Re-captha-version-3-58.top ads (scam) - Free Instructions
Re-captha-version-3-58.top ads Removal Guide
What is Re-captha-version-3-58.top ads?
Re-captha-version-3-58.top is a fake website designed by scammers – you should avoid it
Re-captha-version-3-58.top is a fraudulent website known for its push notification scam operations. This site, under the guise of legitimacy, tricks users into signing up for its notifications. Users often find themselves redirected to this site via intrusive advertisements or through the installation of potentially unwanted applications (PUAs). Once given permission to send push notifications, Re-captha-version-3-58.top starts inundating its subscribers with deceptive messages. These can range from bogus alerts about virus infections to a barrage of unwelcome advertisements.
As soon as you permit push notifications from Re-captha-version-3-58.top, your browser becomes inundated with unsolicited advertisements that may pop up anytime you are using the browser. These ads generally lack quality, and there's a real concern that some might be deceptive or even contain harmful elements.
The fundamental goal of Re-captha-version-3-58.top is to generate revenue through user engagement by flooding them with a substantial number of advertisements. The critical issue with these ads is their lack of scrutiny for quality or security, leading to a situation where clicking on them could redirect you to unsafe websites or potentially result in your device being infected with malware. Check for more information about this topic below.
| Name | Re-captha-version-3-58.top |
| Type | Push notifications, ads, pop-ups, scam |
| Distribution | Users allow push notifications after they click the “Allow” button within the prompt |
| Symptoms | You may start seeing intrusive pop-ups on your desktop – clicking these may lead to insecure or even malicious websites |
| Risks | If you click on links provided by the website, you might end up infecting your system with malware/PUPs, disclosing your personal information to cybercriminals, or losing money for useless services |
| Removal | To block the intrusive pop-ups, you need to access your browser's settings section. Also, perform a scan with SpyHunter 5Combo Cleaner anti-virus to check for infections |
| Other tips | FortectIntego can help you when dealing with leftover adware files, for example, you can get rid of various browser trackers and fix system damage automatically |
Scams can be found accidentally on the internet
Given the vastness of the internet, it's impractical to expect complete eradication of online fraud. This kind of fraudulent activity encompasses various components, entities, and regulators, all of which are in a state of constant flux. Consequently, scam websites like Re-captha-version-3-58.top can emerge abruptly and swiftly impact numerous users, regardless of the duration of their active presence.
The primary culprits behind these scams are often rogue advertising networks in conjunction with malicious or poorly managed websites. Notable examples include torrent sites and infamous pirated software portals, which are well-known for their risky nature. These sites frequently host deceptive “Download” links that lead to phishing sites and dangerous ads, potentially resulting in severe malware infections like ransomware. Visiting such sites could cause irreversible harm to your digital security, emphasizing the importance of cautiousness and preventive measures when interacting with any dubious links online.
It's also crucial to acknowledge the role of adware in directing users to malicious and phishing websites. Adware, a sneaky type of software, typically operates in the background, disrupting the browsing experience by overlaying ads on content or embedding hyperlinks into text. This increases the chances of encountering hazardous sites, particularly when there's an existing adware infection.
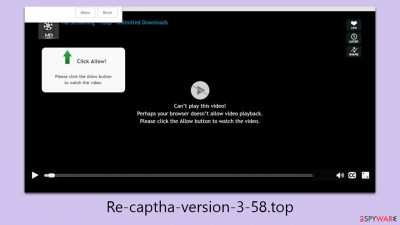
How scams get users tricked
The effectiveness of scams like the Re-captha-version-3-58.top push notification scam lies in their manipulative tactics. Scammers use various strategies to deceive users into allowing push notifications. They exploit users' familiarity with common internet protocols and human curiosity, leading users to mistakenly believe their requests are valid. Here are some typical methods used:
- “Click Allow to confirm you are not a robot”
This method leverages the widespread use of the “CAPTCHA” system on many legitimate websites, which typically requires solving a puzzle or entering distorted text to verify human identity. Scammers mimic this process by instructing users to click “Allow” as a way to confirm they're not a robot. This tactic appears familiar and seemingly innocuous, prompting many users to comply unwittingly.
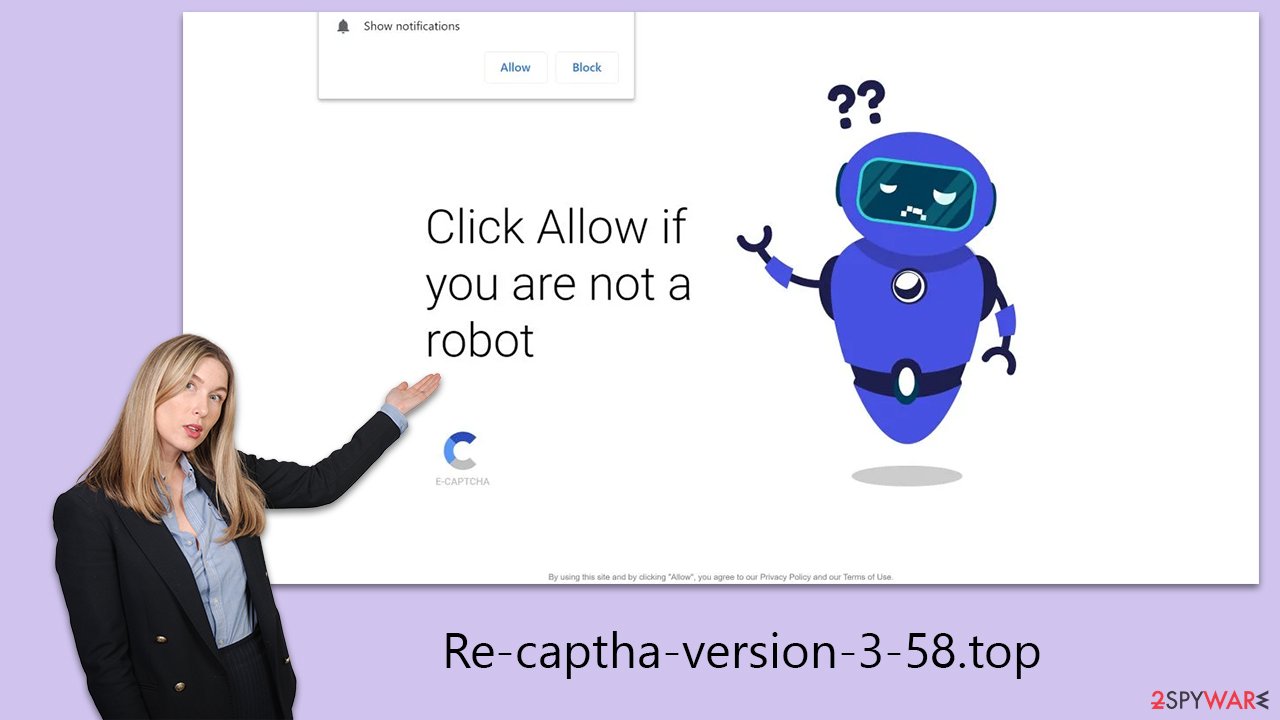
- “Click Allow if you are 18+”
This tactic plays on curiosity, implying that adult or restricted content will become accessible once the user confirms they are over 18 by clicking “Allow.” The allure of exclusive content often tempts users to click without fully understanding the implications.
It's essential to recognize that these prompts are deceptive. Clicking “Allow” does not reveal any content, nor does it perform a legitimate CAPTCHA verification. The sole outcome is the activation of push notifications, which scammers use to flood users with unwanted ads.
Remember, legitimate websites rarely request age or human verification via push notifications. Always approach such requests with skepticism. If you encounter them, it's advisable to close the site or leave it immediately. Internet safety largely depends on distinguishing false from true and being aware of these scamming techniques is crucial for a safer online journey.
Removal of suspicious components
When addressing the issue of intrusive push notifications from harmful sites like Re-captha-version-3-58.top, it's critical to check your system for adware or other types of malware infections. These infections not only redirect users to phishing websites but also employ sophisticated techniques that make them hard to identify.
For a thorough cleansing of your system from such threats, it's advisable to conduct a complete scan using reliable security software – SpyHunter 5Combo Cleaner or Malwarebytes. These anti-malware programs are proficient in detecting and eliminating a broad spectrum of malware. Additionally, to improve your system's overall health and efficiency, consider using a system optimization tool FortectIntego. Such a utility can help clean your browsers, remove unneeded files, and fix any issues that might have arisen due to malware infections or other related problems.
Once you've ensured your system is free from any hidden threats, follow the detailed instructions in the next section of this article. These steps are designed to help you permanently stop the annoying pop-ups that originate from Re-captha-version-3-58.top.
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.





