Waqq ransomware (virus) - Recovery Instructions Included
Waqq virus Removal Guide
What is Waqq ransomware?
Waqq ransomware – a dangerous Windows virus that locks all personal files and demands ransom
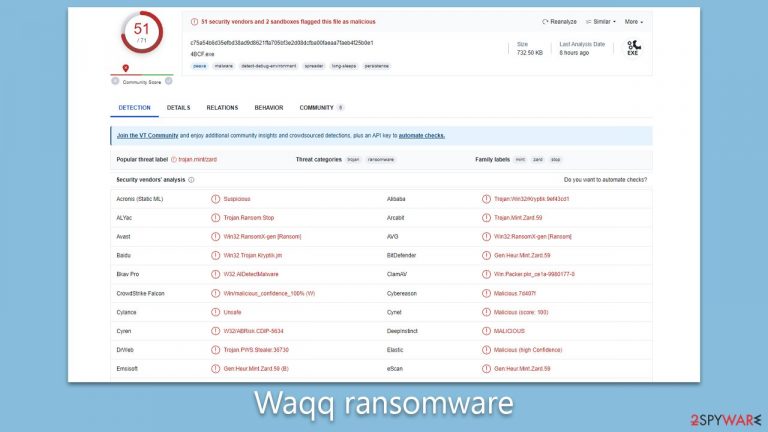
Waqq is a ransomware-type of threat that has been making waves in the cybersecurity world due to its destructive potency and robust encryption methods. As a member of the notorious Djvu malware family, it employs a similar strategy to its siblings but carries its unique signature – appending a “.waqq” extension to all compromised files using an RSA encryption cipher. The moment the malicious code infiltrates a system, it launches an all-out attack on all accessible files, rendering them inaccessible and leaving the user helpless.
Once the encryption process is complete, the Waqq ransomware places a “_readme.txt” ransom note in the affected folders. This ominous text file outlines the hacker's demand – a hefty ransom of $980 in exchange for a decryptor that promises to restore the encrypted files. However, the ransom note does mention a 50% discount, lowering the ransom to $490 if the victims respond within a specified time frame. The victims are directed to communicate with the perpetrators through two email addresses:
- support@freshmail.top.
- datarestorehelp@airmail.cc.
This nefarious business model has caused immense distress among not only users but also significant concerns within the cybersecurity community. To learn more about Waqq ransomware, its removal, and possible data recovery methods, please check the information below.
| Name | Waqq virus |
|---|---|
| Type | Ransomware, file-locking malware |
| File extension | .waqq extension appended to all personal files, rendering them useless |
| Family | Djvu |
| Ransom note | _readme.txt dropped at every location where encrypted files are located |
| Contact | support@freshmail.top and datarestorehelp@airmail.cc |
| File Recovery | There is no guaranteed way to recover locked files without backups. Other options include paying cybercriminals (not recommended, might also lose the paid money), using Emisoft's decryptor (works for a limited number of victims), or using third-party recovery software |
| Malware removal | After disconnecting the computer from the network and the internet, do a complete system scan using the SpyHunter 5Combo Cleaner security program |
| System fix | Upon installation, malware like ransomware can damage essential system files, leading to crashes and errors. To instantly mend such harm, FortectIntego PC repair, an automated solution, can be used. |
How ransomware spreads and how to avoid it
The distribution of ransomware like Waqq and other Djvu variants predominantly occurs through a method dubbed bundling. In 99% of cases, unsuspecting users get infected while downloading pirated software or cracked versions of paid applications. Cybercriminals smartly package the ransomware with these installers, which, when executed, simultaneously install the malicious software unbeknownst to the user. Consequently, the ransomware goes on to encrypt files, demanding a hefty ransom for their decryption.
Preventing ransomware infection involves a combination of safe practices and robust security measures. First, avoid downloading pirated software or cracked applications. It's crucial to remember that freebies from non-official sources often come with harmful extras. Stick to downloading software from the official vendor sites or trusted sources.
Second, ensure your computer's security software is always up-to-date. Regular updates fortify your system against new and evolving threats. Set automatic updates when possible to never miss any critical security patches.
Lastly, consider regular backups of your essential data. This measure won't prevent an infection, but it can save your files if an infection occurs. Store backups in a separate location, such as an external hard drive or a cloud-based service, to ensure they aren't affected in case of a ransomware attack.
The delivered ransom note
The ransom note that Waqq ransomware delivers reads as follows:
ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-vdhH9Qcpjj
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshmail.topReserve e-mail address to contact us:
datarestorehelp@airmail.ccYour personal ID:
This note serves as the attacker's communication, assuring the victims that all their important files are encrypted with a unique key. It further states the only way to recover the files is by purchasing a decrypt tool and the unique key, priced at $980. However, the hackers offer a 50% discount if contact is made within the first 72 hours, reducing the price to $490.
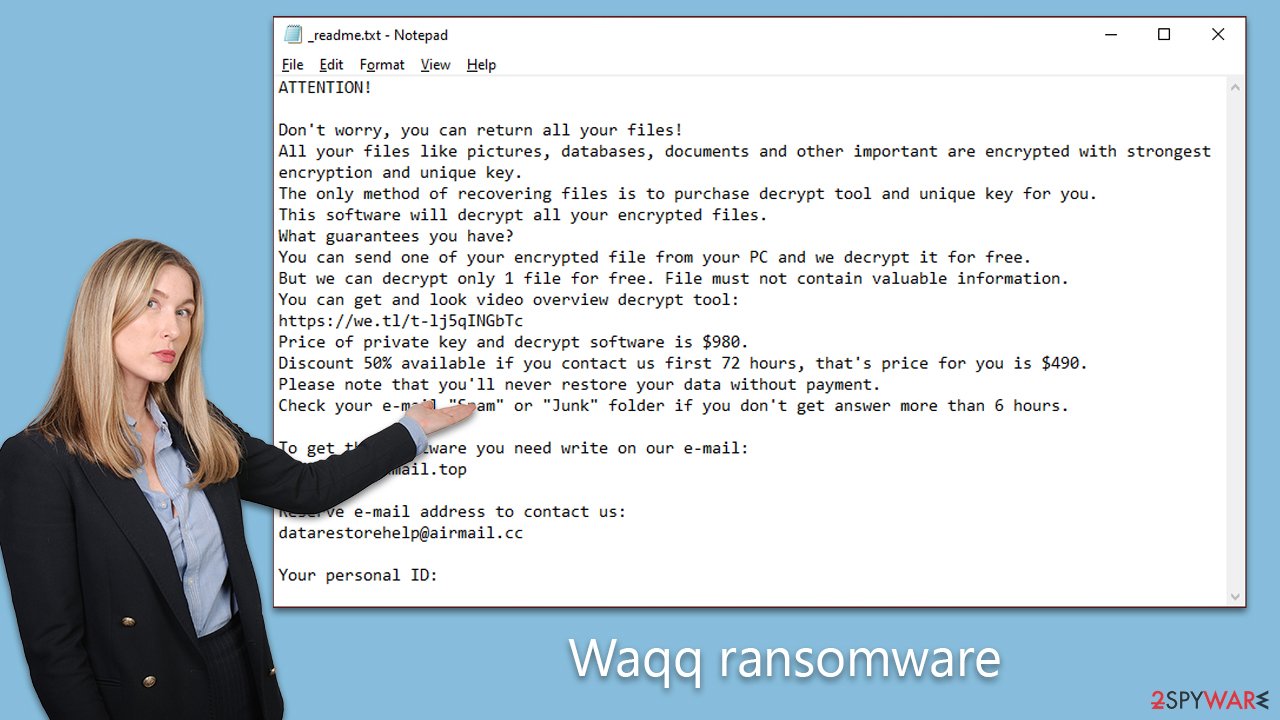
They also offer to decrypt one non-valuable file for free as a demonstration of their “honest” intentions. Victims are directed to contact the attackers via two email addresses, further enforcing the sense of urgency and desperation instilled by the attack. Please do not contact cybercriminals, as there is never a guarantee that they will deliver on their promises.
Step 1. Malware removal
Discovering that your files have been seized by ransomware can be a shocking and distressing experience. The Waqq ransomware, in particular, targets virtually all types of personal files, including precious photos and vital documents. The criminals behind this exploit prey on the emotional and practical value that these files hold for their victims. However, succumbing to the demands of these nefarious individuals should not be your first course of action. Instead, consider the following alternatives.
Begin by purging the ransomware from your system. Although the Waqq ransomware may self-destruct after encrypting your files, it may have installed additional malicious payloads or components that continue to jeopardize your system. For comprehensive removal, use potent anti-malware software such as SpyHunter 5Combo Cleaner or Malwarebytes. These applications are designed to root out the ransomware along with any residual malicious elements that may linger undetected.
In some instances, malware can hinder the removal process by interfering with your security software. If you encounter this issue, consider running the scan in Safe Mode, a more secure environment for tackling malware (instructions provided below).
Post-infection, your system may experience technical issues like crashes and errors due to damage caused by the ransomware. To address this, use a reliable PC repair tool like FortectIntego to diagnose and rectify system damage. This method is more convenient than a complete Windows reinstallation, which can be complex and time-consuming.
Step 2. Data recovery
The final stage in this ordeal is to regain access to your encrypted files without lining the pockets of cybercriminals. Many individuals unfamiliar with data encryption may believe that a simple antivirus scan would suffice, or perhaps, once their files are locked, recovery is impossible. Neither of these notions is accurate.
Several viable data recovery options exist:
- Restoring files from a recent backup is arguably the most dependable method. However, this is contingent on having up-to-date backups.
- File recovery software can be used to scan your hard drive and possibly recover deleted or damaged files, potentially including those encrypted by the ransomware.
- Utilize Emsisoft's decryption tool designed specifically for Djvu ransomware victims. This method might not work for all, but it's worth a shot.
Begin with the Emsisoft decryptor. Download the application from the Emsisoft official website, run it, and follow the instructions. The tool will attempt to decrypt the files and, based on the decryption key availability and its compatibility with your files, one of three outcomes will present: successful decryption, an error indicating unavailable keys, or an online ID-related issue rendering decryption impossible.
If decryption proves unsuccessful, don't lose hope. Consider using specialized data recovery software like Data Recovery Pro. Download and install it, run a deep scan, and follow the prompts to recover your files.
In certain cases, due to the diligent efforts of security researchers and law enforcement agencies, decryption tools become available when ransomware servers are seized, and decryption keys are released. Keep an eye on the provided links for any such updates:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

If you need more detailed instructions on the mentioned recovery methods, please check out the information below.
Getting rid of Waqq virus. Follow these steps
Isolate the infected computer
Some ransomware strains aim to infect not only one computer but hijack the entire network. As soon as one of the machines is infected, malware can spread via the network and encrypt files everywhere else, including Network Attached Storage (NAS) devices. NAS devices are commonly compromised via reused administrator credentials and remote access services, and attackers may also delete existing snapshots. If your computer is connected to a network, it is important to isolate it to prevent re-infection after ransomware removal is complete.
In modern environments, ransomware often spreads using stolen credentials, remote management tools, VPN connections, and cloud synchronization services, not only through shared network drives.
The easiest way to disconnect a PC from everything is simply to plug out the ethernet cable. This does not disconnect wireless networks, VPN connections, or cloud services, which must also be disabled separately. However, in the corporate environment, this might be extremely difficult to do (also would take a long time). In many organizations, devices are centrally managed, and network isolation is typically performed by IT or security teams using endpoint security or device management tools. The method below will disconnect from all the networks, including local and the internet, isolating each of the machines involved.
On modern Windows systems, network connections can also be disabled through the Settings app or automatically isolated using endpoint detection and response (EDR) tools.
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
If you are using some type of cloud storage you are connected to, you should disconnect from it immediately. It is also advisable to disconnect all the external devices, such as USB flash sticks, external HDDs, etc. Once the malware elimination process is finished, you can connect your computers to the network and internet, as explained above, but by pressing Enable instead. Before reconnecting, credentials should be reset, persistence mechanisms checked, and backups verified to ensure reinfection does not occur.
Restore Windows "hosts" file to its original state
Some ransomware might modify Windows hosts file in order to prevent users from accessing certain websites online. For example, Djvu ransomware variants add dozens of entries containing URLs of security-related websites, such as 2-spyware.com. Each of the entries means that users will not be able to access the listed web addresses and will receive an error instead.
Here's an example of “hosts” file entries that were injected by ransomware:
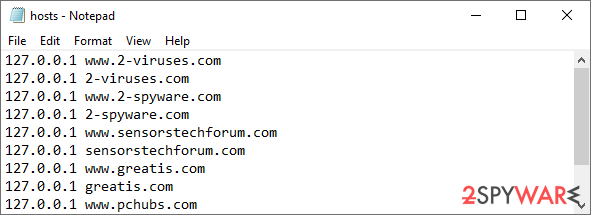
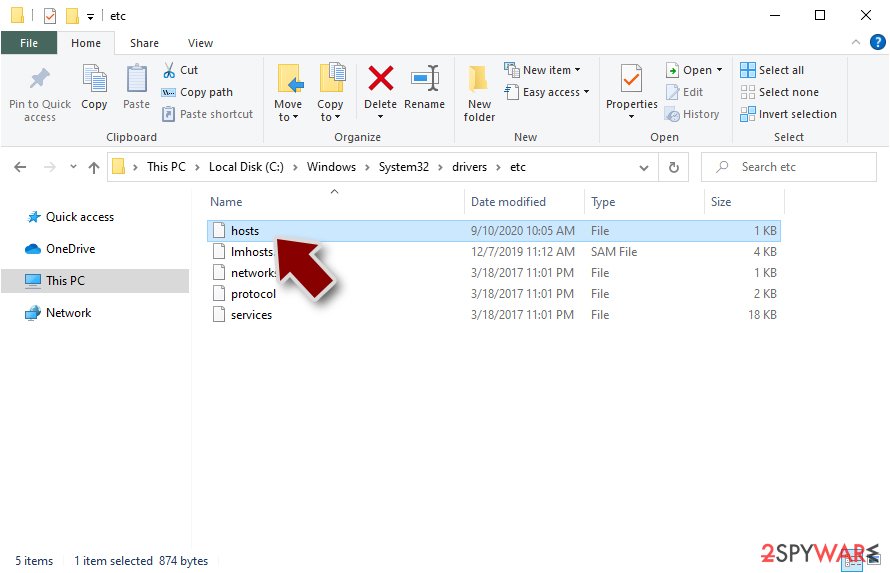
In order to restore your ability to access all websites without restrictions, you should either delete the file (Windows will automatically recreate it) or remove all the malware-created entries. If you have never touched the “hosts” file before, you should simply delete it by marking it and pressing Shift + Del on your keyboard. For that, navigate to the following location:
C:\\Windows\\System32\\drivers\\etc\\
Restore files using data recovery software
Since many users do not prepare proper data backups prior to being attacked by ransomware, they might often lose access to their files permanently. Paying criminals is also very risky, as they might not fulfill the promises and never send back the required decryption tool.
While this might sound terrible, not all is lost – data recovery software might be able to help you in some situations (it highly depends on the encryption algorithm used, whether ransomware managed to complete the programmed tasks, etc.). Since there are thousands of different ransomware strains, it is immediately impossible to tell whether third-party software will work for you.
Therefore, we suggest trying regardless of which ransomware attacked your computer. Before you begin, several pointers are important while dealing with this situation:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.

- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.

Use Emsisoft decrytor for Djvu/STOP
If your computer got infected with one of the Djvu variants, you should try using Emsisoft decryptor for Djvu/STOP. It is important to mention that this tool will not work for everyone – it only works if data was locked with an offline ID due to malware failing to communicate with its remote servers.
Even if your case meets this condition, somebody from the victims has to pay criminals, retrieve an offline key, and then share it with security researchers at Emsisoft. As a result, you might not be able to restore the encrypted files immediately. Thus, if the decryptor says your data was locked with an offline ID but cannot be recovered currently, you should try later. You also need to upload a set of files – one encrypted and a healthy one to the company's servers before you proceed.
- Download the app from the official Emsisoft website.

- After pressing Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.

- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.

- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.

- Press Decrypt.

From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Waqq and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
