Cezar ransomware / virus (Virus Removal Guide) - Feb 2020 update
Cezar virus Removal Guide
What is Cezar ransomware virus?
Cezar ransomware is a file-locking infection that compromises Run and RunOnce keys to execute during Windows boot

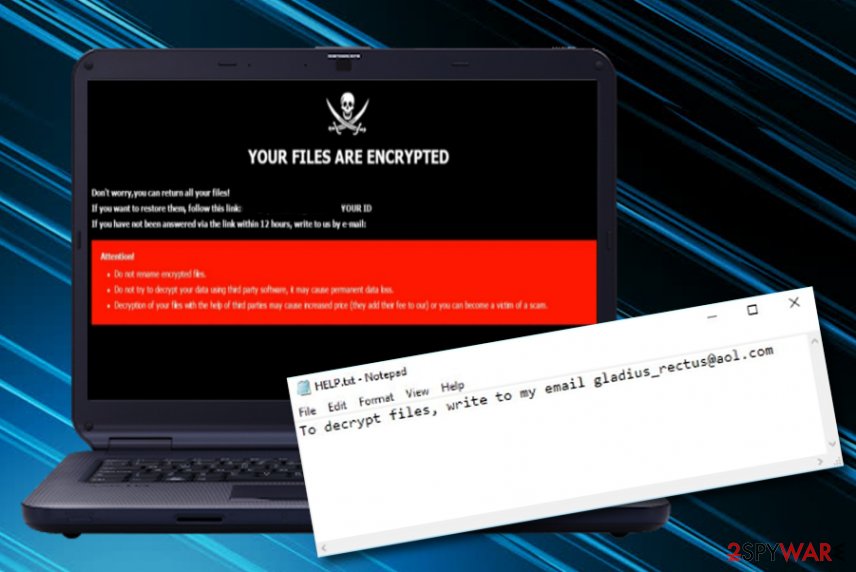
Cezar ransomware is a file-encrypting virus that can cause the loss of all files on the targeted machine. It is the continuation of the infamous Dharma ransomware[1] and has emerged in August 2017. The malicious program[2] encrypts all data by adding a specific file extension that includes the victim’s ID number, cybercriminals' email address, and either .cezar or .cesar file extension. Cezar virus encrypts all the data that is found on the infected Windows computer system, including pdfs, Microsoft Office documents, images, audios, videos, virtual drive files, and more.
It then drops the ransom note called HELP.txt which urges users to contact the cybercriminals via email gladius_rectus@aol.com or gladius_rectus@india.com. Users must pay the ransom in Bitcoin to get their data back, otherwise, it will be left blocked forever. At least this is what the cybercriminals want you to believe. However, staying away from ransom payments would be a wiser choice than accepting them as the crooks might try to scam you.
Users on Reddit have been complaining about Cezar ransomware virus rooting in their systems and supposedly compromising the RDP configuration to get in.[3] Also, security researchers have already noticed that the ransomware virus is delivered via Necurs botnet through phishing email messages and their infectious attachments. Nevertheless, some people have seen this ransomware provided as RaaS on the Dark Web's market where anyone who wants to play with the malware and infect potential victims can purchase it for a specific price.
| SUMMARY | |
| Name | Cezar |
| Type | Ransomware virus/malware |
| Family | Dharma ransomware |
| First discovered | This cyber threat was first spotted in August 2017 and has emerged again in 2020 |
| Encryption | The ransomware virus employs a unique encryption cipher such as AES to lock up all files, folders, and documents found on the Windows computer system. Afterward, the .cezar or .cesar appendix is added to each filename |
| Ransom note | The malware provides the HELP.txt ransom note, after the encryption, that includes crooks' email addresses: gladius_rectus@aol.com or gladius_rectus@india.com |
| Related files | When the malware infiltration process happens, Cezar virus can bring files such as notepad.exe, svchost.exe, setup.exe, patch.exe, update.exe, and software-update.exe and install them in the system |
| Modules | The newly-updated version of Cezar ransomware might be capable of tracking user activity, harvesting private details, etc. |
| Distribution | Spreading of this parasite relies on various different techniques such as phishing email messages and their malicious attachments, botnets and other malware, cracked software such as key generators or fake setups from torrenting networks, vulnerable RDP settings |
| Removal | If you have been dealing with this malware lately, you should take action against it ASAP. Our recommendation would be to employ a reliable antimalware product that will be capable of dealing with the ransomware virus |
| Data recovery | There is no official decrypter released for .cezar or .cesar files at the moment. However, our security experts have provided some alternative data recovery tools that you can find at the end of this article |
| Fixing tool | If your computer system has experienced some type of damage, you can try fixing things with the help of software such as FortectIntego |
When Cezar ransomware appears on the targeted Windows computer, it heads for the Run and RunOnce keys that allow the payload to execute every time when the machine is turned on. Furthermore, the malware might include some files in the system, for example, notepad.exe, svchost.exe, setup.exe, patch.exe, update.exe, and software-update.exe. Following a successful computer infiltration and data encryption, Cezar ransomware drops a ransom note that contains a short message from criminals to the victim:
To decrypt files, write to my email gladius_rectus@aol.com
This short Cesar ransomware ransom note is provided in a simple .txt file named “HELP.txt.” However, it’s quite an unusual ransom message because it does not include any information about data recovery possibilities and how it may cost for the victims. It is clear why cybercriminals do not want to reveal the final price of the ransom – they might be open to negotiations with potential victims. In addition, different versions of Cesar malware might be adding one of the following file extensions to encrypted files:
- .id-.[JasonStewem@aolonline.top].cesar;
- .id-.[btc2017@india.com].cesar;
- id-.[bonum_malum@aol.com].
However, even though Cezar ransomware developers do not provide any particular information about the ransom price, most of the demands vary from $100 to $2000 or even more and need to be transferred during a particular time period. Also, criminals are very likely to urge for some type of digital currency such as Bitcoin as this type of cryptocurrency allows the hackers to stay safe from tracking and keep their identities a secret.

A big problem with .cesar ransomware is that it is capable of deleting Shadow Volume Copies by executing specific PowerShell command. Sadly, the Shadow Copies are necessary for recovering files using third-party software and criminals seek to make this data recovery method not work for the victims. Currently, the official decryptor for .cezar and .cesar files is not released yet. However, some versions of Dharma are already decryptable.[4] Thus, there’s hope.
If this ransomware has hit your computer, we strongly recommend using a decent antispyware product to remove Cezar ransomware from the system. Once you eliminate the ransomware virus and all the malicious payload that was brought to the computer as a result of the dangerous infection, you might be interested in tools such as FortectIntego or SpyHunter 5Combo Cleaner if there are any corrupted areas on the Windows device as this type of software might help to fix them.
You should not put Cezar ransomware removal aside because it is a highly important task that you must complete. Only after deleting the virus from the system you will be able to use it again securely. The reason why we recommend using the automatic spyware/malware removal tool is that some viruses spread in tandem with other severe malware variants such as Trojans or keyloggers and you will need strong software to deal with all these potential cyber threats.
Update 2020: Cezar (Dharma) ransomware searching for targets in Italy
According to security researchers, Cezar ransomware that was first discovered in 2017, decided to renew its activities in 2020. This time malicious actors are targetting people who live in Italy by delivering them malware-laden payload through email spam that contains VBS (Visual Basic Scripts).
Furthermore, investigations have provided results that Cezar virus includes improved functionality but uses the same operating principle as earlier. The ransomware virus employs a cipher such as AES and locks up all the components that are found on the infected Windows PC. However, researchers have found out that the malware was added with some complex modules and now might be capable of these activities:
- Cybercriminals can have the ability to track victims and their computers.
- The malware might be programmed to hijack the users' activities.
- The virus can include harvesting of personally-identifiable information from the infected device.
Methods used for malware distribution
According to LesVirus.fr experts,[5]Dharma ransomware variants usually employ traditional malware distribution techniques for proliferation. Most of the time it arrives as a malicious email attachment[6] that needs to be opened by the computer user in order to be run. To convince the victim to open the document, criminals spoof the sender’s address and rename the malicious file as invoice, a message from courier, receipt, or another important document that might interest the potential victim.
Furthermore, ransomware viruses can also get spread through other malware forms such as trojans and botnets and be downloaded as a regular file at first until the embedded macros are enabled. However, this is still not all about the possible distribution techniques of file-encrypting viruses. These malicious threats can get infiltrated through hacked RDPs. Hackers usually steal the password or search for unlocked configuration and connect to the computer system remotely.
In addition, ransomware is often uploaded on torrenting websites that are filled with game cracks, key generators, fake setups, and various questionable files that look harmless only from the first view. Since you have learned about the distribution tactics of ransomware viruses, it would be recommendable to also learn about their prevention:
- Always investigate your received email. Check the sender, view the content for possible grammar mistakes, and measure the expectancy of such message. Also, do not open any questionable attachments without scanning them with an antimalware program.
- Avoid visiting peer-to-peer networks. Make sure that you get all of your products and services from official sources. It is better to pay more than to deal with malware and its consequences later.
- Install reliable antivirus protection. If you do not already have antimalware software on your Windows computer, you should get one ASAP. Make sure that you keep this tool regularly updated.
Steps to take after Cesar virus attack
Cezar ransomware removal is the first thing you should do when you discover that you are infected with this malware. Postponing the elimination might relate in more damage to your Windows computer system. Besides, you will not be able to recover your files properly with additional software until the parasite is residing on your device.
If you want to remove Cezar ransomware, you should rely on automatical software that would be able to delete with this parasite. However, if your antivirus tool is being blocked by the malware, you can try diminishing malicious processes on your Windows computer system by rebooting it in Safe Mode with Networking.
Furthermore, Cezar ransomware virus can have posed some type of harm on your device during the infection process or might have infiltrated additional malware to the system. To check for possible damage, use SpyHunter 5Combo Cleaner or Malwarebytes. If these tools find any compromised areas on the machine, you might have a chance of repairing them with software such as FortectIntego.
Video clip displaying Cesar ransomware removal
Cezar ransomware virus is a complex malware form that can be hard to eliminate if you have no understandings of how to complete the process and what tools to use for it. Our cybersecurity experts understand the struggle and decided to create some visual material that would be very easy for all users to understand. Look below and you will find the Youtube video:
Getting rid of Cezar virus. Follow these steps
Manual removal using Safe Mode
If you want to deactivate some malicious settings on your Windows operating system and disable the ransomware virus from operating further, you should reboot the device in Safe Mode with Networking as described below
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Cezar using System Restore
You can try diminishing malware-induced changes and deactivating the virus itself by opting for System Restore. If you do not know how to complete such a task, the following instructions will help you
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Cezar. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Cezar from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Unfortunately, .cezar file extension is undefeatable and currently there are no ways to restore your files for free. Unless you have a backup, the chances to restore them are very low. Despite that, you can try the following methods:
If your files are encrypted by Cezar, you can use several methods to restore them:
Data Recovery Pro perfectly helps to recover corrupted files
Data Recovery Pro can be used on files that were corrupted, and it can also help to restore deleted files. Although it wasn't created for the recovery of encrypted files, you can still try it and see what it can do.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Cezar ransomware;
- Restore them.
Windows Previous Versions feature might be useful
Windows Previous Versions feature is useful if you do not have a large number of files to return. Also, the Windows Restore function should have been enabled before the attack occurred.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Try ShadowExplorer software
ShadowExplorer is a software that can help you to restore files from Shadow Volume Copies. If the virus failed to delete these copies, there is still hope to recover some of your files.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
The .cezar and .cesar files decrypter is not developed yet.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Cezar and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Ransomware: the Tool of Choice for Cyber Extortion. FireEye. Current Threats.
- ^ Robert Hackett. Everything to Know About The Latest Worldwide Ransomware Attack. Fortune. Fortune 500 Daily & Breaking Business News.
- ^ .CEZAR ransomware. Reddit. Forum Comments.
- ^ Dharma Ransomware Master Encryption Key Released. The Merkle. The latest Crypto, Finance, Infosec, and Tech news.
- ^ LesVirus. LesVirus. Malware Removal Tutorials.
- ^ Chris Hoffman. How To Spot A Dangerous Email Attachment. MakeUseOf. The website about technology and gadgets.





















