RevServicesX (Free Instructions) - Removal Guide
RevServicesX Removal Guide
What is RevServicesX?
RevServicesX is a Trojan Horse that is used to mine cryptocurrency without users' permission
| Name | RevServicesX |
|---|---|
| Type | Trojan Horse |
| Sub-type | Bitcoin Miner Trojan |
| Main dangers | Use CPU power, affects OS performance, can work as a backdoor |
| Danger level | High |
| Strategy | Use more than 80% of PC's CPU's and graphics card power while mining cryptocurrency |
| Distribution | Software bundles, insecure emails |
| Elimination | Use FortectIntego for the virus removal |
Next to typical activity related to bitcoin mining, this virus can also be used for other dangerous tasks. This trojan horse can easily drop another virus on your computer without your knowledge. Additionally, it can track you to collect sensitive information and connect to its C&C servers to transfer this data to its owners without being noticed.
However, the main issue with RevServicesX bitcoin miner is that it can use the entire CPU's power for generating needed cryptocurrency. While you may not notice such activity on your computer for some time, sooner or later you should see that it keeps crashing, overheating, etc. Beware that such activity can easily shorten the life of the computer's processor.
As there is no outward indication that the program is running, here is a list of symptoms that a user should pay attention to indicate if they are infected with the RevServicesX trojan:
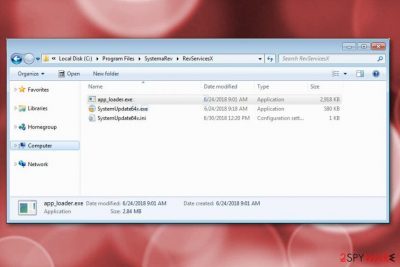
- You can see app_loeader.exe or SystemUpdate64x.exe running in your Task Manager;
- Task manager also can show almost 100% CPU utilization;
- PC or programs might start running slower than previously;
- Computer's general performance becomes slower.
If you want to prevent these issues on your machine, make sure you remove RevServicesX virus from the system. Otherwise, there is no guarantee that the developers of this virus won't start using these type of programs for spreading ransomware or other malware. Vayarasa.in[3] team is highly recommending infected users to proceed with automatic removal option. Keep in mind that this is a serious virus that must be eliminated immediately after being noticed. To delete malicious files and prevent unwanted activity, be smart and use anti-malware tools like FortectIntego or Malwarebytes.

Trojan horses are spread using different techniques
Virus developers have been relying on many different ways for spreading malware like this. The most common ways used by Trojan developers are insecure spam email attachments that have a malicious attachment added to them to infect target users. Trojans can infiltrate the system stealthily, the minute you open the “invoice”, “image” or similar attachment.
To avoid such fake email messages, you need to double check them first. Make sure you check the sender, his or her email address and similar information. Besides, always think have you ever dealt with the company the sender is representing. Typically, people download attachments from companies they have never heard of.
Also, do not forget to be cautious when downloading and installing freeware. While the most people tend to skip through some important steps, you should never choose Quick or Default options just to save your time while installing software on your system. Rushing thru such important steps might cause a lot of trouble, so make sure you opt for Custom or Advanced installation mode only. At this point, you should deselect unwanted components and be sure that you only get the software you need.
RevServicesX miner termination is important for the lifespan of your PC
To remove RevServicesX from the computer, you need to use professional anti-malware tools. Keep in mind that you are dealing with the serious malware that can cause numerous unwanted activities behind your back. We can suggest FortectIntego, Malwarebytes and SpyHunter 5Combo Cleaner which have been tested with this and similar viruses. However, make sure you update these tools before a scan as it is an important process while trying to eliminate the Trojan horse completely.
If you are not willing to download these programs on the system, note that RevServicesX removal is a difficult procedure, so rely on programs and tools that you can trust. Otherwise, during the termination of this malware, you can lose the important data.
How to prevent from getting trojans
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ What is CPU?. Wikipedia. The free encyclopedia.
- ^ Jack Danahy. The 3 Biggest Malware Trends to Watch in 2018. Securityweek. Internet and enterprise security news.
- ^ Vayarasa. Vayarasa. Spyware news.
