Block Access Site adware (virus) - Free Guide
Block Access Site adware Removal Guide
What is Block Access Site adware?
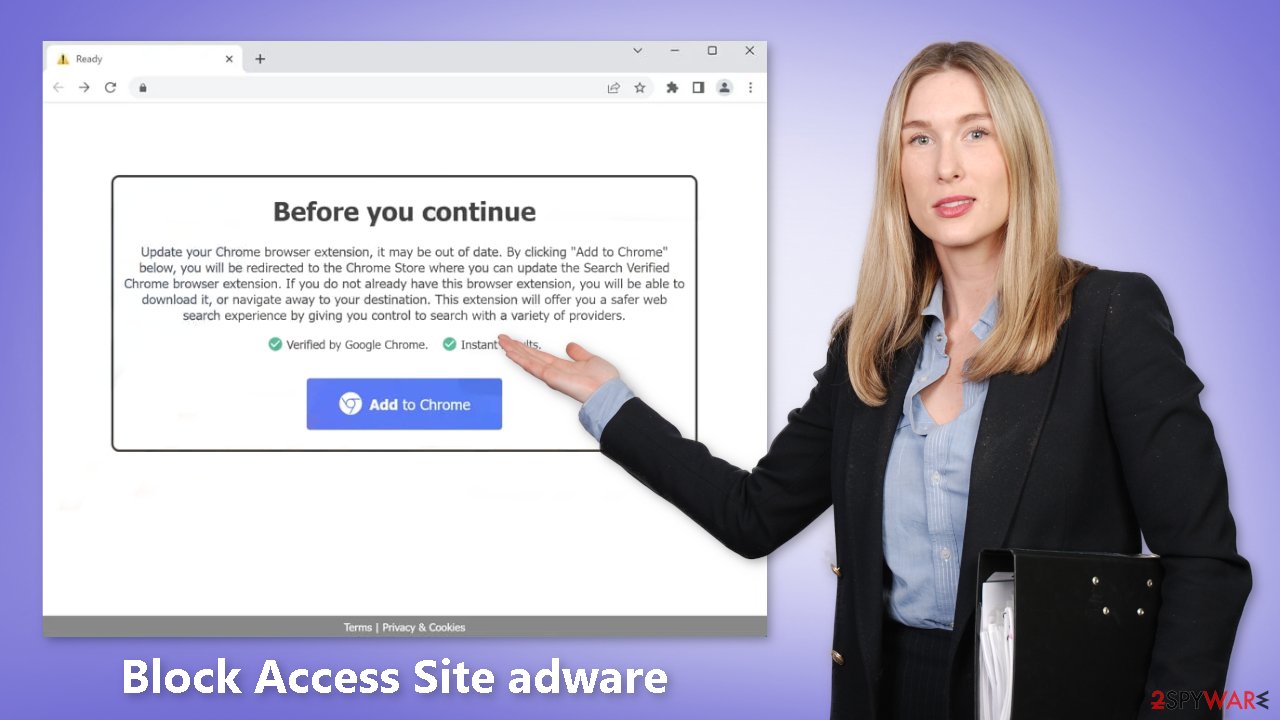
Block Access Site is a bogus browser extension that acts as adware when installed

Block Access Site is a bogus browser extension that acts as adware.[1] It causes an increased amount of commercial content, like pop-ups, banners, and redirects. It is advertised as an extension that blocks access to websites to increase productivity. The pop-ups may appear even when the browser is closed.
The main purpose of such applications is to generate revenue from pay-per-click advertising. They may also use rogue advertising networks[2] that place ads leading to dangerous websites. By clicking on links embedded in the ads, people may end up on scam pages that try to lure out personal information, trick people into downloading PUPs (potentially unwanted programs),[3] and even malware.
Usually, users start seeing ads promoting fake antivirus programs, software deals, adult websites, surveys, giveaways, and dubious dating platforms. If there is anyone else using the affected machine, especially children, it is important to remove this intruder as soon as possible.
| NAME | Block Access Site |
| TYPE | Browser hijacker; adware |
| SYMPTOMS | The extension starts generating intrusive advertisements and may change the main settings |
| DISTRIBUTION | Shady websites; deceptive ads, freeware installations |
| DANGERS | The ads may lead to dangerous websites controlled by crooks who try to take advantage of less IT-savvy users |
| ELIMINATION | Remove the extension through browser settings |
| FURTHER STEPS | Use FortectIntego to clear your browsers and fix any remaining damage |
Distribution methods
The Block Access Site is being promoted on a website that falsely claims the Chrome browser is out of date and offers to update it. The plugin is added to the web browser after completing the steps provided on this suspicious website. The fake Block Access Site extension has also been found on shady download pages. These “Downloader” sites are often found on websites that engage in illegal activities and are full of deceptive ads and sneaky redirects.
Google has stated that they will remove fake “Download” and “Play” buttons, but they still exist. Fake “Downloader” pages often use social engineering tactics[4] to trick users into installing a browser extension to “continue to the website” or for “security reasons.” However, you should never have to install any plugins or programs to access content on a legitimate website.
To avoid falling victim to these scams, it is recommended to only use official web stores and developer websites when installing extensions. These apps go through an extensive review process before they are listed on digital marketplaces, but it's still important to do your own research, read reviews, check ratings, and look at the number of users.
Freeware installations
Adware is frequently spread through the use of freeware distribution platforms, which secretly bundle additional programs into the installer. Many people quickly skip through the installation process and do not notice these additional files. While purchasing software licenses may seem costly, it can save you money in the long run by keeping your system running smoothly.
To avoid inadvertently installing adware, it's important to always select the “Custom” or “Advanced” installation method, read the Privacy Policy and Terms of Use to understand how your data will be used, and carefully review the file list to uncheck any unrelated applications.
Remove Block Access Site adware
Block Access Site adware is most likely attached as an extension to your browser that causes push notification spam, banners, surveys, redirects, and other commercial content. You should go to your browser settings and look at the extension list. We recommend removing plugins one by one to see if you notice any changes.
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Adware. Wikipedia, the free encyclopedia.
- ^ Zeljka Zorz. How does a rogue ad network function?. Helpnetsecurity. Cybersecurity News and Analysis.
- ^ Wendy Zamora. What is a PUP? – How to avoid potentially unwanted programs. Malwarebytes. Security Tips, Tricks, and How-Tos.
- ^ What is Social Engineering?. Webroot. Security for business.










