BlueCheeser ransomware (Decryption Steps Included) - Improved Instructions
BlueCheeser virus Removal Guide
What is BlueCheeser ransomware?
BlueCheeser ransomware – a file-encrypting parasite that urges payment of $400 in Bitcoin cryptocurrency
BlueCheeser ransomware is a malware string that employes the Advanced Encryption Standard[1] to lock up all files that are located on the infected device. Afterward, all filenames receive the .himr extension and the malware starts providing ransom demands via Instructions.txt Notepad message. BlueCheeser ransomware includes the crooks' Bitcoin wallet address and urges to transfer $400 in BTC. This is the total price required for the release of locked files. According to the English language that is used for writing the ransom message, hackers are targeting English-speaking people.
First discovered by a cybersecurity researcher named Raby,[2] BlueCheeser ransomware arrives at the computer system with the help of deceptive techniques such as email spam, hacked RDPs, cracked software, fake flash player updates, malvertising, or infectious hyperlinks. After the infiltration process, the ransomware virus brings the BlueCheeser.exe file to the Windows computer system and includes the executable in the Windows Task Manager section.
| Name | BlueCheeser ransomware |
| Category | Ransomware virus/malware |
| Discoverer | Raby |
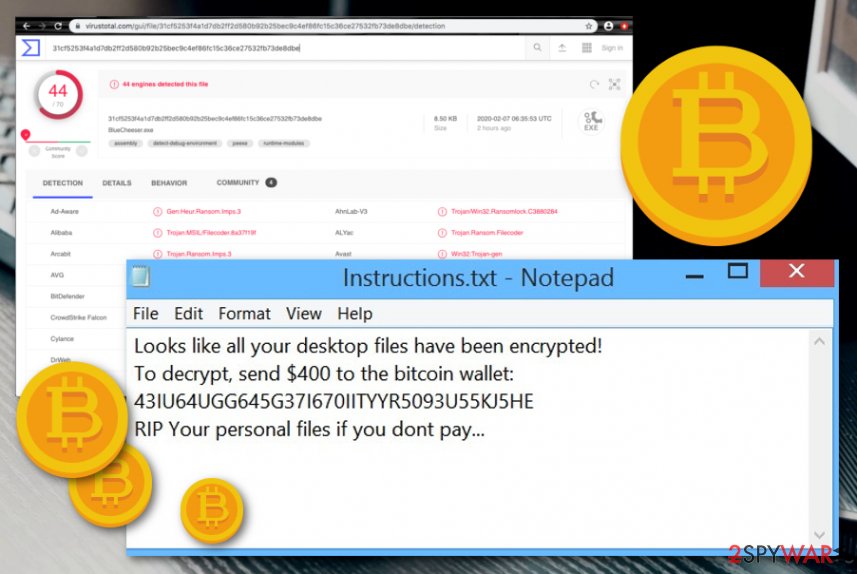
| Detection list | According to VirusTotal information, this malicious string has been discovered by 44 AV engines out of the total 70, at the time of writing |
| Encryption | The cyber threat employs the Advanced Encryption Standard and locks all the files and documents that are found on the targeted PC. All of the filenames get .himr extension added |
| Ransom demands | Cybercriminals provide ransom demands that reach up to $400 in Bitcoin. Also, they add the Bitcoin wallet number in the Instructions.txt ransom note |
| Target | According to the language in which the ransom note is written, the crooks are targetting English-speaking people |
| Related file | Once the malware breaks through the system's security, it can start planting on the computer whatever it wants. This includes the BlueCheeser.exe executable that is injected into the Windows Task Manager area |
| Distribution | The malware gets distributed through stealth techniques such as email spamming, the delivery of infected attachments, cracked software, fake updates, malvertising, infectious links, etc. |
| Termination | Get rid of the ransomware virus as soon as you find it lurking on your computer system. For this process, employ only reliable antimalware tools |
| Fix software | If you have discovered any system compromisation on your Windows machine, try using software such as FortectIntego for fixing the altered areas |
According to VirusTotal provided information,[3] BlueCheeser ransomware has been detected by 44 AV engines out of the total 70 available ones. Some of the detection names include Gen:Heur.Ransom.Imps.3, Trojan.Encoder.30952, HEUR:Trojan-Ransom.MSIL.Gen.gen, Trojan:Win32/Occamy.C, Ransom_Gen.R011C0WAC20, and others.
BlueCheeser ransomware alters the Windows Registry and Task Manager for its own purposes. The cyber infection ensures that it is booted every time when the infected computer turns on. In order to do this, the malware includes specific keys and processes to the sections that are mentioned above.
Additionally, BlueCheeser ransomware can be able to scan the entire computer system once in a while and look for encryptable documents. The malicious actors want to make sure that no components have been left unencrypted.
Afterward, BlueCheeser ransomware uses the Advanced Encryption standard to lock up files such as word documents, PDF documents, excel sheets, audio files, video files, .zip content, .exe components, and many more. Once the encryption is performed, the user cannot access the blocked files properly anymore.
However, you should expect that BlueCheeser ransomware will try to harden the recovery process for you. This can happen by deleting the Shadow Volume Copies of encrypted files and documents by running specific PowerShell commands. Also, both encryption and decryption keys are safely stored on a remote server that is reachable only for the criminals.
BlueCheeser ransomware developers try to frighten the victims by claiming that their files will be lost forever if they do not agree to pay. This type of claim is written as the last line of the Instructions.txt ransom message:
Looks like all your desktop files have been encrypted!
To decrypt, send $400 to the bitcoin wallet: 43IU64UGG645G37I670IITYYR5093U55KJ5HE
RIP Your personal files if you dont pay…
BlueCheeser virus might also target your Windows hosts file and aim to permanently damage it. This type of activity is performed when the cybercriminals want to prevent users from entering various cybersecurity forums and pages.
However, you should know that there is a big reason not to pay the cybercriminals, no matter how frightening BlueCheeser ransomware looks to you. The main fact is that hackers are very likely to scam their victims. They might provide you a fake tool or no key at all after you pay them the demanded ransom and just simply run off uncaught.
BlueCheeser ransomware makes the computer system vulnerable to other infections and might even disable the antivirus software to let in some other threats. Ransomware viruses are often used for the distribution of other malware such as trojans. These parasites aim to steal personal information and money, mine cryptocurrency, overuse the CPU power.
If you are looking for a way to avoid these possible consequences, the best thing to do would be to remove BlueCheeser ransomware from your Windows computer system and get rid of all the additional malicious products that were injected in your device during the ransomware attack.
You can successfully complete the BlueCheeser ransomware removal with the help of reliable antimalware products that will take care of the task for you. A piece of advice would be not to try to get rid of the cyber threat on your own as there is a chance of failure due to the complexity that this parasite has.
If you have any trouble with the elimination, try rebooting your PC in Safe Mode with Networking first. When BlueCheeser ransomware is permanently gone, you should start thinking about data recovery possibilities. Travel to the very end of this article where you will find three file restoring options some of which might appear really handy.
Be aware of unknown email messages
Ransomware is quite commonly delivered through infectious emails that pretend to be official letters from healthcare, financial, or shipping organizations. Such messages can travel to your email spam section but might also fall in the inbox. Regarding this fact, it is very important to measure the expectancy of such a letter.
According to NoVirus.uk experts,[4] if you have not been waiting for a particular email message to come, you should think if its links or attached documents are worth loading. If you have already downloaded the questionable file, do not risk your computer's safety by launching the attached component without scanning it with a trustworthy antivirus program.
Furthermore, you should always check if the message is coming from an official email or some type of weird-looking one. Plus, if you find any grammar mistakes in the contact of the text message, this might be an accurate sign that you are dealing with something unknown as reliable companies would not leave any mistakes in their official texts.
To add, ransomware infections can also get distributed through other sources such as hacked RDPs that included weak passwords or none at all, fake flash player updates, malvertising ads, etc. You should always be careful while browsing the Internet and make sure to employ a reliable antivirus product.
BlueCheeser ransomware removal guidelines
BlueCheeser ransomware removal should be taken care of as soon as possible by using specific tools only. Anti-spyware and anti-malware products are the best help in this type of situation as they can get rid of all the malicious components that the virus has planted. However, if your antivirus is having some trouble with detecting or removing the ransomware, you should try booting your computer in Safe Mode with Networking or activating System Restore.
When you remove BlueCheeser ransomware from your Windows device, it is time to search for some damage that might have been applied by the malware. Tools such as SpyHunter 5Combo Cleaner and Malwarebytes are capable of scanning the computer system. If this software provides any results with system problems and damage, you can try repairing all the altered objects by employing another automatical utility such as FortectIntego.
Getting rid of BlueCheeser virus. Follow these steps
Manual removal using Safe Mode
To deactivate malicious settings and changes on your Windows computer system, you should boot your device in Safe Mode with Networking by employing the following instructions.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove BlueCheeser using System Restore
To disable the ransomware virus and all the malicious changes that it has brought to your device, you should opt for the System Restore feature. Enable this function with the help of the following guidelines.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of BlueCheeser. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove BlueCheeser from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts..himr files signify about the encryption process. Keep in mind that the developers of BlueCheeser ransomware virus will try to convince you to pay the ransom price. However, this is not recommendable as you are taking a risk of getting scammed. Instead, use some of the material provided below.
If your files are encrypted by BlueCheeser, you can use several methods to restore them:
Try employing Data Recovery Pro for file restoring purposes.
If the ransomware virus has encrypted your files, you can try repairing some of them by using this piece of software and completing every step as required.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by BlueCheeser ransomware;
- Restore them.
Activate Windows Previous Versions feature for data recovery.
Try using this type of software if the ransomware has affected your files. However, make sure that you have booted the System Restore feature in the past, otherwise, this method might not work.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow Explorer might be helpful for file restore.
If the ransomware virus did not permanently delete or destroy your files' Shadow Volume Copies, you can give this piece of software a try.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Cybersecurity experts are still working on the official .himr files decrypter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from BlueCheeser and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Advanced Encryption Standard. Wikipedia. The free encyclopedia.
- ^ raby_mr. Raby. Twitter Posts. Twitter. Social platform.
- ^ 44 engines detected this file. BlueCheeser.exe. Virus Total. Detection information.
- ^ NoVirus.uk. NoVirus. Security and spyware news.





















