Azop ransomware (virus) - Free Instructions
Azop virus Removal Guide
What is Azop ransomware?
Azop is a dangerous file-locking virus that demands $490/980 for a decryption tool
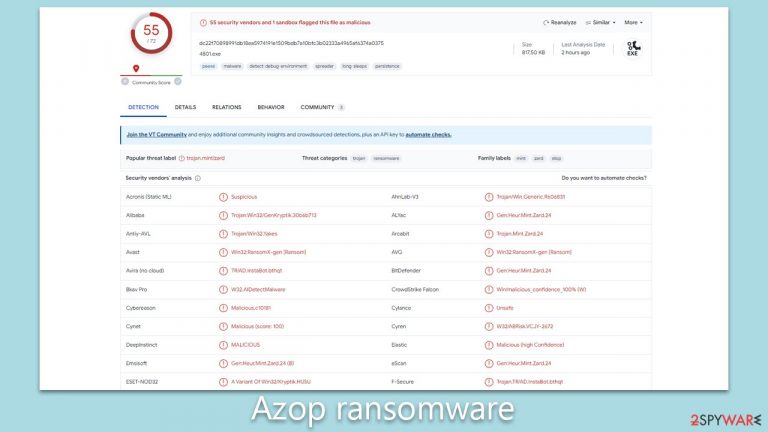
Azop ransomware is a formidable threat in the domain of cybersecurity due to its exceptional encryption capabilities and potency. As an offshoot of the well-known Djvu malware strain, this virus operates with a strategy consistent with its predecessors but is distinguished by its signature move – appending “.azop” to every compromised file, utilizing the RSA encryption cipher. Upon penetrating a computer system, it immediately embarks on an aggressive encryption spree, targeting every file within its reach, thus leaving the user's data inaccessible.
Upon successful encryption, Azop ransomware deposits a “readme.txt” ransom note within the compromised folders. This text file, filled with dire content, details the cybercriminal's demand: a ransom amounting to $980 in return for a decryption tool alleged to retrieve the affected files. Nevertheless, an element of mercy appears to be present. The ransom note mentions a 50% concession, reducing the amount to $490, provided victims make contact within a stipulated duration. For establishing communication, victims are provided with two email points of contact: support@freshmail.top and datarestorehelp@airmail.cc.
This malicious monetization strategy has not only plunged many users into a state of distress but has also raised red flags within the cybersecurity realm. For in-depth details about Azop virus, its elimination techniques, and potential data recovery solutions, refer to the subsequent information.
| Name | Azop virus |
|---|---|
| Type | Ransomware, file-locking malware |
| File extension | .azop extension appended to all personal files, rendering them useless |
| Family | Djvu |
| Ransom note | _readme.txt dropped at every location where encrypted files are located |
| Contact | support@freshmail.top and datarestorehelp@airmail.cc |
| File Recovery | There is no guaranteed way to recover locked files without backups. Other options include paying cybercriminals (not recommended, might also lose the paid money), using Emisoft's decryptor (works for a limited number of victims), or using third-party recovery software |
| Malware removal | After disconnecting the computer from the network and the internet, do a complete system scan using the SpyHunter 5Combo Cleaner security program |
| System fix | Upon installation, malware can cause severe damage to system files, resulting in instability issues such as crashes and errors. However, FortectIntego PC repair can automatically fix any such damage |
Ransomware distribution techniques
The propagation of ransomware like Azop, along with other Djvu variants, is chiefly facilitated through a tactic known as bundling. In the vast majority of incidents, individuals unknowingly become victims while downloading illicit copies of software or breached versions of premium applications.
Cybercriminals integrate the ransomware within these software installers. When a user runs such an installer, the hidden ransomware is simultaneously introduced into the system, often unnoticed. Following this installation, the ransomware begins its encryption campaign and subsequently demands a sizable ransom for the retrieval of the encrypted data.
To shield oneself from ransomware attacks, it's imperative to employ a blend of good online habits and rigorous security protocols. First and foremost, abstain from downloading pirated content or tampered software. It's essential to understand the reality that seemingly free downloads from unauthorized sources frequently harbor malicious payloads. Commit to obtaining software strictly from the official websites of vendors or other credible platforms.
Furthermore, it's vital to ensure that your computer's defense mechanisms, in the form of security software, are consistently updated. Frequent updates equip your system to counteract both established and emerging cyber threats. Whenever feasible, activate automatic update settings to guarantee no lapse in obtaining essential security enhancements.
In conclusion, cultivating the habit of regularly backing up indispensable data is a wise move. While this strategy doesn't directly thwart ransomware, it acts as a safety net for your data in the unfortunate event of an infection. It's advisable to store these backups in isolated environments, be it an external storage device or a cloud-based solution, to guarantee their immunity from potential ransomware onslaughts.
Cybercriminals' demands and why you shouldn't listen to them
Azop ransomware, like other Djvu variants, is meticulously crafted to extort funds from its victims. It achieves this by encrypting a wide range of commonly used file types, spanning from .jpg, .doc, to .pdf, and beyond. Ingeniously, these malware strains are coded to bypass system-specific files, particularly executables. This ensures the core functionality of the host device's operating system remains intact, although unforeseen repercussions can still materialize.
Subsequent to its encryption campaign, the ransomware plants a ransom message on the victimized device. This note serves to acquaint the user with the ransom sum, as well as the potential means to regain their encrypted data. An excerpt of a typical ransom note reads:
ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-e5pgPH03fe
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshmail.topReserve e-mail address to contact us:
datarestorehelp@airmail.ccYour personal ID:
The modus operandi of these cyber felons encompasses a suite of manipulative techniques geared towards pressuring victims into complying with their demands. A recurring ploy involves instilling the belief that acceding to the payment is the sole avenue for data recovery. Amplifying the allure of their proposition, they frequently dangle a 50% discount, contingent on payments being transacted within a prescribed window, often a mere 72 hours. Some even showcase their decryption prowess by offering complimentary decryption for a single file.
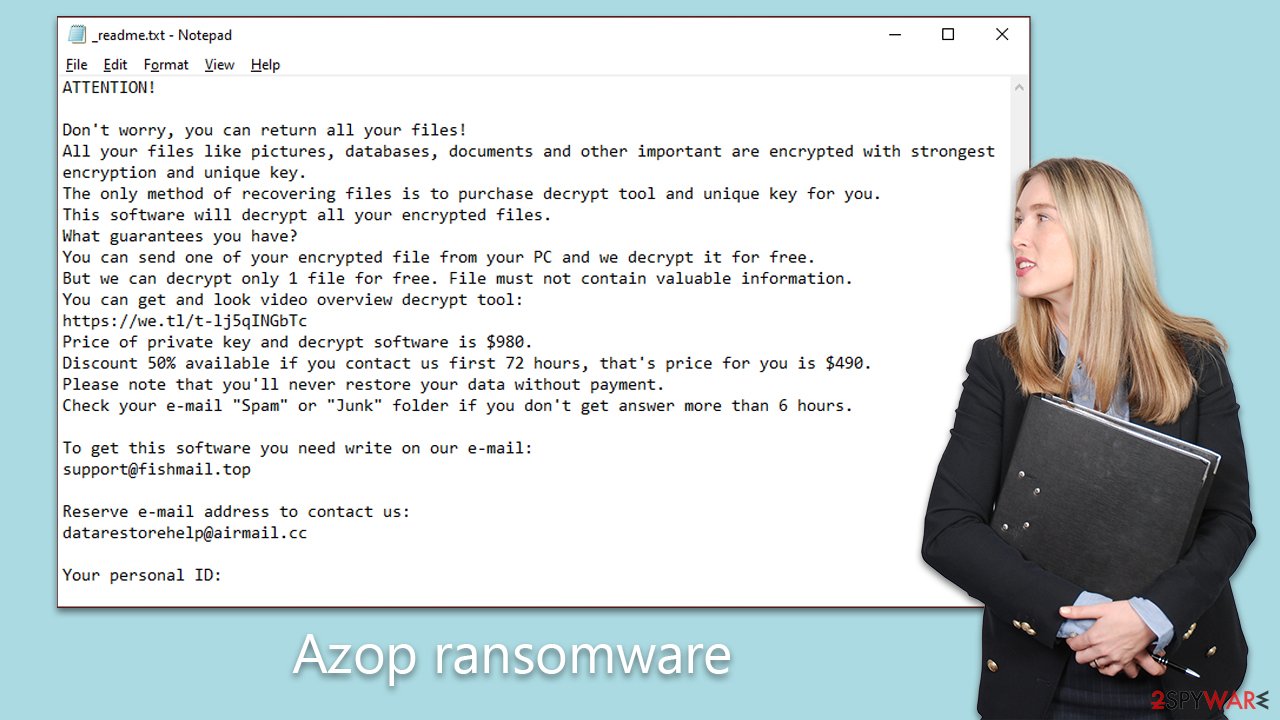
Such stratagems cultivate a heightened sense of urgency, luring victims into a hasty decision. Contrary to their assertions, succumbing to the ransom rarely guarantees the delivery or efficacy of the decryption solution. Furthermore, such capitulation inadvertently emboldens these malefactors, perpetuating and intensifying the prevalence of ransomware attacks.
Remove the ransomware and attempt to recover files
Addressing a ransomware attack necessitates precision, ensuring the adoption of the right measures to circumvent any exacerbation of the situation. Hasty decisions, like succumbing to the demand for ransom, can lead to significant financial losses without any assurance of obtaining the decryption solution.
Upon discerning the presence of ransomware on your system, your immediate action should be to disconnect the compromised device from the internet. This curtails the malware's potential for proliferation and severs its link with the Command and Control servers, which malefactors utilize for relaying directives to the ransomware.
Subsequently, initiate a thorough scan using your updated antivirus software, such as SpyHunter 5Combo Cleaner or Malwarebytes, making certain that its malware definitions are current. This scan will identify and expunge the Azop ransomware, paving the way for the subsequent data recovery process.
For those possessing a contemporary backup, leveraging it to restore your system could emerge as the most efficient recourse for data retrieval. Nonetheless, in the absence of backups, several alternatives are at your disposal, such as employing decryption utilities like Emsisoft's decryptor or resorting to specialized software tailored for data recovery. Comprehensive guidance on the deployment of these tools and other recovery avenues is elucidated further below.
Post the ransomware's removal, it's prudent to utilize a system repair tool akin to FortectIntego to meticulously analyze and rectify any system inconsistencies or malfunctions traceable to the malware's activity. While a fresh installation of the Windows OS can yield comparable outcomes, it might be daunting for some, carrying the risk of total data loss.
Equally paramount is the commitment to proactive measures to thwart subsequent intrusions, encompassing consistent backups of crucial files and cultivating an acute awareness of potential cyber threats. It's also imperative to notify the relevant law enforcement agencies about the breach and restore the integrity of any breached accounts spanning online banking or social platforms.
In summation, the adoption of judicious steps in the aftermath of a ransomware attack is instrumental in mitigating damages and fortifying against ensuing cyber threats. Adherence to the outlined procedures, supplemented with preventive measures, enables victims to not only recuperate their compromised data but also to fortify their digital defenses.
Getting rid of Azop virus. Follow these steps
Important steps to take before you begin malware removal
File encryption is one component of a ransomware infection, which may also include credential theft, persistence mechanisms, and lateral movement. However, it is important to understand that malware may perform various changes within a Windows operating system, including persistence, scheduled tasks, registry modifications, and security feature tampering.
IMPORTANT for those without backups! →
If you attempt to use security or recovery software immediately, you might permanently damage your files, and even a working decryptor then would not be able to save them.
Before you proceed with the removal instructions below, you should copy the encrypted files onto a separate medium, such as USB flash drive or SSD, and then disconnect them from your computer. The storage device should remain disconnected after copying to prevent accidental modification or deletion. Encrypted data itself does not contain active malicious code, but only the encrypted files—not executables or scripts—should be transferred.
The instructions below might initially seem overwhelming and complicated, but they are not difficult to understand as long as you follow each step in the appropriate order. This comprehensive free guide will help you to handle the malware removal and data recovery process correctly.
If you have any questions, comments, or are having troubles with following the instructions, please do not hesitate to contact us via the Ask Us section.
IMPORTANT! →
It is vital to eliminate malware infection from the computer fully before starting the data recovery process, otherwise ransomware might re-encrypt retrieved files from backups repeatedly.
Isolate the infected computer
Some ransomware strains aim to infect not only one computer but hijack the entire network. As soon as one of the machines is infected, malware can spread via the network and encrypt files everywhere else, including Network Attached Storage (NAS) devices. NAS devices are commonly compromised via reused administrator credentials and remote access services, and attackers may also delete existing snapshots. If your computer is connected to a network, it is important to isolate it to prevent re-infection after ransomware removal is complete.
In modern environments, ransomware often spreads using stolen credentials, remote management tools, VPN connections, and cloud synchronization services, not only through shared network drives.
The easiest way to disconnect a PC from everything is simply to plug out the ethernet cable. This does not disconnect wireless networks, VPN connections, or cloud services, which must also be disabled separately. However, in the corporate environment, this might be extremely difficult to do (also would take a long time). In many organizations, devices are centrally managed, and network isolation is typically performed by IT or security teams using endpoint security or device management tools. The method below will disconnect from all the networks, including local and the internet, isolating each of the machines involved.
On modern Windows systems, network connections can also be disabled through the Settings app or automatically isolated using endpoint detection and response (EDR) tools.
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
If you are using some type of cloud storage you are connected to, you should disconnect from it immediately. It is also advisable to disconnect all the external devices, such as USB flash sticks, external HDDs, etc. Once the malware elimination process is finished, you can connect your computers to the network and internet, as explained above, but by pressing Enable instead. Before reconnecting, credentials should be reset, persistence mechanisms checked, and backups verified to ensure reinfection does not occur.
Scan your system with anti-malware
If you are a victim of ransomware, you should employ anti-malware software for its removal. Some ransomware can self-destruct after the file encryption process is finished. Even in such cases, malware might leave various data-stealing modules or could operate in conjunction with other malicious programs on your device.
SpyHunter 5Combo Cleaner or Malwarebytes can detect and eliminate all ransomware-related files, additional modules, along with other viruses that could be hiding on your system. The security software is really easy to use and does not require any prior IT knowledge to succeed in the malware removal process.
Restore Windows "hosts" file to its original state
Some ransomware might modify Windows hosts file in order to prevent users from accessing certain websites online. For example, Djvu ransomware variants add dozens of entries containing URLs of security-related websites, such as 2-spyware.com. Each of the entries means that users will not be able to access the listed web addresses and will receive an error instead.
Here's an example of “hosts” file entries that were injected by ransomware:
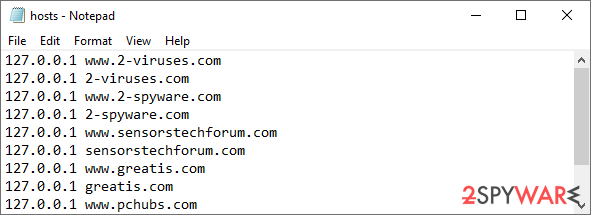
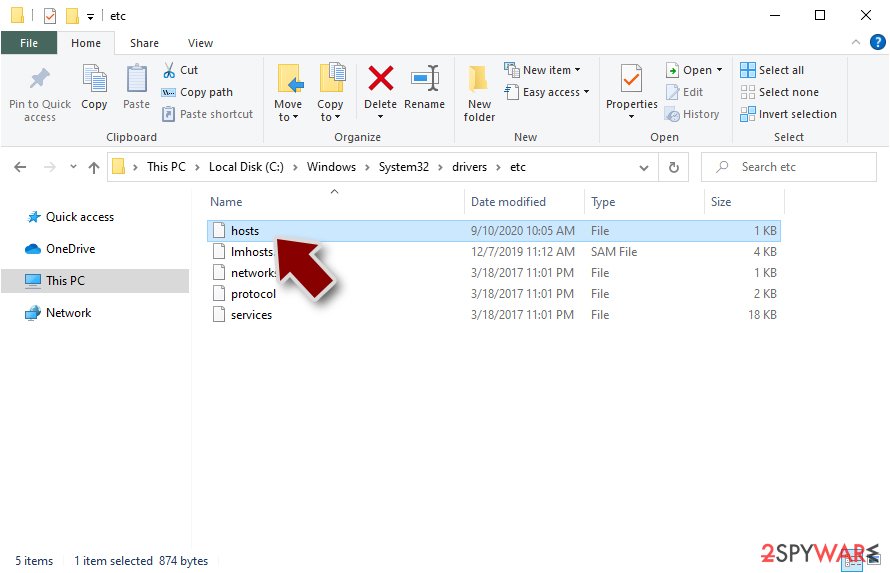
In order to restore your ability to access all websites without restrictions, you should either delete the file (Windows will automatically recreate it) or remove all the malware-created entries. If you have never touched the “hosts” file before, you should simply delete it by marking it and pressing Shift + Del on your keyboard. For that, navigate to the following location:
C:\\Windows\\System32\\drivers\\etc\\
Use Emsisoft decrytor for Djvu/STOP
If your computer got infected with one of the Djvu variants, you should try using Emsisoft decryptor for Djvu/STOP. It is important to mention that this tool will not work for everyone – it only works if data was locked with an offline ID due to malware failing to communicate with its remote servers.
Even if your case meets this condition, somebody from the victims has to pay criminals, retrieve an offline key, and then share it with security researchers at Emsisoft. As a result, you might not be able to restore the encrypted files immediately. Thus, if the decryptor says your data was locked with an offline ID but cannot be recovered currently, you should try later. You also need to upload a set of files – one encrypted and a healthy one to the company's servers before you proceed.
- Download the app from the official Emsisoft website.

- After pressing Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.

- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.

- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.

- Press Decrypt.

From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
Restore files using data recovery software
Since many users do not prepare proper data backups prior to being attacked by ransomware, they might often lose access to their files permanently. Paying criminals is also very risky, as they might not fulfill the promises and never send back the required decryption tool.
While this might sound terrible, not all is lost – data recovery software might be able to help you in some situations (it highly depends on the encryption algorithm used, whether ransomware managed to complete the programmed tasks, etc.). Since there are thousands of different ransomware strains, it is immediately impossible to tell whether third-party software will work for you.
Therefore, we suggest trying regardless of which ransomware attacked your computer. Before you begin, several pointers are important while dealing with this situation:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.

- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.

Find a working decryptor for your files
File encryption is a process that is similar to applying a password to a particular file or folder. However, from a technical point of view, encryption is fundamentally different due to its complexity. By using encryption, threat actors use a unique set of alphanumeric characters as a password that can not easily be deciphered if the process is performed correctly.
There are several algorithms that can be used to lock data (whether for good or bad reasons); for example, AES uses the symmetric method of encryption, meaning that the key used to lock and unlock files is the same. Unfortunately, it is only accessible to the attackers who hold it on a remote server – they ask for a payment in exchange for it. This simple principle is what allows ransomware authors to prosper in this illegal business.
While many high-profile ransomware strains such as Djvu or Dharma use immaculate encryption methods, there are plenty of failures that can be observed within the code of some novice malware developers. For example, the keys could be stored locally, which would allow users to regain access to their files without paying. In some cases, ransomware does not even encrypt files due to bugs, although victims might believe the opposite due to the ransom note that shows up right after the infection and data encryption is completed.
Therefore, regardless of which crypto-malware affects your files, you should try to find the relevant decryptor if such exists. Security researchers are in a constant battle against cybercriminals. In some cases, they manage to create a working decryption tool that would allow victims to recover files for free.
Once you have identified which ransomware you are affected by, you should check the following links for a decryptor:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

If you can't find a decryptor that works for you, you should try the alternative methods we list below. Additionally, it is worth mentioning that it sometimes takes years for a working decryption tool to be developed, so there are always hopes for the future.
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
