Loqw ransomware (virus) - Recovery Instructions Included
Loqw virus Removal Guide
What is Loqw ransomware?
Loqw ransomware is a dangerous virus that encrypts users' personal files
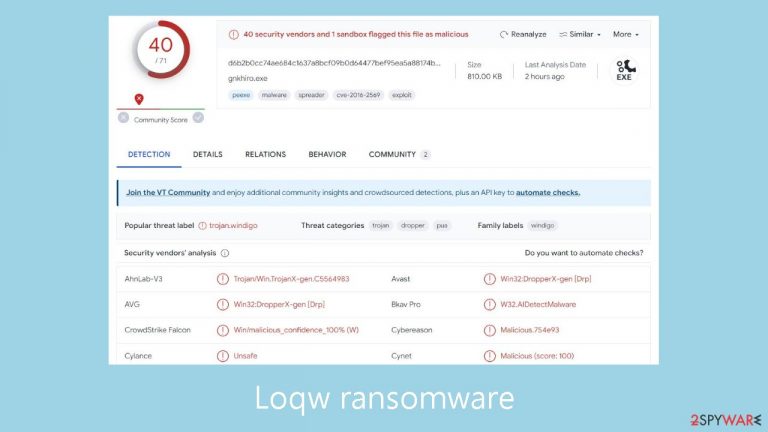
Loqw is an exceptionally destructive computer virus that employs an advanced RSA encryption algorithm to secure personal documents, videos, pictures, databases, and other data. Because of this code's intricacy, decrypting files without the hackers' unique decryption key is extremely difficult.
As a result, getting back access to your data almost becomes impossible. The virus adds a .loqw extension to encrypted files and replaces their original icons with a new one, making the data unreadable. There could be serious repercussions from this disturbance, particularly for those who don't have backup copies of their important data.
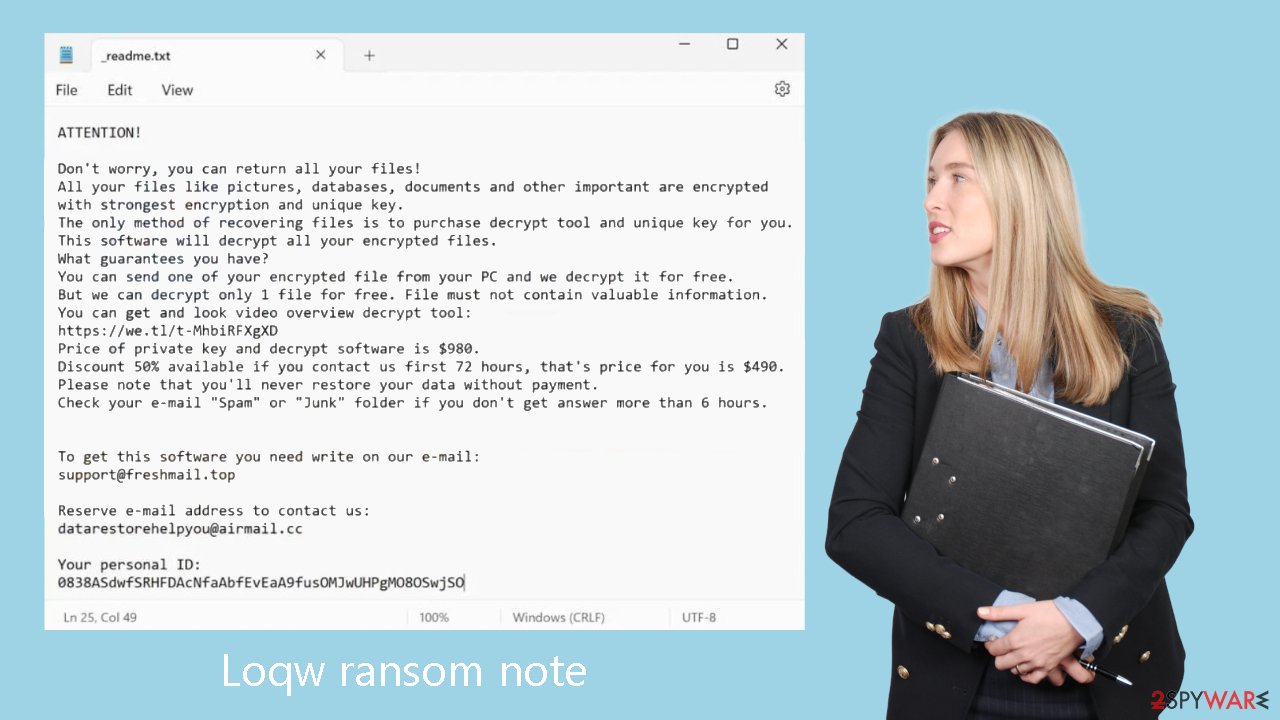
The ransom note file _readme.txt is left behind by the malware when it has successfully infected a system. This file contains a request for payment in cryptocurrency, usually asking victims to send $480 or $980 in Bitcoin.
| NAME | Loqw |
| TYPE | Ransomware, file-locking malware |
| MALWARE FAMILY | Djvu ransomware |
| FILE EXTENSION | .loqw |
| RANSOM NOTE | _readme.txt |
| RANSOM AMOUNT | $490/$980 |
| CONTACT | support@freshmail.top, datarestorehelpyou@airmail.cc |
| FILE RECOVERY | There is no guaranteed way to recover locked files without backups. Other options include paying cybercriminals (not recommended, might also lose the paid money), using Emisoft's decryptor (works for a limited number of victims), or using third-party recovery software |
| MALWARE REMOVAL | After disconnecting the computer from the network and the internet, do a complete system scan using a security program |
| SYSTEM FIX | As soon as it is installed, malware has the potential to severely harm some system files, causing instability problems, including crashes and errors. Any such damage can be automatically repaired by using FortectIntego PC repair |
The ransom note
Cybercriminals use the ransom note as a means of communication, asking for money to release the victim's files in return. According to the note, all of the victim's files, including databases, papers, photos, and other important data, have been encrypted with strong algorithms and a unique key. The only way to get back access to the files is to pay the hackers, who will then give you a decryption program and the matching private key.
ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-MhbiRFXgXD
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshmail.topReserve e-mail address to contact us:
datarestorehelpyou@airmail.ccYour personal ID:
–
The cybercriminals propose decryption of one file as a token gesture if the victim submits it as a small assurance. But they make it clear that the file shouldn't include any important information. To further entice the victim, they provide a video demonstration of the decryption tool. The established price for the private key and decryption software is $980; but, if the victim contacts the cybercriminals within the first 72 hours, the amount drops to $490. The notice emphasizes that paying is the only way for the victim to get their data back.
The ransom message lists two email addresses for correspondence: datarestorehelp@airmail.cc and support@freshmail.top. The victim is instructed by the crooks to send an email to request the decryption software. However, interacting with the cybercriminals is strongly discouraged for several reasons.
Cybercriminals are extremely unreliable since, by encrypting the victim's files, they have already committed crimes. There is no guarantee that they will provide the required tools or decrypt the files, even after they have received the ransom. Interacting with cybercriminals puts more people and organizations in danger down the road since it just serves to legitimize their illegal behavior and offer financial support for it.
Remove Loqw ransomware
For those who have never dealt with an attack by ransomware, navigating the aftermath can be difficult. But, making the correct decisions is essential and can have a big impact on your chances of getting your data back.
As soon as possible, disconnect your computer from the internet to prevent malware infections on other devices on the same network. Disconnecting your device can help stop the spread of malware because it frequently uses networks to interact with distant Command & Control servers. To do this, take the actions listed below:
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet
- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
You can manually remove the Loqw ransomware from your device if it has taken over and it is currently offline. However, because of its complexity, this process calls for extensive IT knowledge. Generally speaking, it is recommended to use specialist software created especially for ransomware removal or to seek the assistance of an expert.
If not done correctly, trying to remove the ransomware manually carries dangers and could do further harm. As a result, to properly remove the virus, it is advised to do a thorough system scan using reliable security software like SpyHunter 5Combo Cleaner or Malwarebytes. These technologies are skilled in locating and removing every harmful element connected to ransomware.
In addition, it is strongly advised to utilize a trustworthy recovery program FortectIntego to handle any possible problems with the system, including crashes or errors, that might occur after the virus has been successfully removed.
Recover .loqw files
Despite popular assumptions, security software is unable to accomplish the amazing feat of recovering personal files encrypted by ransomware. Its main job is to detect and get rid of dangerous apps while protecting your device from more dangers in the future. Beyond the scope of anti-malware software, a different method is required for the recovery of encrypted ransomware data. Still, having this kind of software is essential for seeing any problems and strengthening device security.
Ransomware encrypts files and creates a distinct ID and difficult encryption key when it is launched. The hackers coordinating the attack receive this information and utilize it to obtain the matching decryption key needed to access the users' data. Unfortunately, these crooks do not give away the decryptor for free because their goal is to take advantage of the situation.
We highly advise looking into the alternatives listed below rather than choosing to pay. As there's a chance of corruption during the recovery procedure, make a backup copy of the encrypted data before moving further. The Emsisoft decryption tool is a viable solution, but there is no guarantee that it will work in your particular situation.
- Download the app from the official Emsisoft website.

- After pressing Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.

- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.

- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.

- Press Decrypt.

From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
If your data was encrypted with an online ID, Emsisoft's tool won't work. In such a case, we recommend trying specialized data recovery software instead.
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders which you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
Another alternative is to exercise patience and wait for security researchers and companies to develop a free decryption tool. This often occurs when vulnerabilities are identified within the encryption code used by the malware or when law enforcement agencies seize the cybercriminals' servers. It is important to note that there is no guarantee that such a solution will be created in the future. Nevertheless, we recommend following the provided links to explore the possibility of finding a decryptor for this particular virus.
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

Getting rid of Loqw virus. Follow these steps
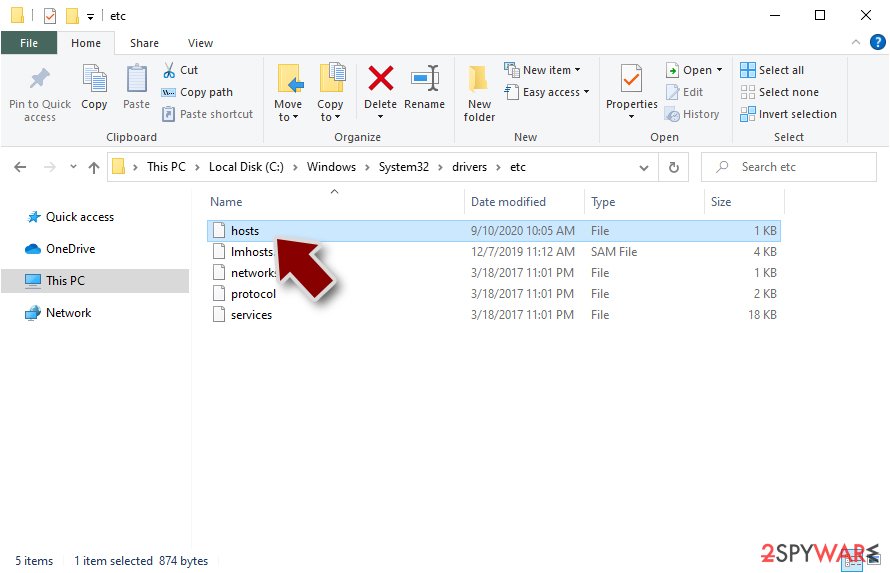
Restore Windows "hosts" file to its original state
Some ransomware might modify Windows hosts file in order to prevent users from accessing certain websites online. For example, Djvu ransomware variants add dozens of entries containing URLs of security-related websites, such as 2-spyware.com. Each of the entries means that users will not be able to access the listed web addresses and will receive an error instead.
Here's an example of “hosts” file entries that were injected by ransomware:
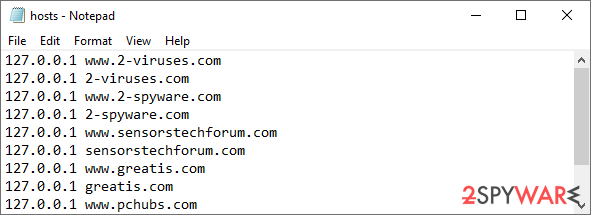
In order to restore your ability to access all websites without restrictions, you should either delete the file (Windows will automatically recreate it) or remove all the malware-created entries. If you have never touched the “hosts” file before, you should simply delete it by marking it and pressing Shift + Del on your keyboard. For that, navigate to the following location:
C:\\Windows\\System32\\drivers\\etc\\
Report the incident to your local authorities
Ransomware is a lucrative, highly illegal business, and authorities are actively targeting ransomware operators. The level of investigation and follow-up depends on the country, the scale of the incident, and whether the attack is linked to known ransomware groups. To increase the likelihood of identifying the culprits, the agencies need information. In many cases, reports are used primarily for intelligence gathering, trend analysis, and victim support rather than immediate identification of attackers.
Therefore, by reporting the crime, you could help stop the cybercriminal activities and catch the threat actors. Reporting does not guarantee investigation or recovery of data, but it contributes to broader efforts to track ransomware campaigns. Make sure you include all the possible details, including how did you notice the attack, when it happened, etc. Relevant details may also include affected systems, ransom demands, cryptocurrency wallet addresses, and any communication with the attackers. Additionally, providing documents such as ransom notes, encrypted files, or malware executables would be beneficial.
Law enforcement agencies typically deal with online fraud and cybercrime, although it depends on where you live. Here is the list of local authority groups that handle incidents like ransomware attacks, sorted by country:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

If your country is not listed above, you should contact the local police department or communications center.
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
