Alureon - Misused name. Detailed guide. Removal instructions for 2019
Alureon Removal Guide
What is Alureon?
Alureon is a persistent Trojan used to steal data and inject malicious pieces on the system too

Alureon is a relatively old cyber threat – it was first spotted by researchers in 2007 and reached its peak in 2010 when it was considered the second biggest botnet at the time.[1] The virus entered PCs by being manually installed by users, such as when they downloaded rogue anti-virus software like Security Essentials 2010. After making several modifications within the system, the malware establishes itself as a rootkit[2] and starts intercepting the system's network traffic, resulting in sensitive data harvesting. The threat also disables anti-malware software and redirects victims to spoofed websites on Google Chrome or any browser. Having in mind its danger level, there is no surprise that virus developers have included it into several scams, including “Windows Detected ALUREON” and “You have a ALUREON virus” scam.
| Name | Alureon virus |
| Type | Trojan/rootkit/botnet |
| Also known as | Windows Detected ALUREON scam; You Have A ALUREON Virus |
| First spotted | 2010 |
| Activity | Self-replicating trojan steals personal data and redirects to malicious websites |
| Main dangers | Loss of data, additional malware infections |
| Infiltration |
|
| Elimination | Use powerful anti-malware software to eliminate the rootkit |
| Optimization | Use FortectIntego to repair the damage done by malware |
Since Alureon virus does not emit any symptoms, users were not aware of the presence of the threat on their machines. Fortunately, cybercriminals made a mistake within its code, which led 0×80070032, 0x800704ec and 0×80501001 BSoDs appearing on victims' systems (32-bit versions of Windows OS) after the MS10-015 software update. This allowed experts to research the threat and work on the virus removal.
As soon as the rootkit enters the machine, it hijacks spoolsv.exe service and updates the master boot record which allows the virus to execute alternative Windows loading process. It also creates a randomly named copy of itself and copies it into the system folder. The threat then infects system drivers and modifies Windows Registry to assure persistence.
Researchers reported that Alureon is capable of changing DNS settings.[3] This allows the virus to reroute users to spoofed or malicious websites, where more malware can be obtained by using click fraud or other deceptive ways.
Once settled, the threat begins its activity immediately. After modifying system settings, the malware is capable of stealing the following:
- Credit card information;
- Usernames and passwords or all accounts;
- Social security numbers;
- PayPal information;
- Other sensitive data.
While it is an old threat, it does not mean it is not active anymore. Users can still get infected, so there might be a need to remove Alureon virus from their systems permanently. We recommend using reputable security software like SpyHunter 5Combo Cleaner, Malwarebytes in Safe Mode without an internet connection. Additionally, experts recommend changing passwords and using system repair tools like FortectIntego to fix the damage done by the rootkit.

Scams use the name of the malicious program
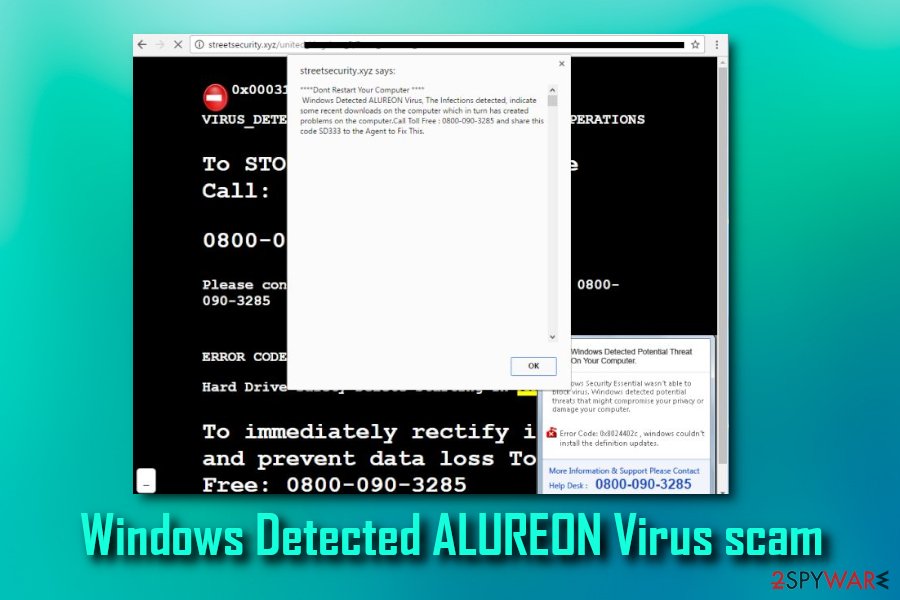
Being a rootkit, Alureon is hardly detected, so it is worth mentioning that there are crooks that make use of the notoriety of the popular malware name. However, you can hardly miss the Windows Detected ALUREON Virus scam that is floating around the Internet. In this case, you can be sure that the malware reported in the alert is fake.
“Windows Detected ALUREON virus” or “You Have A ALUREON Virus” pop-up belongs to the category of tech support scam. These alerts are displayed on the web browser after infecting it with an adware-type virus. Once installed, this threat generates dubious notifications and uses social engineering techniques to trick users into contacting scammers via the given number. Once contacted, they seek the following goals:
- Get the remote access to the system;
- Trick the user into installing malware by presenting it as effective anti-virus;
- Make the user pay for “fixing the system.”
“You Have A ALUREON Virus” or a similar scam is typically displayed within the browser. Because of special techniques, sometimes this window can't be left when desired and even increases the illusion that a real virus is hiding on the system. However, you just need to leave the affected web browser by canceling it and then remove the related adware from the system.
File an links on the internet can inject the payload of the notorious trojan
While some malware uses weak RDP or exploits kits to infiltrate systems (does not rely on the person to initiate the download), most of the cyber threats are installed by users themselves. Of course, they are not aware of the consequences when they download and install rogue software or use file-sharing, torrent sites. Nevertheless, users can also be tricked by social engineering used by criminals and believe that there is a need to download and install the malicious file.
Thus, users are advised to be vigilant when it comes to downloading freeware on their machines. Do not visit suspicious sites and do not download pirated software or keygens and cracks. While you may think you got yourself a free application, the malware is doing its job by stealing personal information in the background.
Additionally, we recommend you obtain legitimate security software that can protect from unauthorized file intrusion. Make sure that the anti-virus program is kept up to date at all times.
Find the Alureon virus and remove it from your machine with AV tools
No matter which version of the malware has infected your system, you should take care of the trojan removal without wasting your time. If you are lucky enough to find out that it is just a scam, you need to get rid of Windows Detected ALUREON Virus by removing all suspicious entries hiding in your system. Additionally, you should reset your web browser to default. Instructions on how to do that are given below.
However, if the real threat is hiding in your system, do not even try to remove Alureon virus manually as it makes hundreds of changes. We highly recommend opting for professional help to fix your system fully. You can attempt to eliminate the threat by using security software as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes. If you find out that the virus is blocking your anti-malware, make sure you reboot your computer to Safe Mode with Networking before a scan:
- Click on Windows Start button and write msconfig.exe into the command line;
- Click this entry and select Boot tab;
- Check Safe boot and Network options;
- Click OK and Restart buttons.
Remember that the rootkit can be especially hard to remove, therefore, you might have to disconnect your PC from the internet and only then attempt the elimination.
How to prevent from getting trojans
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Gregg Keizer. Microsoft smacks patch-blocking rootkit second time. Computerworld. The Voice of Business Technology.
- ^ Rootkit. Technopedia. Site that explains technology.
- ^ Win32/Alureon. Microsoft. Windows Defender Security Intelligence.
