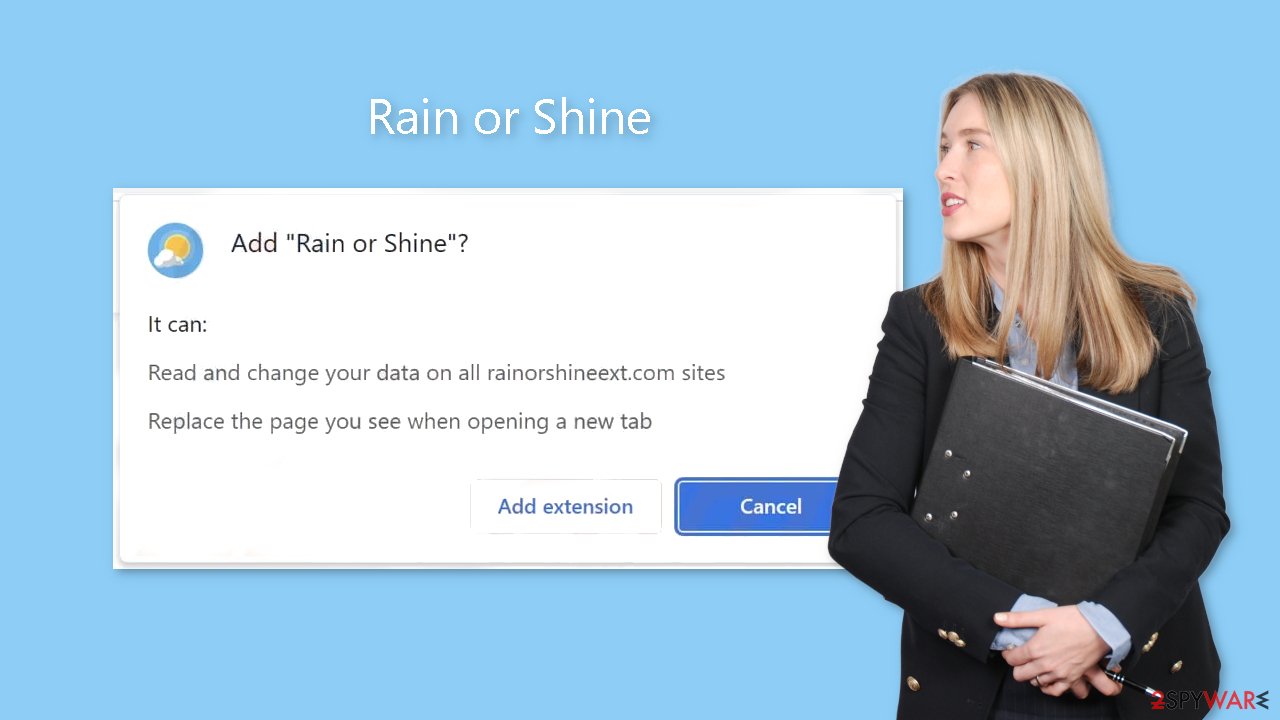
Rain or Shine is categorized as a browser hijacker due to its capacity to modify essential browser settings such as the homepage, new tab address, and default search engine. Users may also be subjected to an excess of commercial content, such as pop-up adverts, banners, and redirects. These programs' creators put user security and privacy below their own profits.
This plugin might make use of dishonest ad networks that insert dubious ads into your browser. As a result, users may unintentionally visit suspicious websites that attempt to trick them into disclosing personal information or downloading malware and potentially unwanted programs (PUPs).[1]
The lack of observable advantages for users is a defining characteristic of browser hijackers. With beautiful landscape wallpapers, they can change your homepage's appearance on the surface, but their functionality is still limited. With user data and pay-per-click advertising as their main sources of income, Rain or Shine's developers make little attempt to create services that are actually beneficial.
The irony is that a lot of browser hijackers promote themselves as tools that might increase productivity or offer other benefits. Unfortunately, users frequently do not undertake sufficient or any research, which results in rash installations that are later regretted. This raises the question of how browser hijackers spread so quickly online.
| NAME | Rain or Shine |
| TYPE | Browser hijacker; potentially unwanted program |
| SYMPTOMS | Changed homepage, search engine, new tab address is set to rain.rainorshineext.com |
| DISTRIBUTION | Questionable sites, deceptive ads, freeware installations |
| DANGERS | Data gathering about users' browsing activity, links embedded in the search results, pop-ups can lead to dangerous websites |
| ELIMINATION | You can remove an unwanted extension via browser settings or by scanning your system with anti-malware tools |
| FURTHER STEPS | Use FortectIntego repair tool to fix any remaining damage left |
Distribution methods
Even though it happens infrequently, certain browser hijackers are able to gain access to trusted websites. The difficulty arises from the fact that digital marketplace administrators frequently find it difficult to recognize potentially undesirable programs. What one user may consider to be truly important, another user may consider to be a virus. As a result, some of these hijackers manage to get past the strict vetting procedures.
Users unknowingly install these hijackers from questionable websites or freeware[2] distribution sites more frequently than not. Many people believe that the internet is a safe place and that viruses are a thing of the past. The truth, however, is considerably different. Scammers have started creating sophisticated marketing campaigns using social engineering techniques to make their goods seem reliable and professional.
Crooks frequently claim that their browser extension was created in partnership with well-known tech companies like Google or Apple. Some even go so far as to prominently show endorsements, like “Recommended by Chrome.” It's essential to control your impulsive behavior and continuously do your homework before introducing new products and services to your devices in order to protect your digital security. Look for ratings, search engine results, and related reports.
You'll frequently find a small number of search results while looking up a browser hijacker's name. We strongly advocate sticking with extensions that are offered in legitimate web stores that come with a large user base, good ratings, and positive reviews. It's not a good idea to rely on arbitrary online sources for free digital goods.
The danger posed by cookies
In an era where data serves as the new currency, websites and web-based applications harness this information to generate profits. These tiny data files known as cookies[3] are used to retain a variety of information, including your IP address, geolocation, visited pages, clicked links, and online purchases. Then, by selling this information to ad networks and other third parties, they can use it to target you with ever more specialized advertisements.
Security experts advise routine cookie and cache clearing as a defense against this. However, a lot of people find this process tedious and time-consuming, which makes them disregard it. A maintenance tool named FortectIntego can carry out this action on your behalf. Among other advantages, it optimizes your device by addressing performance problems, system failures, and corrupted files in addition to erasing this data and stopping tracking.
Remove the Rain or Shine browser plugin
You can remove browser extensions by going to your browser settings:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.
![Remove extensions from Edge Remove extensions from Edge]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Remove the PUP hiding in your system
Simply deleting the browser extension might not be enough because you might still have adware on your computer. The best course of action is to use specialized security software like SpyHunter 5Combo Cleaner or Malwarebytes if you continue to see settings changes, persistent pop-ups, and banners. These instruments guarantee the thorough deletion of the potentially unwanted application (PUA), as well as every related file and registry entry.
It can be difficult to pinpoint the program that is causing these problems because it might not have the same name as the browser extension. To avoid suspicion, developers will occasionally disguise these programs as practical tools. When it comes to finding questionable programs on your computer and getting rid of them, anti-malware software outperforms manual removal.
Nevertheless, if you are confident about identifying the program responsible for these symptoms and prefer manual removal, we offer step-by-step instructions for both Windows and Mac systems:
Windows 10/8:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Windows 7/XP:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.
![Uninstall from Windows 7/XP Uninstall from Windows 7/XP]()
- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Mac:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
How to prevent from getting browser hijacker
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Chris Hoffman. PUPs Explained: What is a “Potentially Unwanted Program”?. HowToGeek. Technology Magazine.
- ^ Tim Fisher. What Is Freeware?. Lifewire. Internet, Networking and Security.
- ^ What are Cookies?. Kaspersky. Home Security.










