Topwebanswers.com browser hijacker (Tutorial) - Chrome, Firefox, IE, Edge
Topwebanswers.com browser hijacker Removal Guide
What is Topwebanswers.com browser hijacker?
Topwebanswers.com is a browser hijacker that might negatively impact your browsing sessions
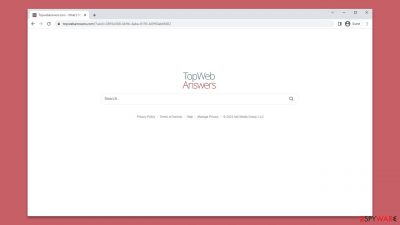
Topwebanswers.com is a website that replaces the default homepage and new tab on web browsers such as Google Chrome, Mozilla Firefox, and Microsoft Edge. It is a browser hijacker that is often distributed through software bundles or fake updates, misleading users into installing it. Once on the system, Topwebanswers.com takes over the browser settings and sets itself as the default homepage and new tab.
The most notable effect of Topwebanswers.com is the alteration of the search results. Instead of using the default search engine, it uses its own search engine, which is customized to display ads and sponsored links prominently. This affects the user experience by cluttering the search results and poses a security risk, as some of these sponsored links could lead to potentially harmful websites.
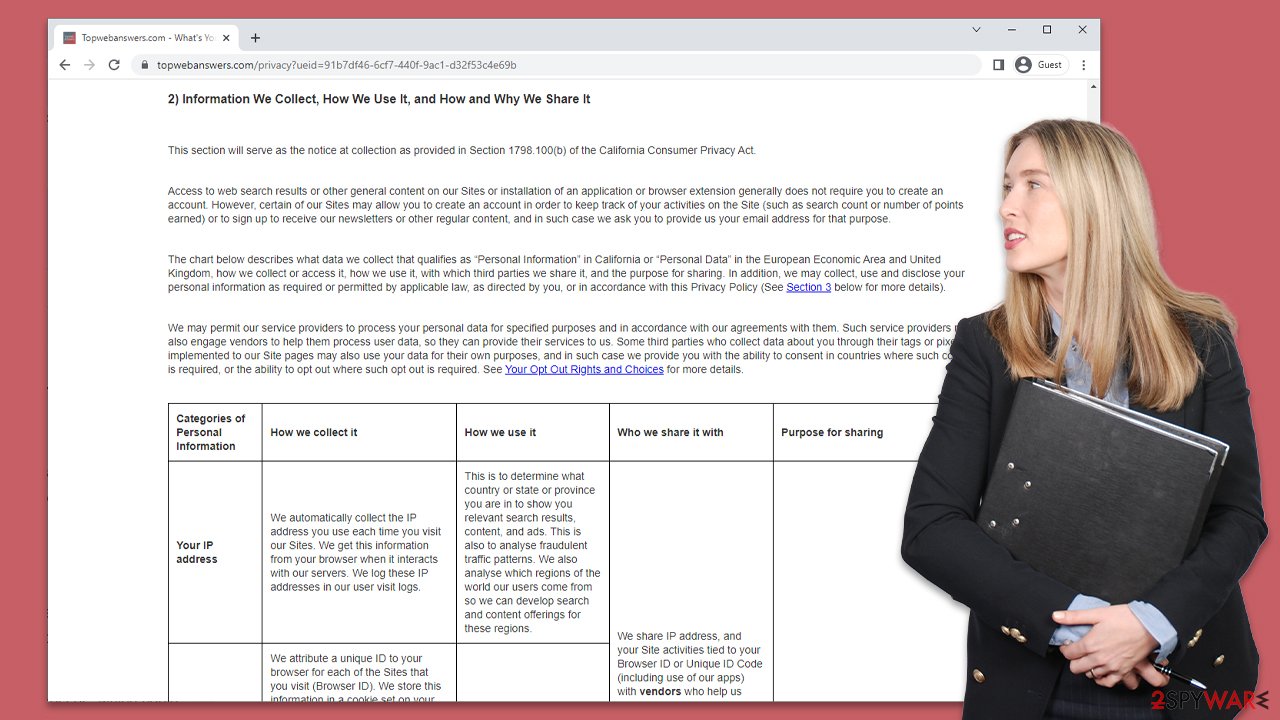
Furthermore, the app may also collect user data such as browsing history, search queries, and IP addresses, which could be used for targeted advertising or sold to third-party advertisers. Thus, if you have noticed the mentioned changes to your browser, it is time to get rid of this potentially unwanted application, and we explain of how to do it below in detail.
| Name | Topwebanswers.com |
| Type | Browser hijacker, potentially unwanted application |
| Distribution | Software bundles, third-party websites, misleading ads |
| Symptoms | A browser extension or an application installed on the device; homepage and new tab address set to Topwebanswers.com; ads and sponsored links in search results and elsewhere; promotes other potentially unwanted apps |
| Risks | Installation of other potentially unwanted programs/malware, personal data disclosure to unknown parties, monetary loss |
| Removal | You can eliminate the browser extension by accessing your browser's settings. A scan with powerful security software SpyHunter 5Combo Cleaner is also recommended |
| Other tips | After removing all potentially unwanted applications, we recommend you employ the FortectIntego utility to clean your web browsers and repair any damaged system files |
How browser hijackers sneak into your system
Browser hijackers are a notorious type of software that can cause serious damage to your computer system. In order to spread and gain popularity, the developers of these hijackers often resort to fraudulent tactics that are common among potentially unwanted programs. Top Web Answers, for instance, is a browser hijacker that employs such tactics to spread itself.
One of the most common ways that browser hijackers spread is through software bundling. Many people prefer to download free software from third-party websites without realizing that this is where most malicious or unwanted apps originate. During the installation process, users may skip steps or click through stages without reading the instructions, which can allow optional components to enter the system without their knowledge.
To avoid falling victim to this type of fraudulent distribution practice, paying attention to the installation process of any apps you download from unofficial sources is crucial. Always select the Advanced/Custom options and uncheck all of the pre-ticked checkboxes when possible. You should also be on the lookout for deceitful components, such as fine-print text or buttons that are strategically placed out of sight.
It is also important to note that using software cracks and other sites that offer pirated software is never a good idea. Such sites can be a breeding ground for ransomware and other dangerous malware that can infect your computer system. In addition to being illegal, this methodology can pose a serious threat to the safety and security of your computer. It is best to avoid pirated websites altogether and only download software from reputable sources.
Removal of Topwebanswers.com hijack
Browser hijackers have become a prevalent issue for internet users, and one of the most popular types is extensions. Due to their easy creation and rebranding, extensions can be used to spread unwanted programs without detection from security applications. However, the upside to this is that extensions usually have a smaller operation scope compared to programs installed on the system level.
Developers of browser hijackers are constantly creating new tactics to prevent users from uninstalling these unwanted apps. One such tactic is the use of the “Managed by your organization” feature, which makes it difficult for users to remove apps in a regular way. Thankfully, Topwebanswers.com does not use this tactic, making it easier for users to remove it.
The instructions below should help you remove the browser extension that has taken over your browser. It is noteworthy that the extension name might differ from user to user, but it is likely to be Top Web Answers – so you should look for it:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Internet Explorer
- Open Internet Explorer, click on the Gear icon (IE menu) on the top-right corner of the browser
- Pick Manage Add-ons.
- You will see a Manage Add-ons window. Here, look for suspicious plugins. Click on these entries and select Disable.
![Remove add-ons from Internet Explorer Remove add-ons from Internet Explorer]()
Additional security measures and removal of trackers
As we previously mentioned, browser hijackers and other potentially unwanted applications are often spread through deceptive techniques like bundling. If you find an app on your system that you did not intentionally install, there is a high likelihood that additional PUPs may also be present.
Visiting high-risk websites like torrents or illegal streaming sites and downloading software cracks could lead to malware infections. These infections could potentially include ransomware, which can result in losing personal files unless a ransom is paid to cybercriminals.
We suggest scanning your system with reputable security software, such as SpyHunter 5Combo Cleaner or Malwarebytes, to ensure that there is no hidden and more dangerous malware. Anti-malware software is an essential first line of defense against incoming malware attacks.
Cleaning your browsers from cookies and other trackers is also important since third parties may continue tracking you otherwise. Using a repair and maintenance utility like FortectIntego is the easiest way to get rid of leftover files, but a manual method can also be used by following these steps:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
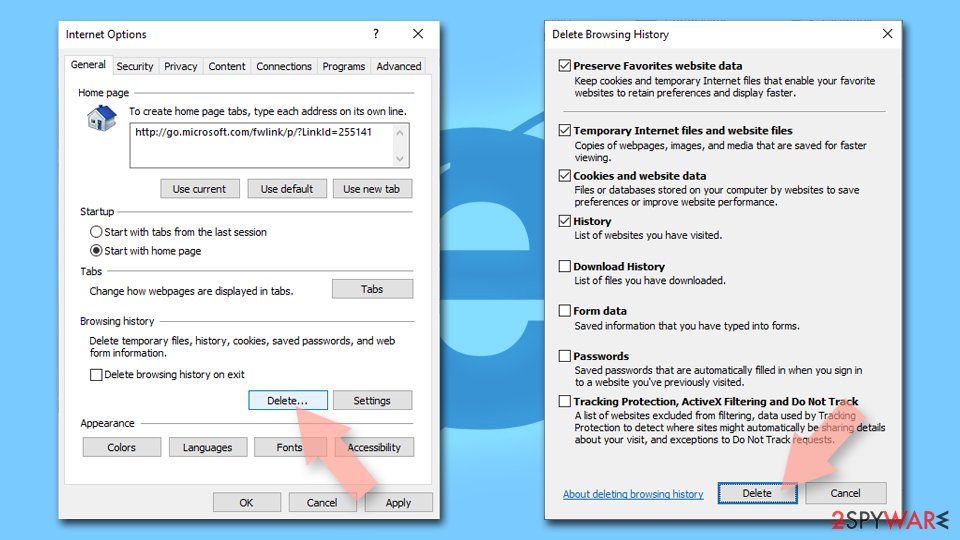
Internet Explorer
- Press on the Gear icon and select Internet Options.
- Under Browsing history, click Delete…
- Select relevant fields and press Delete.
![Clear temporary files from Internet Explorer Clear temporary files from Internet Explorer]()
How to prevent from getting browser hijacker
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.