Cms100.xyz ads (fake) - Free Guide
Cms100.xyz ads Removal Guide
What is Cms100.xyz ads?
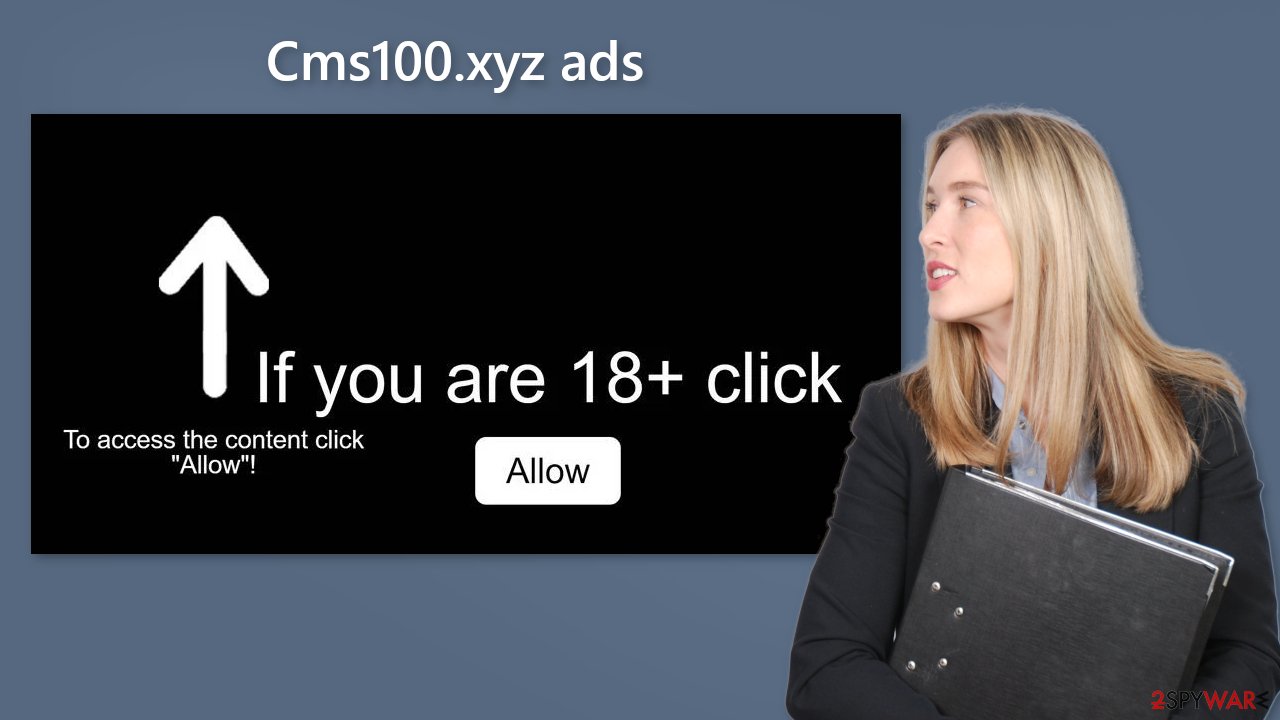
Cms100.xyz shows a deceptive message to get users to click on the “Allow” button

Cms100.xyz is a fake website that was created by crooks. The main goal of this page is to generate revenue from pay-per-click advertising.[1] It displays a deceptive message asking users to click “Allow” if they are over 18 to access the content. However, there is no content to explore on this site.
Users start getting spammed with annoying pop-up ads that can appear even when the browser is closed. Crooks may be using rogue advertising networks[2] that place ads leading to scam pages. On these dangerous websites, people can get tricked into providing personal information, downloading PUPs (potentially unwanted programs),[3] and even malware.
| NAME | Cms100.xyz |
| TYPE | Push notification spam; adware |
| SYMPTOMS | Annoying pop-up ads start appearing in the corner of the screen, sometimes even when the browser is closed |
| DISTRIBUTION | Shady websites, deceptive ads, freeware bundling |
| DANGERS | Links embedded in the pop-ups may lead to dangerous pages where people can get tricked into providing their personal information or downloading PUPs and malware |
| ELIMINATION | Disable push notification via browser settings |
| FURTHER STEPS | Use a maintenance tool like FortectIntego to clear your browsers from cookies and cache |
Distribution of push notification spam sites
There are thousands of pages just like Cms100.xyz. They are easy to create and duplicate. They may also become a good passive income source as crooks can get paid for every click users make. To avoid them it is important to know how they are spread on the Internet.
Usually, they are placed behind deceptive ads and sneaky redirects on other shady sites. That is why we recommend only visiting websites that you know and trust. Do not use illegal streaming pages because they are unregulated. They may display fake “Download” and “Play” buttons.[4]
It is also worth noting that the appearance of spam sites could be also explained by an adware infection. It operates in the background without the users' knowledge and causes an increased amount of commercial content, like pop-ups, banners, and redirects.
Disable the pop-ups
The first thing you should do is go to your browser settings and see if you can disable the push notifications from there:
Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate Privacy and security section and pick Site Settings > Notifications.
![Stop notifications on Chrome PC 1 Stop notifications on Chrome PC 1]()
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
![Stop notifications on Mozilla Firefox 1 Stop notifications on Mozilla Firefox 1]()
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
MS Edge:
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.
![Stop notifications on Edge 1 Stop notifications on Edge 1]()
- Toggle the switch to the left to turn notifications off on Microsoft Edge.
MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
Protect your data while browsing
You have probably noticed, that almost every website you visit asks to “Allow” cookies. They are small data files that can track data, like your IP address, geolocation, websites you visit, links you click on, and things you purchase online. Generally, this is not a bad thing as it helps websites to personalize the user experience.
However, fraudsters can use this information to make a profit. Cookies can be sold to advertising networks or other third parties. If the pages you visit do not have strong security, cookies can also be hijacked and used for malicious purposes.
That is why it is important to clear your browsers regularly. This can be automated with a maintenance tool like FortectIntego. It can delete all cookies and cache and fix system damage, like errors, and registry issues which is especially helpful after a virus infection.
Adware removal
Once you block the notifications, there is still a chance that there is adware hiding in your system. You might be experiencing an increased amount of commercial content like surveys, banners, pop-ups, and redirects. We strongly suggest deploying professional security tools like SpyHunter 5Combo Cleaner or Malwarebytes to scan your machine if you have any of these symptoms.
Antivirus software can detect suspicious processes running on your machine and eliminate all the related files. What is more, it can prevent such infections in the future by warning you about a suspicious download. You can also remove programs manually, but it can be difficult to identify PUPs as they are often disguised as “handy” tools that you use every day.
It may look like antivirus software, system optimizer, media player, etc. Besides, manual removal can sometimes result in a renewal of the infection, as people fail to eliminate all the related files and entries. Otherwise, if you want to perform manual removal, you can follow the instructions posted below for Windows and Mac systems:
Windows 10/8:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Windows 7/XP:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.
![Uninstall from Windows 7/XP Uninstall from Windows 7/XP]()
- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Mac:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ What Is PPC? Learn the Basics of Pay-Per-Click (PPC) Marketing. Wordstream. Advertising Solutions.
- ^ Zeljka Zorz. How does a rogue ad network function?. Helpnetsecurity. IT Insights.
- ^ Wendy Zamora. What is a PUP? – How to avoid potentially unwanted programs. Malwarebytes. Security Tips and Tricks.
- ^ Andy Maxwell. Google Targets Fake ‘Download’ and ‘Play’ Buttons. Torrentfreak. Filesharing News.












