BestChangeRu ransomware (Decryption Steps Included) - Free Guide
BestChangeRu virus Removal Guide
What is BestChangeRu ransomware?
BestChangeRu ransomware is the cryptovirus that targets Russian users and demands 25 000 Rubles in Bitcoin

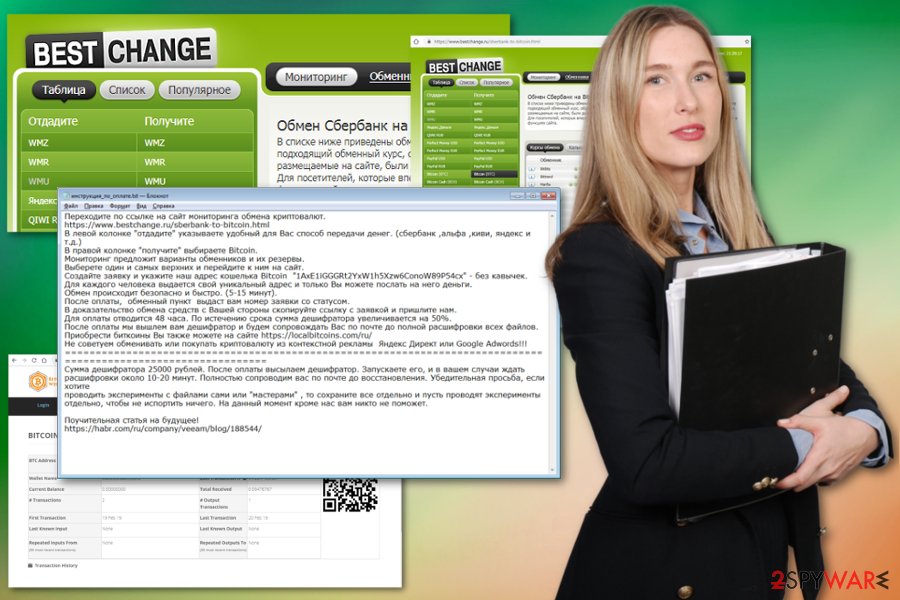
BestChangeRu ransomware is the crypto-extortion based virus that encrypts users' data and requires ransom to return files. Once your files are locked with a robust encryption algorithm, ransomware places инструкция по оплате.txt (payment instruction.txt) ransom note on the system and informs victims about how to proceed next. BestChangeRu virus authors demand 25 000 Rubles in Bitcoin, although they also note in the message that the price doubles after 48 hours. There is no guarantee that the alleged decryption tool exists, so stay away from contacting these people and remove BestChange Russia ransomware instead. Since the ransom note is written in the Russian language, it is clear that virus authors are targeting Russians, although it does not mean that victims from other parts of the world cannot be infected.
| Name | BestChangeRu ransomware |
|---|---|
| Type | Cryptovirus/data locker[1] |
| Symptoms | Encrypts files |
| Ransom note | инструкция по оплате.txt -payment instruction.txt |
| Main language | Russian |
| Ransom amount | 25 000 Russian Rubles in Bitcoin |
| Distribution method | Spam email attachments |
| Elimination | Use the anti-malware program for BestChangeRu ransomware removal and FortectIntego for virus damage |
Once the system gets infected, BestChangeRu ransomware virus changes certain system settings to enable the encryption on particular types of data. It affects your photos, documents, video or audio files or even archives and databases and files after data-locking could no longer be opened.
When BestChangeRu ransomware is done with the encryption and additional changes on the device, it delivers a ransom message in the form of the text file called инструкция по оплате.txt (payment instruction.txt) and places this file on every folder that contains locked files. The ransom note reads the following (translated from Russian):
Follow the link to the cryptocurrency exchange monitoring site.
https://www.bestchange.ru/sberbank-to-bitcoin.html
In the left-hand column “give” you indicate a convenient way for you to transfer money. (Sberbank, alpha, kiwi, yandex, etc.)
In the right-hand “get” column choose Bitcoin.
Monitoring will offer options for exchangers and their reserves.
Select the one and the top and go to them on the site.
Create a request and specify our Bitcoin wallet address ” 1AxE1iGGGRt2YxW1h5Xzw6ConoW89P54cx ” – without quotes.
Each person is given a unique address and only you can send money to him.
The exchange takes place safely and quickly. (5-15 minutes).
After payment, the exchange office will give you the application number with the status.
As proof of your exchange, copy the link with the application and send it to us.
48 hours are allowed for payment. At the end of the period, the amount of the decoder is increased by 50%.
After payment, we will send you a descrambler and will accompany you by mail until full decryption of all files.
You can also buy bitcoins at https://localbitcoins.com/ru/
We do not recommend to exchange or buy cryptocurrency from contextual advertising Yandex Direct or Google Adwords !!!
================================================= ================================================= ===========
The amount of the decoder is 25,000 rubles. After payment we will send the decoder. Run it, and in your cases wait for decryption about 10-20 minutes. Fully escort you to the mail before recovery. We kindly ask you if you want
to experiment with the files yourself or the “masters”, then save everything separately and let them conduct experiments separately, so as not to spoil anything. At the moment, except for us, no one will help you.
An instructive article for the future!
https://habr.com/ru/company/veeam/blog/188544/
Virus developers wrote a long message for BestChangeRu ransomware victims, and there are a few interesting features. The main focus of this note is to inform users about the payment and other actions, as the first line provides a link to BestChange website.
Further instructions on the cryptocurrency transaction show that BestChange Russia ransomware developers prefer Bitcoin over other currencies. Victims get 48 hours to pay up, but the ransom may increase by 50% after that. Based on previous ransomware victims, we do not recommend fulfilling this demand.[2]
Another interesting fact about the BestChangeRu ransomware ransom note is the link at the very end of the text that delivers to an article about Backup rule “3-2-1”.[3] This seems to be a joke because when your files get encrypted, data backups is the best solution for your lost files. However, you can employ special data recovery tools if you have no backups. Stay away from paying the demanded amount because it may lead to permanent money loss.
We highly recommend you to remove BestChangeRu ransomware as soon as possible so that you can avoid additional changes to the system or even virus damage. This is especially crucial when you think about data recovery later on.
For BestChangeRu ransomware removal, you should get a reputable anti-malware program and scan the system thoroughly. During the system check, a tool can indicate all threats and remove them from the computer while cleaning the damage. We can recommend using FortectIntego for the process.
Spam email contains infected files as attachments
Commonly used techniques like malspam campaigns get used by ransomware developers to deliver infected files with malicious macros or malware scripts. Researchers[4] often advise paying more attention to emails you get because of the risk this technique creates.
When you receive the email you were not expecting, pay more attention to details and information on the email itself because an URL presented in the email or the text directly like a button may load the page which triggers the extraction of malicious ransomware payload.
Also, attachments that contain malware droppers look legitimate enough for a user to download and open on the device. Stay away from files in .rar, .zip or .docx formats if attached to the email sent from questionable address. Once the document is opened or archive extracted, malicious script is triggered and releases infection on the system.
Avoid opening emails with suspicious senders or subject lines, sent from legitimately-looking service you do not use. You should delete those emails from the spam section or even the regular inbox if you are not sure about the purpose of the message.
Eliminate BestChangeRu ransomware and make sure to clean the system fully
For the best BestChangeRu ransomware removal results, users should get automatic malware-fighting tools like FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes. These programs can ensure total virus termination and performance improvement of the machine.
When BestChange Russia ransomware virus infiltrates the system, in addition to the encryption process, it changes system settings and adds malicious files/processes. Because of this reason, ransomware elimination requires professional help and additional features like the Safe Mode.
Once you remove BestChangeRu ransomware from the system entirely, you can attempt file recovery procedure. In case you do the opposite, all your recovered data will be immediately encrypted again. In case you have no backups, use our instructions for using third-party recovery applications.
Getting rid of BestChangeRu virus. Follow these steps
Manual removal using Safe Mode
Get rid of the BestChangeRu ransomware virus using antivirus tool but enter the Safe Mode with Networking first
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove BestChangeRu using System Restore
System Restore is the essential feature on Windows that allows users to get back to a previous state of the computer by choosing the restore point
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of BestChangeRu. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove BestChangeRu from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by BestChangeRu, you can use several methods to restore them:
Try Data Recovery Pro when you need an alternative for file backups
This program can recover data encrypted by ransomware, but it also helps with accidentally deleted files
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by BestChangeRu ransomware;
- Restore them.
Yet another Windows feature that helps when BestChangeRu ransomware affects the system is Windows Previous Versions feature
Unfortunately, Windows Previous Versions can only work for file recovery after System Restore
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Try ShadowExplorer to restore encrypted data
Use ShadowExplorer for file recovery when Shadow Volume Copies are left untouched
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Decrytption tool is not developed yet for BestChangeRu ransomware
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from BestChangeRu and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ 3 Reasons the Ransomware Threat will Continue. Trendmicro. Simply security blog.
- ^ Shaun Nichols. Less than half of paying ransomware targets get their files back. Theregister. Breaking news.
- ^ Michael Gillespie. Ransomware detection report. Twitter. Social media platform.
- ^ DieViren. Dieviren. Spyware related news.





















