Smartdownloader.site browser hijacker (Free Guide)
Smartdownloader.site browser hijacker Removal Guide
What is Smartdownloader.site browser hijacker?
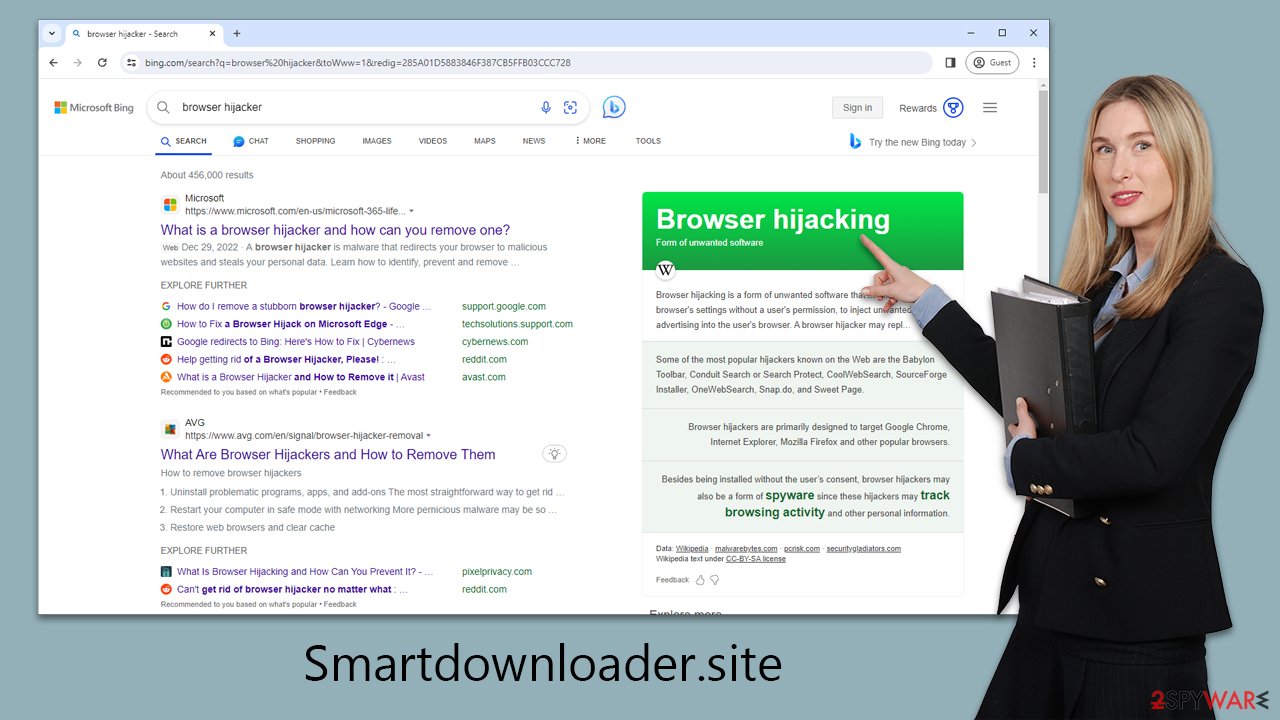
Smartdownloader.site web address is related to a browser hijacker infection
A browser hijacker is a type of unwanted software that is frequently installed accidentally as a result of deceptive software bundling. Once installed, this type of software changes the homepage and new tab address to something like Smartdownloader.site. This URL will also be displayed on every tab opened in Google Chrome or another browser.
Another indicator of this problem is a changed search box that leads searchers to an unfamiliar search engine, such as m.nearbyme.io, or, depending on the user's location, to more recognizable ones – Yahoo or Bing.
These search results are modified, with promotional links and advertisements displayed at the top to attract clicks. Meanwhile, the Smartdownloader.site hijacker silently collects surfing data from users for targeted advertising.
If you have found that your homepage and new tab address have been altered without your permission, you should follow the instructions below to find out more about this issue and learn how to remove the unwanted software easily.
| Name | Smartdownloader.site |
| Type | Browser hijacker, potentially unwanted application |
| Distribution | Software bundles, ads, redirects |
| Symptoms | Redirects searches through alternative providers; shows irrelevant links, inserts ads into searches and elsewhere |
| Risks | Installation of other potentially unwanted programs/malware, personal data disclosure to unknown parties, monetary loss |
| Removal | You can eliminate the browser hijacker by adjusting your browser's settings. Scanning your system with SpyHunter 5Combo Cleaner security software will confirm that no adware or malware is running in the background |
| Other tips | After you eliminate the hijacker, you should also clean your web browsers to avoid tracking and other issues. You can use FortectIntego as a quick solution |
Distribution methods of potentially unwanted apps
First and foremost, we must discuss the methods used to propagate the deceptive software. Most users would not install these apps on purpose because they do not like having their browser settings modified without their knowledge. Because developers and distributors are well aware of this, they utilize deception to trick consumers into installing PUPs without being aware of it.
Because many people use third-party websites to download free software (including unlicensed software sites like torrents), freeware packages are the primary means by which browser hijackers proliferate. Because distributors are compensated to do so, they frequently bundle software, which benefits both sides.
This is the explanation why, even if you download your desired app, you may end up with programs you are unaware of. In some rare circumstances, individuals unknowingly download and install malware.
As such, you should always download software from monitored websites or, ideally, from official sources. During the installation procedure, always select Advanced mode, which allows you to uncheck pre-ticked checkboxes. Also, keep an eye out for deceptive button placement and false remarks – thoroughly study the installation instructions. Most essential, never be in a hurry.
Why having a browser hijacker on your system is not a good idea
Although browser hijackers are not normally considered harmful, they can be annoying and constitute a threat to your privacy. Smartdownloader.site is a browser hijacker observed for its distracting ads and data-tracking capabilities. You may be exposed to advertisements supporting additional browser hijackers or adware if you have a potentially unwanted program installed on your computer.
Smartdownloader.site can gather a variety of information about your surfing habits, such as search queries, visited websites, clicked links, timestamps, technical device information, and ISP data, which can be collected automatically using tracking cookies or web beacons. While this is not inherently dangerous, it may cause some people to be concerned about their privacy.
If your browser was recently compromised, it may be difficult to restore the original settings without disabling or deleting the software. We recommend the latter because the app offers no genuine benefits and can continue to track your data and display annoying adverts in the background.
Removal of the Smartdownloader.site hijacker
It may be difficult to establish which app is producing these symptoms when the browser homepage is hijacked by a suspicious website. In other words, you won't find a Smartdownloader.site extension or application on your system, and it can be called anything.
To begin the removal procedure, we recommend doing a comprehensive system scan with SpyHunter 5Combo Cleaner, Malwarebytes, or another robust protection program. This is especially crucial if you haven't recently installed any questionable apps; there could even be malware that feeds you secondary payloads without your knowledge.
If you would rather remove Smartdownloader.site hijacker manually, you should look for unwanted browser extensions as follows:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
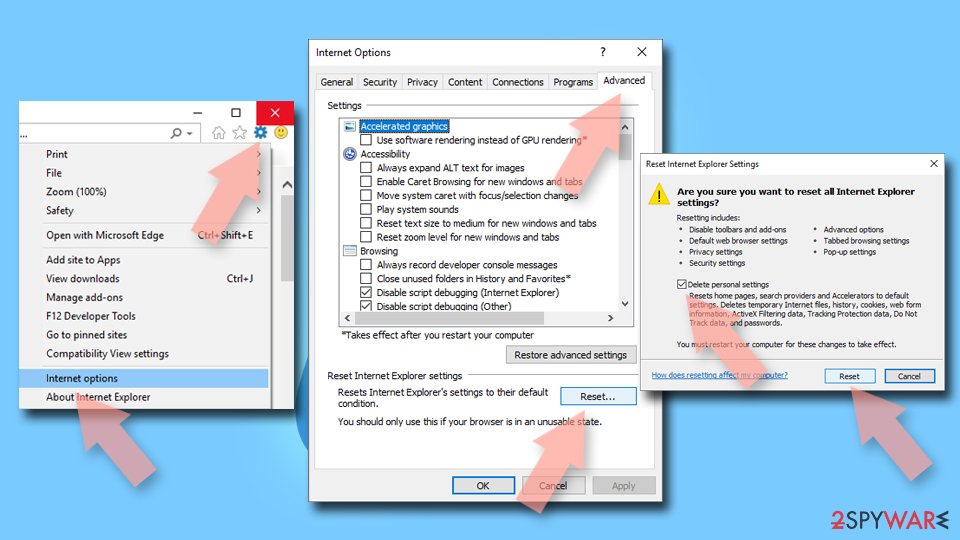
Internet Explorer
- Open Internet Explorer, click on the Gear icon (IE menu) on the top-right corner of the browser
- Pick Manage Add-ons.
- You will see a Manage Add-ons window. Here, look for suspicious plugins. Click on these entries and select Disable.
![Remove add-ons from Internet Explorer Remove add-ons from Internet Explorer]()
Unless you remove trackers from your local cache folders, Smartdownloader.site may continue to track various information about you (cookies, visited websites, links clicked, search queries, and more). If you want an automatic solution, we offer FortectIntego maintenance utility. Check out the guide below for manual steps:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Internet Explorer
- Click on the Gear icon > Internet options and select the Advanced tab.
- Select Reset.
- In the new window, check Delete personal settings and select Reset.
![Reset Internet Explorer Reset Internet Explorer]()
Keep in mind that Smartdownloader.site also asks users to enable push notifications. If you have (accidentally) enabled them, you can get rid of them manually as we explain in the instructions below.
Getting rid of Smartdownloader.site browser hijacker. Follow these steps
Stop browser notifications
Remove unwanted notifications from Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate Privacy and security section and pick Site Settings > Notifications.

- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Remove unwanted notifications from Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Remove unwanted notifications from Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.

- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Remove unwanted notifications from Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

Remove unwanted notifications from MS Edge:
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.

- Toggle the switch to the left to turn notifications off on Microsoft Edge.

Remove unwanted notifications from MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Remove unwanted notifications from Internet Explorer:
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
- Locate web address in question under Allowed sites and pick Remove.

How to prevent from getting browser hijacker
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.