Broforyou.me ads (fake) - Free Guide
Broforyou.me ads Removal Guide
What is Broforyou.me ads?
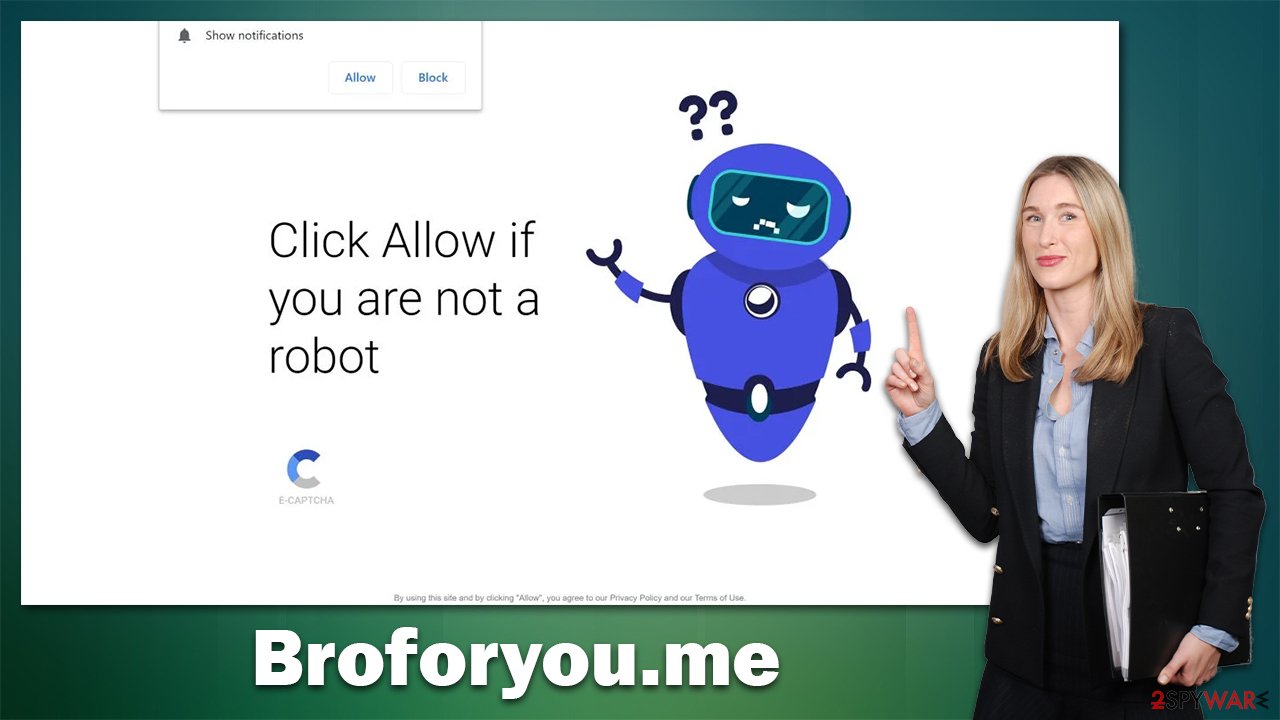
Broforyou.me shows fake messages only to send you intrusive ads later

Broforyou.me is a malicious website created by fraudsters that serve intrusive push notifications containing ads to unsuspecting users. Generally, people don't access this domain intentionally but are instead redirected from shady links on torrents, cracks, and online streaming sites which have been booby-trapped with malignant codes. Moreover, some forms of adware may be the cause of these redirects alongside an increase in pop-ups, banners auto play videos, and so forth appearing on your screen without your consent or knowledge.
When visiting the Broforyou.me website, users can fall victim to accidentally pressing the “Allow” button in the push notification prompt, thereby allowing it to send notifications straight to their screens without warning. These pop-ups will appear at any time and take precedence over any other app running on your device.
Broforyou.me ads can be hazardous since their links may lead to malicious websites that attempt to lure you into fraudulent surveys and get-rich-quick schemes. To stay safe online, we implore you not to engage in such suspicious activity – instead, take the necessary steps for the removal of these unwanted advertisements.
| Name | Broforyou.me |
| Type | Push notifications, ads, pop-ups, scam |
| Distribution | Intrusive pop-ups can start showing up at some point after the “Allow” button is pressed within the notification prompt |
| Symptoms | You may start seeing intrusive pop-ups on your desktop – clicking these may lead to insecure or even malicious websites |
| Risks | Shown pop-ups incorporate fake notices and push scams. Links can also lead to websites filled with malware |
| Removal | You can stop unwanted notifications by accessing web browser settings. If you suspect adware infection, you should use SpyHunter 5Combo Cleaner security software to get rid of it |
| Other tips | It is important to clean web browser caches to prevent further data tracking and other issues related to web data corruption – use FortectIntego to do this quicker |
How do scammers behind Broforyou.me operate
The push notification feature is both legitimate and commonly utilized by websites to send useful information directly to users. Unfortunately, scammers are aware of this as well and may try to convince individuals to subscribe so that they can receive ads or sponsored content- which would provide them with steady income via advertising. Therefore it is important for everyone to be mindful when engaging in such activities.
To entice users to sign up for push notifications, scammers often misrepresent the feature and mask it as something else. For instance, they might deceive individuals into believing that robot verification is essential in order to advance. Since some customers may have encountered a captcha previously, they can hastily believe this claim and click Allow. A few other messages you should watch out for include the following:
- If you are 18+ tap Allow
- Click Allow to confirm you're not a robot
- Can't play this video! Perhaps, your browser doesn't allow video playback. Click “Allow” button to play video
- Click “Allow” to continue streaming
- Just one more step! “Allow” to continue, etc.
Phishing methods are a common occurrence in the digital world, but if you have ever encountered one of these scams before, it is easy to detect them when they arrive again. Genuine websites will never lock their content behind push notifications' consent – regardless of what is written on the page.
Clicking the “Allow” button would lead to an unrestricted delivery of information from that particular website straight onto your screen. Therefore be vigilant and remember: no respectable site employs this method.
How to remove adware and Broforyou.me pop-ups
Although it may seem daunting if you have enabled notifications from a malicious website, do not fear. You can disable this activity with ease via your browser settings. It is imperative that you don't interact with links sent by these untrustworthy websites, as doing so could leave you vulnerable to malware infections, data breaches, or even financial scams.
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
After you have managed those pesky notifications, take a few more minutes to investigate the presence of any adware on your system. Usually installed by unwitting users through bundling or similar strategies, this type of unwanted software can be an unwelcome surprise if not identified and removed promptly.
For maximum protection, we suggest performing a complete system scan with either SpyHunter 5Combo Cleaner or Malwarebytes anti-malware. This can ensure that no malicious programs have infiltrated your device and will give you peace of mind. In addition, it is critical to clear browser caches as persistent trackers remain even after PUPs are eradicated – using FortectIntego would be the most efficient way for this task.
General tips on online protection from phishing content
One of the most important ways to avoid being redirected to phishing websites is to always be vigilant about the web pages you are visiting. Be sure to double-check the URL for any suspicious characters or misspellings, and be aware that some scammers may use authentic-looking URLs to trick unsuspecting users. Additionally, it’s prudent to never click on links that have been sent to you via email or social media, as these could be malicious. When in doubt, always type the URL manually into your browser.
You can also take extra security measures by avoiding public Wi-Fi whenever possible and enabling two-factor authentication for any accounts that offer it. Additionally, regularly updating your software and keeping antivirus programs enabled can help protect you from potential threats.
Be aware of recent updates to the Terms of Service for any websites or services you use. If a service begins logging more data all of a sudden, this could be a warning sign that your information is vulnerable. Stay up-to-date, and be sure to read any changes in the ToS before agreeing.
If you believe you may have been redirected to a phishing website, take immediate steps to protect yourself. Contact the website or service in question and report any suspicious activity. Change any passwords associated with the website or service, and consider turning on two-factor authentication for extra security.
Finally, closely monitor your accounts and credit report in the coming months to ensure that no fraudulent activity has taken place. Any suspicious activity should be reported to the appropriate authorities.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.






