Clay ransomware (Virus Removal Guide) - Free Instructions
Clay virus Removal Guide
What is Clay ransomware?
Clay ransomware – computer infection that holds files hostage until $300 ransom is paid in bitcoin
Clay ransomware is a cryptovirus that was first discovered by a security researcher xiaopao.[1] This malware attacks Windows operating systems via various methods, including spam emails, malicious links, software cracks, etc. Once installed, it operates just like any other virus of such type – it locks all videos, music, documents, and other files on the system with strong encryption. Suchlike data can no longer be accessed by victims. Unlike other ransomware, the Clay virus does not append an extension to the encrypted files.
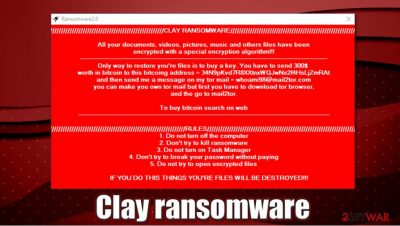
After the encryption process, the malware drops a ransom note, which comes in the form of a pop-up window titled “Ransomware2.0.” It explains to users what happened to their files and asks them to transfer $300 worth of bitcoin to 34N9pKvd7R8XXtnxWQJwNs2f4HsLjZmRAt digital wallet in order to return encrypted data. Crooks behind Clay ransomware virus also leave an email behind for communication – whoami98@mail2tor.com.
| Name | Clay ransomware |
|---|---|
| Type | Ransomware, data locking malware, cryptovirus |
| Malware family | No connections to known malware families have been found |
| File extension | No file extension is appended to the affected files, although they can not be opened regardless |
| Ransom note | “Ransomware2.0” pop-up window |
| Contact | whoami98@mail2tor.com |
| Ransom size | $300 |
| Bitcoin wallet | 34N9pKvd7R8XXtnxWQJwNs2f4HsLjZmRAt |
| File Recovery | If no backups are available, recovering data is almost impossible. Nonetheless, we suggest you try the alternative methods that could help you in some cases – we list them below |
| Malware removal | Perform a full system scan with powerful security software, such as SpyHunter 5Combo Cleaner |
| System fix | Malware can seriously tamper with Windows systems, causing errors, crashes, lag, and other stability issues after it is terminated. To remediate the OS and avoid its reinstallation, we recommend scanning it with the FortectIntego repair tool |
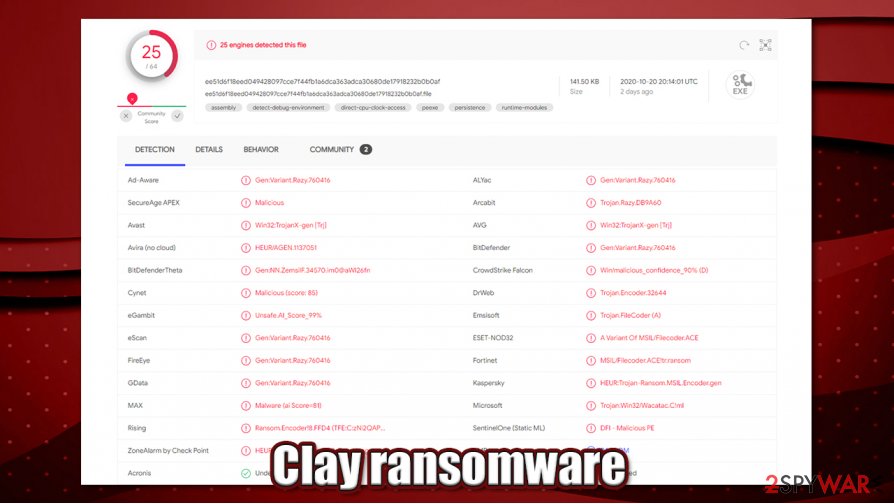
Clay ransomware is one of many new computer infections that are designed for money extortion. Cybercriminals are very interested in creating this type of malware, as it can be very profitable if successful. Therefore, they could use several different methods to deliver the infection to as many computers as possible. Speaking of which, several anti-malware solutions recognize the sample, which is detected under the following names:[2]
- Win32:TrojanX-gen [Trj]
- Trojan.Encoder.32644
- Trojan:Win32/Wacatac.C!ml
- Gen:Variant.Razy.760416
- HEUR:Trojan-Ransom.MSIL.Encoder.gen, etc.
Once the virus is installed, it would perform Windows system changes for the encryption to be successful. For example, it would delete Shadow Copies to prevent the usage of automatic system backups for easy recovery after Clay ransomware removal.
Besides regular system changes, the malware also disables certain system functions – Task Manager in particular. Therefore, users can not launch it to stop the malicious process from running. As a result, all the incoming files are encrypted, so the computer becomes almost unusable.
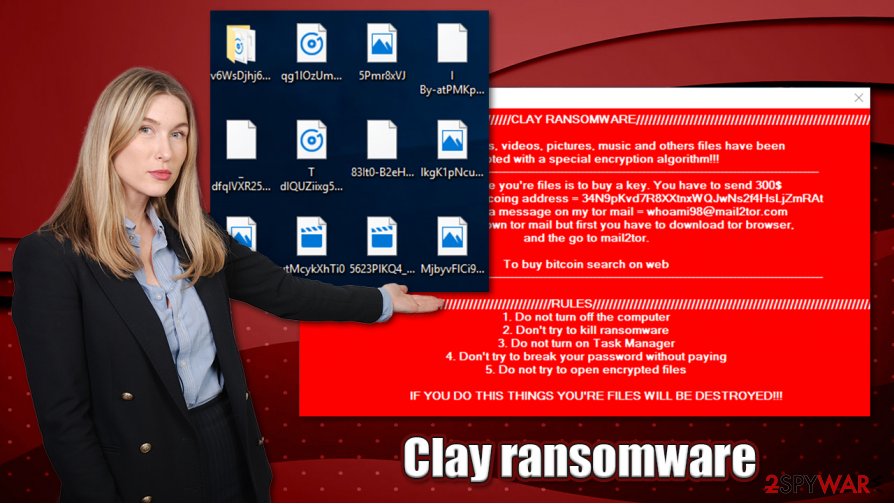
Clay ransomware encrypts files with a strong encryption algorithm,[3] although it does not append any file extension. Suchlike modified files lose regular icons, however. After that, a ransom note is delivered, which reads:
////////////////////////////////CLAY RANSOMWARE////////////////////////////////
All your documents. videos. pictures. music and other files have been
encrypted with a special encryption algorithm!!!___________________________________
Only way to restore you're files is to buy a key. You have to send $300
worth in bitcoin to this bitcoing address = 34N9pKvd7R8XXtnxWQJwNs2f4HsLjZmRAt
and then send me a message on my tor mail = whoami98@mail2tor.com
you can make your own tor mail but first you have to download tor browser.
and the go to mail2tor.to buy bitcoin search on web
___________________________________
///////////////////////////////////////RULES//////////////////////////////////////
1. Do not turn off the computer
2. Don't try to kill ransomware
3. Do not turn on Task Manager
4. Don't try to break your password without paying
5. Do no try to open encrypted filesIF YOU DO THIS THINGS YOU'RE FILES WILL BE DESTROYED!!!
//////////////////////////////////////////////////////////////////////////////////////////
DECRYPT FILES
REAMING TIME: 00:59:39
Since the virus modifies Windows system heavily, you should access Safe Mode with Networking before you attempt to remove Clay ransomware virus from your system – we explain how below. Once in Safe Mode, initiate a full system scan with SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable security software. FortectIntego can also serve as an excellent tool to recover normal Windows functions and remediate system files. After that, refer to alternative methods for data recovery.
Paying cybercriminals is risky. How to recover encrypted files?
In the ransom note, cybercriminals behind the Clay file virus say that there is no other method to recover data besides paying them. They also include a timer that only gives victims an hour, although it is not specified what it does. Presumably, it indicates the time when recovering the decryptor is possible, however, there is no evidence for that.
The harsh truth is that only cybercriminals have the required key that would unlock files encrypted by the Clay virus. However, security experts[4] do not recommend paying or contacting the attackers for that matter, as they might never deliver their promises, even after bitcoin payment is sent. As a result, you might not only lose access to your files but also the money that you paid to crooks. This is especially true for new malware strains, where not many successful decryption tool retrievals were observed.
Instead, you can rely on alternative methods to recover Clay virus files, although keep in mind that for them to work, malware should fail to delete Shadow Copies. Nonetheless, third-party recovery applications might sometimes be able to recover at least some files. For detailed instructions, check the bottom section of this post.
Clay ransomware removal and file recovery
Before we begin this Clay ransomware removal guide, we would like to say that data recovery without obtaining the key from the attackers is unlikely. However, there is always a chance of retrieving at least some of your lost files, so you should not give up before you try. Alternatively, you can pay the $300 to threat actors, although it might end in a disaster to you – do it at your own risk.
As crooks mention in their ransom note “Ransomware2.0,” even shutting down the computer might damage files permanently. They might be bluffing – or not. Thus, just to be safe, you should make a copy of all the encrypted data before you remove Clay ransomware virus. Encrypted data does not hold any malicious code inside, so it is safe to use.
Finally, use the instructions below to access Safe Mode with Networking and scan your computer fully with SpyHunter 5Combo Cleaner, Malwarebytes, or another security tool. Afterward, you can perform further checks for Windows system damage and remediation with FortectIntego. Once you are sure that the machine is clear from the virus, check the data recovery guide below; maybe you will get lucky.
Getting rid of Clay virus. Follow these steps
Manual removal using Safe Mode
Since Clay files virus disables some Windows features, enter Safe Mode with Networking and initiate full system scan:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Clay using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Clay. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Clay from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Clay, you can use several methods to restore them:
Data Recovery Pro option
This program might be able to extract some working copies of files from your hard drive.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Clay ransomware;
- Restore them.
Make use of Windows Previous Versions feature
If malware failed to delete Shadow Copies, follow these steps:
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer can automate data recovery process
In case Shadow Copies remain on the system, ShadowExplorer can help you recover data quicker.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryption tool is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Clay and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ xiaopao. Twitter. Social Network.
- ^ ee51d6f18eed049428097cce7f44fb1a6dca363adca30680de17918232b0b0af. Virus Total. File and URL analysis.
- ^ What is Encryption? | Types of Encryption. Cloudflare. Security solutions.
- ^ Usunwirusa. Usunwirusa. Cybersecurity advice and malware insights.





















