Rownowlive.site ads (Tutorial) - Chrome, Firefox, IE, Edge
Rownowlive.site ads Removal Guide
What is Rownowlive.site ads?
Rownowlive.site shows misleading messages to make people allow notifications

Rownowlive.site is a notable push notification scam site that skillfully deceives internet users into subscribing to its notifications. Many users may inadvertently encounter this site and become ensnared in a stream of misleading advertisements and deceptive content.
Once users are persuaded to subscribe, they are bombarded with constant unsolicited pop-up notifications. These notifications interfere with their online activities, emerging regardless of the website or task they are engaged in. Alarmingly, these pop-ups often contain fabricated stories, ranging from false virus infection alerts designed to instill panic, to misleading notifications of lottery wins aimed at exploiting the unsuspecting.
Rownowlive.site employs a traditional phishing tactic to exploit its victims. It displays fictitious security threats and offers counterfeit solutions, potentially leading users to unintentionally divulge personal information.
Understanding the tactics used by such scam sites is crucial for maintaining online safety. In this article, we delve into the deceptive practices of Rownowlive.site, highlighting its methods and offering guidance on how to stay secure in the digital landscape.
| Name | Rownowlive.site |
| Type | Push notifications, ads, scam, pop-ups |
| Distribution | Push notifications show up at some point after the “Allow” button in the notification prompt is clicked |
| Symptoms | You may start seeing intrusive pop-ups on your desktop – clicking these may lead to insecure or even malicious websites |
| Risks | Push notification prompts might include links to malicious websites, resulting in financial losses, personal information disclosure, or malware infections |
| Removal | To prevent the site from displaying notifications to you, access the site permission section via your web browser settings – you can find more details below. We also recommend checking the system for adware with SpyHunter 5Combo Cleaner security software |
| Other tips | It is important to clean web browser caches to prevent further data tracking and other issues related to web data corruption – use FortectIntego to do this quicker |
How you might have ventured to a scam site
The internet, a revolutionary tool in reshaping our communication and information-gathering methods, also harbors significant risks, notably cyber fraud. Due to its vast and constantly evolving nature, the digital world becomes a breeding ground for scam sites like Rownowlive.site, which rapidly prey on unwary users.
The proliferation of these threats is often exacerbated by unethical advertising networks and poorly regulated websites that distribute or host dangerous content. This may include malicious ads, compromised files, or deceptive “Download” buttons, thereby extending the scammers' reach.
Websites offering unauthorized content, such as pirated software or torrent downloads, are particularly perilous. Engaging with these sites not only risks redirecting users to phishing domains but also acts as conduits for malware infiltration, making any interaction with them potentially dangerous.
Adding to the problem is adware, a type of software that can be intrusive and harmful. Operating in the background, adware can alter your online experience by overlaying ads on standard content or embedding links within text. Such intrusions increase the likelihood of users being inadvertently led to dubious sites. Therefore, vigilance is essential in navigating these online domains to maintain a safe digital environment.
Scammers use simple yet effective tactics to trick users
Upon landing on Rownowlive.site, users often encounter a startling and unexpected redirect, a core tactic of this scam. Instead of reaching their intended content, they are greeted with deceptive requests that mimic genuine online interactions, catching them off-guard.
Users face various cunning prompts, such as:
-
If you are 18+, click Allow
-
Click Allow to watch the video
-
Press “Allow” bot verify, that you are not robot
-
Browser verification in progress – click the button “Allow” to access
-
Click “Allow” to win a prize and get it in our shop!
These prompts are shrewdly designed to exploit users' familiarity with similar, legitimate online requests. Users often encounter websites asking for age verification, human validation, or suggesting that browser settings may be blocking video playback. The similarity of these deceptive prompts to legitimate requests often convinces users to click the “Allow” button.
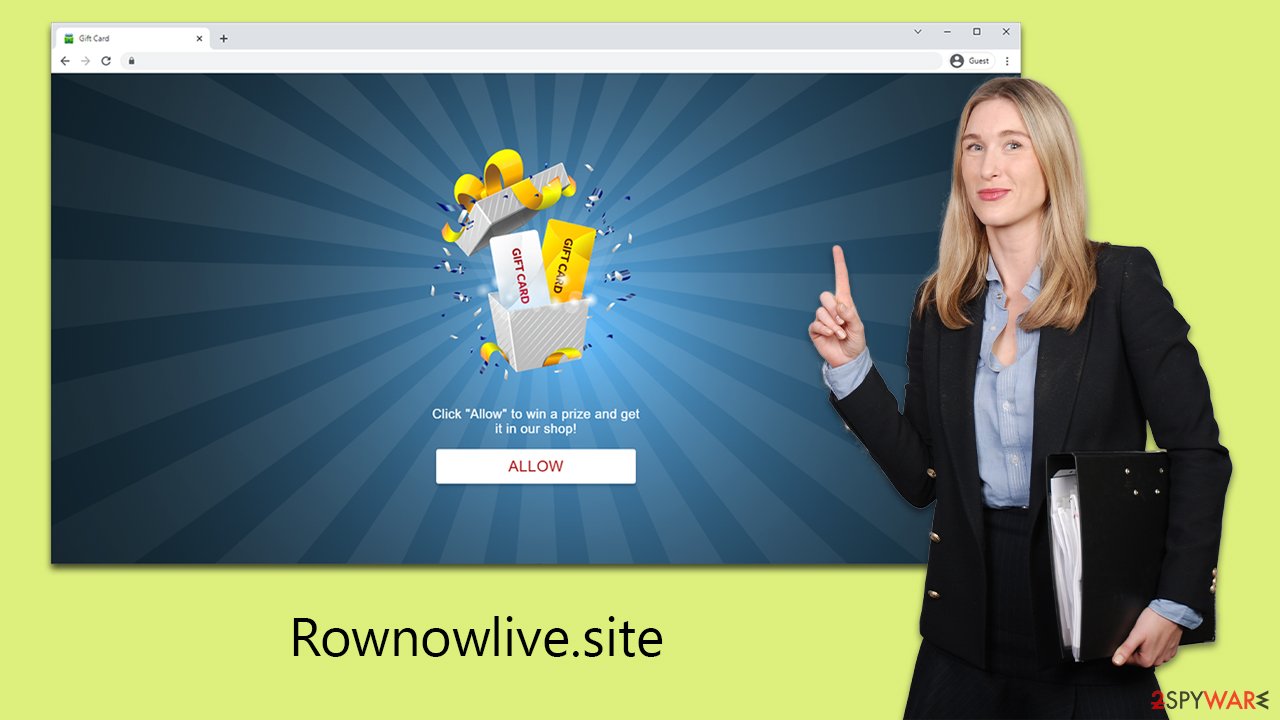
In essence, the operators behind the Rownowlive.site use social engineering techniques to lure users into their traps. The push notification feature, inherently benign and intended for legitimate purposes, has been maliciously altered by these cybercriminals.
By creating scenarios that prompt users to click “Allow” on these questionable sites, scammers gain the ability to send intrusive and potentially harmful ads directly to users' desktops. Thus, a tool originally designed for user benefit has been twisted into a conduit for scam spread.
How to get rid of unwanted pop-ups and remove infections from the system
Before addressing the intrusion of ads from Rownowlive.site, it's crucial to examine your system for any signs of infection. If your device has fallen prey to adware or other types of malware, you might notice an increase in ads and frequent redirections to suspicious sites during your web browsing.
Employ the use of reliable security software, such as SpyHunter 5Combo Cleaner or Malwarebytes, to detect and eliminate adware and malware from your system effectively. Likewise, using a repair tool FortectIntego can aid in the removal of trackers and address any potential damages inflicted by viruses. This step ensures that your system maintains optimal performance and alleviates concerns regarding your computer's stability efficiently.
To halt unwanted push notifications, start by navigating to the settings or options menu of your web browser. Most browsers feature a specific section for privacy and security in their settings, where site permissions can be managed. Within this area, you will typically find a category designated for notifications.
In the notifications settings, you'll see a list of all websites authorized to send you push notifications. If you identify a website that has been sending undesired notifications, like Rownowlive.site, you have the option to alter its permission from “Allow” to “Block” or “Ask.” For more comprehensive guidance, refer to the following steps provided.
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.






