Baldr malware (Removal Guide) - Free Instructions
Baldr malware Removal Guide
What is Baldr malware?
Baldr malware – a trojan that is linked to Russian underground hackers
Baldr malware is a new, cross-platform information-stealing trojan that captures valuable information including passwords and important files. The virus is offered on the black market forums[1] for as low as $150. The data this malware steals mainly includes profiles, cryptocurrency wallets, text documents and Telegram sessions or records from VPN clients. It was spotted back in 2018, and in 2019 more information was published by cybersecurity researchers.
Security experts link this Trojan to at least three Russian hacker groups: Agressor is responsible for the distribution of this malware, Overdot manages sales and promotion, and LordOdin takes over its development. The reports on this malware state that the Baldr trojan appears skillfully crafted and persistent.[2]
| Name | Baldr malware |
|---|---|
| Type | Info-stealer |
| Category | Trojan |
| Symptoms | Affects performance of the machine, infiltrates other programs |
| Main danger | Steals information like passwords, credit card information, valuable files. Can lead to privacy issues or money loss |
| Distribution | Fallout EK, fake updates and software cracks, spam email attachments |
| Price online | $150 |
| Detection names |
|
| Elimination | Use FortectIntego for Baldr malware removal. Make sure to clean the system and get rid of the virus damage and additionally installed threats |
Baldr malware is an information-stealing tool that can be purchased online by anyone for $150, meaning that even novice hackers can use it. On the other hand, more advanced malicious actors might take up the development and expand the range of capabilities this malware can offer.
While lesser threats like potentially unwanted programs mainly focus on harvesting non-personally identifiable information, the Baldr virus can access and steal personal and even financial information:
- cryptocurrency wallet data;
- messaging application data;
- information from VPN clients;
- records from the computer directly;
- auto-fill passwords.
As any other trojan, Baldr malware is designed to infiltrate a targeted system and remain running in the background unnoticed. However, this is a virus that targets every victim individually it has no automatic spreading mechanism, as far as reports show. It is pushed and promoted by his authors and distributors.
There is no effort to hide the exfiltration process, and the trojan sends all the data in one network transfer that becomes obvious and noticeable no matter how little files it involves. Baldr malware searches for particular files on the machine and steals data stored on them:
- Doc;
- Docz;
- Log;
- Txt.
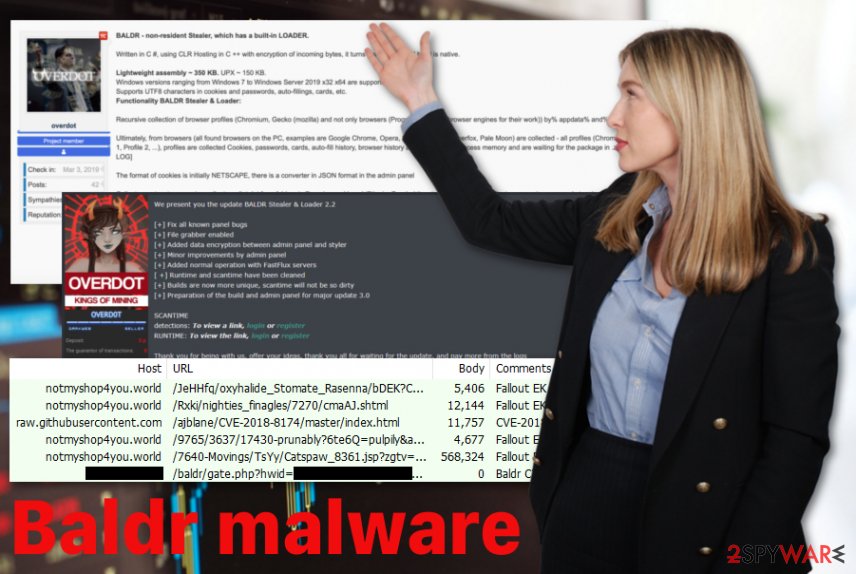
Baldr malware virus first appeared in January and right now malicious actors distribute 2.2 version of the trojan. Many cybercriminals reviewed this product of Russian hackers positively in hacking online forums. The virus often operates in a grab-and-go mode which means that it gathers data from the computer and sends to an attacker.
You need to remove Baldr malware as soon as you noticed because this threat infiltrates the targeted system, grabs all the needed data and packs it in the zip file to send it back to the developer. It can auto-delete itself after this process, and it makes much more difficult to know whether you've been affected by this it or not.
Baldr malware removal, later on, may only reveal traces of the damage and additionally installed malware not traces of this info-stealer. If the damage is already made, you need a professional tool like FortectIntego and remove all programs, files, malicious processes or even fix issues with your operating system.
Many experts[4] comment on the Baldr virus popularity and state that information stealers have been developed more powerful and efficient. Developers push new features and functions, make small threats that can affect everyday users and businesses.
People think they are downloading software, updates or free cracks, or gets Bitcoins for free but the only thing they get is this Baldr info-stealer. It may even lead to stolen cryptocurrency since the trojan exfiltrates data regarding various cryptocurrency wallets.
Trojan distribution and how to defend against it
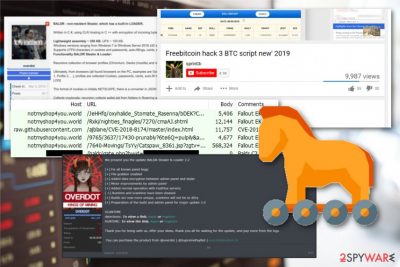
Russian hackers operate this info-stealer and distributed mainly in underground forums with the help of Agressor. It also is distributed via campaigns involving exploit kits or social engineering campaigns when fake Bitcoin generator application is promoted on YouTube and other platforms.
FallOut exploit kit in particular reported as one of the methods used to deliver this trojan. Trojanized applications disguised as cracks or hacking tools deliver this malware instead of the wanted app or tool.
Another more common way to spread this type of threats is spam emails and file attachments containing malicious scripts of harmful viruses like Trojans, malware, and keystroke loggers or even ransomware. Once the email is received and opened, it takes a few clicks of the mouse, and the machine gets infected.
You can avoid this infiltration if you pay more attention to these notifications, avoid opening and downloading ransom documents, executable files or archives attached to the email. Keeping anti-malware software running on the PC can also create the advantage of blocking the malicious content before initial infiltration.
Baldr malware damage elimination requires a thorough system cleaning
Given that Baldr malware virus is distributed using various campaigns, including exploit kits, keeping your machine up-to-date and all issues with the OS fixed can give you the advantage. It is especially crucial for businesses and companies because reducing the attack surface by removing unnecessary plugins and fixing system issues can help to keep the network safe.
However, when the trojan is already affecting the machine or a whole network, Baldr malware removal requires professional tools and proper help. FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes can clean the machine after the virus attack and possibly fix the damage or remove unwanted additional installs and intruders.
Make sure to remove Baldr malware and programs installed without our permission and consent. Based on malware distribution ways, this trojan can come with other threats or deliver a secondary payload of the cryptovirus or ransomware, so your machine may be at much more significant risk besides this info-stealer.
Getting rid of Baldr malware. Follow these steps
Manual removal using Safe Mode
Try rebooting to Safe Mode and then scan the computer with anti-malware, since Baldr malware can disable some security functions. This way trojan can be terminated properly:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Baldr malware using System Restore
System Restore may also help when removing Baldr trojan because this feature can restore the computer to a state when the malware was not running on the machine:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Baldr malware. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Baldr malware and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Brian Stack. Here's how much your personal information is selling for on the Dark Web. Experian. Information solutions.
- ^ Charlie Osborne. Grab-and-go Baldr malware enters the black market. ZDNet. Technology news.
- ^ Private_Cheat by pc_Ret v8.exe analysis. Virustotal. Online malware scanner.
- ^ Usunwirusa. Usunwirusa. Spyware related news.





















