“Win Mac Book M2” scam (fake) - Free Guide
“Win Mac Book M2” scam Removal Guide
What is “Win Mac Book M2” scam?
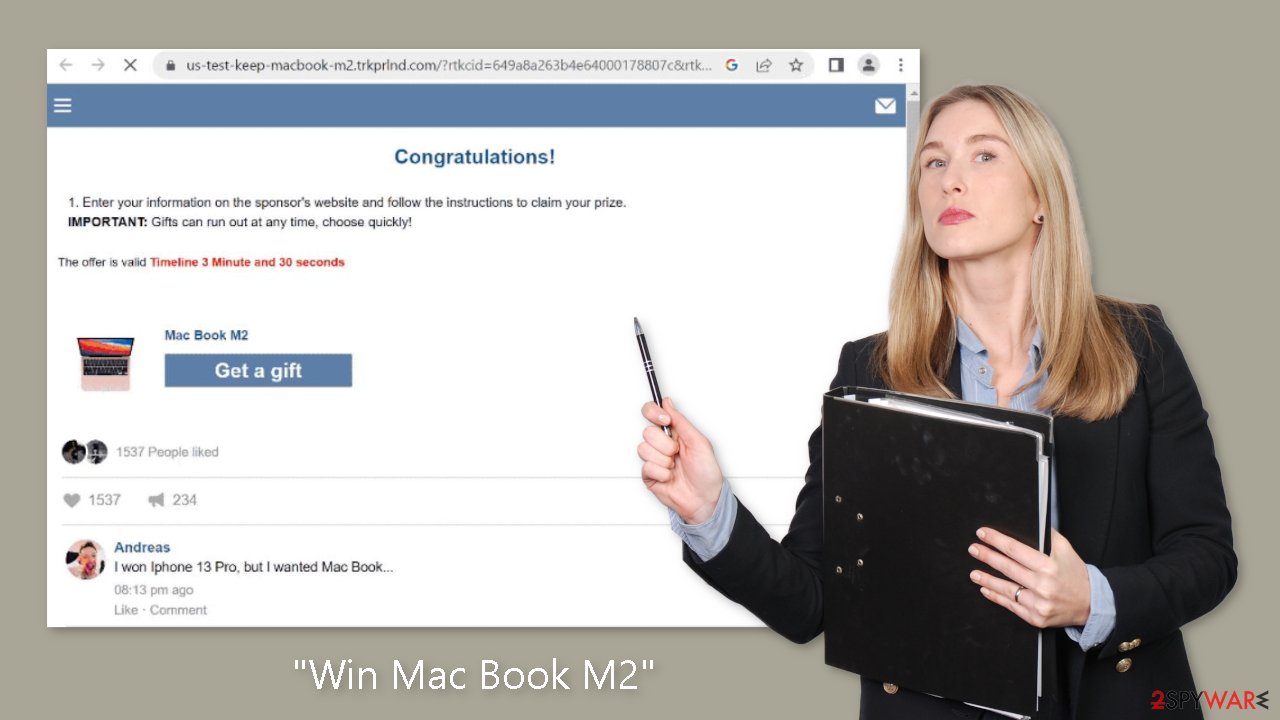
“Win Mac Book M2” is a fake phishing site designed to trick unsuspecting users

The internet is a vast and dynamic space that offers countless opportunities, but it is also a haven for scammers who seek to exploit unsuspecting users for personal gain. The “Win Mac Book M2” scheme is one such scam that has recently gained popularity. This deceptive campaign preys on people's desire for prizes and rewards, luring them in with the promise of winning a highly sought-after Mac Book M2 in exchange for providing personal information to a sponsored website.
Behind the guise of a generous giveaway, however, lurks a nefarious phishing[1] attempt designed to deceive and steal valuable data from unsuspecting victims. In this article, we will investigate the complexities of the “Win Mac Book M2” scam, expose its tactics, and shed light on the potential risks.
| NAME | Win Mac Book M2 |
| TYPE | Online scam, fraud, phishing |
| SYMPTOMS | Claims that a user can win a MacBook M2 |
| DISTRIBUTION | Shady websites, deceptive ads |
| DANGERS | Monetary losses, personal data compromise, malware infections |
| ELIMINATION | It is recommended to scan your system with antivirus tools to check it for adware |
| FURTHER STEPS | If you want to clean your web browsers quickly and/or fix virus damage automatically, we recommend using the FortectIntego repair tool |
Tactics of the “Win Mac Book M2” scam
When users come across the “Win Mac Book M2” scam, they are greeted with an ostensibly exciting message of congratulations and the enticing opportunity to win a valuable prize. The con uses a variety of psychological techniques to create a sense of urgency and exclusivity. For example, the webpage prominently displays a countdown timer, which ticks away to indicate that the offer is limited and time-sensitive.
In an attempt to boost credibility, the page also includes fabricated comments that look like Facebook testimonials from alleged previous winners. Users are instructed to enter their information on a sponsor's website and follow further instructions in order to claim the promised prize. This process usually begins innocently enough by asking for the user's email address in order to contact them.
However, the deception is revealed when users are redirected to a different website rather than receiving a reward. This redirect can take you to a variety of malicious sites, including phishing sites that target other sensitive data, such as login credentials, personally identifiable information, or credit card numbers. Victims may be duped into making fraudulent payments under the guise of shipping fees, transactions, subscriptions, or other bogus charges in some cases.
Phishing scams and the threats they pose to user security
Phishing scams, such as the “Win Mac Book M2” scheme, are more than just annoyances; they pose serious threats to user security. These scams lay the groundwork for a wide range of malicious activities by luring people into providing personal information. Email addresses obtained through such schemes can be used in spam campaigns, flooding victims' inboxes with unwanted and potentially harmful messages.
In turn, spam is used to promote various scams and malware, such as trojans, ransomware, and cryptominers, which can compromise the integrity of a user's system and result in significant financial losses. Furthermore, falling victim to phishing scams puts people at risk of identity theft.
Cybercriminals can use stolen personal information to assume the victim's identity, conduct fraudulent activities, or sell the data on the dark web. Identity theft can have devastating consequences, ranging from financial ruin to reputational damage.
Safeguarding against online scams and malicious redirects
Individuals must take proactive measures to protect themselves online in a digital landscape rife with fraudulent schemes. Users can reduce the risks associated with scams like the “Win Mac Book M2” scheme by staying informed and implementing best practices for online safety.
To begin with, exercising caution while browsing the internet is critical. Scam sites frequently employ rogue advertising networks, which can force-open deceptive webpages upon access or when interacting with certain elements on a page, such as buttons, text input fields, links, or advertisements. Users should exercise caution when clicking on suspicious links or engaging with dubious content.
Mistyping the URL of a website can also result in a redirect to a deceptive page. As a consequence, it is critical to double-check URLs before visiting them and to avoid visiting websites that offer pirated content or other dubious services. Such sites frequently use rogue advertising networks, making them more vulnerable to hosting scams or redirecting users to malicious sites.
Furthermore, users should exercise caution when granting permission for browser notifications. For example, the “Win Mac Book M2” scam asks for permission to send browser notification spam. Denying notification requests and blocking notifications from suspicious sites can help protect you from being exposed to scams and unwanted advertisements.
Another important practice is to only download software from official and verified sources. Users should exercise caution during the installation process and avoid accepting bundled software or agreeing to potentially harmful additional offers. Vigilance in this area can aid in the prevention of bundled or malicious software infiltration.
Disable push notifications
Push notifications have been used for many years; they can be used on both desktop and mobile devices, and many websites allow you to enable them when you visit them. While some may choose to do so, most users are unwilling to expose themselves to potential spam, so they will have little experience with push notifications.
Unfortunately, scammers are constantly devising new ways to trick users into subscribing because they are guaranteed that ads will be served directly to them, regardless of which websites are being visited at the time. Scammers can generate revenue over time by forcibly displaying advertisements to users.
The “Win Mac Book M2” scam frequently leads to websites that deceptively ask people to enable notifications. For example, you may be informed that there is a video to be viewed and that the only way to access it is to click the “Allow” button. If you comply, you will be allowing that site to send you push notification spam, along with a slew of malicious links and misleading messages.
To stop the malicious activity, go to your browser's site settings and block the relevant URL from sending you these notifications. Take the following steps:
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the URL's drop-down menu.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
- Click on More actions and select Block.
Check your system for adware
Scam content is unfortunately common when visiting suspicious websites, whether intentionally or unintentionally. Despite their popularity, peer-to-peer[2] networks and software crack distributors pose significant risks due to booby-trapped links and malware spread via repacked software installers or malicious ads. Adware[3] infections can also cause redirections to scams such as the “Win Mac Book M2” scheme, increasing the likelihood of encountering phishing attempts.
It is strongly recommended that you check your system for infections using reputable security software such as SpyHunter 5Combo Cleaner or Malwarebytes. Adware and malware can not only compromise your privacy, but they can also damage your system, resulting in unexpected errors and instability. To effectively remove these threats, consider using FortectIntego. If you prefer to do it yourself, use the instructions below to locate and remove adware from your system.
Getting rid of “Win Mac Book M2” scam. Follow these steps
Uninstall from Windows
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ Peer-to-peer. Wikipedia. The free encyclopedia.
- ^ Adware. Malwarebytes. Cybersecurity Basics.









